MA - A city man has been charged with illegally taping two phone conversations he had with a man who wanted to arrange the robbery of a company in Lawrence, police said.
Charles "Dino" Manjounes, 48, of 94 Keeley St., was arrested Friday at 3:45 p.m. at his work place, Riverside Pizza, 181 Groveland St., and charged with extortion by threat or injury and two counts of unlawful wiretapping...
Manjounes had put an employee of Colony Foods in contact with a person identified merely as "Death," according to Schena's report. "Death'' told the employee the robbery would cost $20,000. When the employee protested, Death said the cost would be $30,000 — and that he would drag him out of his work place and kill him if he failed to pay, the report said. (more)
Thursday, December 15, 2011
Nelson Mandela 'spy' cameras confiscated by police
 South African police have confiscated cameras they say were illegally filming Nelson Mandela's house in his home village of Qunu in the Eastern Cape.
South African police have confiscated cameras they say were illegally filming Nelson Mandela's house in his home village of Qunu in the Eastern Cape. Police spokesman Vishnu Naidoo told the BBC that two media groups were being investigated.
The cameras were found in a neighbour's house and had been constantly filming the ex-president's residence, he said. (more)
Security Quote of the Day
"The Android platform is where the malware action is. I believe that smart phones are going to become the primary platform of attack for cybercriminals in the coming years." ~ Bruce Schneier, author of the best sellers "Schneier on Security," "Beyond Fear," "Secrets and Lies," and "Applied Cryptography," and an inventor of the Blowfish, Twofish, Threefish, Helix, Phelix, and Skein algorithms.
Industrial Espionage Gang Sends Malicious Emails
A cybercrime gang that primarily targets companies from the chemical industry has launched a new series of attacks that involve malware-laden emails purporting to be from Symantec, the security vendor responsible for exposing its operation earlier this year.
Dubbed the Nitro attacks, the gang's original industrial espionage efforts began sometime in July and lasted until September. The attackers' modus operandi involved sending emails that carried a variant of the Poison Ivy backdoor and were specifically crafted for each targeted company...
"The same group is still active, still targeting chemical companies, and still using the same social engineering modus operandi," security researchers from Symantec said in a blog post on Monday. (more)
Dubbed the Nitro attacks, the gang's original industrial espionage efforts began sometime in July and lasted until September. The attackers' modus operandi involved sending emails that carried a variant of the Poison Ivy backdoor and were specifically crafted for each targeted company...
"The same group is still active, still targeting chemical companies, and still using the same social engineering modus operandi," security researchers from Symantec said in a blog post on Monday. (more)
Monday, December 12, 2011
Cell Phone Spyware Scam Accusations
"Ever get the feeling you've been cheated? Now you can find out the truth."
That's a banner on the website for SMS Privato Spy, which advertises smartphone spyware that allows customers to secretly monitor a spouse or co-worker's phone and collect that person's calls, texts and GPS locations.
According to security experts, however, the truth is that customers have been getting nothing for the $50, $75, $100 or $125 they paid for one of Privato Spy's four packages. (more)
That's a banner on the website for SMS Privato Spy, which advertises smartphone spyware that allows customers to secretly monitor a spouse or co-worker's phone and collect that person's calls, texts and GPS locations.
According to security experts, however, the truth is that customers have been getting nothing for the $50, $75, $100 or $125 they paid for one of Privato Spy's four packages. (more)
Electronic chip in bath soap raises huge stink
India - Expatriate Indian consumers have become suspicious of a brand of bath soap manufactured by a multinational company after consumers back home complained about an electronic chip embedded in the soap.
Reports from India suggest that a bathing soap-related survey being conducted for Britain-based organisations in Beemapalli near Thiruvananthapuram, Kerala, was called off after residents, who had earlier agreed to the survey, panicked...
The survey was being conducted for the stated purpose of finding out the health and hygiene habits of the people living in coastal areas, to which the residents of Beemapalli consented. However, once the realization of an embedded chip in the bathing soap dawned upon the locals, they feared that the soap might 'eavesdrop' on them or even film them in the shower. (more)
The chip was a motion sensor. The survey participants agreed to use the soap for five days and return it, at which point they would be paid money for being part of the survey.
