Estonia - Old Town Tallinn in Estonia feels like it should be on top of a wedding cake, the old city walls, church steeples, narrow cobblestone streets, and pastel colors putting forth a true Medievil vibe...
There are many hotels located within the Old Town walls to choose from, but if you want a true taste of KGB history during your visit, consider the Sokos Hotel Viru just outside Old Town. Opened in 1972, it's the largest hotel in Estonia with over 500 rooms, and during Soviet occupation, the KGB had an office on the top floor (the 23rd floor, which did not have a button on the elevator).
They always denied their presence, but they bugged the guests, literally.
The KGB tapped 60 rooms, installed mics in the plates in the dining room, instructed elevator attendants to keep track of guests’ comings and goings, and drilled holes through hotel room walls to take photographs and keep a watch on suspected guests, which included visiting journalists and Finnish visitors who would hold meet and greets with their families in the lobby (the visiting Fins weren’t allowed to visit their family in their homes under Soviet Law). Even if you don’t stay the night, be sure to pop in for a drink and to check out the museum that allows you to tour the former KGB offices. (more)
Tuesday, April 30, 2013
Sunday, April 28, 2013
Spybuster Tip # 523: Twitter Password Security Test
WARNING
The link below is a clever gag.
Similar sites are password collection scams.
If you take the test on any of them, don't enter real information.
http://www.ismytwitterpasswordsecure.com/
The link below is a clever gag.
Similar sites are password collection scams.
If you take the test on any of them, don't enter real information.
http://www.ismytwitterpasswordsecure.com/
Saturday, April 27, 2013
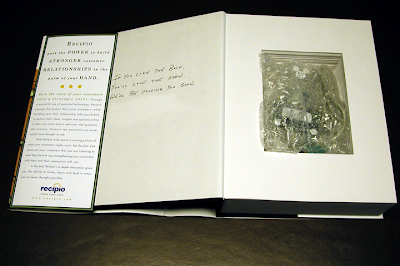
FutureWatch: Trojan Horse Wi-Fi's and More - In Your Mail
This promotion is legitimate.
But, imagine this small, inexpensive technology as an espionage tool...
Microsoft is putting in real WiFi hardware hotspots inside some copies of the latest issue of Forbes magazine. The unique Office 365 promotion was revealed in a post on the Slickdeals.net message board. The WiFi router, when activated, offers 15 days of free WiFi service via T-Mobile's network on up to five devices at once.
In any case, if you get one of these Forbes magazine ads, keep in mind that the router still needs to be charged; it apparently lasts up to three hours on a single charge. (more)
BTW, for your techie types, it uses a Mediatek chip (RT5350), "The world's smallest wireless router-on-a-chip."
Hiding electronic gadgets in the mail is not a new idea.
Many years ago, a company hollowed out a book, planted a computer mouse inside, and mailed it to top executives.
We detected one of these books during a weekend sweep. It was on an executive's desk, in the unopened mail.
Was it a bug?
Was it a bomb?
No, just a insensitive marketing gag.
Apparently, the company is no longer in business.
FutureWatch: This will happen again, but next time it might be a bug ...or, a bomb.
Regularly scheduled TSCM inspections can find these things lurking in your office.
But, imagine this small, inexpensive technology as an espionage tool...
Microsoft is putting in real WiFi hardware hotspots inside some copies of the latest issue of Forbes magazine. The unique Office 365 promotion was revealed in a post on the Slickdeals.net message board. The WiFi router, when activated, offers 15 days of free WiFi service via T-Mobile's network on up to five devices at once.
In any case, if you get one of these Forbes magazine ads, keep in mind that the router still needs to be charged; it apparently lasts up to three hours on a single charge. (more)
BTW, for your techie types, it uses a Mediatek chip (RT5350), "The world's smallest wireless router-on-a-chip."
Hiding electronic gadgets in the mail is not a new idea.
Many years ago, a company hollowed out a book, planted a computer mouse inside, and mailed it to top executives.
We detected one of these books during a weekend sweep. It was on an executive's desk, in the unopened mail.
Was it a bug?
Was it a bomb?
No, just a insensitive marketing gag.
Apparently, the company is no longer in business.
FutureWatch: This will happen again, but next time it might be a bug ...or, a bomb.
Regularly scheduled TSCM inspections can find these things lurking in your office.
Labels:
advice,
book,
business,
cautionary tale,
computer,
espionage,
find,
FutureWatch,
Hack,
marketing,
TSCM,
weird
Friday, April 26, 2013
How to Bug an Entire Country - Drop Poop & Rocks
During the Cold War, both sides liberally used the “bug”--the remote listening device--to surreptitiously get wind of what the other side was up to by listening in on a room, a building, or, in the case of East Berlin, an entire city.
But in America’s cooling war in Afghanistan, U.S. forces may undertake what could be the biggest bugging operation of all time, planting sensors all over the entire country that could feed the U.S. military intelligence from inside that country for the next two decades. It’s the rough equivalent of bugging an entire country.
The palm-sized devices at the U.S. military’s disposal aren’t listening devices per se, but they would detect anyone moving nearby and report the movement back to an intelligence outpost, letting special operators know when a remote mountain pass or a known smuggling trail is being utilized. Some of the sensors could be buried, others disguised as rocks or other geological artifacts.
The point is, they would be littered all across Afghanistan’s landscape, a lingering legacy of a decade-long conflict that would last 20 years more. (more)
 |
| Click to enlarge |
The palm-sized devices at the U.S. military’s disposal aren’t listening devices per se, but they would detect anyone moving nearby and report the movement back to an intelligence outpost, letting special operators know when a remote mountain pass or a known smuggling trail is being utilized. Some of the sensors could be buried, others disguised as rocks or other geological artifacts.
 |
| CIA monkey poop sensor - Vietnam era. |
Labels:
CIA,
detection,
government,
Hack,
historical,
spybot,
surveillance,
tracking,
weird
Interesting Security Technologies - Sunpass Bug & Butterfly Authentication
Doug Blakeway, President & CEO, Nanotech Security Corp., reveals new surveillance technologies in the company's Annual Report...
(from their subsidiary) "The CTR-1300 JOEY, a disguised Variable Power Audio Transmitter Utilizing a new LiPo internal battery and incorporated into the Garage Door Opener, EZ Pass, and Sunpass as disguises."
and, the latest in anti-counterfeiting technology...
"Nanotech is developing what it sees as a highly sophisticated and commercially viable nanotechnology for use in anti-counterfeiting as well as product and document authentication. It will potentially be used to authenticate a huge range of items, including currency, legal documents and commercial products.
The specialized optical features are comprised of arrays of hundreds of millions of nano-holes–implanted directly onto various substrates and which emit unique light signatures that we believe cannot be reproduced by a counterfeiter.
KolourOptics® is the trade name for this revolutionary authentication feature which produces nano-scale surface structures similar to those found on the wings of the iridescent blue Morpho Butterfly.
The features can be directly applied to banknotes and other valuable documents and products and will produce light signatures are both “overt” (visible to the naked eye) and some that are “covert” (machine readable only)." (more)
(from their subsidiary) "The CTR-1300 JOEY, a disguised Variable Power Audio Transmitter Utilizing a new LiPo internal battery and incorporated into the Garage Door Opener, EZ Pass, and Sunpass as disguises."
and, the latest in anti-counterfeiting technology...
 |
| Click to enlarge. |
The specialized optical features are comprised of arrays of hundreds of millions of nano-holes–implanted directly onto various substrates and which emit unique light signatures that we believe cannot be reproduced by a counterfeiter.
KolourOptics® is the trade name for this revolutionary authentication feature which produces nano-scale surface structures similar to those found on the wings of the iridescent blue Morpho Butterfly.
The features can be directly applied to banknotes and other valuable documents and products and will produce light signatures are both “overt” (visible to the naked eye) and some that are “covert” (machine readable only)." (more)
Spouse Spying Increase Seen By 92% of Divorce Attorneys
In this new age of technology, spy gadgets are no longer just for actors in James Bond movies. Studies show more spouses are using spy equipment to catch the other red-handed.
