Privacy is a multifaceted gem. Like a diamond, the sum of its part is what makes the whole. Lose clarity, lose value. Lose the right color, lose value. Lose weight, lose value.
Electronic surveillance privacy is only one facet of your privacy diamond. Get to know the folks make up some of privacy's other angles...
Why Is Privacy So Damn Important Anyway?
Privacy is so much more than the right to keep information secret within yourself. It provides the right to express yourself and expose yourself within small groups of trusted associates precisely because confidentiality is respected within the group. The current collection of online executives belittle privacy as no longer relevant in the new digital age. And they are precisely the ones who protect their privacy with the most vehemence. Look how revealing Mark Zuckerberg is not, on his own Facebook page. He sued in Massachusetts to keep information about his career secret.
Privacy is essential for mental health, for a quality of life. And so it is not about whether you “don’t have anything to hide.” It’s about all of us, and the value to society in having autonomous, assertive individuals with the opportunity to learn and take risks and make good decisions in dignity and uninterrupted contemplation. Call it privacy.
~Robert Ellis Smith, author / publisher, expert witness on privacy, credit reporting, surveillance, medical confidentiality, Social Security numbers, and identity theft. Keep current on privacy topics with his newsletter Privacy Journal, and all of his books. (more)
Ultimate Privacy... How to Become Invisible.
In 1959, J. J. (Jack) Luna sold his outdoor advertising business in the Upper Midwest and moved with his wife and small children to the Canary Islands off the coast of West Africa. Outwardly, he was a professional writer and photographer. Secretly, he worked underground in an activity that was at that time illegal under the regime of Generalissimo Francisco Franco.
In 1970 Franco yielded to intense pressure from the western world and moderated Spain's laws, leaving Luna free to come in from the cold. By that time, however, privacy had become an ingrained habit. In the years that followed he started up various one-person low-profile businesses, built them up and then sold them.
Luna is especially interested in designing and building secret spaces and hiding places. He currently has a 3300-square foot three-level safe house for sale that is set in an almost-invisible location despite being within city limits. The exterior is complete but the interior is unfinished, awaiting a buyer who will decide which spaces or rooms are to have secret entrances. The approximate price, when finished according the buyer’s instructions, will be $795,000, plus (if desired) the cost of a secret escape tunnel into the adjoining forest. The location is in the Pacific Northwest. (...or so we are told. Remember, we are dealing with the Invisible Man here.) (more)
~JJ Luna, International Privacy Consultant, and author — How to Become Invisible.
Wednesday, April 2, 2014
Smartphone kill-switch could save consumers $2.6 billion per year...
...and why you will probably never see it.
 Technology that remotely makes a stolen smartphone useless could save
American consumers up to $2.6 billion per year if it is implemented
widely and leads to a reduction in theft of phones, according to a new
report...
Technology that remotely makes a stolen smartphone useless could save
American consumers up to $2.6 billion per year if it is implemented
widely and leads to a reduction in theft of phones, according to a new
report...
Americans currently spend around $580 million replacing stolen phones each year and $4.8 billion paying for handset insurance... (more)
Do you really think phone and insurance companies are going to kill this goose?
 Technology that remotely makes a stolen smartphone useless could save
American consumers up to $2.6 billion per year if it is implemented
widely and leads to a reduction in theft of phones, according to a new
report...
Technology that remotely makes a stolen smartphone useless could save
American consumers up to $2.6 billion per year if it is implemented
widely and leads to a reduction in theft of phones, according to a new
report...Americans currently spend around $580 million replacing stolen phones each year and $4.8 billion paying for handset insurance... (more)
Do you really think phone and insurance companies are going to kill this goose?
Nikola Tesla Redux - Wireless Power Finally Arrives
via one of our top Canadian Blue Blaze irregulars...
TODAY
"We're going to transfer power without any kind of wires," says Dr Hall, now Chief Technology Officer at WiTricity, a startup developing wireless "resonance" technology.
"But, we're not actually putting electricity in the air. What we're doing is putting a magnetic field in the air." ...
In the house of the future, wire-free energy transfer could be as easy as wireless internet.
