Washington, DC - Waves of civil servants, military and law enforcement officers, business people, students, diplomats and tourists saturate the city.
That is the scene on a typical weekday in the world’s most powerful city — whose business revolves around secret meetings, information and documents. Woven into that orderly bedlam are sophisticated networks of foreign nationals whose sole purpose is to steal secrets.
They are spies.
According to the International Spy Museum in D.C., an educational and historical center of U.S. intelligence documentation and artifacts, there are “more than 10,000 spies in Washington.”
While there may be some quibbling about the actual numbers, the FBI agrees with the premise.
“It’s unprecedented — the threat from our foreign adversaries, specifically China on the economic espionage and the espionage front,” said Brian Dugan, Assistant Special Agent in Charge for Counterintelligence with the FBI’s Washington Field Office.
As this unparalleled wave of international espionage, aided by technology, explodes in D.C., the variety of spies has diversified, as well.
“A spy is nondescript. A spy is going to be someone that’s going to be a student in school, a visiting professor, your neighbor. It could be a colleague or someone that shares the soccer field with you,” Dugan said. more
Showing posts with label information security. Show all posts
Showing posts with label information security. Show all posts
Wednesday, June 19, 2019
Tuesday, June 18, 2019
Security Message Screen Savers for Business Computers and Laptops (FREE)
Three stock Security Message Screen Savers to choose from. Five rotating screens with the top five information security best practices employees can implement themselves.
FREE to use as-is with "Logo goes here" removed, or can be customized with your business logo.
Need to customize? Contact us for details and cost.
- Reminders work.
- Put your idle computer screens to work as your security helpers.
- Three backgrounds to choose from, or commission custom screens.
 |
| Click link to see these information security screensavers in action. |
Need to customize? Contact us for details and cost.
Monday, May 20, 2019
FutureWatch: New Mobile App Fends off Espionage Attacks
Innovative technology from the Karlsruhe Institute of Technology (KIT) and the FZI Research Center for Computer Science
can put an end to espionage on our cell phones.....
For example, it is possible to give apps wrapped in AVARE access to the contacts in the address book, but not to all of the stored information...
In addition, AVARE can extend the location information to a radius of several kilometers and disguise the exact location. Thus, a weather app can continue to provide reliable forecasts without knowing the exact location of the user...
The AVARE code is available as open source software on the AVARE website and the scientists hope that their program will be taken up by other developers who will help to extend the current beta version to a version 1.0. more video (cartoon)
For example, it is possible to give apps wrapped in AVARE access to the contacts in the address book, but not to all of the stored information...
In addition, AVARE can extend the location information to a radius of several kilometers and disguise the exact location. Thus, a weather app can continue to provide reliable forecasts without knowing the exact location of the user...
The AVARE code is available as open source software on the AVARE website and the scientists hope that their program will be taken up by other developers who will help to extend the current beta version to a version 1.0. more video (cartoon)
Tuesday, May 14, 2019
Police Can't Take Suspect's Garbage Without a Warrant, in Oregon
The Oregon Supreme Court on Thursday disagreed with more than 50 years
of state case law by ruling that Oregonians retain a privacy interest in
the garbage they leave on the curb for pick-up. That means police can’t
search the garbage without a warrant even after a truck hauls it away...
The majority opinion noted that even the U.S. Supreme Court has said Americans don’t have a reasonable expectation of privacy “in trash left for collection in an area accessible to the public.” But the U.S. Supreme Court also said individual states are free to impose “more stringent constraints on police” based on their own constitutions.
Thursday’s ruling applies to curbside refuse collected from private homes. It doesn’t appear to apply to trash thrown in public garbage cans in public places. more
The majority opinion noted that even the U.S. Supreme Court has said Americans don’t have a reasonable expectation of privacy “in trash left for collection in an area accessible to the public.” But the U.S. Supreme Court also said individual states are free to impose “more stringent constraints on police” based on their own constitutions.
