MD -
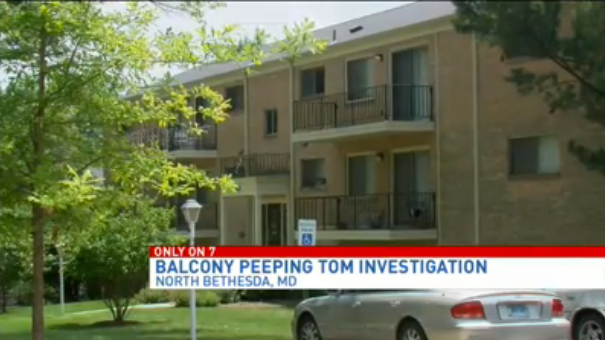
Imagine living on the third floor of your condominium building and glancing outside to find a camera looking back. That is exactly what a woman told police she saw, and now her downstairs neighbor is facing multiple criminal charges.
According to police, Donald Beard, 60,
repeatedly attached a camera to a long metal pole. Beard would then walk onto his second floor balcony... and hoist the pole, camera rolling, to spy on the woman who lived upstairs.
Around 10 p.m. one night... the victim looked outside her living room window and saw a metal pole swinging back-and-forth. A camera was attached, recording her every move. She immediately called police...
While searching Beard's computers, external hard drives, flash cards, cell phones, tablets, cameras, and other electronic devices,
detectives say they uncovered 16 individual videos of the victim. One clip showed the middle-aged women topless.
As for a motive, Beard reportedly told police his unique surveillance mission was "for investigative purposes", claiming his neighbor was spending time with married men and he wanted to catch her in the act...
Police say Beard also kept an audio journal of the victim's daily activities. more video