Katana FT-1 is a miniature voice recorder with built-in Wi-Fi transmitter.
It records high quality audio on a MicroSD card. Yet to listen to the records you don’t even have to touch the voice recorder. All the collected data can be downloaded to an FTP server or host computer using ad-hoc Wi-Fi connection or via Internet.
To ensure high quality sound and fast upload Katana FT-1 exploits a dedicated audio processor with sophisticated voice compression algorithms (like Vorbis Ogg) and hi-speed Wi-Fi module. So 1 hour of high quality audio recording can be uploaded in just about 14 seconds. (more)
Why do I mention it?
So you will know what you're up against.
Friday, November 28, 2014
Aged Law Urped Up to Decrypt Phone Data
The Justice Department is turning to a 225-year-old law to tackle a very modern problem: password-protected cellphones.
Prosecutors last month asked a federal magistrate in Manhattan to order an unnamed phone maker to provide “reasonable technical assistance” to unlock a password-protected phone that could contain evidence in a credit-card-fraud case, according to court filings...
...the government on Oct. 10 obtained a search warrant to examine the contents of the phone. In the credit-card case, the phone was locked, so prosecutors asked U.S. Magistrate Judge Gabriel Gorenstein to order the manufacturer to unlock it. They cited the All Writs Act, originally part of a 1789 law that gives courts broad authority to carry out their duties. (more)
Prosecutors last month asked a federal magistrate in Manhattan to order an unnamed phone maker to provide “reasonable technical assistance” to unlock a password-protected phone that could contain evidence in a credit-card-fraud case, according to court filings...
...the government on Oct. 10 obtained a search warrant to examine the contents of the phone. In the credit-card case, the phone was locked, so prosecutors asked U.S. Magistrate Judge Gabriel Gorenstein to order the manufacturer to unlock it. They cited the All Writs Act, originally part of a 1789 law that gives courts broad authority to carry out their duties. (more)
Log Jam - Forces You to Shut Up and Experience Where You Are
Artist and coder Allison Burtch has created a new device to save us from our cellphones and ourselves.
It comes in the form of a 10-inch birch log that jams cellular radio signals, and it’s called the Log Jammer. Packed with about $200 of hardware including a power source, a circuit board of her own design, voltage control components, an amplifier, and an antenna, it can produce radio noise at the 1950 megahertz frequency commonly used by cellphones. It’s powerful enough to block all cellphone voice communications in a 20-foot bubble, and its log-like exterior is designed to unobtrusively create that radio-jamming zone in the great outdoors...
Burtch sees her creation as the inverse of the increasingly common sight of cellular towers disguised as trees. Instead of hiding technology in nature to let people remain connected everywhere, the Log Jammer blends into a natural setting to cut off that constant remote communication—to force people to experience the place they’re in. Burtch paraphrases French philosopher Gilles Deleuz: “The problem is no longer getting people to express themselves,” she says. “It’s creating a needed gap of solitude in which they might find something to say.” (more)
It comes in the form of a 10-inch birch log that jams cellular radio signals, and it’s called the Log Jammer. Packed with about $200 of hardware including a power source, a circuit board of her own design, voltage control components, an amplifier, and an antenna, it can produce radio noise at the 1950 megahertz frequency commonly used by cellphones. It’s powerful enough to block all cellphone voice communications in a 20-foot bubble, and its log-like exterior is designed to unobtrusively create that radio-jamming zone in the great outdoors...
Burtch sees her creation as the inverse of the increasingly common sight of cellular towers disguised as trees. Instead of hiding technology in nature to let people remain connected everywhere, the Log Jammer blends into a natural setting to cut off that constant remote communication—to force people to experience the place they’re in. Burtch paraphrases French philosopher Gilles Deleuz: “The problem is no longer getting people to express themselves,” she says. “It’s creating a needed gap of solitude in which they might find something to say.” (more)
Sunday, November 23, 2014
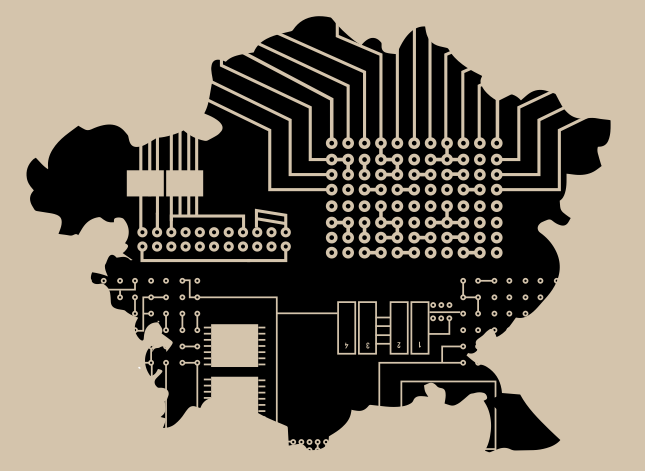
How They Do It - Spying on Citizens in Central Asia
A recent report from Privacy International
has tried to shine some light on the methods Central Asian governments are using to track their populaces – and to examine how closely they mirror Russian and Chinese examples, as well as which Western companies have supplied the necessary technology along the way. (more)
has tried to shine some light on the methods Central Asian governments are using to track their populaces – and to examine how closely they mirror Russian and Chinese examples, as well as which Western companies have supplied the necessary technology along the way. (more)
Hey Kids! You Too Can Have Cool NSA Spy Toys
Welcome to the home of the NSA Playset.
 In the coming months and beyond, we will release a series of dead simple, easy to use tools to enable the next generation of security researchers. We, the security community have learned a lot in the past couple decades, yet the general public is still ill equipped to deal with real threats that face them every day, and ill informed as to what is possible.
