Sensational recordings and documents show how South Africa’s largest JSE-listed company, cigarette giant British American Tobacco (BAT), appears to be committing “industrial espionage” on a grand scale, running a network of “agents” placed to spy inside rival organisations.
This evidence, uncovered as part of a year-long Business Times investigation, raises questions about the tobacco company’s ethics, and highlights shady dealings that are understood to have been reported to the authorities in South Africa and the UK, where it is headquartered.
One agent, who was placed in a senior position within BAT’s rivals, said that BAT’s “worldwide” practice of making secret payments to agents could be considered “international money-laundering”.
“They had a deal to pay me for industrial espionage, and may I say I’m not the only one in our little circle. There are [government intelligence agents] who have left the state, and gone to work for BAT,” said the agent.
The claim that BAT was involved in spying on rivals is corroborated by affidavits, audio and video recordings, copies of financial transactions and the accounts of five cigarette manufactures, a state informant, sources close to the South African Revenue Services and one of BAT’s senior agents...
Business Times has a recording of a conversation between a senior BAT official and one of its secret agents, in which the tobacco executive tells the agent not to “sell us out” by spilling the beans on the spying. (more)
Sunday, March 30, 2014
History - Nixon's Plumbers Tap More Pipes
Jeff Stein provides new information that suggests the Nixon White House may have bugged the Pentagon telephones of senior American military officials.
Stein managed to track down Dave Mann, a former member of the Pentagon’s Counterintelligence Force, who in 1971 stumbled upon a classified report claiming that listening bug signals had been detected emanating from offices in the Joint Chiefs of Staff. The signals had been picked up by a technical surveillance countermeasures (TSCM) team during a routine sweep of the Pentagon, in search of unauthorized interception devices.
Mann ran some tests to verify the TSCM team’s report, and discovered that the bug signals originated from the personal office telephone line of General William Westmoreland, who was then the US Army’s Chief of Staff. He also discovered that the telephone of his assistant had been compromised, as well as the telephone lines belonging to the US Army’s assistant secretary, its logistics director, and at least one general.
Mann’s personal conclusion was that the phone lines were most likely bugged with the cooperation of the Chesapeake and Potomac Telephone Company, which was at that the time considered an operational wing of the FBI, under Director J. Edgar Hoover...
Mann, who is now semi-retired from the military and lives in Tennessee, told Stein that “there was a lot —and I mean a lot— of pressure to prove GRAPPLE TRIP to be a fluke or a miswired telephone”. Which is precisely what happened: the investigation concluded that the bug signals were emitted due to “crossed wires in the telephone system”. (more)
 |
| Why is this man laughing? |
Mann ran some tests to verify the TSCM team’s report, and discovered that the bug signals originated from the personal office telephone line of General William Westmoreland, who was then the US Army’s Chief of Staff. He also discovered that the telephone of his assistant had been compromised, as well as the telephone lines belonging to the US Army’s assistant secretary, its logistics director, and at least one general.
Mann’s personal conclusion was that the phone lines were most likely bugged with the cooperation of the Chesapeake and Potomac Telephone Company, which was at that the time considered an operational wing of the FBI, under Director J. Edgar Hoover...
Mann, who is now semi-retired from the military and lives in Tennessee, told Stein that “there was a lot —and I mean a lot— of pressure to prove GRAPPLE TRIP to be a fluke or a miswired telephone”. Which is precisely what happened: the investigation concluded that the bug signals were emitted due to “crossed wires in the telephone system”. (more)
Saturday, March 29, 2014
NY Private Detective Firm Keeps Corporate Spies at Bay
Private investigators are most commonly associated with scorned spouses and cheap motels, but one PI firm based in New York is sniffing out scandal in a much more upscale (and more unusual) venue: the boardrooms of Fortune 500 companies.
