NY - Embattled Windham Supervisor Stacy M. Post is facing additional charges in a six-count indictment handed up by a Greene County grand jury.
Post’s second indictment cites alleged illegal activities between Feb. 22 and March 3, 2014, at the Windham Town Hall by the supervisor and former police chief. The first indictment was released in February, after her arrest by state police on Jan. 12...
The most recent indictment charges Post with installing video and audio surveillance software and hardware on her office computer “for the purpose of eavesdropping on individuals without their knowledge or consent” and with using eavesdropping equipment in her possession to eavesdrop on town employee Cynthia Nelson, former town employee Bette Rhoades, Town Clerk Bonnie Poehmel and Councilman Wayne Van Valin between Feb. 25 and March 3, 2014. more
Sunday, November 29, 2015
Saturday, November 28, 2015
Spy for Art's Sake
Spy vs. Spy: Tech-Savvy Swiss Duo Bitnik Refines the Art of Espionage
‘I’ve hijacked your surveillance camera. How about a game of chess?” The words filled a closed-circuit television screen that only seconds before had shown commuters in London’s Charing Cross station.
Whichever security guard read the message soon saw it replaced by a chessboard and the words: “You are white. I am black. Call me or text me to make your move. This is my phone number: 075 8246 0851.”
In the heart of the world’s most surveilled city, two artists were registering their polite protest with the help of a laptop and an interfering transmitter. Carmen Weisskopf and Domagoj Smoljo, a Swiss team known as !Mediengruppe Bitnik, have been co-opting the spy’s arsenal to practice their own, artistic style of counter-espionage...
Artists and spies are loners, operating on the margins. They observe, gather intelligence, surgically intervene, and detect and disseminate artifice. They try to stay ahead of everyone else. more
‘I’ve hijacked your surveillance camera. How about a game of chess?” The words filled a closed-circuit television screen that only seconds before had shown commuters in London’s Charing Cross station.
Whichever security guard read the message soon saw it replaced by a chessboard and the words: “You are white. I am black. Call me or text me to make your move. This is my phone number: 075 8246 0851.”
In the heart of the world’s most surveilled city, two artists were registering their polite protest with the help of a laptop and an interfering transmitter. Carmen Weisskopf and Domagoj Smoljo, a Swiss team known as !Mediengruppe Bitnik, have been co-opting the spy’s arsenal to practice their own, artistic style of counter-espionage...
Artists and spies are loners, operating on the margins. They observe, gather intelligence, surgically intervene, and detect and disseminate artifice. They try to stay ahead of everyone else. more
"Tell me all your secrets," said Barbie, in an unusually deep voice.
The new 'Hello Barbie' doll has come under scrutiny after security experts warned it could be exploited by hackers to spy on young children.
The doll is the 'world's first' interactive doll and has speech recognition and WiFi connectivity so that it can store what owners like and dislike, which manufacturer Mattel says will give everyone a 'unique experience' with the toy...
Bosses and designers behind the new Barbie have come out and defended the doll, saying that it is safe to use. more
The doll is the 'world's first' interactive doll and has speech recognition and WiFi connectivity so that it can store what owners like and dislike, which manufacturer Mattel says will give everyone a 'unique experience' with the toy...
Bosses and designers behind the new Barbie have come out and defended the doll, saying that it is safe to use. more
Affairs of Spy Pairs... and more
- Thousands Protest Arrest of 2 Turkish Journalists on Spying Charges more
- 2 Kenyans Arrested for Spying for Iran more
- AQIM Islamists say killed two men for spying for France more
- Two pensioners appear in court charged with spying on allotment holders in Stirling more

- More than 10 Japanese detained in China for spying since 2012 more
Thursday, November 26, 2015
Vintage Spy Camera Auction in Hong Kong
An incredible archive of rare vintage spy cameras that would rival James Bond's own collection has emerged for sale for £400,000.