In the coming months and beyond, we will release a series of dead simple, easy to use tools to enable the next generation of security researchers. We, the security community have learned a lot in the past couple decades, yet the general public is still ill equipped to deal with real threats that face them every day, and ill informed as to what is possible.
Inspired by the NSA ANT catalog, we hope the NSA Playset will make cutting edge security tools more accessible, easier to understand, and harder to forget. Now you can play along with the NSA! (more)
If you are thinking of contributing a new NSA Playset project, please keep in mind the following requirements:
1. A Silly Name
If your project is similar to an existing NSA ANT project, you can come up with a clever play on that name. For example, if your project is similar to FOXACID, maybe you could call it COYOTEMETH. Of course, if your project doesn't quite line up with anything in the ANT Catalog, you can come up with your own name. If you are feeling less creative, try out the handy name generator found here: http://www.nsanamegenerator.com/ (more)
 In the coming months and beyond, we will release a series of dead simple, easy to use tools to enable the next generation of security researchers. We, the security community have learned a lot in the past couple decades, yet the general public is still ill equipped to deal with real threats that face them every day, and ill informed as to what is possible.
In the coming months and beyond, we will release a series of dead simple, easy to use tools to enable the next generation of security researchers. We, the security community have learned a lot in the past couple decades, yet the general public is still ill equipped to deal with real threats that face them every day, and ill informed as to what is possible.Inspired by the NSA ANT catalog, we hope the NSA Playset will make cutting edge security tools more accessible, easier to understand, and harder to forget. Now you can play along with the NSA! (more)
If you are thinking of contributing a new NSA Playset project, please keep in mind the following requirements:
1. A Silly Name
If your project is similar to an existing NSA ANT project, you can come up with a clever play on that name. For example, if your project is similar to FOXACID, maybe you could call it COYOTEMETH. Of course, if your project doesn't quite line up with anything in the ANT Catalog, you can come up with your own name. If you are feeling less creative, try out the handy name generator found here: http://www.nsanamegenerator.com/ (more)
Labels:
amateur,
eavesdropping,
fun,
FutureWatch,
Hack,
NSA,
wiretapping
This Week in Wiretap News
ID - The former information technology director of a hospital in Blackfoot was sentenced to three years of probation after he was convicted of wiretapping. A Bingham County judge imposed the sentence for 46-year-old Jack York on Friday. York was accused along with three others of recording telephone calls by a former hospital doctor and his staff between June 2009 and August 2010. (more) (more)
Taiwan - An aide to Ko Wen-je was arrested yesterday by Taipei prosecutors looking into alleged wiretapping of the independent Taipei mayoral hopeful's office... (more)
DC - American investigators intercepted a conversation this year in which a Pakistani official suggested that his government was receiving American secrets from a prominent former State Department diplomat, officials said, setting off an espionage investigation that has stunned diplomatic circles here, The New York Times in a report Friday said. That conversation led to months of secret surveillance on the former diplomat, Robin L. Raphel, and an F.B.I. raid last month at her home, where agents discovered classified information, the officials said. (more)
Turkey - More details have surfaced about the Gülenists' wiretapping of the then prime minister Recep Tayyip Erdoğan, after an indictment regarding the investigation was submitted to court. The Gülenists planned every step in detail, according to the indictment. The Ankara chief public prosecutor's office has prepared an indictment on 13 suspects, who are accused of wiretapping then Prime Minister Recep Tayyip Erdoğan, charging the suspects with "political spying" after an investigation into the alleged offenders was completed. (more)
CA - Counsel Timothy Perry discusses how wiretaps are vulnerable to attack, especially in white collar cases. He explains some details of the wiretap statute and discusses how defense attorneys can best address wiretap evidence in a white collar case. (video)
NC - A judge Friday unsealed a trove of court documents that could shed light on a secret cellphone tracking program used by police nationwide. The judge in Charlotte, N.C., acted after a petition from the Charlotte Observer to make the documents public. Included are 529 requests from local Charlotte-Mecklenburg police asking judges to approve the use of a technology known as StingRay, which allows cellphone surveillance. (more)
NYC - Add New York City’s Taxi and Limousine Commission to the list of powerful groups investigating Uber for allegedly spying on its users. The commission, which regulates Uber, is “looking into allegations” that the mobile car-hailing app violated users’ privacy by tracking them without their permission. (more)
Taiwan - An aide to Ko Wen-je was arrested yesterday by Taipei prosecutors looking into alleged wiretapping of the independent Taipei mayoral hopeful's office... (more)
DC - American investigators intercepted a conversation this year in which a Pakistani official suggested that his government was receiving American secrets from a prominent former State Department diplomat, officials said, setting off an espionage investigation that has stunned diplomatic circles here, The New York Times in a report Friday said. That conversation led to months of secret surveillance on the former diplomat, Robin L. Raphel, and an F.B.I. raid last month at her home, where agents discovered classified information, the officials said. (more)
Turkey - More details have surfaced about the Gülenists' wiretapping of the then prime minister Recep Tayyip Erdoğan, after an indictment regarding the investigation was submitted to court. The Gülenists planned every step in detail, according to the indictment. The Ankara chief public prosecutor's office has prepared an indictment on 13 suspects, who are accused of wiretapping then Prime Minister Recep Tayyip Erdoğan, charging the suspects with "political spying" after an investigation into the alleged offenders was completed. (more)
CA - Counsel Timothy Perry discusses how wiretaps are vulnerable to attack, especially in white collar cases. He explains some details of the wiretap statute and discusses how defense attorneys can best address wiretap evidence in a white collar case. (video)
NC - A judge Friday unsealed a trove of court documents that could shed light on a secret cellphone tracking program used by police nationwide. The judge in Charlotte, N.C., acted after a petition from the Charlotte Observer to make the documents public. Included are 529 requests from local Charlotte-Mecklenburg police asking judges to approve the use of a technology known as StingRay, which allows cellphone surveillance. (more)
NYC - Add New York City’s Taxi and Limousine Commission to the list of powerful groups investigating Uber for allegedly spying on its users. The commission, which regulates Uber, is “looking into allegations” that the mobile car-hailing app violated users’ privacy by tracking them without their permission. (more)
Adequately Protected Trade Secrets Can Keep You Out of Court... and a winner in court.
by Mark L. Krotoski, Esq.