The American Academy of Matrimonial Lawyers says in the past three years 92 percent of divorce attorneys saw an increase in evidence from text messages, emails and GPS trackers. In fact in 2011, a Minnesota man was thrown in jail for installing a GPS on his wife's car as he searched for proof she was cheating.
The American Academy of Matrimonial Lawyers says in the past three years 92 percent of divorce attorneys saw an increase in evidence from text messages, emails and GPS trackers. In fact in 2011, a Minnesota man was thrown in jail for installing a GPS on his wife's car as he searched for proof she was cheating.
Labels:
amateur,
eavesdropping,
historical,
lawsuit,
mores,
poll,
privacy,
recording,
spycam,
spyware,
surveillance,
survey,
tracking,
wiretapping
Thursday, April 25, 2013
Latest in Government Work Clothes - Immunity Suits
...documents show that the Justice Department secretly agreed to provide AT&T and other participating providers with so-called “2511 letters” that granted them immunity for activity that might otherwise have violated federal wiretapping laws. (more)
Spy Stories Behind "Peggy Sue" and "Winnie the Pooh"
 U.S. country star Jerry Naylor revealed he used his international fame as cover to work as a secret agent for the CIA... Naylor, 74, who replaced Buddy Holly in the Crickets, says he was recruited on more than 100 occasions to spy for America under his guise as a touring singer. (more)
U.S. country star Jerry Naylor revealed he used his international fame as cover to work as a secret agent for the CIA... Naylor, 74, who replaced Buddy Holly in the Crickets, says he was recruited on more than 100 occasions to spy for America under his guise as a touring singer. (more) The man who created Winnie the Pooh was a First World War spy, top secret files reveal. The papers — rescued from a skip — prove AA Milne worked for a covert arm of military intelligence in a propaganda war against the Germans. They uncover the secret double life of the man behind Tigger, Christopher Robin and Piglet — and should have been burned. (more)
The man who created Winnie the Pooh was a First World War spy, top secret files reveal. The papers — rescued from a skip — prove AA Milne worked for a covert arm of military intelligence in a propaganda war against the Germans. They uncover the secret double life of the man behind Tigger, Christopher Robin and Piglet — and should have been burned. (more)
Verizon's Tilt-Shift-Focus on Espionage
Ninety-six percent of cyber espionage cases targeting intellectual property and business trade secrets were attributed to “threat actors in China,” while the remaining four percent were unknown, according to the “2013 Data Breach Investigations Report," which is issued by Verizon, a large U.S. telecom firm...
“Verizon doesn't explain how they determine that an event is state-sponsored, nor how they distinguish between legitimate attacks originating from China and those which use compromised servers in Chinese IP space,” said Jeffrey Carr, CEO of Taia Group, a cyber-security firm. “Hence, any conclusion that they try to draw about the government of China has to be taken with a great degree of skepticism.”
Carr said he believes a lot of the espionage originating in China could “actually be the work of non-state actors working in the Chinese IP space.” (more)
 Keep in mind this report is from a telecommunications company. It is a tilt-shift-focus photo. The center of attention is their product – data-motion. Non-IT methods of espionage are out of focus.
Keep in mind this report is from a telecommunications company. It is a tilt-shift-focus photo. The center of attention is their product – data-motion. Non-IT methods of espionage are out of focus.
The result is a distorted reality field with micro-bickering over "who" is to blame, instead of what can be done about it.
Wake up. Pockets are being picked. "Who" doesn't matter. Keeping your intellectual wallet safe matters.
Successful counterespionage requires a clear, sharp, holistic vision. Beware the tilt-shift folks who focus on IT alone. They miss all the end runs. Budget for a 360º lens. ~Kevin
“Verizon doesn't explain how they determine that an event is state-sponsored, nor how they distinguish between legitimate attacks originating from China and those which use compromised servers in Chinese IP space,” said Jeffrey Carr, CEO of Taia Group, a cyber-security firm. “Hence, any conclusion that they try to draw about the government of China has to be taken with a great degree of skepticism.”
Carr said he believes a lot of the espionage originating in China could “actually be the work of non-state actors working in the Chinese IP space.” (more)
 Keep in mind this report is from a telecommunications company. It is a tilt-shift-focus photo. The center of attention is their product – data-motion. Non-IT methods of espionage are out of focus.
Keep in mind this report is from a telecommunications company. It is a tilt-shift-focus photo. The center of attention is their product – data-motion. Non-IT methods of espionage are out of focus. The result is a distorted reality field with micro-bickering over "who" is to blame, instead of what can be done about it.
Wake up. Pockets are being picked. "Who" doesn't matter. Keeping your intellectual wallet safe matters.
Successful counterespionage requires a clear, sharp, holistic vision. Beware the tilt-shift folks who focus on IT alone. They miss all the end runs. Budget for a 360º lens. ~Kevin
New Book - "Eavesdropping, Surveillance and Espionage"
New Book
"...examines the escalating security and privacy threats from spy cameras, audio bugs, telephone bugs, GPS trackers, GSM listening devices, surveillance software, smart-phone compromises and other high-tech technologies that are actively marketed to civilians. Modern security professionals must grasp the magnitude of these emerging threats, how they are identified and the counter-measures by which they are neutralized."
The press release explains...
"Eavesdropping, Surveillance And Espionage: Threats, Techniques and Countermeasures is a comprehensive introduction to TSCM specifically for law enforcement, private investigators, homeland security, key military personnel, foreign service and diplomatic staff, intelligence operatives, private security contractors, TSA, security advisors and other security professionals in the private and public sectors.
Authored by Norbert Zaenglein, author of Disk Detective, Secret Software and the Covert Bug Book, the new TSCM book fills a much needed gap in security awareness related to civilian surveillance capabilities, a development that impacts military, government, diplomatic venues, homeland security, corporations, businesses and the general public.
The essential new security manual explains how mass production of sophisticated surveillance technology pattered after law-enforcement and intelligence-grade spy devices has marshaled the once secretive spy trade into civilian circles with far-reaching implications and consequences." (preview)
Note: Only available at http://www.modernprivacy.info/
"...examines the escalating security and privacy threats from spy cameras, audio bugs, telephone bugs, GPS trackers, GSM listening devices, surveillance software, smart-phone compromises and other high-tech technologies that are actively marketed to civilians. Modern security professionals must grasp the magnitude of these emerging threats, how they are identified and the counter-measures by which they are neutralized."
The press release explains...
"Eavesdropping, Surveillance And Espionage: Threats, Techniques and Countermeasures is a comprehensive introduction to TSCM specifically for law enforcement, private investigators, homeland security, key military personnel, foreign service and diplomatic staff, intelligence operatives, private security contractors, TSA, security advisors and other security professionals in the private and public sectors.
Authored by Norbert Zaenglein, author of Disk Detective, Secret Software and the Covert Bug Book, the new TSCM book fills a much needed gap in security awareness related to civilian surveillance capabilities, a development that impacts military, government, diplomatic venues, homeland security, corporations, businesses and the general public.
The essential new security manual explains how mass production of sophisticated surveillance technology pattered after law-enforcement and intelligence-grade spy devices has marshaled the once secretive spy trade into civilian circles with far-reaching implications and consequences." (preview)
Note: Only available at http://www.modernprivacy.info/
Monday, April 22, 2013
Detecting and Preventing Eavesdropping - U.S. Government Advice
(A long, but worthwhile read.)
One of the most common indicators of eavesdropping is that other people seem to know something they shouldn’t know. If you learn that an activity, plan, or meeting that should be secret is known to an adversary or competitor, you should ask yourself how they might have learned that.
An eavesdropper will often use some pretext to gain physical access to your office or home. It is easy for an outsider to gain access to many office buildings by impersonating a technician checking on such things as the air conditioning or heating. The only props needed are a workman’s uniform, hard hat, clipboard with some forms, and a belt full of tools. If challenged, the imposter might threaten not to come back for three weeks because he is so busy. In one version of this technique, the eavesdropper actually causes a problem and then shows up unrequested to fix it. In other words, you must verify that anyone performing work in or around your office was actually requested and is authorized to do this work. If a worker shows up without being asked, this suggests an attempted eavesdropping operation and should be reported immediately to your security office. Even when the work is requested, outside service personnel entering rooms containing sensitive information should always be accompanied and monitored.