Among the rarities is one of only two existing examples of the Lucky Strike Spy Camera developed for the US Signal Corps between 1949 and 1950. The camera, made by the Mast Development Corp, was built to fit inside the outer wrapper from a packet of Lucky Strike cigarettes. Despite its size it was capable of taking 18 x 16mm still photographs with varying shutter speeds, but ultimately it was rejected. It is worth around £43,000. more
Among the rarities is one of only two existing examples of the Lucky Strike Spy Camera developed for the US Signal Corps between 1949 and 1950. The camera, made by the Mast Development Corp, was built to fit inside the outer wrapper from a packet of Lucky Strike cigarettes. Despite its size it was capable of taking 18 x 16mm still photographs with varying shutter speeds, but ultimately it was rejected. It is worth around £43,000. more
Microsoft Makes Windows 10 Automatic Spying Worse - Update
When Windows 10 was released, many people were up in arms over the operating system’s ability to constantly track how users were interacting with it and would send that information back to Microsoft.
With the first major update for Windows 10 that came out earlier this month, Microsoft has seemingly removed Diagnostics Tracking Service, also known as DiagTrack, which was responsible for the tracking. But it turns out the company has just renamed the service. more
Those who don’t want Windows 10 to constantly send their data back to Microsoft, fear not. There’s a way to disable the service. Forbes has released instructions on how to do so:
With the first major update for Windows 10 that came out earlier this month, Microsoft has seemingly removed Diagnostics Tracking Service, also known as DiagTrack, which was responsible for the tracking. But it turns out the company has just renamed the service. more
Those who don’t want Windows 10 to constantly send their data back to Microsoft, fear not. There’s a way to disable the service. Forbes has released instructions on how to do so:
- Hold down the Windows key and tap the R key
- In the box that opens type ‘services.msc’ and press the Enter key
- In the ‘Services (Local)’ section locate ‘Connected User Experiences and Telemetry’ and double-click it
- In the ‘Service status’ section click ‘Stop’
- Under the ‘Startup type’ drop down menu select ‘Disabled’ and then confirm this and close the window by clicking ‘OK’
Privacy Journal's "Compilation of State and Federal Privacy Laws" - Updated
The Compilation of State and Federal Privacy Laws book
cites and describes more than 600 state and federal laws affecting the confidentiality of personal information and electronic surveillance.
The laws are listed by state, grouped in categories like medical, credit, financial, security breaches, tracking technologies, employment, government, school records, Social Security numbers, marketing, telephone privacy and many more. Canadian laws too.
The 2015 Supplement to Privacy Journal's "Compilation of State and Federal Privacy Laws" (2013) has just been published, adding 20 more laws enacted by states in the past 12 months.
cites and describes more than 600 state and federal laws affecting the confidentiality of personal information and electronic surveillance.
The laws are listed by state, grouped in categories like medical, credit, financial, security breaches, tracking technologies, employment, government, school records, Social Security numbers, marketing, telephone privacy and many more. Canadian laws too.
The 2015 Supplement to Privacy Journal's "Compilation of State and Federal Privacy Laws" (2013) has just been published, adding 20 more laws enacted by states in the past 12 months.
Wednesday, November 25, 2015
How Browser Extensions Steal Logins & Browsing Habits; Conduct Corporate Espionage
via boingboing.com
Seemingly harmless browser extensions that generate emojis, enlarge thumbnails, help you debug Javascript errors and other common utilities routinely run secret background processes that collect and retransmit your login credentials, private URLs that grant access to sensitive files, corporate secrets, full PDFs and other personally identifying, potentially compromising data.
Many extensions conduct surveillance without any notification at all, but some do legal backflips to cover up their activities -- characterizing your installation of the extension as explicit permission to spy; pretending that URLs are by nature anonymous and so on. The data is aggregated and sold to unnamed third parties, reputedly for $0.04/user/month. Many of the spying extensions have more than a million users. One of the extensions identified as conducting secret spying advertises itself as a privacy-enhancing tool (!).