Reports from India suggest that a bathing soap-related survey being conducted for Britain-based organisations in Beemapalli near Thiruvananthapuram, Kerala, was called off after residents, who had earlier agreed to the survey, panicked...
The survey was being conducted for the stated purpose of finding out the health and hygiene habits of the people living in coastal areas, to which the residents of Beemapalli consented. However, once the realization of an embedded chip in the bathing soap dawned upon the locals, they feared that the soap might 'eavesdrop' on them or even film them in the shower. (more)
Saturday, December 10, 2011
The Latest Video Enhancement Trick: De-Blurring
About a year ago I looked at work by two video enhancement specialists; Doug Carner, CPP/CHS-III of Forensic Protection and Jim Hoerricks - author of Forensic Photoshop, a comprehensive imaging workflow for forensic professionals.
Today, Doug advised me of a trick that every security professional should have up their sleeve, de-blurring. He explained how he de-blurs motion this way...
 "Light originates and reflects from objects in very predictable ways. As the camera and object move, they distort the captured image. These distortions can be reversed using a filter that acts like mathematical eye glasses.
"Light originates and reflects from objects in very predictable ways. As the camera and object move, they distort the captured image. These distortions can be reversed using a filter that acts like mathematical eye glasses.For this example, we used the bent light streak seen at the far right of the license plate. The process could have just as easily been applied to the mud flaps or tires."
Wow, major difference!
This got me thinking. How good will this technology become?
Just two months ago, Adobe gave the world a sneak peek.
When you view this video, set it to HD and go full screen. The magic begins about 2 minutes into the clip and continues with several photos being blur corrected.
Unfortunately, this was only a sneak preview. It is not available to the general public in Photoshop yet.
Just to re-cap, here are some of the things Doug can do to enhance your crummy videos...
Just to re-cap, here are some of the things Doug can do to enhance your crummy videos...
• High-resolution video and audio extraction or capture
• Adaptive military-grade video jitter stabilization
• Video de-interlace, de-sequence and de-multiplex
• Intelligent temporal noise and artifact suppression
• Fast-Fourier compression and camera age reversal
• Sub-pixel shift fusion over time, space and frequency
• Adjust video brightness, contrast, saturation and size
• Color channel isolation and focus/motion blur correction
• Audio noise suppression and speech amplification
• Video zoom, trim, crop and speed adjustments
• Multiplex to original with event highlight for court exhibit
• Image extraction, cropping, enlarging and printing
Want to conduct your own experiments with de-blurring?
Visit the Department of Computer Science and Engineering at The Chinese University of Hong Kong. Play with their GPU Blur Removal Software v2.0 just released last month. (Windows Trial Version)
• Adaptive military-grade video jitter stabilization
• Video de-interlace, de-sequence and de-multiplex
• Intelligent temporal noise and artifact suppression
• Fast-Fourier compression and camera age reversal
• Sub-pixel shift fusion over time, space and frequency
• Adjust video brightness, contrast, saturation and size
• Color channel isolation and focus/motion blur correction
• Audio noise suppression and speech amplification
• Video zoom, trim, crop and speed adjustments
• Multiplex to original with event highlight for court exhibit
• Image extraction, cropping, enlarging and printing
Want to conduct your own experiments with de-blurring?
Visit the Department of Computer Science and Engineering at The Chinese University of Hong Kong. Play with their GPU Blur Removal Software v2.0 just released last month. (Windows Trial Version)
Friday, December 9, 2011
Business Telephone Systems Still Vulnerable to Toll Fraud
A Compilation of Phreaking Evidence from 2004-2011 - 25 pages .pdf (download)
Phreaking is a slang term coined to describe the activity of a culture of people who study, experiment with, or explore telecommunication systems, such as equipment and systems connected to public telephone networks. They are often mistakenly lumped in with criminal phone hackers. It is also a mistake to think that this was only a 1970's - 1980's phenomena.
Phreaking is a slang term coined to describe the activity of a culture of people who study, experiment with, or explore telecommunication systems, such as equipment and systems connected to public telephone networks. They are often mistakenly lumped in with criminal phone hackers. It is also a mistake to think that this was only a 1970's - 1980's phenomena.
• PABX/PBX hacking (phreaking) is common. It's organized crime and big business.