Murray Associates, a counterespionage security company, has been de-bugging conference rooms and securing trading floors from the prying eyes of sneaky competitors since 1978. (more)
Murray Associates, a counterespionage security company, has been de-bugging conference rooms and securing trading floors from the prying eyes of sneaky competitors since 1978. (more)
10 Years Ago - 120 Coke Cans Spur a Military TSCM Alert
"Into the Wayback, Sherman."
THIS SECURITY BULLETIN APPLIES TO ALL SSCC SITES/FACILITIES/RESTRICTED
AREAS WHERE CLASSIFIED/SENSITIVE OPERATIONS ARE CONDUCTED
 The SSCC Security Office was recently informed that the Coca Cola Company has a summer game promotion running from 5/17 - 7/12/04 in all 50 states and the District of Columbia that has the capability to compromise classified information.
The SSCC Security Office was recently informed that the Coca Cola Company has a summer game promotion running from 5/17 - 7/12/04 in all 50 states and the District of Columbia that has the capability to compromise classified information.
The company has intermixed approximately 120 Coca-Cola cans that actually contain GPS locators equipped with a SIM card, keypad and GPS chip transponder so it functions as a cell phone and GPS locator. The cans are concealed in specially marked 12, 18, 20, or 24 can multi-packs of Coca-Cola Classic, Vanilla Coke, Cherry Coke and Caffeine Free Coke.
The hi-tech Coke "Unexpected Summer" promotion can has a button, microphone, and a tiny speaker on the outside of the can. Pressing the larger red button starts the game in process, thus activating the GPS signal and a cell phone used by the customer to call a special hotline. Consumers who find these cans, activate the technology, and call the hot line must agree to allow Coke "search teams" using the GPS tracker (accurate to within 50 feet), to surprise them anyplace, anytime within three weeks to deliver a valuable prize.
Until such time as this sales promotion ends and all 120 cans are accounted for, Coca-Cola packages should be opened and inspected before taking them into any area marked as a "Restricted Area" or where the location is sensitive or classified meetings/discussions, etc. are in progress or have the potential to occur at any time.
If one of these hi-tech game cans is found in snack bars, cafeterias, vending machines, etc. immediately report it to the Security Manager. While the can is your personal property, you must report obtaining it and immediately remove it from NSWC Crane work spaces.
As with any other two-way communications device, the hi-tech cans are not to be brought into any NSWC Crane classified facility under any circumstances.
While high technology is our livelihood, everyone must be alert to technology applications that can endanger National Security and the effectiveness of our support to the war fighters. Please report similar applications by marketers, etc. to the Security Office so the information can be widely disseminated. (source) (T-shirt)
THIS SECURITY BULLETIN APPLIES TO ALL SSCC SITES/FACILITIES/RESTRICTED
AREAS WHERE CLASSIFIED/SENSITIVE OPERATIONS ARE CONDUCTED
 The SSCC Security Office was recently informed that the Coca Cola Company has a summer game promotion running from 5/17 - 7/12/04 in all 50 states and the District of Columbia that has the capability to compromise classified information.
The SSCC Security Office was recently informed that the Coca Cola Company has a summer game promotion running from 5/17 - 7/12/04 in all 50 states and the District of Columbia that has the capability to compromise classified information. The company has intermixed approximately 120 Coca-Cola cans that actually contain GPS locators equipped with a SIM card, keypad and GPS chip transponder so it functions as a cell phone and GPS locator. The cans are concealed in specially marked 12, 18, 20, or 24 can multi-packs of Coca-Cola Classic, Vanilla Coke, Cherry Coke and Caffeine Free Coke.
The hi-tech Coke "Unexpected Summer" promotion can has a button, microphone, and a tiny speaker on the outside of the can. Pressing the larger red button starts the game in process, thus activating the GPS signal and a cell phone used by the customer to call a special hotline. Consumers who find these cans, activate the technology, and call the hot line must agree to allow Coke "search teams" using the GPS tracker (accurate to within 50 feet), to surprise them anyplace, anytime within three weeks to deliver a valuable prize.