Detectify Labs have posted a technical explanation of how Chrome extensions conduct surveillance, and note near the end of their analysis that Firefox extensions are just as prone to spying. more
Seemingly harmless browser extensions that generate emojis, enlarge thumbnails, help you debug Javascript errors and other common utilities routinely run secret background processes that collect and retransmit your login credentials, private URLs that grant access to sensitive files, corporate secrets, full PDFs and other personally identifying, potentially compromising data.
Many extensions conduct surveillance without any notification at all, but some do legal backflips to cover up their activities -- characterizing your installation of the extension as explicit permission to spy; pretending that URLs are by nature anonymous and so on. The data is aggregated and sold to unnamed third parties, reputedly for $0.04/user/month. Many of the spying extensions have more than a million users. One of the extensions identified as conducting secret spying advertises itself as a privacy-enhancing tool (!).
Detectify Labs have posted a technical explanation of how Chrome extensions conduct surveillance, and note near the end of their analysis that Firefox extensions are just as prone to spying. more
Microsoft Makes Windows 10 Automatic Spying Worse
Earlier this month Microsoft finally went on record admitting that automatic spying within Windows 10 cannot be stopped.
This sparked a lot of outrage and with ‘Threshold 2’ it appeared Microsoft had done a sharp U-turn because the background service at the heart tracking (the ‘Diagnostics Tracking Service’ aka ‘DiagTrack’) appeared to have been removed. Critics celebrated and it was another well deserved pat on the back for Microsoft.
Except it turns out Microsoft had just been very sneaky. What Tweakhound discovered and was subsequently confirmed by BetaNews, is Microsoft simply renamed DiagTrack. It is now called the ‘Connected User Experiences and Telemetry Service’ – which is both a) deliberately vague, and b) misleading (don’t ‘Connected User Experiences’ sound great). more
This sparked a lot of outrage and with ‘Threshold 2’ it appeared Microsoft had done a sharp U-turn because the background service at the heart tracking (the ‘Diagnostics Tracking Service’ aka ‘DiagTrack’) appeared to have been removed. Critics celebrated and it was another well deserved pat on the back for Microsoft.
Except it turns out Microsoft had just been very sneaky. What Tweakhound discovered and was subsequently confirmed by BetaNews, is Microsoft simply renamed DiagTrack. It is now called the ‘Connected User Experiences and Telemetry Service’ – which is both a) deliberately vague, and b) misleading (don’t ‘Connected User Experiences’ sound great). more
Two Spies Out This Week
Ronald Pelton, former National Security Agency employee convicted of selling defense and communication secrets he gained during his career has been released from federal custody 30 years after his arrest. more
Jonathan J. Pollard was released on parole from federal prison on Friday after serving 30 years of a life sentence for violations of the Espionage Act. more
Jonathan J. Pollard was released on parole from federal prison on Friday after serving 30 years of a life sentence for violations of the Espionage Act. more
FutureWatch: No Lens Spycams Thinner than a Dime
How thin can a camera be? Very, say Rice University researchers who have developed patented prototypes of their technological breakthrough.
FlatCam, invented by the Rice labs of electrical and computer engineers Richard Baraniuk and Ashok Veeraraghavan, is little more than a thin sensor chip with a mask that replaces lenses in a traditional camera.
"We can make curved cameras, or wallpaper that's actually a camera," says Richard Baraniuk, professor of electrical and computer engineering at Rice University. "You can have a camera on your credit card or a camera in an ultrathin tablet computer."
Making it practical are the sophisticated computer algorithms that process what the sensor detects and converts the sensor measurements into images and videos. more
FlatCam, invented by the Rice labs of electrical and computer engineers Richard Baraniuk and Ashok Veeraraghavan, is little more than a thin sensor chip with a mask that replaces lenses in a traditional camera.
"We can make curved cameras, or wallpaper that's actually a camera," says Richard Baraniuk, professor of electrical and computer engineering at Rice University. "You can have a camera on your credit card or a camera in an ultrathin tablet computer."