If all goes to WiTricity's plans, smartphones will charge in your pocket as you wander around, televisions will flicker with no wires attached, and electric cars will refuel while sitting on the driveway. (more)
YESTERDAY
In 1891, Nikola Tesla gave a lecture for the members of the American Institute of Electrical Engineers in New York City, where he made a striking demonstration. In each hand he held a gas discharge tube, an early version of the modern fluorescent bulb. The tubes were not connected to any wires, but nonetheless they glowed brightly during his demonstration. Tesla explained to the awestruck attendees that the electricity was being transmitted through the air by the pair of metal sheets which sandwiched the stage. He went on to speculate how one might increase the scale of this effect to transmit wireless power and information over a broad area, perhaps even the entire Earth. As was often the case, Tesla's audience was engrossed but bewildered. (more)
TOMORROW
No more replacing batteries in wireless bugging devices, voice recorders and spycams!
Interesting side note... Leon Theremin invented a wireless bugging device that didn't need batteries back in the 1940's. (more)
TODAY
"We're going to transfer power without any kind of wires," says Dr Hall, now Chief Technology Officer at WiTricity, a startup developing wireless "resonance" technology.
"But, we're not actually putting electricity in the air. What we're doing is putting a magnetic field in the air." ...
In the house of the future, wire-free energy transfer could be as easy as wireless internet.
If all goes to WiTricity's plans, smartphones will charge in your pocket as you wander around, televisions will flicker with no wires attached, and electric cars will refuel while sitting on the driveway. (more)
YESTERDAY
In 1891, Nikola Tesla gave a lecture for the members of the American Institute of Electrical Engineers in New York City, where he made a striking demonstration. In each hand he held a gas discharge tube, an early version of the modern fluorescent bulb. The tubes were not connected to any wires, but nonetheless they glowed brightly during his demonstration. Tesla explained to the awestruck attendees that the electricity was being transmitted through the air by the pair of metal sheets which sandwiched the stage. He went on to speculate how one might increase the scale of this effect to transmit wireless power and information over a broad area, perhaps even the entire Earth. As was often the case, Tesla's audience was engrossed but bewildered. (more)
TOMORROW
No more replacing batteries in wireless bugging devices, voice recorders and spycams!
Interesting side note... Leon Theremin invented a wireless bugging device that didn't need batteries back in the 1940's. (more)
Tuesday, April 1, 2014
FCC Frees More Bandwidth - Wireless Eavesdropping Becomes Harder to Detect
The Federal Communications Commission approved measures on Monday that will free up more airwaves for Wi-Fi and wireless broadband...
Unlike the airwaves used for mobile phone traffic, which are licensed to a specific company, unlicensed spectrum can be used by anyone. Previous establishments of unlicensed airwaves led to innovations like garage-door openers, baby monitors, wireless microphones* and Wi-Fi networks. (more)
* Want to hear a Broadway play, live, for free? Park your butt near any Broadway theater at showtime. Bring along a scanning radio receiver and search for the wireless microphones. This trick will work in most other cities as well, as long as the wireless microphones are using frequency modulation (FM). Most still do.
The same trick works near Boardrooms, and hotel conference centers...
Unlike the airwaves used for mobile phone traffic, which are licensed to a specific company, unlicensed spectrum can be used by anyone. Previous establishments of unlicensed airwaves led to innovations like garage-door openers, baby monitors, wireless microphones* and Wi-Fi networks. (more)
* Want to hear a Broadway play, live, for free? Park your butt near any Broadway theater at showtime. Bring along a scanning radio receiver and search for the wireless microphones. This trick will work in most other cities as well, as long as the wireless microphones are using frequency modulation (FM). Most still do.
The same trick works near Boardrooms, and hotel conference centers...
Labels:
advice,
business,
eavesdropping,
espionage,
government,
Hack,
wireless
The Tale of the Eavesdropping Husbands, or Peek-A-Boo, SEC You
A man is being charged with violating a duty of trust by trading during a blackout window after he overheard work calls made by his wife.
“Spouses and other family members may gain access to highly confidential information about public companies as part of their relationship of trust,” said Jina L. Choi, director of the SEC’s San Francisco Regional Office. “In those circumstances, family members have a duty to protect and safeguard that information, not to trade on it.”