Gifts are another means of infiltrating a bug into a target office. Be a little suspicious if you receive from one of your contacts a gift of something that might normally be kept in your office -- for example, a framed picture for the wall or any sort of electronic device. Electronic devices are especially suspicious as they provide an available power supply, have space for concealing a mike and transmitter, and it is often difficult to distinguish the bug from other electronic parts. Have any gift checked by a technical countermeasures specialist before keeping it in a room where sensitive discussions are held.
Unusual sounds can be a tip off that something is amiss. Strange sounds or volume changes on your phone line while you are talking can be caused by eavesdropping. However, they can also be caused by many other things and are relatively common, so this is not a significant indicator unless it happens repeatedly. On the other hand, if you ever hear sounds coming from your phone while it is hung up, this is significant and definitely should be investigated. If your television, radio, or other electrical appliance in a sensitive area experiences strange interference from some other electronic device, this should also be investigated if it happens repeatedly.
Illegal entry to your office or home to install an eavesdropping device sometimes leaves telltale signs, especially if done by an amateur. Evidence of improper entry with nothing being taken is suspicious. Installing an eavesdropping device sometimes involves moving ceiling tiles, electrical outlets, switches, light fixtures, or drilling a pinhole opening in the wall or ceiling of the target room (drilling in from the other side of the wall or ceiling). This can leave a small bit of debris, especially white dry-wall dust that should not be cleaned up. It should be reported to the security office.
In summary, protection against the installation of eavesdropping devices requires:
What to Do if You Suspect
You Have Been Bugged
If you suspect you are bugged, do not discuss your suspicions with others unless they have a real need to know. Above all, do not discuss your suspicions in a room that might be bugged. Do not deviate from the normal pattern of conversation in the room. Advise your security officer promptly, but do not do it by phone. The bug may be in the telephone instrument. Do it in person, and discuss the problem in an area that you are confident is secure.
These security measures are important to ensure that the perpetrator does not become aware of your suspicions. A perpetrator who becomes aware you are suspicious will very likely take steps to make it more difficult to find the device. He may remove the device or switch it off remotely.
A Technical Security Countermeasures (TSCM) survey, also known as a "sweep," is a service provided by highly qualified personnel to detect the presence of technical surveillance devices and hazards and to identify technical security weaknesses that could facilitate a technical penetration of the surveyed facility. It consists of several parts.
Contact me for additional information on conducting a professional technical information security survey, which is more through than the standard TSCM sweep. ~Kevin
(original government post)
Detecting and Preventing Eavesdropping
Any indication that an adversary or competitor is using illegal means to collect information should alert you to the possibility, at least, that listening devices might be planted in your office or home. There are a number of specific warning signs that you may be the target of eavesdropping. Of course, if eavesdropping is done by a professional, and done correctly, you may not see any of these signs.One of the most common indicators of eavesdropping is that other people seem to know something they shouldn’t know. If you learn that an activity, plan, or meeting that should be secret is known to an adversary or competitor, you should ask yourself how they might have learned that.
An eavesdropper will often use some pretext to gain physical access to your office or home. It is easy for an outsider to gain access to many office buildings by impersonating a technician checking on such things as the air conditioning or heating. The only props needed are a workman’s uniform, hard hat, clipboard with some forms, and a belt full of tools. If challenged, the imposter might threaten not to come back for three weeks because he is so busy. In one version of this technique, the eavesdropper actually causes a problem and then shows up unrequested to fix it. In other words, you must verify that anyone performing work in or around your office was actually requested and is authorized to do this work. If a worker shows up without being asked, this suggests an attempted eavesdropping operation and should be reported immediately to your security office. Even when the work is requested, outside service personnel entering rooms containing sensitive information should always be accompanied and monitored.
Gifts are another means of infiltrating a bug into a target office. Be a little suspicious if you receive from one of your contacts a gift of something that might normally be kept in your office -- for example, a framed picture for the wall or any sort of electronic device. Electronic devices are especially suspicious as they provide an available power supply, have space for concealing a mike and transmitter, and it is often difficult to distinguish the bug from other electronic parts. Have any gift checked by a technical countermeasures specialist before keeping it in a room where sensitive discussions are held.
Unusual sounds can be a tip off that something is amiss. Strange sounds or volume changes on your phone line while you are talking can be caused by eavesdropping. However, they can also be caused by many other things and are relatively common, so this is not a significant indicator unless it happens repeatedly. On the other hand, if you ever hear sounds coming from your phone while it is hung up, this is significant and definitely should be investigated. If your television, radio, or other electrical appliance in a sensitive area experiences strange interference from some other electronic device, this should also be investigated if it happens repeatedly.
Illegal entry to your office or home to install an eavesdropping device sometimes leaves telltale signs, especially if done by an amateur. Evidence of improper entry with nothing being taken is suspicious. Installing an eavesdropping device sometimes involves moving ceiling tiles, electrical outlets, switches, light fixtures, or drilling a pinhole opening in the wall or ceiling of the target room (drilling in from the other side of the wall or ceiling). This can leave a small bit of debris, especially white dry-wall dust that should not be cleaned up. It should be reported to the security office.
In summary, protection against the installation of eavesdropping devices requires:
- Alert employees.
- Round the clock control over physical access by outsiders to the area to be protected.
- Continuous supervision/observation of all service personnel allowed into the area for repairs or to make alterations.
- Thorough inspection by a qualified technical countermeasures specialist of all new furnishings, decorations, or equipment brought into the area.
What to Do if You Suspect
You Have Been Bugged
If you suspect you are bugged, do not discuss your suspicions with others unless they have a real need to know. Above all, do not discuss your suspicions in a room that might be bugged. Do not deviate from the normal pattern of conversation in the room. Advise your security officer promptly, but do not do it by phone. The bug may be in the telephone instrument. Do it in person, and discuss the problem in an area that you are confident is secure.
These security measures are important to ensure that the perpetrator does not become aware of your suspicions. A perpetrator who becomes aware you are suspicious will very likely take steps to make it more difficult to find the device. He may remove the device or switch it off remotely.
- Never try to find a bug or wiretap yourself. What’s the point? If you are suspicious enough to look, you already know you should not have any sensitive conversation in that room. If there is a bug there, do-it-yourself approaches probably will not find it. If you look and don’t find it, that certainly shouldn’t give you any sense of confidence that you can speak freely in that room. Don’t be misled by what you see on television, in the movies, or in spy-shop catalogs. Detecting bugs is difficult even for the professionals who specialize in that work.
A Technical Security Countermeasures (TSCM) survey, also known as a "sweep," is a service provided by highly qualified personnel to detect the presence of technical surveillance devices and hazards and to identify technical security weaknesses that could facilitate a technical penetration of the surveyed facility. It consists of several parts.
- An electronic search of the radio frequency (RF) spectrum to detect any unauthorized emanations from the area being examined.
- An electronically enhanced search of walls, ceilings, floors, furnishings, and accessories to look for clandestine microphones, recorders, or transmitters, both active and quiescent.
- A physical examination of interior and exterior areas such as the space above false ceilings and heating, air conditioning, plumbing, and ventilation systems to search for physical evidence of eavesdropping.
- Identification of physical security weaknesses that could be exploited by an eavesdropper to gain access to place technical surveillance equipment in the target area.
Contact me for additional information on conducting a professional technical information security survey, which is more through than the standard TSCM sweep. ~Kevin
(original government post)
Saturday, April 20, 2013
Interesting Question About Jamming Bugs & SpyCams
Q. "Looking for a bug jammer that will block out all bugs video or audio near my doorway looking at the rj4000 from the bug jammer store wondering if what they say is true they claim it will block 1 g bugs and 1.2 g bugs with a jamming frequency between 900 to 1000 mhz and 1100 mhz to 1300mhz for bugs"
A. Good thing you asked.
You really don't want to solve your problem this way.