• Telephone systems everywhere are targets and telecommunications bandits know how to gain access to your phone system by reconfiguring it to route their own calls through it.
• Phreakers can hack phone systems, voicemail boxes and PINs in a few seconds to gain illegal access to your extensions.
• Most toll fraud is generated after hours and on holidays when it's least likely to be detected.
• Phreakers can gain the most by routing expensive international calls through private phone systems.
• Terrorist organisations use telecommunications fraud to generate funds by illegally gaining access to private phone systems and then re-selling the service.
• Many businesses leave their phone systems completely unprotected.
• You will end up paying the bill after they've hijacked your phone system and extensions to make illegal calls anywhere they choose - often at a huge cost... (more)
Ask your counterespionage consultant to look into this for you. Specifying the correct controls, procedures and security hardware to protect your communications is their specialty.
Don't have a counterespionage consultant?!?! Contact me for a referral.
Ask your counterespionage consultant to look into this for you. Specifying the correct controls, procedures and security hardware to protect your communications is their specialty.
Don't have a counterespionage consultant?!?! Contact me for a referral.
Thursday, December 8, 2011
"I'm Dreaming of a Spy Christmas"
Specifications:
• Take up to 3 minutes of video (at resolution 640 X 480) or take hundreds of photos (at resolution 1280 X 960).
• Take up to 3 minutes of video (at resolution 640 X 480) or take hundreds of photos (at resolution 1280 X 960).
• 3-Channel control allows flying up and down, forward & backward, left and right
• Stabilized by sophisticated built in gyroscope for the clearest pictures
• Use the remote transmitter button to take the pictures and video
• Plug in computer to download the video and photos
• User friendly Graphic Unit Interface on PC to adjust the photo or video setting.
• Real time capturing to see the effect on screen.
White color LED to indicate photo capturing or video recording.
White color LED to indicate photo capturing or video recording.
• Download videos and photos through USB
Charging through transmitter or USB (more)
Charging through transmitter or USB (more)
--------
Fei Lun Full Function Radio Control Spy Video Car
• Audio & Video (with Night Vision Transmitter)
(more)
-------
Using Spy Gadgets: The Definitive Guide to Finding Out Anything About Anyone Using Spy Tools, Spy Gear, Spy Equipment, Spy Cameras, Spy Toys, or a Spy Bug From a Spy Shop
By Dick Peplowski
 Are you constantly wondering about certain people and wondering about their real past or present lives? You’ve surely thought, “That guy just seems to have something “off”” as we all have and want to know the truth. So how do you find the truth? Sadly, to find out the real dirt on someone, you’ve had to pay a fortune for a private investigator to get it for you. The good news is that is no longer the case! You can literally become your own Sherlock Holmes and find out all the dirt on people that you want. The best part is that you are going to be learning how to do this through the use of awesome spy tools that you can easily obtain. These will give you the power of Inspector Gadget when it comes to finding out the real dirt on someone. You learn about all the spy tools you could ever want to use plus many more in Dick Peplowski's "Using Spy Gadgets: The Definitive Guide to Finding Out Anything About Anyone Using Spy Tools, Spy Gear, Spy Equipment, Spy Cameras, Spy Toys, or a Spy Bug From a Spy Shop." This is all broken down in an easy to understand and easy to apply system for personal surveillance success. (more)
Are you constantly wondering about certain people and wondering about their real past or present lives? You’ve surely thought, “That guy just seems to have something “off”” as we all have and want to know the truth. So how do you find the truth? Sadly, to find out the real dirt on someone, you’ve had to pay a fortune for a private investigator to get it for you. The good news is that is no longer the case! You can literally become your own Sherlock Holmes and find out all the dirt on people that you want. The best part is that you are going to be learning how to do this through the use of awesome spy tools that you can easily obtain. These will give you the power of Inspector Gadget when it comes to finding out the real dirt on someone. You learn about all the spy tools you could ever want to use plus many more in Dick Peplowski's "Using Spy Gadgets: The Definitive Guide to Finding Out Anything About Anyone Using Spy Tools, Spy Gear, Spy Equipment, Spy Cameras, Spy Toys, or a Spy Bug From a Spy Shop." This is all broken down in an easy to understand and easy to apply system for personal surveillance success. (more)