Tyrone Hawk of Los Gatos, Calif., overheard his wife, a finance manager at multinational computer technology corporation Oracle Corp speaking of her company’s plan to acquire Acme Packet Inc. Hawk also had a conversation with his wife in which she informed him that there was a blackout window for trading Oracle securities because it was in the process of acquiring another company, the SEC said.
In an unrelated case, the SEC alleges that Ching Hwa Chen of San Jose, Calif., profited from gleaning confidential information in mid-2012 that his wife’s employer, Informatica Corp., would miss its quarterly earnings target for the first time in 31 consecutive quarters. During a drive to vacation in Reno, Nev., Chen overheard business calls by his wife, who previously advised Chen not to trade in Informatica securities under any circumstances. (more)
P.S.
Hawk agreed to pay more than $300,000 to settle the SEC’s charges.
Chen agreed to pay approximately $280,000 to settle the SEC’s charges.
“Spouses and other family members may gain access to highly confidential information about public companies as part of their relationship of trust,” said Jina L. Choi, director of the SEC’s San Francisco Regional Office. “In those circumstances, family members have a duty to protect and safeguard that information, not to trade on it.”
Tyrone Hawk of Los Gatos, Calif., overheard his wife, a finance manager at multinational computer technology corporation Oracle Corp speaking of her company’s plan to acquire Acme Packet Inc. Hawk also had a conversation with his wife in which she informed him that there was a blackout window for trading Oracle securities because it was in the process of acquiring another company, the SEC said.
In an unrelated case, the SEC alleges that Ching Hwa Chen of San Jose, Calif., profited from gleaning confidential information in mid-2012 that his wife’s employer, Informatica Corp., would miss its quarterly earnings target for the first time in 31 consecutive quarters. During a drive to vacation in Reno, Nev., Chen overheard business calls by his wife, who previously advised Chen not to trade in Informatica securities under any circumstances. (more)
P.S.
Hawk agreed to pay more than $300,000 to settle the SEC’s charges.
Chen agreed to pay approximately $280,000 to settle the SEC’s charges.
Business Espionage: Invisibility & Examples of Tactics
There are three primary reasons that we don't hear more about corporate espionage:
- Because businesses often don’t realize they’ve been compromised.
- If they do find out, a public announcement would be counterproductive, eroding investor confidence.
- Finally, industrial espionage works both ways — companies may keep compromises quiet to preserve their own business intelligence gathering activities.
- Buying Trade Secrets
- Digging Up Dirt, Literally
- Employee Poaching
- Classified Ads
- Cyber Theft
Sunday, March 30, 2014
Murray Security Tip # 415 - iPhone - The Spy in Your Pocket
Did you know, your iPhone keeps track of where you go?
Check it out. Buried deep in your Settings menu is the proof. To see it, navigate this path:
You can turn it off and clear the history.
One more reason to use quality password protection.
~Kevin
Check it out. Buried deep in your Settings menu is the proof. To see it, navigate this path:
- Settings
- Privacy
- Location Services
- System Services
- Frequent Locations
- History
You can turn it off and clear the history.
One more reason to use quality password protection.
~Kevin
Business Espionage: BAT Spies Smoking Gun
Sensational recordings and documents show how South Africa’s largest JSE-listed company, cigarette giant British American Tobacco (BAT), appears to be committing “industrial espionage” on a grand scale, running a network of “agents” placed to spy inside rival organisations.
This evidence, uncovered as part of a year-long Business Times investigation, raises questions about the tobacco company’s ethics, and highlights shady dealings that are understood to have been reported to the authorities in South Africa and the UK, where it is headquartered.
One agent, who was placed in a senior position within BAT’s rivals, said that BAT’s “worldwide” practice of making secret payments to agents could be considered “international money-laundering”.
“They had a deal to pay me for industrial espionage, and may I say I’m not the only one in our little circle. There are [government intelligence agents] who have left the state, and gone to work for BAT,” said the agent.
The claim that BAT was involved in spying on rivals is corroborated by affidavits, audio and video recordings, copies of financial transactions and the accounts of five cigarette manufactures, a state informant, sources close to the South African Revenue Services and one of BAT’s senior agents...