Here's why...
• Jamming is illegal in the U.S. http://www.fcc.gov/encyclopedia/jammer-enforcement
"seizure of unlawful equipment" " subjects the operator to possible fines, imprisonment, or both"
• Your imported purchase runs the risk of being confiscated by Customs before it even reaches you.
• The RF jammer RJ4000 ALSO jams 2.4 GHz Wi-Fi and 1.5 GHz GPS signals. Your neighbors will complain.
But, yes, it will probably do what they say, assuming the bug/spycam transmitter is less powerful than the jammer's transmitter.
Best advice: Think of an alternate way to solve your concerns. ~Kevin
A. Good thing you asked.
You really don't want to solve your problem this way.
Here's why...
• Jamming is illegal in the U.S. http://www.fcc.gov/encyclopedia/jammer-enforcement
"seizure of unlawful equipment" " subjects the operator to possible fines, imprisonment, or both"
• Your imported purchase runs the risk of being confiscated by Customs before it even reaches you.
• The RF jammer RJ4000 ALSO jams 2.4 GHz Wi-Fi and 1.5 GHz GPS signals. Your neighbors will complain.
 |
| Estimated area of noticeable interference. Actual jamming area is less. |
Best advice: Think of an alternate way to solve your concerns. ~Kevin
Friday, April 19, 2013
Sand Sized Gyroscopes to Track You Anywhere
Mini-gyroscopes developed to guide smartphones and medical equipment...
Prof. Koby Scheuer of Tel Aviv University`s School of Physical Engineering is now scaling down this crucial sensing technology for use in smartphones, medical equipment and more futuristic technologies.
 Working in collaboration with Israel`s Department of Defense, Prof. Scheuer and his team of researchers have developed nano-sized optical gyroscopes that can fit on the head of a pin — and, more usefully, on an average-sized computer chip — without compromising the device`s sensitivity... Measuring a millimeter by a millimeter (0.04 inches by 0.04 inches), about the size of a grain of sand, the device can be built onto a larger chip that also contains other necessary electronics...
Working in collaboration with Israel`s Department of Defense, Prof. Scheuer and his team of researchers have developed nano-sized optical gyroscopes that can fit on the head of a pin — and, more usefully, on an average-sized computer chip — without compromising the device`s sensitivity... Measuring a millimeter by a millimeter (0.04 inches by 0.04 inches), about the size of a grain of sand, the device can be built onto a larger chip that also contains other necessary electronics...
Nano-gyroscopes integrated into common cellphones could provide a tracking function beyond the capabilities of existing GPS systems. "If you find yourself in a place without reception, you would be able to track your exact position without the GPS signal," he says.
There are benefits to medical science as well... (more)
Prof. Koby Scheuer of Tel Aviv University`s School of Physical Engineering is now scaling down this crucial sensing technology for use in smartphones, medical equipment and more futuristic technologies.
 Working in collaboration with Israel`s Department of Defense, Prof. Scheuer and his team of researchers have developed nano-sized optical gyroscopes that can fit on the head of a pin — and, more usefully, on an average-sized computer chip — without compromising the device`s sensitivity... Measuring a millimeter by a millimeter (0.04 inches by 0.04 inches), about the size of a grain of sand, the device can be built onto a larger chip that also contains other necessary electronics...
Working in collaboration with Israel`s Department of Defense, Prof. Scheuer and his team of researchers have developed nano-sized optical gyroscopes that can fit on the head of a pin — and, more usefully, on an average-sized computer chip — without compromising the device`s sensitivity... Measuring a millimeter by a millimeter (0.04 inches by 0.04 inches), about the size of a grain of sand, the device can be built onto a larger chip that also contains other necessary electronics...Nano-gyroscopes integrated into common cellphones could provide a tracking function beyond the capabilities of existing GPS systems. "If you find yourself in a place without reception, you would be able to track your exact position without the GPS signal," he says.
There are benefits to medical science as well... (more)
Pentagon’s Spies Pimp Their Phones
The Pentagon has big plans for its spy agency. But first it’s going to upgrade its secret agents’ cellphones.
 That’s the gist of a recent request for information from the cryptic Virginia Contracting Activity (or VACA), the public face for the Defense Intelligence Agency’s secretive contract business. According to the request, the DIA is looking for a company with the “ability to work and store classified information at the SECRET Collateral Level” to design custom “cellular phone point-to-point communication systems.” In other words, a private communications link. (more)
That’s the gist of a recent request for information from the cryptic Virginia Contracting Activity (or VACA), the public face for the Defense Intelligence Agency’s secretive contract business. According to the request, the DIA is looking for a company with the “ability to work and store classified information at the SECRET Collateral Level” to design custom “cellular phone point-to-point communication systems.” In other words, a private communications link. (more)
 That’s the gist of a recent request for information from the cryptic Virginia Contracting Activity (or VACA), the public face for the Defense Intelligence Agency’s secretive contract business. According to the request, the DIA is looking for a company with the “ability to work and store classified information at the SECRET Collateral Level” to design custom “cellular phone point-to-point communication systems.” In other words, a private communications link. (more)
That’s the gist of a recent request for information from the cryptic Virginia Contracting Activity (or VACA), the public face for the Defense Intelligence Agency’s secretive contract business. According to the request, the DIA is looking for a company with the “ability to work and store classified information at the SECRET Collateral Level” to design custom “cellular phone point-to-point communication systems.” In other words, a private communications link. (more)
Top Wi-Fi Routers Easy to Hack, Says Study
The most popular home wireless routers are easily hacked and there's little you can do to stop it, says a new study by research firm Independent Security Evaluators.
Thirteen popular routers were tested and found vulnerable to hacks in a new study by research firm Independent Security Evaluators.
The Wi-Fi router you use to broadcast a private wireless Internet signal in your home or office is not only easy to hack, says a report released today, but the best way to protect yourself is out of your hands.
The report, written by research firm Independent Security Evaluators of Baltimore, found that 13 of the most popular off-the-shelf wireless routers could be exploited by a "moderately skilled adversary with LAN or WLAN access." It also concludes that your best bet for safer Wi-Fi depends on router vendors upping their game. All 13 routers evaluated can be taken over from the local network, with four of those requiring no active management session. Eleven of the 13 can be taken over from a Wide-Area Network (WAN) such as a wireless network, with two of those requiring no active management session. (more)
How to Hack-proof Your Wireless Router
(Maybe not hack-proof but at least hack-resistant.)
Thirteen popular routers were tested and found vulnerable to hacks in a new study by research firm Independent Security Evaluators.
The Wi-Fi router you use to broadcast a private wireless Internet signal in your home or office is not only easy to hack, says a report released today, but the best way to protect yourself is out of your hands.
 |
| Click to enlarge. |
How to Hack-proof Your Wireless Router
(Maybe not hack-proof but at least hack-resistant.)
DoD Inspector General v. Army Commercial Mobile Devices (CMD)
There are lessons for your organization in this report.
Insert your organization's name where you see the word "Army".
"The Army did not implement an effective cybersecurity program for commercial mobiles (sic) devices. If devices remain unsecure, malicious activities could disrupt Army networks and compromise sensitive DoD information." (full report)
Insert your organization's name where you see the word "Army".
 |
| Click to enlarge. |
Wednesday, April 17, 2013
If you travel with a cell phone, tablet and/or laptop...
...this should interest you...
35,000. That’s how many business travelers depart the United States every day. With them goes over 40,000 cell phones, more than 50,000 laptops, and nearly 500,000 pages of business documents holding privileged information. When you travel abroad, your company is at risk.
Among Enemies tells you how to protect yourself.
Luke Bencie has traveled to more than 100 countries over the past 15 years on behalf of the U.S. intelligence community, as well as for the private defense industry.
While abroad, he has experienced, firsthand and sometimes painfully, the threat of espionage and the lengths to which foreign intelligence services and other hostile global competitors will go to steal American business secrets.
Mr. Bencie currently serves as the managing director of Security Management International, LLC, a security-consulting firm in the Washington, D.C. area.