Trade secrets can be among the most valuable assets a company has. According to one study, "Two thirds of enterprises’ information portfolio value comes from the secrets they create."
 One trade secret can lead to many products. As a unique form of intellectual property, trade secrets can be vital not only to a company and its employees, but also to other jobs, investments, an industry, the economy and, depending on the trade secrets, even national security.
One trade secret can lead to many products. As a unique form of intellectual property, trade secrets can be vital not only to a company and its employees, but also to other jobs, investments, an industry, the economy and, depending on the trade secrets, even national security.
Two Key Questions for Trade Secret Owners
Given the importance of trade secrets, trade secret owners should ask two key questions:
(1) How many trade secrets do you have?
(2) Are your trade secrets adequately protected?
Many companies have trade secrets which can generate substantial value for the company. Regrettably, experience has shown that large and small companies have not taken the steps necessary to protect them. When the unexpected misappropriation occurs, it is clearly too late...
A culture of protection can establish the tone within the company to safeguard the trade secrets. A layered approach to security has proven effective in past cases to mitigate any misappropriation and to establish the reasonableness of the security measures. An objective assessment of the measures safeguarding the trade secrets can assist in determining the reasonableness u der trade secret law. Most importantly, companies should develop a trade secret protection plan in advance of any misappropriation.
So, as a trade secret owner, how do you answer the two questions? How confident are you that your trade secrets are reasonably protected and will survive court scrutiny if that ever becomes necessary? (more)
If you need help answering these questions, call me. An information security evaluation by an independent outside specialist can help with answers and will count toward fulfilling the adequacy requirement.
Trade secrets can be among the most valuable assets a company has. According to one study, "Two thirds of enterprises’ information portfolio value comes from the secrets they create."
 One trade secret can lead to many products. As a unique form of intellectual property, trade secrets can be vital not only to a company and its employees, but also to other jobs, investments, an industry, the economy and, depending on the trade secrets, even national security.
One trade secret can lead to many products. As a unique form of intellectual property, trade secrets can be vital not only to a company and its employees, but also to other jobs, investments, an industry, the economy and, depending on the trade secrets, even national security.Two Key Questions for Trade Secret Owners
Given the importance of trade secrets, trade secret owners should ask two key questions:
(1) How many trade secrets do you have?
(2) Are your trade secrets adequately protected?
Many companies have trade secrets which can generate substantial value for the company. Regrettably, experience has shown that large and small companies have not taken the steps necessary to protect them. When the unexpected misappropriation occurs, it is clearly too late...
A culture of protection can establish the tone within the company to safeguard the trade secrets. A layered approach to security has proven effective in past cases to mitigate any misappropriation and to establish the reasonableness of the security measures. An objective assessment of the measures safeguarding the trade secrets can assist in determining the reasonableness u der trade secret law. Most importantly, companies should develop a trade secret protection plan in advance of any misappropriation.
So, as a trade secret owner, how do you answer the two questions? How confident are you that your trade secrets are reasonably protected and will survive court scrutiny if that ever becomes necessary? (more)
If you need help answering these questions, call me. An information security evaluation by an independent outside specialist can help with answers and will count toward fulfilling the adequacy requirement.
Thursday, November 20, 2014
FREE - Enemy-of-the-State Spyware Detection Tool
via eff.org...
"Detekt is an easy-to-use, open source tool that allows users to check their Windows PCs for signs of infection by surveillance malware that we know is being used by government to spy on activists and journalists.
Some of the software used by states against innocent citizens is widely available on the Internet, while more sophisticated alternatives are made and sold by private companies and sold to governments everywhere from the United States and Europe to Ethiopia and Vietnam.
Detekt makes it easy for at-risk users to check their PCs for possible infection by this spyware, which often goes undetected by existing commercial anti-virus products." (more)
"Detekt is an easy-to-use, open source tool that allows users to check their Windows PCs for signs of infection by surveillance malware that we know is being used by government to spy on activists and journalists.
Some of the software used by states against innocent citizens is widely available on the Internet, while more sophisticated alternatives are made and sold by private companies and sold to governments everywhere from the United States and Europe to Ethiopia and Vietnam.
Detekt makes it easy for at-risk users to check their PCs for possible infection by this spyware, which often goes undetected by existing commercial anti-virus products." (more)
Labels:
App,
computer,
counterespionage,
FREE,
government,
privacy,
software
Covert Video Leaves Business Running Around Like a Chicken with its...
TN - Koch Foods on Wednesday denied its Chattanooga processing plant is inhumanely treating chickens by scalding the birds alive and shackling them upside-down before slicing open their throats, wings and chests while still conscious.
The allegations by animal protection group Mercy for Animals...
The Los Angeles-based group released covert video that it said was taken inside the Koch Chattanooga plant and another operation in Mississippi, complaining that workers are also cruelly throwing chickens and hiding cockroaches from federal inspectors.