Business Times has a recording of a conversation between a senior BAT official and one of its secret agents, in which the tobacco executive tells the agent not to “sell us out” by spilling the beans on the spying. (more)
This evidence, uncovered as part of a year-long Business Times investigation, raises questions about the tobacco company’s ethics, and highlights shady dealings that are understood to have been reported to the authorities in South Africa and the UK, where it is headquartered.
One agent, who was placed in a senior position within BAT’s rivals, said that BAT’s “worldwide” practice of making secret payments to agents could be considered “international money-laundering”.
“They had a deal to pay me for industrial espionage, and may I say I’m not the only one in our little circle. There are [government intelligence agents] who have left the state, and gone to work for BAT,” said the agent.
The claim that BAT was involved in spying on rivals is corroborated by affidavits, audio and video recordings, copies of financial transactions and the accounts of five cigarette manufactures, a state informant, sources close to the South African Revenue Services and one of BAT’s senior agents...
Business Times has a recording of a conversation between a senior BAT official and one of its secret agents, in which the tobacco executive tells the agent not to “sell us out” by spilling the beans on the spying. (more)
History - Nixon's Plumbers Tap More Pipes
Jeff Stein provides new information that suggests the Nixon White House may have bugged the Pentagon telephones of senior American military officials.
Stein managed to track down Dave Mann, a former member of the Pentagon’s Counterintelligence Force, who in 1971 stumbled upon a classified report claiming that listening bug signals had been detected emanating from offices in the Joint Chiefs of Staff. The signals had been picked up by a technical surveillance countermeasures (TSCM) team during a routine sweep of the Pentagon, in search of unauthorized interception devices.
Mann ran some tests to verify the TSCM team’s report, and discovered that the bug signals originated from the personal office telephone line of General William Westmoreland, who was then the US Army’s Chief of Staff. He also discovered that the telephone of his assistant had been compromised, as well as the telephone lines belonging to the US Army’s assistant secretary, its logistics director, and at least one general.
Mann’s personal conclusion was that the phone lines were most likely bugged with the cooperation of the Chesapeake and Potomac Telephone Company, which was at that the time considered an operational wing of the FBI, under Director J. Edgar Hoover...
Mann, who is now semi-retired from the military and lives in Tennessee, told Stein that “there was a lot —and I mean a lot— of pressure to prove GRAPPLE TRIP to be a fluke or a miswired telephone”. Which is precisely what happened: the investigation concluded that the bug signals were emitted due to “crossed wires in the telephone system”. (more)
 |
| Why is this man laughing? |
Mann ran some tests to verify the TSCM team’s report, and discovered that the bug signals originated from the personal office telephone line of General William Westmoreland, who was then the US Army’s Chief of Staff. He also discovered that the telephone of his assistant had been compromised, as well as the telephone lines belonging to the US Army’s assistant secretary, its logistics director, and at least one general.
Mann’s personal conclusion was that the phone lines were most likely bugged with the cooperation of the Chesapeake and Potomac Telephone Company, which was at that the time considered an operational wing of the FBI, under Director J. Edgar Hoover...
Mann, who is now semi-retired from the military and lives in Tennessee, told Stein that “there was a lot —and I mean a lot— of pressure to prove GRAPPLE TRIP to be a fluke or a miswired telephone”. Which is precisely what happened: the investigation concluded that the bug signals were emitted due to “crossed wires in the telephone system”. (more)
Saturday, March 29, 2014
NY Private Detective Firm Keeps Corporate Spies at Bay
Private investigators are most commonly associated with scorned spouses and cheap motels, but one PI firm based in New York is sniffing out scandal in a much more upscale (and more unusual) venue: the boardrooms of Fortune 500 companies.
Murray Associates, a counterespionage security company, has been de-bugging conference rooms and securing trading floors from the prying eyes of sneaky competitors since 1978. (more)
Murray Associates, a counterespionage security company, has been de-bugging conference rooms and securing trading floors from the prying eyes of sneaky competitors since 1978. (more)
10 Years Ago - 120 Coke Cans Spur a Military TSCM Alert
"Into the Wayback, Sherman."