35,000. That’s how many business travelers depart the United States every day. With them goes over 40,000 cell phones, more than 50,000 laptops, and nearly 500,000 pages of business documents holding privileged information. When you travel abroad, your company is at risk.
Among Enemies tells you how to protect yourself.
Luke Bencie has traveled to more than 100 countries over the past 15 years on behalf of the U.S. intelligence community, as well as for the private defense industry.
While abroad, he has experienced, firsthand and sometimes painfully, the threat of espionage and the lengths to which foreign intelligence services and other hostile global competitors will go to steal American business secrets.
Mr. Bencie currently serves as the managing director of Security Management International, LLC, a security-consulting firm in the Washington, D.C. area.
Sen. Mitch McConnell's "Bug" - Recorded Acoustical Leakage
The center of political intrigue and an FBI investigation in Kentucky's U.S. Senate race is the otherwise inconspicuous second floor hallway of the Watterson West office building in Louisville.
...behind plain, black doors is Sen. Mitch McConnell's campaign headquarters.
It is in this hallway on February 2 that two members of the Progress Kentucky SuperPAC allegedly recorded a private campaign strategy meeting underway inside an office on the other side of one of those plain, black doors, according to Jacob Conway a member of the Jefferson County Democratic Party's Executive Committee.
"You have about a half an inch gap right there where a recording device or a microphone could have been inserted," Benton said, pointing to the bottom of the door...
With the campaign's permission, WHAS11 tested whether an iPhone voice memo program could successfully record a conversation by placing the phone's mouthpiece at the bottom door opening.
Playback of the test recording confirmed that it captured the voices of campaign workers meeting behind the door. The workers had been advised of the recording test...
Some legal analysts suggest that if the closed door meeting could be heard from the hallway, the recording might not be a crime. During the WHAS11 visit, some voices could be heard, without electronic assistance, from the hallway. (more)
Imagine, two guys in the hallway listening under the door. Eavesdropping doesn't get any more basic than that. Spying tricks haven't changed, there are just more of them these days. All the old tricks still work.
If they had their offices inspected by a TSCM team they would have been notified about the acoustical leakage vulnerability... in time to protect themselves.
...behind plain, black doors is Sen. Mitch McConnell's campaign headquarters.
It is in this hallway on February 2 that two members of the Progress Kentucky SuperPAC allegedly recorded a private campaign strategy meeting underway inside an office on the other side of one of those plain, black doors, according to Jacob Conway a member of the Jefferson County Democratic Party's Executive Committee.
"You have about a half an inch gap right there where a recording device or a microphone could have been inserted," Benton said, pointing to the bottom of the door...
Playback of the test recording confirmed that it captured the voices of campaign workers meeting behind the door. The workers had been advised of the recording test...
Some legal analysts suggest that if the closed door meeting could be heard from the hallway, the recording might not be a crime. During the WHAS11 visit, some voices could be heard, without electronic assistance, from the hallway. (more)
Imagine, two guys in the hallway listening under the door. Eavesdropping doesn't get any more basic than that. Spying tricks haven't changed, there are just more of them these days. All the old tricks still work.
If they had their offices inspected by a TSCM team they would have been notified about the acoustical leakage vulnerability... in time to protect themselves.
FREE Security "Green" Papers on Laptop, Mobile Phones & Storage Devices
IT Governance is a supplier of corporate and IT Governance related books, toolkits, training and consultancy. They offer a wealth of knowledge and experience.
 Their Green Papers contain information and guidance on specific problems and discuss many issues. Here are two just published this month...
Their Green Papers contain information and guidance on specific problems and discuss many issues. Here are two just published this month...
Technical Briefing on Laptop and Mobile Storage Devices
Technical Briefing on Mobile Phones and Tablets
About two dozen more may be found here.
 Their Green Papers contain information and guidance on specific problems and discuss many issues. Here are two just published this month...
Their Green Papers contain information and guidance on specific problems and discuss many issues. Here are two just published this month...Technical Briefing on Laptop and Mobile Storage Devices
Technical Briefing on Mobile Phones and Tablets
About two dozen more may be found here.
... thus, giving new meaning to a bright idea!
Optogenetics is the process by which genetically-programmed neurons or other cells can be activated by subjecting them to light. Among other things, the technology helps scientists understand how the brain works, which could in turn lead to new treatments for brain disorders.
 Presently, fiber optic cables must be wired into the brains of test animals in order to deliver light to the desired regions. That may be about to change, however, as scientists have created tiny LEDs that can be injected into the brain.
Presently, fiber optic cables must be wired into the brains of test animals in order to deliver light to the desired regions. That may be about to change, however, as scientists have created tiny LEDs that can be injected into the brain.
The LEDs were developed by a team led by Prof. John A. Rogers from the University of Illinois at Urbana-Champaign, and Prof. Michael R. Bruchas from Washington University. The lights themselves can be as small as single cells and are printed onto the end of a flexible plastic ribbon that’s thinner than a human hair. Using a micro-injection needle, they can be injected precisely and deeply into the brain, with a minimum of disturbance to the brain tissue. (more)
FutureWatch - Mico-sensors to allow downloading of consciousness - knowledge, visuals, ideas, etc..
 Presently, fiber optic cables must be wired into the brains of test animals in order to deliver light to the desired regions. That may be about to change, however, as scientists have created tiny LEDs that can be injected into the brain.
Presently, fiber optic cables must be wired into the brains of test animals in order to deliver light to the desired regions. That may be about to change, however, as scientists have created tiny LEDs that can be injected into the brain. The LEDs were developed by a team led by Prof. John A. Rogers from the University of Illinois at Urbana-Champaign, and Prof. Michael R. Bruchas from Washington University. The lights themselves can be as small as single cells and are printed onto the end of a flexible plastic ribbon that’s thinner than a human hair. Using a micro-injection needle, they can be injected precisely and deeply into the brain, with a minimum of disturbance to the brain tissue. (more)
FutureWatch - Mico-sensors to allow downloading of consciousness - knowledge, visuals, ideas, etc..
Tuesday, April 16, 2013
Small Business Espionage Attacks Up 42%
Smaller companies, their websites and their intellectual property are increasingly being targeted by cyberattacks, a new report on IT security trends says.
Targeted attacks were up 42 per cent in 2012 compared to the year before, and businesses with fewer than 250 employees are the fastest growing segment being targeted, according to the annual internet security threat report issued Tuesday by Symantec...
The type of information being targeted by attackers is also changing — financial information is now losing ground to other kinds of competitive data, the report found. (more)
Targeted attacks were up 42 per cent in 2012 compared to the year before, and businesses with fewer than 250 employees are the fastest growing segment being targeted, according to the annual internet security threat report issued Tuesday by Symantec...
The type of information being targeted by attackers is also changing — financial information is now losing ground to other kinds of competitive data, the report found. (more)
McConnell's Suspected Bugger Has Hand Out
The man who is suspected of bugging Senate Minority Leader Mitch McConnell’s office has started a legal defense fund aimed at raising $10,000 — and so far, he’s received $185.
 Breitbart reported that Curtis Morrison, who’s also a Progress Kentucky volunteer, said in a message about his fund that he’s cooperating with the FBI. But he’s struggling to pay for his legal defense...
Breitbart reported that Curtis Morrison, who’s also a Progress Kentucky volunteer, said in a message about his fund that he’s cooperating with the FBI. But he’s struggling to pay for his legal defense...
A Kentucky Democratic Party operative and the founder of Progress Kentucky outed Mr. Morrison last week as the person who allegedly bugged Mr. McConnell’s office, Breitbart reported. (more)
 Breitbart reported that Curtis Morrison, who’s also a Progress Kentucky volunteer, said in a message about his fund that he’s cooperating with the FBI. But he’s struggling to pay for his legal defense...
Breitbart reported that Curtis Morrison, who’s also a Progress Kentucky volunteer, said in a message about his fund that he’s cooperating with the FBI. But he’s struggling to pay for his legal defense...A Kentucky Democratic Party operative and the founder of Progress Kentucky outed Mr. Morrison last week as the person who allegedly bugged Mr. McConnell’s office, Breitbart reported. (more)
The Schizo Illinois Eavesdropping Law
There was major development Tuesday in the fight over the state's controversial eavesdropping law. A court decision now allows citizens to record the audio of police officers on the job in public.