Thursday’s ruling applies to curbside refuse collected from private homes. It doesn’t appear to apply to trash thrown in public garbage cans in public places. more
Monday, April 8, 2019
From Those Wonderful Folks Who Brought You APT - Manditory Free Pen-Testing
New provisions made to China's Cybersecurity Law gives state agencies the legal authority to remotely conduct penetration testing on any internet-related business operating in China, and even copy and later share any data government officials find on inspected systems...
These new provisions, named "Regulations on Internet Security Supervision and Inspection by Public Security Organs" give the MSP the following new powers:
These new provisions, named "Regulations on Internet Security Supervision and Inspection by Public Security Organs" give the MSP the following new powers:
- Conduct in-person or remote inspections of the network security defenses taken by companies operating in China.
- Check for "prohibited content" banned inside China's border.
- Log security response plans during on-site inspections.
- Copy any user information found on inspected systems during on-site or remote inspections.
- Perform penetration tests to check for vulnerabilities.
- Perform remote inspections without informing companies.
- Share any collected data with other state agencies.
- The right to have two members of the People's Armed Police (PAP) present during on-site inspection to enforce procedures. more
Sunday, April 7, 2019
How to Tell if Someone Snoops on Your Computer
Think about all of the personal information stored on your computer -- it's essentially an extension of your whole identity in digital form. You may have all your photos, videos, resumes, contacts, documents and other sensitive information saved on your PC or Mac.
Can you imagine someone snooping around and getting their hands on all that?
But how can you tell if someone was accessing your files and applications without your knowledge? Is someone using your computer behind your back? Thankfully, there are various ways to find out.
Read on and learn these tricks you can use to see if someone is snooping on your PC or Mac... more
Can you imagine someone snooping around and getting their hands on all that?
But how can you tell if someone was accessing your files and applications without your knowledge? Is someone using your computer behind your back? Thankfully, there are various ways to find out.
Read on and learn these tricks you can use to see if someone is snooping on your PC or Mac... more
Sunday, March 31, 2019
Security Tip: Why it Always Pays to Hire The Best.
 Following the revelation that the The National Enquirer had obtained
intimate texts and images between Amazon CEO Jeff Bezos and Lauren
Sanches, Bezos ordered an investigation into who was behind the data
breach.
Following the revelation that the The National Enquirer had obtained
intimate texts and images between Amazon CEO Jeff Bezos and Lauren
Sanches, Bezos ordered an investigation into who was behind the data
breach. In a post on The Daily Beast, Bezos’ security consultant Gavin De Becker says that his team of investigators have “concluded with high confidence that the Saudis had access to Bezos’ phone...” more
Protecting Confidential Information - The Japanese Model
 Japan - The government is making every effort to keep information on the new Imperial era name secret until its announcement Monday and officials are even checking plants inside the Prime Minister’s Office for possible bugging devices...
Japan - The government is making every effort to keep information on the new Imperial era name secret until its announcement Monday and officials are even checking plants inside the Prime Minister’s Office for possible bugging devices...The government will ask members of the expert panel, parliamentary leaders and Cabinet ministers not to bring any recording devices, including smartphones, into the rooms where the new era name will be presented and not to leave there before the announcement.
The government plans to check the belongings of panel members before they enter the Prime Minister’s Office and have government personnel escort them to restrooms so they will not make any contact with outsiders. more
Inside Info Discussed Outside is a Big Deal... killer
Careless talk costs dollars. That’s the lesson from a case heard last week by one of France’s financial regulators.
Lazard Ltd. dealmaker Vincent Le Stradic spent two and a half hours aboard a Eurostar train from London to Paris in 2014 working on a $15 billion takeover bid by Iliad SA for T-Mobile US Inc.
He was oblivious to the fact that the casually dressed man sitting next to him was Alexandre Zaluski, a UBS Group AG banker, who passed the information to a colleague, ultimately resulting in the bank pitching to Iliad to help finance the deal...
It’s an open secret in the media industry that some of the best scoops can be picked up by eavesdropping in lawyers and banker hangouts, from London’s Ye Olde Cheshire Cheese and Michael’s in Midtown Manhattan to Hong Kong’s Captain’s Bar and Mumbai’s Willingdon Sports Club. more
Working on a takeover, merger or acquisition?