The video, narrated by The Simpsons co-creator Sam Simon, demanded that Illinois-based Koch adopt new animal welfare standards to prevent future abuse. (more)
P.S. Last year, Tennessee legislators enacted what critics dubbed an “ag-gag” bill they charged was intended to prevent investigations similar to the Mercy for Animals undercover operations as well as one that targeted Tennessee Walking Horse industry abuse.
Republican Gov. Bill Haslam vetoed the bill after getting deluged with complaints, including a plea from country music star Carrie Underwood.
The allegations by animal protection group Mercy for Animals...
The Los Angeles-based group released covert video that it said was taken inside the Koch Chattanooga plant and another operation in Mississippi, complaining that workers are also cruelly throwing chickens and hiding cockroaches from federal inspectors.
The video, narrated by The Simpsons co-creator Sam Simon, demanded that Illinois-based Koch adopt new animal welfare standards to prevent future abuse. (more)
P.S. Last year, Tennessee legislators enacted what critics dubbed an “ag-gag” bill they charged was intended to prevent investigations similar to the Mercy for Animals undercover operations as well as one that targeted Tennessee Walking Horse industry abuse.
Republican Gov. Bill Haslam vetoed the bill after getting deluged with complaints, including a plea from country music star Carrie Underwood.
Memory Stick Voice Recorder - Patiently Listens 24/7, for 25 Days
This Voice-Activated USB drive looks and functions like an ordinary flash drive. Secretly, this storage device conceals hidden a microphone. Hang on a lanyard or slip into a pocket for discreet recording. Use this unit at the office, school, to covertly record voice as a secret shopper or investigator, or to simply record notes and interviews at school or work.
Voice-activation mode. The voice-activation feature allows you to avoid long hours of silent recording and save battery life. This unit can be on standby for up to 25 days waiting to pickup any voices you may hear.
Portable and easy to use. The flash drive needs no cables or batteries, making it perfect for the covert operative on the go. Recording is as simple as a touch of the button. Choose from normal recording or voice activation. ≈$100.00 (more) (user manual)
Why do I mention this?
So you will know what you're up against.
Voice-activation mode. The voice-activation feature allows you to avoid long hours of silent recording and save battery life. This unit can be on standby for up to 25 days waiting to pickup any voices you may hear.
Portable and easy to use. The flash drive needs no cables or batteries, making it perfect for the covert operative on the go. Recording is as simple as a touch of the button. Choose from normal recording or voice activation. ≈$100.00 (more) (user manual)
Why do I mention this?
So you will know what you're up against.
Speed, Instant Ticket... or, You Can Drive, But You Can't Hide
FutureWatch: Russia - 1200 complexes of photo and video registration will be installed in 381 sections of federal highways and regional roads located in the Moscow region. In particular, new equipment will be installed in almost every district and all major cities of the Moscow region, as well as in the smaller and greater Moscow Ring Road areas...
It is planned that the installation of photo and video registration systems will be conducted at the expense of an investor company, which, in turn, will receive a share of all fines issued for violation of traffic rules detected by cameras...
According to the authors of the idea, cameras will be able to register the majority of traffic violations, including speeding and driving on the oncoming lane. (more)
• Traffic cameras on steroids.
• Becomes operational just before self-driving vehicles, thus making this less necessary.
• Does the government has some other uses in mind? (Duh.)
• Will this surveillance network be adopted by other countries, too? (Duh.)
It is planned that the installation of photo and video registration systems will be conducted at the expense of an investor company, which, in turn, will receive a share of all fines issued for violation of traffic rules detected by cameras...
According to the authors of the idea, cameras will be able to register the majority of traffic violations, including speeding and driving on the oncoming lane. (more)
• Traffic cameras on steroids.
• Becomes operational just before self-driving vehicles, thus making this less necessary.
• Does the government has some other uses in mind? (Duh.)
• Will this surveillance network be adopted by other countries, too? (Duh.)
Wednesday, November 19, 2014
Everything You Wanted to Know About Cell Phone Tracking via Call Detail Records
What is Cellular Data Analysis?
 How is Cellular Data Analysis Used?
How is Cellular Data Analysis Used?
What about Triangulation?
Is There an Accurate Way to Track a Cell Phone Location?
Is cell tower tracking evidence junk science?
Is there a good use for cellular location evidence?
(answers here)
 How is Cellular Data Analysis Used?
How is Cellular Data Analysis Used?What about Triangulation?
Is There an Accurate Way to Track a Cell Phone Location?
Is cell tower tracking evidence junk science?
Is there a good use for cellular location evidence?
(answers here)
Fake Cell Tower Survey on Indiegogo
If there's somethin' strange in your neighborhood
Who ya gonna call (cellbusters)
If it's somethin' weird an it don't look good
Who ya gonna call (cellbusters)
 (more) (sing-a-long)
(more) (sing-a-long)
Who ya gonna call (cellbusters)
If it's somethin' weird an it don't look good
Who ya gonna call (cellbusters)
 (more) (sing-a-long)
(more) (sing-a-long)
Tuesday, November 18, 2014
Your Email is Hacked - Now What?
The State Department has suspended its unclassified email system in response to a suspected hacking attack.
The unprecedented shutdown on Friday was reportedly applied to give technicians an opportunity to repair possible damage, as well as to apply security improvements. (more)
But, what if it's your email? You don't have "technicians" to turn to. Techlicious to the rescue...
Step #1: Change your password.
Step #2: Reclaim your account.
Step #3: Enable two-factor authentication.
Step #4: Check your email settings.
Step #5: Scan your computer for malware.
Step #6: Find out what else has been compromised.
Step #7: Humbly beg for forgiveness from your friends.