THIS SECURITY BULLETIN APPLIES TO ALL SSCC SITES/FACILITIES/RESTRICTED
AREAS WHERE CLASSIFIED/SENSITIVE OPERATIONS ARE CONDUCTED
 The SSCC Security Office was recently informed that the Coca Cola Company has a summer game promotion running from 5/17 - 7/12/04 in all 50 states and the District of Columbia that has the capability to compromise classified information.
The SSCC Security Office was recently informed that the Coca Cola Company has a summer game promotion running from 5/17 - 7/12/04 in all 50 states and the District of Columbia that has the capability to compromise classified information.
The company has intermixed approximately 120 Coca-Cola cans that actually contain GPS locators equipped with a SIM card, keypad and GPS chip transponder so it functions as a cell phone and GPS locator. The cans are concealed in specially marked 12, 18, 20, or 24 can multi-packs of Coca-Cola Classic, Vanilla Coke, Cherry Coke and Caffeine Free Coke.
The hi-tech Coke "Unexpected Summer" promotion can has a button, microphone, and a tiny speaker on the outside of the can. Pressing the larger red button starts the game in process, thus activating the GPS signal and a cell phone used by the customer to call a special hotline. Consumers who find these cans, activate the technology, and call the hot line must agree to allow Coke "search teams" using the GPS tracker (accurate to within 50 feet), to surprise them anyplace, anytime within three weeks to deliver a valuable prize.
Until such time as this sales promotion ends and all 120 cans are accounted for, Coca-Cola packages should be opened and inspected before taking them into any area marked as a "Restricted Area" or where the location is sensitive or classified meetings/discussions, etc. are in progress or have the potential to occur at any time.
If one of these hi-tech game cans is found in snack bars, cafeterias, vending machines, etc. immediately report it to the Security Manager. While the can is your personal property, you must report obtaining it and immediately remove it from NSWC Crane work spaces.
As with any other two-way communications device, the hi-tech cans are not to be brought into any NSWC Crane classified facility under any circumstances.
While high technology is our livelihood, everyone must be alert to technology applications that can endanger National Security and the effectiveness of our support to the war fighters. Please report similar applications by marketers, etc. to the Security Office so the information can be widely disseminated. (source) (T-shirt)
THIS SECURITY BULLETIN APPLIES TO ALL SSCC SITES/FACILITIES/RESTRICTED
AREAS WHERE CLASSIFIED/SENSITIVE OPERATIONS ARE CONDUCTED
 The SSCC Security Office was recently informed that the Coca Cola Company has a summer game promotion running from 5/17 - 7/12/04 in all 50 states and the District of Columbia that has the capability to compromise classified information.
The SSCC Security Office was recently informed that the Coca Cola Company has a summer game promotion running from 5/17 - 7/12/04 in all 50 states and the District of Columbia that has the capability to compromise classified information. The company has intermixed approximately 120 Coca-Cola cans that actually contain GPS locators equipped with a SIM card, keypad and GPS chip transponder so it functions as a cell phone and GPS locator. The cans are concealed in specially marked 12, 18, 20, or 24 can multi-packs of Coca-Cola Classic, Vanilla Coke, Cherry Coke and Caffeine Free Coke.
The hi-tech Coke "Unexpected Summer" promotion can has a button, microphone, and a tiny speaker on the outside of the can. Pressing the larger red button starts the game in process, thus activating the GPS signal and a cell phone used by the customer to call a special hotline. Consumers who find these cans, activate the technology, and call the hot line must agree to allow Coke "search teams" using the GPS tracker (accurate to within 50 feet), to surprise them anyplace, anytime within three weeks to deliver a valuable prize.
Until such time as this sales promotion ends and all 120 cans are accounted for, Coca-Cola packages should be opened and inspected before taking them into any area marked as a "Restricted Area" or where the location is sensitive or classified meetings/discussions, etc. are in progress or have the potential to occur at any time.
If one of these hi-tech game cans is found in snack bars, cafeterias, vending machines, etc. immediately report it to the Security Manager. While the can is your personal property, you must report obtaining it and immediately remove it from NSWC Crane work spaces.