Making it practical are the sophisticated computer algorithms that process what the sensor detects and converts the sensor measurements into images and videos. more
Saturday, November 21, 2015
Ads Go from Subliminal to Ultrasonic - "PSSST... Any devices nearby?"
Privacy advocates are warning federal authorities of a new threat that uses inaudible, high-frequency sounds to surreptitiously track a person's online behavior across a range of devices, including phones, TVs, tablets, and computers.
The ultrasonic pitches are embedded into TV commercials or are played when a user encounters an ad displayed in a computer browser. While the sound can't be heard by the human ear, nearby tablets and smartphones can detect it. When they do, browser cookies can now pair a single user to multiple devices and keep track of what TV commercials the person sees, how long the person watches the ads, and whether the person acts on the ads by doing a Web search or buying a product.
Cross-device tracking raises important privacy concerns, the Center for Democracy and Technology wrote in recently filed comments to the Federal Trade Commission. The FTC has scheduled a workshop on Monday to discuss the technology. Often, people use as many as five connected devices throughout a given day—a phone, computer, tablet, wearable health device, and an RFID-enabled access fob. Until now, there hasn't been an easy way to track activity on one and tie it to another.
"As a person goes about her business, her activity on each device generates different data streams about her preferences and behavior that are siloed in these devices and services that mediate them," CDT officials wrote. "Cross-device tracking allows marketers to combine these streams by linking them to the same individual, enhancing the granularity of what they know about that person." more
The ultrasonic pitches are embedded into TV commercials or are played when a user encounters an ad displayed in a computer browser. While the sound can't be heard by the human ear, nearby tablets and smartphones can detect it. When they do, browser cookies can now pair a single user to multiple devices and keep track of what TV commercials the person sees, how long the person watches the ads, and whether the person acts on the ads by doing a Web search or buying a product.
Cross-device tracking raises important privacy concerns, the Center for Democracy and Technology wrote in recently filed comments to the Federal Trade Commission. The FTC has scheduled a workshop on Monday to discuss the technology. Often, people use as many as five connected devices throughout a given day—a phone, computer, tablet, wearable health device, and an RFID-enabled access fob. Until now, there hasn't been an easy way to track activity on one and tie it to another.
"As a person goes about her business, her activity on each device generates different data streams about her preferences and behavior that are siloed in these devices and services that mediate them," CDT officials wrote. "Cross-device tracking allows marketers to combine these streams by linking them to the same individual, enhancing the granularity of what they know about that person." more
FBI Investigates Drone Crash Outside NJ Refinery
Industrial espionage, terrorists, or innocent hobbyist? You decide.
The FBI and local police are investigating after a drone fell out of the sky and crashed into a truck in New Jersey on Wednesday morning.
As CBS2’s Christine Sloan reported, of particular concern to authorities is that the incident happened on a road just outside a Phillips 66 refinery in Linden.
The driver of the truck apparently got out and had words with the operator of the drone, who took off, investigators said.
John Victor Jacobson, head of New Jersey-based Drone Service Systems, said he cannot think of a good reason to fly one of these air crafts in such a sensitive area. more
This location is also very close to Newark Airport, to the South of its runway flight path.
The FBI and local police are investigating after a drone fell out of the sky and crashed into a truck in New Jersey on Wednesday morning.
As CBS2’s Christine Sloan reported, of particular concern to authorities is that the incident happened on a road just outside a Phillips 66 refinery in Linden.
The driver of the truck apparently got out and had words with the operator of the drone, who took off, investigators said.
John Victor Jacobson, head of New Jersey-based Drone Service Systems, said he cannot think of a good reason to fly one of these air crafts in such a sensitive area. more
This location is also very close to Newark Airport, to the South of its runway flight path.
The New Cowboy Spy
From the Ol' Timer...
"Howdy, partner. There is a new surveillance risk in town, and he be a-aimin' at you.