Citizens can legally record video of police officers doing their jobs on the public way, as long as you don't interfere, but the Illinois Eavesdropping Act does not permit you to record audio.
If you do, you're still subject to arrest and criminal charges, even though two state court judges in Illinois have declared the law unconstitutional.
It remains a law on the books without clarity though a new agreement just approved by a federal court judge will change things in Cook County. (more)
Weird.
Citizens can legally record video of police officers doing their jobs on the public way, as long as you don't interfere, but the Illinois Eavesdropping Act does not permit you to record audio.
If you do, you're still subject to arrest and criminal charges, even though two state court judges in Illinois have declared the law unconstitutional.
It remains a law on the books without clarity though a new agreement just approved by a federal court judge will change things in Cook County. (more)
Weird.
Labels:
cell phone,
eavesdropping,
government,
law,
police,
recording,
weird
RFID Tracks Jewelry Popularity
Interesting application of RFID technology.
RFID smart shelves can help retailers analyze market demand.
 Beyond sales reports, retailers want to understand which items had the highest shopper interest. For example, while one jewelry item is picked up 100 times and sold 90 time, another jewelry item is picked up 100 times but only sold 10 times. Retail statistics monitoring shopper behavior cannot be accurately counted by man.
Beyond sales reports, retailers want to understand which items had the highest shopper interest. For example, while one jewelry item is picked up 100 times and sold 90 time, another jewelry item is picked up 100 times but only sold 10 times. Retail statistics monitoring shopper behavior cannot be accurately counted by man.
However, the RFID Jewelry Smart Shelf Solution developed by Alpha Solutions enables retailers to clearly see data on which types of jewelry are picked up frequently. From the data obtained, discount promotions and programs can be made for the jewelry types that are having trouble selling.
RFID smart shelves can help retailers analyze market demand.
 Beyond sales reports, retailers want to understand which items had the highest shopper interest. For example, while one jewelry item is picked up 100 times and sold 90 time, another jewelry item is picked up 100 times but only sold 10 times. Retail statistics monitoring shopper behavior cannot be accurately counted by man.
Beyond sales reports, retailers want to understand which items had the highest shopper interest. For example, while one jewelry item is picked up 100 times and sold 90 time, another jewelry item is picked up 100 times but only sold 10 times. Retail statistics monitoring shopper behavior cannot be accurately counted by man.However, the RFID Jewelry Smart Shelf Solution developed by Alpha Solutions enables retailers to clearly see data on which types of jewelry are picked up frequently. From the data obtained, discount promotions and programs can be made for the jewelry types that are having trouble selling.
Thursday, April 11, 2013
There is a Magazine for Everything... Even Penetration Testing
Kamil Sobieraj, editor of PenTest Magazine introduced me to his publication this week. It was an eye-opener. If you have anything to do with protecting information, you will find this as interesting as I did...
PenTest Magazine is a weekly downloadable IT security magazine, devoted exclusively to penetration testing. It features articles by penetration testing specialists and enthusiasts, experts in vulnerability assessment and management. All aspects of pen testing, from theory to practice, from methodologies and standards to tools and real-life solutions are covered.
48 issues per year (4 issues in a month).
A different title is published every week of the month:
• PenTest Regular – 1st Monday
• Auditing & Standards PenTest – 2nd Monday
• PenTest Extra – 3rd Monday
• Web App Pentesting – 4th Monday
 ...about 200 pages of content per month.
...about 200 pages of content per month.
Each issue contains...
• News
• Tools testing and reviews
• Articles – advanced technical articles showing techniques in practice
• Book review
• Interviews with IT security experts
(more)
Nice to know there is a smart way to keep up with the bad guys.
PenTest Magazine is a weekly downloadable IT security magazine, devoted exclusively to penetration testing. It features articles by penetration testing specialists and enthusiasts, experts in vulnerability assessment and management. All aspects of pen testing, from theory to practice, from methodologies and standards to tools and real-life solutions are covered.
48 issues per year (4 issues in a month).
A different title is published every week of the month:
• PenTest Regular – 1st Monday
• Auditing & Standards PenTest – 2nd Monday
• PenTest Extra – 3rd Monday
• Web App Pentesting – 4th Monday
 ...about 200 pages of content per month.
...about 200 pages of content per month.Each issue contains...
• News
• Tools testing and reviews
• Articles – advanced technical articles showing techniques in practice
• Book review
• Interviews with IT security experts
(more)
Nice to know there is a smart way to keep up with the bad guys.
Wednesday, April 10, 2013
Campaign Headquarters Bugged - FBI Investigating
Senate Minority Leader Mitch McConnell (R-Ky.) accused opponents Tuesday of bugging his headquarters and asked for an FBI investigation after a recording from an internal campaign meeting surfaced in a magazine report.
The 12-minute audiotape released by Mother Jones magazine reveals McConnell and his campaign staff at a Feb. 2 meeting lampooning actress Ashley Judd — then a potential Senate candidate — and comparing her to “a haystack of needles” because of her potential political liabilities. Judd has since decided not to run.
“We’ve always said the left will stop at nothing to attack Sen. McConnell, but Nixonian tactics to bug campaign headquarters is above and beyond,” campaign manager Jesse Benton said in a statement. (more)
UPDATE: "It is our understanding that the tape was not the product of a Watergate-style bugging operation. We cannot comment beyond that." – David Corn, Editor, Mother Jones (more)
Note: More than one person is heard speaking on the tapes (above is just an excerpt). Based on this, (and room echoes) the FBI will be able to figure out the location of the microphone. Hope everyone remembers where they were sitting.
The 12-minute audiotape released by Mother Jones magazine reveals McConnell and his campaign staff at a Feb. 2 meeting lampooning actress Ashley Judd — then a potential Senate candidate — and comparing her to “a haystack of needles” because of her potential political liabilities. Judd has since decided not to run.
“We’ve always said the left will stop at nothing to attack Sen. McConnell, but Nixonian tactics to bug campaign headquarters is above and beyond,” campaign manager Jesse Benton said in a statement. (more)
UPDATE: "It is our understanding that the tape was not the product of a Watergate-style bugging operation. We cannot comment beyond that." – David Corn, Editor, Mother Jones (more)
Note: More than one person is heard speaking on the tapes (above is just an excerpt). Based on this, (and room echoes) the FBI will be able to figure out the location of the microphone. Hope everyone remembers where they were sitting.
Tuesday, April 9, 2013
Shodan - The Scary Search Engine
Cautionary Tale...
Unlike Google, which crawls the Web looking for websites, Shodan navigates the Internet's back channels. It's a kind of "dark" Google, looking for the servers, webcams, printers, routers and all the other stuff that is connected to and makes up the Internet...
It's stunning what can be found with a simple search on Shodan. Countless traffic lights, security cameras, home automation devices and heating systems are connected to the Internet and easy to spot.
Shodan searchers have found control systems for a water park, a gas station, a hotel wine cooler and a crematorium. Cybersecurity researchers have even located command and control systems for nuclear power plants and a particle-accelerating cyclotron by using Shodan.
What's really noteworthy about Shodan's ability to find all of this -- and what makes Shodan so scary -- is that very few of those devices have any kind of security built into them. (more)
Unlike Google, which crawls the Web looking for websites, Shodan navigates the Internet's back channels. It's a kind of "dark" Google, looking for the servers, webcams, printers, routers and all the other stuff that is connected to and makes up the Internet...
It's stunning what can be found with a simple search on Shodan. Countless traffic lights, security cameras, home automation devices and heating systems are connected to the Internet and easy to spot.
Shodan searchers have found control systems for a water park, a gas station, a hotel wine cooler and a crematorium. Cybersecurity researchers have even located command and control systems for nuclear power plants and a particle-accelerating cyclotron by using Shodan.