• Audio & Video (with Night Vision Transmitter)
(more)
-------
Using Spy Gadgets: The Definitive Guide to Finding Out Anything About Anyone Using Spy Tools, Spy Gear, Spy Equipment, Spy Cameras, Spy Toys, or a Spy Bug From a Spy Shop
By Dick Peplowski
 Are you constantly wondering about certain people and wondering about their real past or present lives? You’ve surely thought, “That guy just seems to have something “off”” as we all have and want to know the truth. So how do you find the truth? Sadly, to find out the real dirt on someone, you’ve had to pay a fortune for a private investigator to get it for you. The good news is that is no longer the case! You can literally become your own Sherlock Holmes and find out all the dirt on people that you want. The best part is that you are going to be learning how to do this through the use of awesome spy tools that you can easily obtain. These will give you the power of Inspector Gadget when it comes to finding out the real dirt on someone. You learn about all the spy tools you could ever want to use plus many more in Dick Peplowski's "Using Spy Gadgets: The Definitive Guide to Finding Out Anything About Anyone Using Spy Tools, Spy Gear, Spy Equipment, Spy Cameras, Spy Toys, or a Spy Bug From a Spy Shop." This is all broken down in an easy to understand and easy to apply system for personal surveillance success. (more)
Are you constantly wondering about certain people and wondering about their real past or present lives? You’ve surely thought, “That guy just seems to have something “off”” as we all have and want to know the truth. So how do you find the truth? Sadly, to find out the real dirt on someone, you’ve had to pay a fortune for a private investigator to get it for you. The good news is that is no longer the case! You can literally become your own Sherlock Holmes and find out all the dirt on people that you want. The best part is that you are going to be learning how to do this through the use of awesome spy tools that you can easily obtain. These will give you the power of Inspector Gadget when it comes to finding out the real dirt on someone. You learn about all the spy tools you could ever want to use plus many more in Dick Peplowski's "Using Spy Gadgets: The Definitive Guide to Finding Out Anything About Anyone Using Spy Tools, Spy Gear, Spy Equipment, Spy Cameras, Spy Toys, or a Spy Bug From a Spy Shop." This is all broken down in an easy to understand and easy to apply system for personal surveillance success. (more)Wednesday, December 7, 2011
Town Clerk Allegedly Testifies to Electronic Eavesdropping
MI - Augusta Township Clerk Kathy Giszczak allegedly testified in a deposition that she electronically eavesdropped on a conversation between the township's deputy treasurer and supervisor.
That allegation surfaced as part of an Open Meetings Act lawsuit pitting one half of the board against the other half.

Electronic eavesdropping is a felony punishable by up to five years in prison, though no criminal charges have been brought against Giszczak. A hearing on the OMA lawsuit is scheduled for Dec. 13. (more)
That allegation surfaced as part of an Open Meetings Act lawsuit pitting one half of the board against the other half.
Electronic eavesdropping is a felony punishable by up to five years in prison, though no criminal charges have been brought against Giszczak. A hearing on the OMA lawsuit is scheduled for Dec. 13. (more)
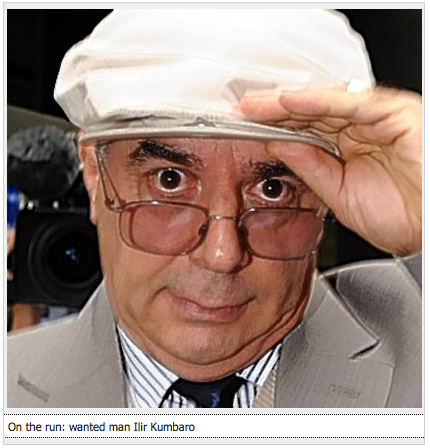
Albanian Ex-Spy Chief Disappears
UK - Scotland Yard today issued a nationwide appeal to track down a former Albanian spy chief who is on the run after failing to attend an extradition hearing.
Ilir Kumbaro, 58, was due to appear at Westminster magistrates' court, where he faced being sent back to Albania on charges of kidnapping and torturing three men.
When he failed to show up last Thursday, police checked his home in Forest Hill, other addresses and hospitals. All ports and airports were alerted but there has been no sign of him.