Put an information security consultant on your team.
Lazard Ltd. dealmaker Vincent Le Stradic spent two and a half hours aboard a Eurostar train from London to Paris in 2014 working on a $15 billion takeover bid by Iliad SA for T-Mobile US Inc.
He was oblivious to the fact that the casually dressed man sitting next to him was Alexandre Zaluski, a UBS Group AG banker, who passed the information to a colleague, ultimately resulting in the bank pitching to Iliad to help finance the deal...
It’s an open secret in the media industry that some of the best scoops can be picked up by eavesdropping in lawyers and banker hangouts, from London’s Ye Olde Cheshire Cheese and Michael’s in Midtown Manhattan to Hong Kong’s Captain’s Bar and Mumbai’s Willingdon Sports Club. more
Working on a takeover, merger or acquisition?
Put an information security consultant on your team.
Wednesday, March 27, 2019
Information Security and Cryptography Seminar - June 17-19, 2019
 This seminar provides an in-depth coverage of Information Security and Cryptography from both a conceptual and an application-oriented viewpoint. At the same time, the mathematical, algorithmic, protocol-specific, and system-oriented aspects are explained in a way understandable to a wide audience. This includes the foundations needed to understand the different approaches, a critical look at the state-of-the-art, and a perspective on future security technologies.
This seminar provides an in-depth coverage of Information Security and Cryptography from both a conceptual and an application-oriented viewpoint. At the same time, the mathematical, algorithmic, protocol-specific, and system-oriented aspects are explained in a way understandable to a wide audience. This includes the foundations needed to understand the different approaches, a critical look at the state-of-the-art, and a perspective on future security technologies. The material is presented at three different levels. At the highest level, the basic concepts are presented in detail, but abstractly (e.g., as black boxes), without mathematics. No background is required to follow at this level. At an intermediate level, the most important concrete schemes, models, algorithms, and protocols are presented as well as their applications. Here some minimal mathematical and systems background is assumed. At the deepest level, which is not required to understand the higher levels, different special topics, requiring some mathematical background, are discussed.
Lecturers:
Prof. David Basin and Prof. Ueli Maurer
Advanced Technology Group GmbH
Grundgasse 13
9500 Wil
Switzerland
F: +41 (0)44 632 1172
Seminar Location:
Marriott Courtyard Zurich North
Max-Bill-Platz 19
CH-8050 Zurich
Switzerland
more
Tuesday, March 19, 2019
Keep Your Number Private – And Still Receive Calls!
An inexpensive and easy service...
 "Keep your real phone number hidden while making calls and sending texts
for work, dating, Craigslist sales, and more thanks to Hushed. You'll
use their simple and secure app to easily make calls on your second
number (you'll even choose the area code) without committing to another
long, expensive phone contract. Customize your voicemail and use Wi-Fi
or data to talk without expensive service charges. It's true
communication anonymity delivered." more
"Keep your real phone number hidden while making calls and sending texts
for work, dating, Craigslist sales, and more thanks to Hushed. You'll
use their simple and secure app to easily make calls on your second
number (you'll even choose the area code) without committing to another
long, expensive phone contract. Customize your voicemail and use Wi-Fi
or data to talk without expensive service charges. It's true
communication anonymity delivered." more
Bonus:
 "Keep your real phone number hidden while making calls and sending texts
for work, dating, Craigslist sales, and more thanks to Hushed. You'll
use their simple and secure app to easily make calls on your second
number (you'll even choose the area code) without committing to another
long, expensive phone contract. Customize your voicemail and use Wi-Fi
or data to talk without expensive service charges. It's true
communication anonymity delivered." more
"Keep your real phone number hidden while making calls and sending texts
for work, dating, Craigslist sales, and more thanks to Hushed. You'll
use their simple and secure app to easily make calls on your second
number (you'll even choose the area code) without committing to another
long, expensive phone contract. Customize your voicemail and use Wi-Fi
or data to talk without expensive service charges. It's true
communication anonymity delivered." moreBonus:
- The Murray Associates Smartphone Security Tips
- How to Block Caller ID
Wednesday, January 30, 2019
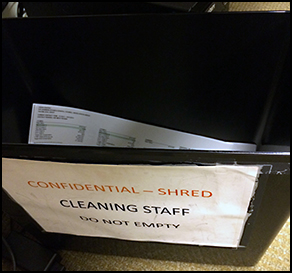
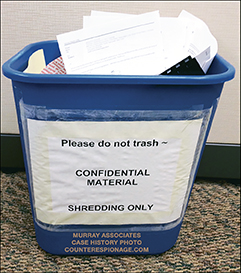
Shred Bin Security – Yours Stinks – Fix it for Free
Shred Bin Security — How to upgrade it... probably for free!