What's really noteworthy about Shodan's ability to find all of this -- and what makes Shodan so scary -- is that very few of those devices have any kind of security built into them. (more)
Free - Computer Security Tools Book
"Open Source Security Tools: A Practical Guide to Security Applications"
Few frontline system administrators can afford to spend all day worrying about security. But in this age of widespread virus infections, worms, and digital attacks, no one can afford to neglect network defenses.
Written with the harried IT manager in mind, Open Source Security Tools is a practical, hands-on introduction to open source security tools. Seasoned security expert Tony Howlett has reviewed the overwhelming assortment of these free and low-cost solutions to provide you with the “best of breed” for all major areas of information security.
By Tony Howlett. Published by Prentice Hall. Part of the Bruce Perens' Open Source Series.
Offered Free by: informIT
A 600-page PDF, written in 2004, which still contains useful information.
Few frontline system administrators can afford to spend all day worrying about security. But in this age of widespread virus infections, worms, and digital attacks, no one can afford to neglect network defenses.
Written with the harried IT manager in mind, Open Source Security Tools is a practical, hands-on introduction to open source security tools. Seasoned security expert Tony Howlett has reviewed the overwhelming assortment of these free and low-cost solutions to provide you with the “best of breed” for all major areas of information security.
By Tony Howlett. Published by Prentice Hall. Part of the Bruce Perens' Open Source Series.
Offered Free by: informIT
A 600-page PDF, written in 2004, which still contains useful information.
Sunday, April 7, 2013
Son Bugs Mom (yawn)... with a Wiretap!
UK - Police have arrested a Lincoln man on suspicion that he bugged his 90-year-old mother’s phone.
Richard Stamler, 59, was arrested Thursday night for unlawful interception of communications, a felony, Lincoln Police Officer Katie Flood said.
Stamler’s sister called police March 28 to say she found a recording device in the basement of her mother’s home that had been connected to the phone line, Flood said.
The woman played the tape, Flood said, and recognized her brother’s voice reciting date information. The device was set to record any time someone in the house picked up a phone. (more)
Richard Stamler, 59, was arrested Thursday night for unlawful interception of communications, a felony, Lincoln Police Officer Katie Flood said.
Stamler’s sister called police March 28 to say she found a recording device in the basement of her mother’s home that had been connected to the phone line, Flood said.
The woman played the tape, Flood said, and recognized her brother’s voice reciting date information. The device was set to record any time someone in the house picked up a phone. (more)
Saturday, April 6, 2013
Canadian Technical Security Conference (CTSC) - April 23-25, 2013
Canadian Technical Security Conference (CTSC) - April 23-25, 2013
The annual Canadian Technical Security Conference (CTSC) event (Cornwall, Ontario) is a three (3) day professional development and networking opportunity with a local, regional, national and international following of professional technical operators, TSCM specific and test & measurement based equipment manufacturers and service providers.
The conference is being held at Strathmere, near Ottawa.
GPS Coordinates, Latitude 45.157216, Longitude 75.703858
This annual CTSC conference event is of special interest to local, regional and international technical security professionals from the private sector, corporate security industry, financial sector, oil, gas and mining sector, government, law enforcement and military organizations and agencies. (more) Contact: Paul D Turner, TSS TSI
This is the conference's 8th year. Every year I hear reports about how worthwhile it is. Every year they schedule it when I am obligated to be elsewhere :(
The annual Canadian Technical Security Conference (CTSC) event (Cornwall, Ontario) is a three (3) day professional development and networking opportunity with a local, regional, national and international following of professional technical operators, TSCM specific and test & measurement based equipment manufacturers and service providers.
The conference is being held at Strathmere, near Ottawa.
GPS Coordinates, Latitude 45.157216, Longitude 75.703858
This annual CTSC conference event is of special interest to local, regional and international technical security professionals from the private sector, corporate security industry, financial sector, oil, gas and mining sector, government, law enforcement and military organizations and agencies. (more) Contact: Paul D Turner, TSS TSI
This is the conference's 8th year. Every year I hear reports about how worthwhile it is. Every year they schedule it when I am obligated to be elsewhere :(
Burglar Used SpyCams to Case High-Income Homes
The discovery of a hidden camera may help solve a series of break-ins at upscale homes in several North Texas cities.
"This one has already been camouflaged," said Dalworthington Gardens police Det. Ben Singleton, holding what looks like a piece of bark that would go unnoticed in most yards.
It's actually a video camera not much bigger than a matchbox, and it's activated by a motion detector. Such cameras turned up in March planted outside several upscale homes in Dalworthington Gardens.
"I've never seen anything like this," Singleton said. (more)
"This one has already been camouflaged," said Dalworthington Gardens police Det. Ben Singleton, holding what looks like a piece of bark that would go unnoticed in most yards.
It's actually a video camera not much bigger than a matchbox, and it's activated by a motion detector. Such cameras turned up in March planted outside several upscale homes in Dalworthington Gardens.
"I've never seen anything like this," Singleton said. (more)
New Italian Cocktail "The Gepetto" - Thwarted by SpyCam
A retired Italian carpenter has been arrested after his sleuthing wife suspected he was trying to poison her and set about trying to prove it with the help of a spy alarm clock bought on the internet.
The drama began in February in the northern Italian town of Dalmine, where the couple had reportedly lived for almost 40 years. The 61-year-old woman grew suspicious when some water brought to her by her husband created a burning sensation in her mouth.
The woman, who has not been named, sent it off for tests in a laboratory, which, when they came back, revealed the presence of hydrochloric acid.
Perturbed, the woman became even more worried when she found a bottle among her husband's things that had no label on it and was filled with a clear liquid. She sent that off to be analyzed, as well, and was told that it, too, was hydrochloric acid.
Police confirmed that she then took advice from relatives and bought a miniature video-camera-cum-alarm-clock, proceeding to film her husband in the kitchen. (more)
 |
| Click to enlarge. |
The drama began in February in the northern Italian town of Dalmine, where the couple had reportedly lived for almost 40 years. The 61-year-old woman grew suspicious when some water brought to her by her husband created a burning sensation in her mouth.
The woman, who has not been named, sent it off for tests in a laboratory, which, when they came back, revealed the presence of hydrochloric acid.
Perturbed, the woman became even more worried when she found a bottle among her husband's things that had no label on it and was filled with a clear liquid. She sent that off to be analyzed, as well, and was told that it, too, was hydrochloric acid.
Police confirmed that she then took advice from relatives and bought a miniature video-camera-cum-alarm-clock, proceeding to film her husband in the kitchen. (more)
The Era of Women Spies is Returning
White House counterterrorism adviser Lisa Monaco is all poised to head the FBI, following last week's appointment of Julia Pierson as director of the Secret Service and an unnamed CIA agent will be the first woman to lead the agency's clandestine service.
With these back-to-back developments, the era of women spies seems to have returned.
Some of them became legends and remained in the history as picturesque creatures, who with their skill, grace, charm or nerve, pulled the strings behind the most delicate political movements of the world.
Learn more about some of the most famous and sexy spy women...
• Mata Hari
• Virginia Hall
• Hedy Lamarr
• Elizabeth Van Lew • Belle Boyd
• Sarah Emma Edmonds
• Noor Inayat Khan
With these back-to-back developments, the era of women spies seems to have returned.
Some of them became legends and remained in the history as picturesque creatures, who with their skill, grace, charm or nerve, pulled the strings behind the most delicate political movements of the world.
Learn more about some of the most famous and sexy spy women...
• Mata Hari
• Virginia Hall
• Hedy Lamarr
• Elizabeth Van Lew • Belle Boyd
• Sarah Emma Edmonds
• Noor Inayat Khan
Friday, April 5, 2013
Amazing Drone Footage - Just for fun - Enjoy Your Weekend
The SkyMotion Video team provided the aerial video services for the 2012 Tourism Partnership of Niagara commercials for the Niagara Falls region shoot - making use of their state of the art remote controlled helicopter drone.
Niagara Falls has of course been filmed countless times in the past using full sized helicopters. However, with this remote controlled helicopter, the shoot was not limited by minimum altitude restrictions, and so was able to achieve shots which were unlike any before. Flying only a couple feet above the water, the camera was able to approach the waterfall edge to give the viewer a true sense of the shear scale of the world famous falls.