Step #8: Prevent it from happening again.
Full details for each step are outlined here.
The unprecedented shutdown on Friday was reportedly applied to give technicians an opportunity to repair possible damage, as well as to apply security improvements. (more)
But, what if it's your email? You don't have "technicians" to turn to. Techlicious to the rescue...
Step #1: Change your password.
Step #2: Reclaim your account.
Step #3: Enable two-factor authentication.
Step #4: Check your email settings.
Step #5: Scan your computer for malware.
Step #6: Find out what else has been compromised.
Step #7: Humbly beg for forgiveness from your friends.
Step #8: Prevent it from happening again.
Full details for each step are outlined here.
Dark Hotel - Cleverly Engineered to Conduct Corporate Espionage
A new advanced persistent threat (APT),
known as DarkHotel, is now targeting C-level executives of major
businesses.
Instead of trying to compromise governments to steal state
secrets, Dark Hotel is cleverly engineered to conduct corporate
espionage, likely for a foreign state-sponsored group, utilizing poor
wireless hotel security - a rather clever technique for when business
leaders are staying in hotels...
Dragnet 2014 - "The IMSI Catcher Caper"
The Wall Street Journal has revealed details of a secret spy program.
The newspaper says the justice department is collecting data from thousands of cell phones at major airports across the country.
The U.S. Marshals Service operates airplanes with a device (IMSI Catcher) on board that tricks your phone into thinking it is a cell tower.
Phones are programmed to connect automatically to the strongest cell tower signal, which is usually this new device at the airport. When it does, it transmits your unique registration information.
The newspaper says the technology is supposed to locate cell phones linked to criminal suspects, but in the process the government is collecting data on thousands of other people as well. (more)
The newspaper says the justice department is collecting data from thousands of cell phones at major airports across the country.
The U.S. Marshals Service operates airplanes with a device (IMSI Catcher) on board that tricks your phone into thinking it is a cell tower.
Phones are programmed to connect automatically to the strongest cell tower signal, which is usually this new device at the airport. When it does, it transmits your unique registration information.
The newspaper says the technology is supposed to locate cell phones linked to criminal suspects, but in the process the government is collecting data on thousands of other people as well. (more)
New App to Detect Fake Cell Phone Towers
This is an Android-based project to detect and avoid fake base stations (IMSI-Catchers) in GSM/UMTS Networks.
Both law enforcement agencies and criminals use IMSI-Catchers, which are false mobile towers acting between the target mobile phone(s) and the service providers real towers. As such it is considered a Man In the Middle (MITM) attack. (more)
Both law enforcement agencies and criminals use IMSI-Catchers, which are false mobile towers acting between the target mobile phone(s) and the service providers real towers. As such it is considered a Man In the Middle (MITM) attack. (more)
From the No Free Lunch Files
An accused perv landlord charged with secretly filming a woman he’d set up in a rent-free Upper West Side pad pleaded not guilty to several felony counts Monday.
Eli Kadoch, 48, was indicted on 10 counts of unlawful surveillance after allegedly setting up spy cameras in the W. 82nd St. apartment of Aksana Kuzmitskaya, where he allegedly watched her in the nude repeatedly for six months beginning in January.
Kuzmitskaya is suing Kadoch and another landlord, Michel Kadoe — who has not been charged criminally — for allegedly taping her most intimate moments after giving her a rent-free apartment while she worked for them as a maid.
Kuzmitskaya says the secret footage included her showering, having sex and using the bathroom. Cameras sent live feeds to Kadoe and Kadoch’s laptops, the lawsuit says. (more)
Eli Kadoch, 48, was indicted on 10 counts of unlawful surveillance after allegedly setting up spy cameras in the W. 82nd St. apartment of Aksana Kuzmitskaya, where he allegedly watched her in the nude repeatedly for six months beginning in January.
Kuzmitskaya is suing Kadoch and another landlord, Michel Kadoe — who has not been charged criminally — for allegedly taping her most intimate moments after giving her a rent-free apartment while she worked for them as a maid.
Kuzmitskaya says the secret footage included her showering, having sex and using the bathroom. Cameras sent live feeds to Kadoe and Kadoch’s laptops, the lawsuit says. (more)
Monday, November 17, 2014
Kevin's Security Scrapbook - iPhone / iPad App - FREE
Get the latest
"Spy News from New York"
on your iPhone or iPad.
 The layout is beautiful, and the navigation is intuitive and easy. This is the most convenient way to read Kevin's Security Scrapbook.
The layout is beautiful, and the navigation is intuitive and easy. This is the most convenient way to read Kevin's Security Scrapbook. Download the app onto your device now.
Friday, November 14, 2014
Why the Valet Needs to be Background Checked, or A Cell Phone Key Machine
Your metal key can be duplicated just by snapping a photo of it with a cell phone.
Leaving your keys unsecured is like writing your passwords on post-it notes. If it can be seen, it can be stolen.
from Wired Magazine...
"My neighbor lives on the second floor of a Brooklyn walk-up, so when I came to his front door he tossed me a pair of keys rather than walk down the stairs to let me in. I opened the door, climbed the stairs, and handed his keys back to him. We chatted about our weekends. I drank a glass of water. Then I let him know that I would be back soon to gain unauthorized access to his home.
Less than an hour later, I owned a key to his front door.
What I didn’t tell my neighbor was that I spent about 30 seconds in the stairwell scanning his keys with software that would let me reproduce them with no specialized skills whatsoever."
Yikes! How did he do it?!?!
In this case, Key.Me made a key using the photos he took.
Spybusters Security Tip # 736: Add your keys to your private-parts list. Show them only to those you trust.