If you have a sizable contract with a shredding company, keep reading.
The Shred Bin Security Conundrum
Your organization realizes they need help getting rid of their wastepaper. Some of it can be recycled. Easy. There are plenty of recycling companies around. Some of it, however, contains sensitive information that must be destroyed.
So, you contact your local "I-Rip-A-Part" shredding company.
You are offered your choice of two shred bin styles, if you are lucky. The elegant particle board beige box, or the converted garbage can.
Both scream security joke. But hey, they only gave you two choices. So, you take what "I-Rip-A-Part" gives you. After all, it's their business. They know best.
Your employees may not laugh out loud, but they get the message. Management either doesn't know much about shred bin security, or they only care enough to make it look like they are doing their due diligence. The result...
Pretty soon these start popping up.
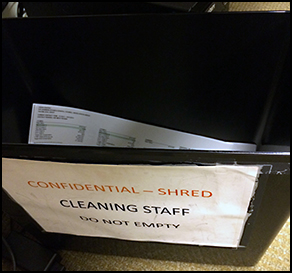
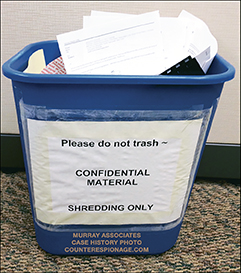
Who's laughing now?
Just the office snoops, competitive intelligence professionals, activists, news media, hackers, etc.
Let me provide some background before providing a workable solution. The crummy shred bin issue is a problem for most U.S. based organizations.
The problem has two roots:
Attacks include: unscrewing the cabinet, picking the cheap lock, sticking a $8.00 flexible grabber through the slot, bending the plastic lid back, or pulling the inner liner bag through the slot... more
If you have a sizable contract with a shredding company, keep reading.
The Shred Bin Security Conundrum
Your organization realizes they need help getting rid of their wastepaper. Some of it can be recycled. Easy. There are plenty of recycling companies around. Some of it, however, contains sensitive information that must be destroyed.
So, you contact your local "I-Rip-A-Part" shredding company.
You are offered your choice of two shred bin styles, if you are lucky. The elegant particle board beige box, or the converted garbage can.
Both scream security joke. But hey, they only gave you two choices. So, you take what "I-Rip-A-Part" gives you. After all, it's their business. They know best.
Your employees may not laugh out loud, but they get the message. Management either doesn't know much about shred bin security, or they only care enough to make it look like they are doing their due diligence. The result...
Pretty soon these start popping up.
Who's laughing now?
Just the office snoops, competitive intelligence professionals, activists, news media, hackers, etc.
Let me provide some background before providing a workable solution. The crummy shred bin issue is a problem for most U.S. based organizations.
The problem has two roots:
- A lack of understanding about information security on the part of the confidential information custodians.
- Shredding companies preying on this ignorance to maximize their profits. (Number one allows number two.)
Attacks include: unscrewing the cabinet, picking the cheap lock, sticking a $8.00 flexible grabber through the slot, bending the plastic lid back, or pulling the inner liner bag through the slot... more
Friday, January 25, 2019
Cybercriminals Home in on Ultra-High Net Worth Individuals
Research shows that better corporate security has resulted in some hackers shifting their sights to the estates and businesses of wealthy families.