As with any other two-way communications device, the hi-tech cans are not to be brought into any NSWC Crane classified facility under any circumstances.
While high technology is our livelihood, everyone must be alert to technology applications that can endanger National Security and the effectiveness of our support to the war fighters. Please report similar applications by marketers, etc. to the Security Office so the information can be widely disseminated. (source) (T-shirt)
Labels:
cell phone,
government,
GPS,
Hack,
historical,
TSCM,
weird
Friday, March 28, 2014
Over 50% of Android Users Don't Use Passwords, Pins or Meaningful Swipes
An ad hoc survey conducted by Google's anti-abuse research lead Elie Bursztein has shown that over half of Android users don't lock their phones in any meaningful way.
After polling 1,500 users, he discovered that 52 percent of those users "open" their device with a simple slide or gesture, 25.5 percent have opted to locking their phones with drawing a pattern on a grid, and 15.1 percent are using a PIN.
Only 3.3 percent have opted for using a password, 2.3 percent for the option where the phone can recognize their face, and 1.8 percent are using other, 3rd party forms of authentication...

...no security is perfect. Both lock patterns and PIN codes can be vulnerable to smudge attacks, as a 2010 Usenix paper illustrates. So whether you use a PIN or a pattern you should change it from time to time. You might also want to go to your phone’s options screen and disable the display of the pattern so people can’t “shouldersurf” it. (more)
 |
| Click to enlarge. |
After polling 1,500 users, he discovered that 52 percent of those users "open" their device with a simple slide or gesture, 25.5 percent have opted to locking their phones with drawing a pattern on a grid, and 15.1 percent are using a PIN.
Only 3.3 percent have opted for using a password, 2.3 percent for the option where the phone can recognize their face, and 1.8 percent are using other, 3rd party forms of authentication...

...no security is perfect. Both lock patterns and PIN codes can be vulnerable to smudge attacks, as a 2010 Usenix paper illustrates. So whether you use a PIN or a pattern you should change it from time to time. You might also want to go to your phone’s options screen and disable the display of the pattern so people can’t “shouldersurf” it. (more)
Google Explains Search Warrant Requests - for ages 2 and older
P.S. Word on the street... the cow is a spy.
Thursday, March 27, 2014
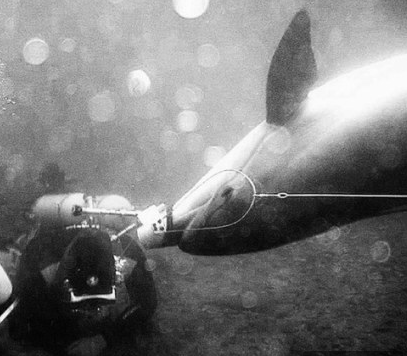
From our, "You can't make this spy stuff up" file. - Spy Dolphins Defect
Ukraine’s secret unit of spy DOLPHINS that can plant bombs and attack divers with guns have defected to Russia.
Last year three of five spy dolphins went absent without leave in the Black Sea - apparently in search of love, but returned to their duties shortly afterwards.
Yury Plyachenko, a former Soviet naval anti-sabotage officer, explained that this was something that had to be taken into account in working with the 007 mammals.
‘If a male dolphin saw a female dolphin during the mating season, then he would immediately set off after her. But they come back in a week or so.’ (more)
- The Ukraine Army has been using dolphins and seals since the 70s
- After the fall of the USSR, the 'dolphin spies' remained in the Ukraine
- The dolphins have been trained to hunt for mines and plant bombs
- They can also attack divers with knives or pistols attached to their heads
- Now, military dolphins in Crimea will be transferred to the Russian Navy
Last year three of five spy dolphins went absent without leave in the Black Sea - apparently in search of love, but returned to their duties shortly afterwards.
Yury Plyachenko, a former Soviet naval anti-sabotage officer, explained that this was something that had to be taken into account in working with the 007 mammals.
‘If a male dolphin saw a female dolphin during the mating season, then he would immediately set off after her. But they come back in a week or so.’ (more)
In Washington, DC this Spring? Need Something Cool to Do?
Check out The International Spy Museum...
Subscribe to:
Comments (Atom)