Worried about board meeting eavesdroppers; business espionage desperados, and bad egg buggists? Darn tootin' you are, and you've hired the local TSCM-slinger to keep you above snakes. Does a fine job of it, too.
Oh, about Mr. New Surveillance Risk. He ain't no fancy foreign spy, crow-bait competitor, or even a chiseler employee. No sir, bub, he's the cow chip of the spy world; a tenderfoot with a mighty powerful weapon. A sneaky dude who'll leave you in court, emptyin' your wallet faster than greased lightning. Yes sir'ee, he's the Workplace Video Voyeur, and he ain't a-playing according to Hoyle."
Thanks for the warning, old timer. You're right as rain. I know. I've run into a couple of these hombres during my time on the trail. Let me tell you a story...
My Fortune 50 client called me a few months ago. Seems, an employee found a spy camera hidden in one of their restrooms. The news media caught wind of it and jumped all over the story. It was an embarrassing mess. It may also be an expensive mess if the people caught by the camera decide to sue.
We had been inspecting their boardroom, executive offices and off-site meeting locations for over two decades. This due diligence resulted in the capture of one spy, on-site (a competitor's employee), one wireless bug, and several general information security loopholes which they quickly patched up.
Nobody expected a bathroom video voyeur, however. Yet this incident held promise of greater damage than any corporate espionage attack. In addition to being costly in dollars and damaging reputation-wise, a video voyeur attack directly affects employee morale. Its hard to put a price on that.
The company asked me for help. They needed to prevent future incidents. Made sense. After one incident, they could face "foreseeability," a legal term. In short, it is the theory that if something happens once you become aware it could happen again. If you do nothing to correct the situation, and it does happen again, you are considered negligent. Sexual harassment in the workplace also plays into future incidents. This makes for an expensive mix in court.
In addition to protecting themselves, the company really wanted to assure their employees that they were taking the situation very seriously.
We discussed several possible solutions.
Sending our Technical Surveillance Countermeasures (TSCM) team to inspect all their restrooms and locker rooms (worldwide) was impractical, of course. What we eventually decided upon was a three-fold strategy, which turned out to be very cost-effective.
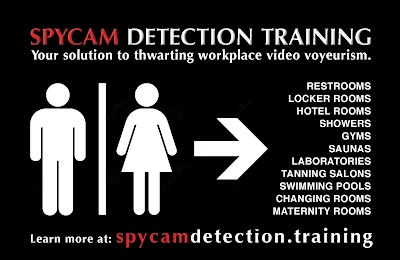 This company-wide solution cost them about as much as a one-day sweep of their executive offices, and it will be used at all their locations, for years to come.
This company-wide solution cost them about as much as a one-day sweep of their executive offices, and it will be used at all their locations, for years to come.
Other companies have not been so lucky. Another New York City firm paid two employees one million dollars apiece in connection with their video voyeur incident.
Yup, ol' timer. The times are changing. Companies need to start watching their butts, when it comes to butt watchers.
~Kevin
"Howdy, partner. There is a new surveillance risk in town, and he be a-aimin' at you.
Worried about board meeting eavesdroppers; business espionage desperados, and bad egg buggists? Darn tootin' you are, and you've hired the local TSCM-slinger to keep you above snakes. Does a fine job of it, too.
Oh, about Mr. New Surveillance Risk. He ain't no fancy foreign spy, crow-bait competitor, or even a chiseler employee. No sir, bub, he's the cow chip of the spy world; a tenderfoot with a mighty powerful weapon. A sneaky dude who'll leave you in court, emptyin' your wallet faster than greased lightning. Yes sir'ee, he's the Workplace Video Voyeur, and he ain't a-playing according to Hoyle."
Thanks for the warning, old timer. You're right as rain. I know. I've run into a couple of these hombres during my time on the trail. Let me tell you a story...