Threat intelligence experts and research groups have seen a shift of cybercriminals increasingly targeting ultra-high net worth (UHNW) individuals and their family businesses...
More than half the attacks were viewed as malicious. And, nearly one-third came from an inside threat, such as an employee intentionally leaking confidential information. more
Congratulations to the corporations who have instituted better information security practices. Their elevated security includes periodic checks for electronic surveillance, or Technical Surveillance Countermeasures (TSCM).
These checks are absolutely necessary at family compounds and home offices. There, guests, staff, and tradespeople have great opportunities to plant audio, video and data electronic surveillance devices.
Threat intelligence experts and research groups have seen a shift of cybercriminals increasingly targeting ultra-high net worth (UHNW) individuals and their family businesses...
More than half the attacks were viewed as malicious. And, nearly one-third came from an inside threat, such as an employee intentionally leaking confidential information. more
Congratulations to the corporations who have instituted better information security practices. Their elevated security includes periodic checks for electronic surveillance, or Technical Surveillance Countermeasures (TSCM).
These checks are absolutely necessary at family compounds and home offices. There, guests, staff, and tradespeople have great opportunities to plant audio, video and data electronic surveillance devices.
Friday, January 18, 2019
Counterespionage Checklist: How to Be Safe on the Internet
An open source checklist of resources designed to improve your online privacy and security. Check things off to keep track as you go. more Scott Adams
Wednesday, January 9, 2019
Security Awareness Report for Executives
What can executives do to create or enhance environments to enable awareness programs to succeed?
The first of its kind, the SANS Security Awareness Executive Report draws data from the 2018 Security Awareness Report to reveal a detailed analysis of what drives a thriving awareness program. more
The first of its kind, the SANS Security Awareness Executive Report draws data from the 2018 Security Awareness Report to reveal a detailed analysis of what drives a thriving awareness program. more
Saturday, January 5, 2019
Protecting Trade Secrets in Court Requires Special Security, Like TSCM
Federal prosecutors said a Chinese national employed by an Oklahoma petroleum company has been charged with stealing trade secrets.
Authorities said Hongjin Tan, 35, is accused of stealing trade secrets from his unnamed U.S.-based employer that operates a research facility in the Tulsa area.
An affidavit filed by the FBI alleges that Tan stole trade secrets about an unidentified product worth between $1.4 and $1.8 billion to his employer to benefit a Chinese company where Tan had been offered work. more
Gal Shpantzer, SANS NewsBites news editor notes... "Have you discussed the concept of trade secrets with your legal counsel? Trade secrets are only legally protected if you secure them in a certain manner, above and beyond normal confidential data. www.justice.gov: Reporting Intellectual Property Crime: A Guide for Victims of Copyright Infringement, Trademark Counterfeiting, and Trade Secret Theft (PDF)
TSCM - Technical Surveillance Countermeasures
An affidavit filed by the FBI alleges that Tan stole trade secrets about an unidentified product worth between $1.4 and $1.8 billion to his employer to benefit a Chinese company where Tan had been offered work. more
Gal Shpantzer, SANS NewsBites news editor notes... "Have you discussed the concept of trade secrets with your legal counsel? Trade secrets are only legally protected if you secure them in a certain manner, above and beyond normal confidential data. www.justice.gov: Reporting Intellectual Property Crime: A Guide for Victims of Copyright Infringement, Trademark Counterfeiting, and Trade Secret Theft (PDF)
 |
| Judge: "When did you last check for bugs?" |
Friday, January 4, 2019
Security Ponder - How Big is Your Digital Footprint?
2019 may be the year you consider smaller shoes...
Those of us at a certain age grew up in a simpler time. Email was largely unheard of. There was no social media, no Facebook, Twitter or Instagram. There was no e-commerce, no Amazon, Alibaba or Taobao. No online banking. No online dating. Credit card transactions were processed manually. Local businesses accepted personal checks.
 In short, there really wasn’t any such thing as a “digital footprint,” where personal information resides virtually, in an electronic ether, potentially available for anyone to see.
In short, there really wasn’t any such thing as a “digital footprint,” where personal information resides virtually, in an electronic ether, potentially available for anyone to see.