However, the Niagara region is not limited to just the falls. The surrounding area is full of beautiful landscapes with quaint towns, and world class vineyards. The area is full of life, and the hope is that these dynamic shots give a real sense of the variety of things offered by not only the falls, but by the region as a whole. (more) (more movies)
PS - The security tie-in's...
• Law Enforcement - Crime scene documentation and assessment.
• Security Consultants - Security assessment surveys.
Niagara Falls has of course been filmed countless times in the past using full sized helicopters. However, with this remote controlled helicopter, the shoot was not limited by minimum altitude restrictions, and so was able to achieve shots which were unlike any before. Flying only a couple feet above the water, the camera was able to approach the waterfall edge to give the viewer a true sense of the shear scale of the world famous falls.
However, the Niagara region is not limited to just the falls. The surrounding area is full of beautiful landscapes with quaint towns, and world class vineyards. The area is full of life, and the hope is that these dynamic shots give a real sense of the variety of things offered by not only the falls, but by the region as a whole. (more) (more movies)
PS - The security tie-in's...
• Law Enforcement - Crime scene documentation and assessment.
• Security Consultants - Security assessment surveys.
Apple's iMessage has DEA Tongue Tied
Encryption used in Apple's iMessage chat service has stymied attempts by federal drug enforcement agents to eavesdrop on suspects' conversations, an internal government document reveals.
An internal Drug Enforcement Administration document seen by CNET discusses a February 2013 criminal investigation and warns that because of the use of encryption, "it is impossible to intercept iMessages between two Apple devices" even with a court order approved by a federal judge...
When Apple's iMessage was announced in mid-2011, Cupertino said it would use "secure end-to-end encryption." It quickly became the most popular encrypted chat program in history: Apple CEO Tim Cook said last fall that 300 billion messages have been sent so far, which are transmitted through the Internet rather than as more costly SMS messages carried by wireless providers. (more)
But... if messages are exchanged between an Apple device and a non-Apple device, they "can sometimes be intercepted, depending on where the intercept is placed." (more)
 |
| Click to enlarge. |
When Apple's iMessage was announced in mid-2011, Cupertino said it would use "secure end-to-end encryption." It quickly became the most popular encrypted chat program in history: Apple CEO Tim Cook said last fall that 300 billion messages have been sent so far, which are transmitted through the Internet rather than as more costly SMS messages carried by wireless providers. (more)
But... if messages are exchanged between an Apple device and a non-Apple device, they "can sometimes be intercepted, depending on where the intercept is placed." (more)
Labels:
cell phone,
data,
encryption,
FBI,
government,
privacy,
surveillance
Security Consultant Alert - IAPSC Annual Conference in Napa, CA
NOTE: It is not too late to register. Be a hero. Take your significant other to Napa for a few days.
The International Association of Professional Security Consultants (IAPSC) Annual Conference is the largest and most exclusive gathering of top security consultants.
Their 2013 conference offers a wide range of topics focused on Security Consulting and Business Profitability, as well as, Technical, Forensic, and IT Security.
Presenters will discuss security standards, best practices, risk management, promotional uses of media, including webinar development, marketing and communications techniques for consultants, retirement and selling your business, as well as technical and forensic security focused sessions.
Visit the conference website
View the conference program
Download the brochure
Register Now
Not yet an IAPSC Member?
When you register to attend the conference, ask about special registration offer available exclusively to new members. (more)
I have been attending IAPSC conferences, each year, for about two decades. Every one has been well worth attending. I return to the office with a broader knowledge of security, fresh ideas about improving services to my clients, and recharged mental batteries. If you are on the fence about going, hop off... and into the vineyard. Try it once. You will see what I mean. Be sure to find me and say hello. ~Kevin
The International Association of Professional Security Consultants (IAPSC) Annual Conference is the largest and most exclusive gathering of top security consultants.
Their 2013 conference offers a wide range of topics focused on Security Consulting and Business Profitability, as well as, Technical, Forensic, and IT Security.
Presenters will discuss security standards, best practices, risk management, promotional uses of media, including webinar development, marketing and communications techniques for consultants, retirement and selling your business, as well as technical and forensic security focused sessions.
Visit the conference website
View the conference program
Download the brochure
Register Now
Not yet an IAPSC Member?
When you register to attend the conference, ask about special registration offer available exclusively to new members. (more)
I have been attending IAPSC conferences, each year, for about two decades. Every one has been well worth attending. I return to the office with a broader knowledge of security, fresh ideas about improving services to my clients, and recharged mental batteries. If you are on the fence about going, hop off... and into the vineyard. Try it once. You will see what I mean. Be sure to find me and say hello. ~Kevin
AppSec USA 2013 is Coming to NYC
Call for Papers NOW OPEN!
CareerFair
Events (Capture the Flag, Battlebots, Lockpick Village, and more)
AppSec USA is a software security conference for technologists, auditors, risk managers, and entrepreneurs, gathering the world's top practitioner, to share the latest research and practices at the Marriott, NYC. It is hosted by OWASP. (Why you would want to attend.)
What is OWASP?
The Open Web Application Security Project (OWASP) is a 501(c)(3) worldwide not-for-profit charitable organization focused on improving the security of software. Their mission is to make software security visible, so that individuals and organizations worldwide can make informed decisions about true software security risks.
Everyone is free to participate in OWASP and all of their materials are available under a free and open software license.
You'll find everything about OWASP here on or linked from our wiki and current information on our OWASP Blog.
OWASP does not endorse or recommend commercial products or services, allowing our community to remain vendor neutral with the collective wisdom of the best minds in software security worldwide.
OWASP is a global group of volunteers with over 36,000 participants. (more)
CareerFair
Events (Capture the Flag, Battlebots, Lockpick Village, and more)
AppSec USA is a software security conference for technologists, auditors, risk managers, and entrepreneurs, gathering the world's top practitioner, to share the latest research and practices at the Marriott, NYC. It is hosted by OWASP. (Why you would want to attend.)
What is OWASP?
The Open Web Application Security Project (OWASP) is a 501(c)(3) worldwide not-for-profit charitable organization focused on improving the security of software. Their mission is to make software security visible, so that individuals and organizations worldwide can make informed decisions about true software security risks.
Everyone is free to participate in OWASP and all of their materials are available under a free and open software license.
You'll find everything about OWASP here on or linked from our wiki and current information on our OWASP Blog.
OWASP does not endorse or recommend commercial products or services, allowing our community to remain vendor neutral with the collective wisdom of the best minds in software security worldwide.
OWASP is a global group of volunteers with over 36,000 participants. (more)
Thursday, April 4, 2013
Blue Bugging - An old topic and growing problem
When you pair your smart phone with your vehicle's audio system and leave that connection open, you may become the target of Blue-bugging.
"They have paired their car and they leave their Bluetooth pairing open and then they get out of the car…they come out of the car and go to a store or something like that and the Bluetooth capability is still on," explains Mike Rohrer with the Arkansas Better Business Bureau.
The BBB advises you switch your Bluetooth into "Not discoverable" mode when you aren't using it…especially in crowded, public places.
Always use at least eight characters in your pin.
When pairing devices for the first time, do it at home or in the office. And download the latest security updates. (more) (video)
There is also a chapter (Bluetooth® Eavesdropping) devoted to the subject of Bluetooth vulnerabilities in, "Is My Cell Phone Bugged?"
"They have paired their car and they leave their Bluetooth pairing open and then they get out of the car…they come out of the car and go to a store or something like that and the Bluetooth capability is still on," explains Mike Rohrer with the Arkansas Better Business Bureau.
The BBB advises you switch your Bluetooth into "Not discoverable" mode when you aren't using it…especially in crowded, public places.
Always use at least eight characters in your pin.
When pairing devices for the first time, do it at home or in the office. And download the latest security updates. (more) (video)
There is also a chapter (Bluetooth® Eavesdropping) devoted to the subject of Bluetooth vulnerabilities in, "Is My Cell Phone Bugged?"
Subscribe to:
Posts (Atom)