Leaving your keys unsecured is like writing your passwords on post-it notes. If it can be seen, it can be stolen.
- Have you ever left your keys with a valet or parking garage attendant?
- Does your administrative assistant leave keys for everything in an open desk?
- Every loan a key to a friend, even just for a minute?
from Wired Magazine...
"My neighbor lives on the second floor of a Brooklyn walk-up, so when I came to his front door he tossed me a pair of keys rather than walk down the stairs to let me in. I opened the door, climbed the stairs, and handed his keys back to him. We chatted about our weekends. I drank a glass of water. Then I let him know that I would be back soon to gain unauthorized access to his home.
Less than an hour later, I owned a key to his front door.
What I didn’t tell my neighbor was that I spent about 30 seconds in the stairwell scanning his keys with software that would let me reproduce them with no specialized skills whatsoever."
Yikes! How did he do it?!?!
In this case, Key.Me made a key using the photos he took.
Spybusters Security Tip # 736: Add your keys to your private-parts list. Show them only to those you trust.
Coca-Cola Guards Best-Kept Secret in US But Not 55 Laptops - An Employee Sues
Coca-Cola is facing a potential class-action lawsuit after one of the people whose personal data was on one of a clutch of laptops stolen from the company says he suffered identity theft as a result of the breach.
Laptops thefts are a common occurrence for most large organizations but the circumstances surrounding the loss of 55 laptops over a six-year period from the drinks giant’s Atlanta office and a bottling firm it acquired were always puzzling.
Made public on 24 January this year, it turned out that an employee, Thomas William Rogers III, had allegedly taken the machines without their loss being realized. The machines contained the records of 74,000 people, all current or former employees, including 18,000 revealing social security numbers. (more)
Moral - Encrypt your laptop data.
Laptops thefts are a common occurrence for most large organizations but the circumstances surrounding the loss of 55 laptops over a six-year period from the drinks giant’s Atlanta office and a bottling firm it acquired were always puzzling.
Made public on 24 January this year, it turned out that an employee, Thomas William Rogers III, had allegedly taken the machines without their loss being realized. The machines contained the records of 74,000 people, all current or former employees, including 18,000 revealing social security numbers. (more)
Moral - Encrypt your laptop data.
Update: A Police Commander's Wife, Their Unlicensed PI Business and Spyware...
CA - A Northern California woman has pleaded guilty to wiretapping a police officer and other people and to possessing spyware.
The U.S. Attorney's Office says Monday that in pleading guilty, Kristin Nyunt admitted that from 2010 to 2012 she used spy software she purchased online.
Federal prosecutors say the 40-year-old woman installed the software on cell phones and computers of several people she spied on, including a police officer. (more) (background)
The U.S. Attorney's Office says Monday that in pleading guilty, Kristin Nyunt admitted that from 2010 to 2012 she used spy software she purchased online.
Federal prosecutors say the 40-year-old woman installed the software on cell phones and computers of several people she spied on, including a police officer. (more) (background)
Labels:
amateur,
cell phone,
eavesdropping,
lawsuit,
PI,
police,
spyware,
wiretapping
73,012 Unsecured Security Cameras You Can Watch
A site linked to 73,012 unsecured security camera locations in 256 countries – all because they are using default passwords.
from the website...
"Sometimes administrator (possible you too) forgets to set the default password on security surveillance system, online camera or DVR. This site now contains access only to cameras without a password and it is fully legal. Such online cameras are available for all internet users. To browse cameras just select the country or camera type.
This site has been designed in order to show the importance of the security settings. To remove your public camera from this site and make it private the only thing you need to do is to change your camera default password." (more)
from the website...
"Sometimes administrator (possible you too) forgets to set the default password on security surveillance system, online camera or DVR. This site now contains access only to cameras without a password and it is fully legal. Such online cameras are available for all internet users. To browse cameras just select the country or camera type.
This site has been designed in order to show the importance of the security settings. To remove your public camera from this site and make it private the only thing you need to do is to change your camera default password." (more)
Wednesday, November 5, 2014
$92 Million Dollar Surveillance Fence Coming to the US Border...
Don't worry US taxpayers. It's not our fence, we're just the immigrants.
Canada - A massive intelligence-gathering network of RCMP video cameras, radar, ground sensors, thermal radiation detectors and more will be erected along the U.S.-Canada border in Ontario and Quebec by 2018, the Mounties said Tuesday.
The $92-million surveillance web, formally known as the Border Integrity Technology Enhancement Project, will be concentrated in more than 100 “high-risk” cross-border crime zones spanning 700 kilometres of eastern Canada, said Assistant Commissioner Joe Oliver, the RCMP’s head of technical operations.
The network will be linked to a state-of-the-art “geospatial intelligence and automated dispatch centre” that will, among other things, integrate the surveillance data, issue alerts for high-probability targets, issue “instant imagery” to officers on patrol and produce predictive analysis reports. (more)
 |
| "There's always a way, eh!" |
The $92-million surveillance web, formally known as the Border Integrity Technology Enhancement Project, will be concentrated in more than 100 “high-risk” cross-border crime zones spanning 700 kilometres of eastern Canada, said Assistant Commissioner Joe Oliver, the RCMP’s head of technical operations.
The network will be linked to a state-of-the-art “geospatial intelligence and automated dispatch centre” that will, among other things, integrate the surveillance data, issue alerts for high-probability targets, issue “instant imagery” to officers on patrol and produce predictive analysis reports. (more)
Weird World Bugging News...
Wait. What!?!? An eavesdropping organ transplant scandal, 47 wiretapping cops, carte blanche surveillance in the USA, SRG's self-licking surveillance ice cream cone, and a spy shop morphing into a pot shop! Too weird.