Detectives, who say he may be using his skills as an ex-head of the Albanian secret police to evade capture, suspect he could still be in London, living under a false identity. One of Eastern Europe's most wanted men, he lived on benefits with his wife and one of his two sons on a Fulham council estate for 12 years before he was discovered...
Police say Kumbaro, who is about 5ft 7in, bald and stout, is likely to be with his wife. He speaks English with an Eastern European accent. Anyone who has seen him is asked to call Crimestoppers on 0800 555 111. (more)
When he failed to show up last Thursday, police checked his home in Forest Hill, other addresses and hospitals. All ports and airports were alerted but there has been no sign of him.
Detectives, who say he may be using his skills as an ex-head of the Albanian secret police to evade capture, suspect he could still be in London, living under a false identity. One of Eastern Europe's most wanted men, he lived on benefits with his wife and one of his two sons on a Fulham council estate for 12 years before he was discovered...
Police say Kumbaro, who is about 5ft 7in, bald and stout, is likely to be with his wife. He speaks English with an Eastern European accent. Anyone who has seen him is asked to call Crimestoppers on 0800 555 111. (more)
Yet Another 'News of the World' Phone Hacking Arrest
UK - British police said Wednesday they have arrested another suspect in their investigation of phone hacking by the News of the World tabloid.
London's Metropolitan police said they arrested a 41-year-old man on suspicion of conspiring to intercept voice-mail messages and pervert the course of justice. The man's name wasn't released. Police said he was being held at a police station in south London. (more)
London's Metropolitan police said they arrested a 41-year-old man on suspicion of conspiring to intercept voice-mail messages and pervert the course of justice. The man's name wasn't released. Police said he was being held at a police station in south London. (more)
Twitter - The Stool Pigeon
If you were thinking that tweet you just sent would soon disappear into the ether, you couldn't be more wrong.
It will soon be stored alongside Thomas Jefferson's draft of the American Declaration of Independence and a Gutenberg Bible.
That's because every public tweet sent since Twitter was launched five-and-a-half years ago is to be be archived by America's national library.
The Library of Congress announced the deal with Twitter last year, but yesterday its digital initiatives manager shone more light on the project. (more)
I understand the anthropological argument. Perhaps, several centuries from now someone will find value in researching old tweets. I suspect they will view tweets as we view graffiti on the walls of Pompeii. But, given the current economic conditions should we really be spending our tax dollars on archiving moronic celebrity tweets? /Rant
It will soon be stored alongside Thomas Jefferson's draft of the American Declaration of Independence and a Gutenberg Bible.
That's because every public tweet sent since Twitter was launched five-and-a-half years ago is to be be archived by America's national library.
The Library of Congress announced the deal with Twitter last year, but yesterday its digital initiatives manager shone more light on the project. (more)
Dorkly Bits: Spy Hunter Pranksters
Never trust the guy in the van. (stupid spy video game parody)
Tuesday, December 6, 2011
"All Your Shreds Are Belong to U.S." Wins Reconstruct Shreds Contest
via gizmag.com...
At the end of October, DARPA (the Defense Advanced Research Projects Agency) launched its Shredder Challenge contest. The objective: create a system for reconstructing shredded papers, then demonstrate it by piecing together five documents, the shredded remains of which were posted on the contest's website. Although the contest had a December 4th deadline, the "All Your Shreds Are Belong to U.S." team correctly reassembled all five documents with two days to spare.
The San Francisco-based team, which beat out approximately 9,000 competitors, used "custom-coded, computer-vision algorithms to suggest fragment pairings to human assemblers for verification." Members of the team spent approximately 600 man-hours developing algorithms and otherwise working on the challenge, completing everything within 33 days. Because it was able to reconstruct all five documents posted in the contest, the team was able to claim the complete prize of US$50,000.
DARPA hosted the contest both to develop methods of reading shredded documents left behind by enemies in war zones, and to identify ways in which U.S. shredded documents could be read by other parties, so that countermeasures could be developed.
DARPA hosted the contest both to develop methods of reading shredded documents left behind by enemies in war zones, and to identify ways in which U.S. shredded documents could be read by other parties, so that countermeasures could be developed.
Missed the contest?
Subscribe to:
Posts (Atom)