But over the last two decades, we’ve moved more and more of our lives into that realm. And almost as soon as we began, people attempted to gain inappropriate access to information of all kinds...
Will we have to change our standards... Time will tell. But there’s no denying our expanding digital footprints are changing the nature of both personal and organizational security.
Monitoring and managing our online personas has become an essential task... more sing-a-long
Those of us at a certain age grew up in a simpler time. Email was largely unheard of. There was no social media, no Facebook, Twitter or Instagram. There was no e-commerce, no Amazon, Alibaba or Taobao. No online banking. No online dating. Credit card transactions were processed manually. Local businesses accepted personal checks.
 In short, there really wasn’t any such thing as a “digital footprint,” where personal information resides virtually, in an electronic ether, potentially available for anyone to see.
In short, there really wasn’t any such thing as a “digital footprint,” where personal information resides virtually, in an electronic ether, potentially available for anyone to see. But over the last two decades, we’ve moved more and more of our lives into that realm. And almost as soon as we began, people attempted to gain inappropriate access to information of all kinds...
Will we have to change our standards... Time will tell. But there’s no denying our expanding digital footprints are changing the nature of both personal and organizational security.
Monitoring and managing our online personas has become an essential task... more sing-a-long
Monday, December 24, 2018
Security Director Alert - Well Produced Information Security Awareness Videos for Employees
Foreign intelligence entities, which may include foreign governments, corporations, and their proxies, are actively targeting information, assets, and technologies that are vital to both U.S. national security and our global competitiveness.
 Increasingly, U.S. companies are in the cross-hairs of these foreign intelligence entities, which are breaching private computer networks, pilfering American business secrets and innovation, and carrying out other illicit activities.
Increasingly, U.S. companies are in the cross-hairs of these foreign intelligence entities, which are breaching private computer networks, pilfering American business secrets and innovation, and carrying out other illicit activities.
The National Counterintelligence and Security Center is dedicated to raising awareness among government employees and private industry about these foreign intelligence threats, the risks they pose, and the defensive measures necessary for individuals and organizations to safeguard that which has been entrusted to their protection.
The following products will enable personnel to better understand these threats and provide guidance and tips for protecting the sensitive information, assets, technologies, and networks to which employees have access. It will also serve to help them protect their personal, confidential information that may be used by others to gain their trust. more
Videos:
Social Media Deception Trailer
Social Media Deception
Social Media Deception Full Video
Social Engineering
Spear Phishing (30 second trailer)
Spear Phishing 2017
Spear Phishing Full Video
Travel Awareness
Human Targeting
Supply Chain Risk Management
Economic Espionage (True story.)
 Increasingly, U.S. companies are in the cross-hairs of these foreign intelligence entities, which are breaching private computer networks, pilfering American business secrets and innovation, and carrying out other illicit activities.
Increasingly, U.S. companies are in the cross-hairs of these foreign intelligence entities, which are breaching private computer networks, pilfering American business secrets and innovation, and carrying out other illicit activities.The National Counterintelligence and Security Center is dedicated to raising awareness among government employees and private industry about these foreign intelligence threats, the risks they pose, and the defensive measures necessary for individuals and organizations to safeguard that which has been entrusted to their protection.
The following products will enable personnel to better understand these threats and provide guidance and tips for protecting the sensitive information, assets, technologies, and networks to which employees have access. It will also serve to help them protect their personal, confidential information that may be used by others to gain their trust. more
Videos:
Social Media Deception Trailer
Social Media Deception
Social Media Deception Full Video
Social Engineering
Spear Phishing (30 second trailer)
Spear Phishing 2017
Spear Phishing Full Video
Travel Awareness
Human Targeting
Supply Chain Risk Management
Economic Espionage (True story.)
Wednesday, December 19, 2018
When Technical Surveillance Countermeasures Warnings Are Met With a Shrug
Hackers infiltrated the European Union’s diplomatic communications network for years, downloading thousands of cables that reveal concerns about an unpredictable Trump administration and struggles to deal with Russia and China and the risk that Iran would revive its nuclear program...