Taiwan - Taipei mayoral candidate Sean Lien (連勝文) said yesterday that his opponent Ko Wen-je (柯文哲) should drop out of the election if police are not able to confirm the existence of the alleged eavesdropping devices that Ko's election team claimed they discovered connected to their office phone; Lien added that Ko is only trying to divert attention away from his recent human organ transaction scandal. (more)
Turkey - Malatya Police Department launched an investigation on Wednesday into 47 police officers, who are allegedly affiliated with the Gülen Movement, for unlawful wiretapping charges. According to initial reports, the investigation encompasses the wiretapping of phone conversations during the past four years. (more)
US - A federal regulatory body is discussing a rule change Nov. 5 that would allow the FBI to conduct electronic surveillance of devices wherever they're located. (more)
UK - Security Research Group shares jumped 17% as the electronic surveillance and property services firm accompanied a significant increase in half-year earnings with a bullish full year outlook. Its Specialist Electronics unit, which sells IED detectors to the military and bugging devices to police forces, recorded an operating profit of £274,000, up from £7,000. The division was helped by a £268,000 deal with Australian homeland security services for its ‘SuperBroom’ handheld detectors (ironically, a bug detector). (more)
NV - Medical marijuana businesses are one step closer to opening up shop in the Silver State... MediFarm is closing in on a deal to buy The Spy Shop building in Midtown. (more)
Taiwan - Taipei mayoral candidate Sean Lien (連勝文) said yesterday that his opponent Ko Wen-je (柯文哲) should drop out of the election if police are not able to confirm the existence of the alleged eavesdropping devices that Ko's election team claimed they discovered connected to their office phone; Lien added that Ko is only trying to divert attention away from his recent human organ transaction scandal. (more)
Turkey - Malatya Police Department launched an investigation on Wednesday into 47 police officers, who are allegedly affiliated with the Gülen Movement, for unlawful wiretapping charges. According to initial reports, the investigation encompasses the wiretapping of phone conversations during the past four years. (more)
US - A federal regulatory body is discussing a rule change Nov. 5 that would allow the FBI to conduct electronic surveillance of devices wherever they're located. (more)
UK - Security Research Group shares jumped 17% as the electronic surveillance and property services firm accompanied a significant increase in half-year earnings with a bullish full year outlook. Its Specialist Electronics unit, which sells IED detectors to the military and bugging devices to police forces, recorded an operating profit of £274,000, up from £7,000. The division was helped by a £268,000 deal with Australian homeland security services for its ‘SuperBroom’ handheld detectors (ironically, a bug detector). (more)
NV - Medical marijuana businesses are one step closer to opening up shop in the Silver State... MediFarm is closing in on a deal to buy The Spy Shop building in Midtown. (more)
Labels:
business,
eavesdropping,
FBI,
government,
law,
weird,
wiretapping
Tuesday, November 4, 2014
Smart Televisions Highly Susceptible to Hacking via Radio Transmission
Researchers discover a
massive security flaw in smart TV’s that allow hackers to intercept data
broadcasts, insert malicious code, and transform the TV into an antenna
that infects all other Internet-connected devices in the household.
Once the television is infected, it seeks out all other devices connected to the router.
The attacks are untraceable as no source IP address or DNS server is ever presented, instead, hackers perform a classic “man-in-the-middle” attack using radio transmissions. The hijacking, which was discovered by Yossef Oren and Angelos Keromytis from the Network Security Lab at Columbia University, can be accomplished with as little as a $250 antenna. (more) (video)
Once the television is infected, it seeks out all other devices connected to the router.
The attacks are untraceable as no source IP address or DNS server is ever presented, instead, hackers perform a classic “man-in-the-middle” attack using radio transmissions. The hijacking, which was discovered by Yossef Oren and Angelos Keromytis from the Network Security Lab at Columbia University, can be accomplished with as little as a $250 antenna. (more) (video)
Rabbi Accused of Planting Mikvah SpyCams... Bails Out
Moving trucks are scheduled to show up at the Georgetown home of Rabbi Barry Freundel, according to signs posted in front of his home on O Street, not far from the Kesher Israel synagogue that provided the house for its longtime religious leader.

Freundel was arrested October 14 and charged with six counts of voyeurism for allegedly hiding video cameras in the synagogue’s mikvah, a ritual bath, to record women as they undressed and showered before entering. Police officers were seen carting computers and hard drives out of Freundel’s house on the day of the arrest.
Freundel, 62, pleaded not guilty and was released on his own recognizance, while police and prosecutors investigate videos and forensic evidence. (more) (back story)

Freundel was arrested October 14 and charged with six counts of voyeurism for allegedly hiding video cameras in the synagogue’s mikvah, a ritual bath, to record women as they undressed and showered before entering. Police officers were seen carting computers and hard drives out of Freundel’s house on the day of the arrest.
Freundel, 62, pleaded not guilty and was released on his own recognizance, while police and prosecutors investigate videos and forensic evidence. (more) (back story)
10 Ways to Spy on Competition (Like They’re Spying On You)
Knowing about your competition has always been important in the world of
business. With the Internet, this marketing intelligence has never been
easier to find out, but it does take discipline and planning...
Actions
Actions
- Follow them. (how-to details in the main article)
- Mystery shop.
- Ask a question.
- Call with a complaint.
- Explore ad monitoring tools.
- Find their backlinks.
- Track their website traffic.
- Find out what customers are saying.
- Determine their social media presence.
- Track their technology.
- Explore web site content changes.
Pest Control Tech Arrested for... Planting Bugs
You can't make this stuff up...