My Fortune 50 client called me a few months ago. Seems, an employee found a spy camera hidden in one of their restrooms. The news media caught wind of it and jumped all over the story. It was an embarrassing mess. It may also be an expensive mess if the people caught by the camera decide to sue.
We had been inspecting their boardroom, executive offices and off-site meeting locations for over two decades. This due diligence resulted in the capture of one spy, on-site (a competitor's employee), one wireless bug, and several general information security loopholes which they quickly patched up.
Nobody expected a bathroom video voyeur, however. Yet this incident held promise of greater damage than any corporate espionage attack. In addition to being costly in dollars and damaging reputation-wise, a video voyeur attack directly affects employee morale. Its hard to put a price on that.
The company asked me for help. They needed to prevent future incidents. Made sense. After one incident, they could face "foreseeability," a legal term. In short, it is the theory that if something happens once you become aware it could happen again. If you do nothing to correct the situation, and it does happen again, you are considered negligent. Sexual harassment in the workplace also plays into future incidents. This makes for an expensive mix in court.
In addition to protecting themselves, the company really wanted to assure their employees that they were taking the situation very seriously.
We discussed several possible solutions.
Sending our Technical Surveillance Countermeasures (TSCM) team to inspect all their restrooms and locker rooms (worldwide) was impractical, of course. What we eventually decided upon was a three-fold strategy, which turned out to be very cost-effective.
- A review of their Recording in the Workplace Policy for completeness and effectiveness. This policy covers all aspects of recording anything to do with the company (audio, video and data). Most companies don't even have policy.
- Development of an on-line spycam detection training program for their local facilities managers and security staff. This would professionally prepare them to conduct simple periodic inspections of the 'expectation of privacy' areas on company property. An inspection log and photos would be kept on file. The log documents inspection dates and results. The photos document changes in the area over time. Both may be used to show due diligence in court.
- A short on-line spycam awareness video was produced for all employees to view. This was placed on the company intranet. It explained the growing social problem of video voyeurism, the steps the company is taking to prevent the problem in the workplace, and self-protection tips employees can use to protect themselves and their families, wherever they are.
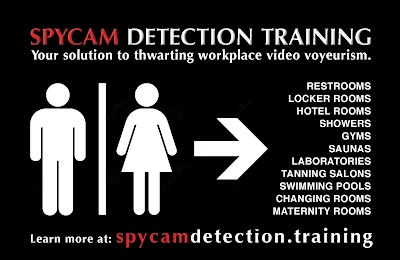 This company-wide solution cost them about as much as a one-day sweep of their executive offices, and it will be used at all their locations, for years to come.
This company-wide solution cost them about as much as a one-day sweep of their executive offices, and it will be used at all their locations, for years to come.
Other companies have not been so lucky. Another New York City firm paid two employees one million dollars apiece in connection with their video voyeur incident.
Yup, ol' timer. The times are changing. Companies need to start watching their butts, when it comes to butt watchers.
~Kevin
Wednesday, November 18, 2015
A Survey of Behind the Scenes Personal Data Sharing to Third Parties by Mobile Apps
A Survey of Behind the Scenes Personal Data Sharing to Third Parties by Mobile Apps
Tested - 110 popular, free Android and iOS apps to look for apps that shared personal, behavioral, and location data with third parties
73% of Android apps shared personal information such as email address with third parties, and 47% of iOS apps shared geo-coordinates and other location data with third parties
93% of Android apps tested connected to a mysterious domain, safemovedm.com, likely due to a background process of the Android phone
A significant proportion of apps share data from user inputs such as personal information or search terms with third parties without Android or iOS requiring a notification to the user more
 |
| Click to Enlarge |
73% of Android apps shared personal information such as email address with third parties, and 47% of iOS apps shared geo-coordinates and other location data with third parties
93% of Android apps tested connected to a mysterious domain, safemovedm.com, likely due to a background process of the Android phone
A significant proportion of apps share data from user inputs such as personal information or search terms with third parties without Android or iOS requiring a notification to the user more
Subscribe to:
Comments (Atom)