The cables were copied from the secure network and posted to an open internet site that the hackers set up in the course of their attack, according to Area 1, the firm that discovered the breach...
Asked on Tuesday about the hack, the National Security Agency said it was still examining the discovery of the European trove. But the former senior intelligence official said that the European Union had been warned, repeatedly, that its aging communications system was highly vulnerable to hacking by China, Russia, Iran and other states.
The official said the warnings were usually received with a shrug...
The Europeans appear, belatedly, to be waking up to the threat. Its senior staff members increasingly use encrypted telephones, and isolated “speech rooms” of Lucite are being installed in key posts... more
The cables were copied from the secure network and posted to an open internet site that the hackers set up in the course of their attack, according to Area 1, the firm that discovered the breach...
Asked on Tuesday about the hack, the National Security Agency said it was still examining the discovery of the European trove. But the former senior intelligence official said that the European Union had been warned, repeatedly, that its aging communications system was highly vulnerable to hacking by China, Russia, Iran and other states.
The official said the warnings were usually received with a shrug...
The Europeans appear, belatedly, to be waking up to the threat. Its senior staff members increasingly use encrypted telephones, and isolated “speech rooms” of Lucite are being installed in key posts... more
When Customs and Border Protection Wants to See Your Cell Phone
Last Thursday's post: Your Mobile Device Could Spill Its Guts (and worse) Get You Arrested
Today: Man sues feds after being detained for refusing to unlock his phone at airport
A Southern California man has become the latest person to sue the federal government over what he says is an unconstitutional search of his phone at the Los Angeles International Airport.
According to his lawsuit, which was recently filed in federal court in Los Angeles, Haisam Elsharkawi had arrived at LAX on February 9, 2017 and was headed to Saudi Arabia to go on a hajj, the Muslim religious pilgrimage...
 Officer Rodriguez, began searching Elsharkawi’s pockets and discovered his phone. Rodriguez asked Elsharkawi to unlock his phone, which he declined to do. He then also refused to answer further questions without having an attorney present...
Officer Rodriguez, began searching Elsharkawi’s pockets and discovered his phone. Rodriguez asked Elsharkawi to unlock his phone, which he declined to do. He then also refused to answer further questions without having an attorney present...
Elsharkawi was taken to a holding cell...
Yet another officer entered the scene, identified in the civil complaint as "Officer Jennifer," who again began questioning Elsharkawi. Eventually, after some back-and-forth, Elsharkawi "felt he had no choice but to acquiesce and unlocked his phone."
Officer Jennifer began searching his phone and asked Elsharkawi about his eBay and Amazon accounts, and "where he got merchandise for his e-commerce business, and what swap meets he frequents. more
Today: Man sues feds after being detained for refusing to unlock his phone at airport
A Southern California man has become the latest person to sue the federal government over what he says is an unconstitutional search of his phone at the Los Angeles International Airport.
According to his lawsuit, which was recently filed in federal court in Los Angeles, Haisam Elsharkawi had arrived at LAX on February 9, 2017 and was headed to Saudi Arabia to go on a hajj, the Muslim religious pilgrimage...
 Officer Rodriguez, began searching Elsharkawi’s pockets and discovered his phone. Rodriguez asked Elsharkawi to unlock his phone, which he declined to do. He then also refused to answer further questions without having an attorney present...
Officer Rodriguez, began searching Elsharkawi’s pockets and discovered his phone. Rodriguez asked Elsharkawi to unlock his phone, which he declined to do. He then also refused to answer further questions without having an attorney present...Elsharkawi was taken to a holding cell...
Yet another officer entered the scene, identified in the civil complaint as "Officer Jennifer," who again began questioning Elsharkawi. Eventually, after some back-and-forth, Elsharkawi "felt he had no choice but to acquiesce and unlocked his phone."
Officer Jennifer began searching his phone and asked Elsharkawi about his eBay and Amazon accounts, and "where he got merchandise for his e-commerce business, and what swap meets he frequents. more
Subscribe to:
Posts (Atom)