IA - Red Oak Police say 38-year-old Aaron Theodore Johnson was arrested Monday for electronic and/or mechanical eavesdropping, a serious misdemeanor, and felon in possession of a firearm, a class D felony. Johnson is charged in connection with an investigation that began at around 11:10 Monday morning, when police received a complaint from 29-year-old Jessica Hale - regarding a recording device found in her residence...
Upon further investigation, authorities later found a second device in the residence's bedroom. The victim told police that the only person granted access to her residence was a pest control technician. Later in the day, a search warrant was obtained for Johnson's residence in the 2700 block of State Highway 48--which is also the location of RMPKA Pest Control Services. (more) (video report)
IA - Red Oak Police say 38-year-old Aaron Theodore Johnson was arrested Monday for electronic and/or mechanical eavesdropping, a serious misdemeanor, and felon in possession of a firearm, a class D felony. Johnson is charged in connection with an investigation that began at around 11:10 Monday morning, when police received a complaint from 29-year-old Jessica Hale - regarding a recording device found in her residence...
Upon further investigation, authorities later found a second device in the residence's bedroom. The victim told police that the only person granted access to her residence was a pest control technician. Later in the day, a search warrant was obtained for Johnson's residence in the 2700 block of State Highway 48--which is also the location of RMPKA Pest Control Services. (more) (video report)
Happy Feet: Espionage can look adorable, too.
Just look at a remote-controlled robot disguised as a penguin that interacts with Emperor penguins in Antarctica.
Scientists are using the fake baby penguin on four wheels to get closer to the colony and collect health and population research...
The international team tested the rover, with the chick and without it, and reported in the journal Nature Methods Sunday that both versions caused less anxiety than humans... (more) (dance-a-long)
Scientists are using the fake baby penguin on four wheels to get closer to the colony and collect health and population research...
The international team tested the rover, with the chick and without it, and reported in the journal Nature Methods Sunday that both versions caused less anxiety than humans... (more) (dance-a-long)
Get ready for a 'Mystery Science Theater' streaming marathon
Football schmootball. Instead of watching NFL teams throw the pigskin around this Thanksgiving, why not watch a "Mystery Science Theater 3000" marathon with new intros by the series creator? (more)
The Official Spybuster sticker is back!
Our beautiful, 4 inch, heavy vinyl Official Spybuster sticker is back! This was a limited edition give-a-way to our clients in 2011. Use it to let everyone know you support privacy.
The printing experts at Stickermule now have it for sale in their Marketplace.
If spying by the NSA, FBI, CIA, TSA, GCHQ, MI5, MI6, other government spies, your significant other, or your parents concerns you, sticker it to them.
If you are in Homeland Security, the NSA, FBI, CIA, GCHQ, MI5, MI6 – protecting us against spies (thank you) – sticker it to them.
Either way, proudly declare, "I'm mad as Hell, and I am not going to take it anymore!"
Looks great on a white coffee cup.
 |
| 4 inch, heavy vinyl |
If spying by the NSA, FBI, CIA, TSA, GCHQ, MI5, MI6, other government spies, your significant other, or your parents concerns you, sticker it to them.
If you are in Homeland Security, the NSA, FBI, CIA, GCHQ, MI5, MI6 – protecting us against spies (thank you) – sticker it to them.
Either way, proudly declare, "I'm mad as Hell, and I am not going to take it anymore!"
Looks great on a white coffee cup.
Monday, November 3, 2014
China Folk Counterespionage Manual
“On the Internet, nobody knows you’re a dog.” Or an American spy. Or a “hostile foreign force.” So says the “China Folk Counterespionage Manual,” a “how to spot a spy” guide circulating on the Internet.
The manual, whose origin is murky, first emerged several years ago and has recently enjoyed a renaissance in popularity on social media sites. It offers Chinese citizens tips on how to detect spies in their midst. It was even cited in Global Times, a state newspaper, in late August following the detention of Kevin and Julia Garratt, a Canadian couple who ran a cafe in Dandong, on the North Korean border, on suspicion of stealing military secrets. In an infographic, the newspaper described them as examples of possible foreign spies masquerading as “ordinary citizens.”
The manual might be something more suited for a James Bond movie if it weren’t for the government’s own new emphasis on rooting out “foreign spies,” demonstrated on Saturday when President Xi Jinping signed an updated national security law, named the Counterespionage Law. (more)
 |
| Click to enlarge. |
The manual might be something more suited for a James Bond movie if it weren’t for the government’s own new emphasis on rooting out “foreign spies,” demonstrated on Saturday when President Xi Jinping signed an updated national security law, named the Counterespionage Law. (more)
Saturday, November 1, 2014
China Passes a Counterespionage Law
China passed a counterespionage law on Saturday aimed at tightening state security and helping build a “comprehensive’’ national security system, state media reported.
The law will allow authorities to seal or seize any property linked to activities deemed harmful to the country, the Xinhua news agency said.
Authorities can also ask organizations or individuals to stop or modify any behavior regarded as damaging to China’s interests, Xinhua said. Refusal to comply would allow enforcement agencies to confiscate properties.
Possession of espionage equipment, as defined by the state security department, had also been made illegal, Xinhua said. The news agency gave no further details. (more) (more)
The law will allow authorities to seal or seize any property linked to activities deemed harmful to the country, the Xinhua news agency said.
Authorities can also ask organizations or individuals to stop or modify any behavior regarded as damaging to China’s interests, Xinhua said. Refusal to comply would allow enforcement agencies to confiscate properties.
Possession of espionage equipment, as defined by the state security department, had also been made illegal, Xinhua said. The news agency gave no further details. (more) (more)
Subscribe to:
Posts (Atom)