Until such time as this sales promotion ends and all 120 cans are accounted for, Coca-Cola packages should be opened and inspected before taking them into any area marked as a "Restricted Area" or where the location is sensitive or classified meetings/discussions, etc. are in progress or have the potential to occur at any time.
If one of these hi-tech game cans is found in snack bars, cafeterias, vending machines, etc. immediately report it to the Security Manager. While the can is your personal property, you must report obtaining it and immediately remove it from NSWC Crane work spaces.
As with any other two-way communications device, the hi-tech cans are not to be brought into any NSWC Crane classified facility under any circumstances.
While high technology is our livelihood, everyone must be alert to technology applications that can endanger National Security and the effectiveness of our support to the war fighters. Please report similar applications by marketers, etc. to the Security Office so the information can be widely disseminated. (source) (T-shirt)
Labels:
cell phone,
government,
GPS,
Hack,
historical,
TSCM,
weird
Friday, March 28, 2014
Over 50% of Android Users Don't Use Passwords, Pins or Meaningful Swipes
An ad hoc survey conducted by Google's anti-abuse research lead Elie Bursztein has shown that over half of Android users don't lock their phones in any meaningful way.
After polling 1,500 users, he discovered that 52 percent of those users "open" their device with a simple slide or gesture, 25.5 percent have opted to locking their phones with drawing a pattern on a grid, and 15.1 percent are using a PIN.
Only 3.3 percent have opted for using a password, 2.3 percent for the option where the phone can recognize their face, and 1.8 percent are using other, 3rd party forms of authentication...

...no security is perfect. Both lock patterns and PIN codes can be vulnerable to smudge attacks, as a 2010 Usenix paper illustrates. So whether you use a PIN or a pattern you should change it from time to time. You might also want to go to your phone’s options screen and disable the display of the pattern so people can’t “shouldersurf” it. (more)
 |
| Click to enlarge. |
After polling 1,500 users, he discovered that 52 percent of those users "open" their device with a simple slide or gesture, 25.5 percent have opted to locking their phones with drawing a pattern on a grid, and 15.1 percent are using a PIN.
Only 3.3 percent have opted for using a password, 2.3 percent for the option where the phone can recognize their face, and 1.8 percent are using other, 3rd party forms of authentication...

...no security is perfect. Both lock patterns and PIN codes can be vulnerable to smudge attacks, as a 2010 Usenix paper illustrates. So whether you use a PIN or a pattern you should change it from time to time. You might also want to go to your phone’s options screen and disable the display of the pattern so people can’t “shouldersurf” it. (more)
Google Explains Search Warrant Requests - for ages 2 and older
P.S. Word on the street... the cow is a spy.
Thursday, March 27, 2014
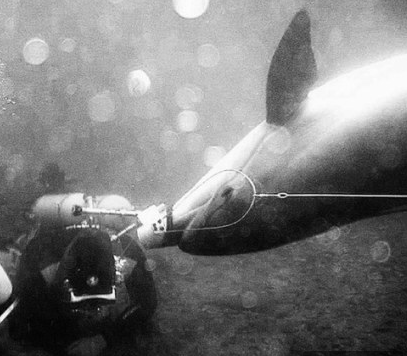
From our, "You can't make this spy stuff up" file. - Spy Dolphins Defect
Ukraine’s secret unit of spy DOLPHINS that can plant bombs and attack divers with guns have defected to Russia.
Last year three of five spy dolphins went absent without leave in the Black Sea - apparently in search of love, but returned to their duties shortly afterwards.
Yury Plyachenko, a former Soviet naval anti-sabotage officer, explained that this was something that had to be taken into account in working with the 007 mammals.
‘If a male dolphin saw a female dolphin during the mating season, then he would immediately set off after her. But they come back in a week or so.’ (more)
- The Ukraine Army has been using dolphins and seals since the 70s
- After the fall of the USSR, the 'dolphin spies' remained in the Ukraine
- The dolphins have been trained to hunt for mines and plant bombs
- They can also attack divers with knives or pistols attached to their heads
- Now, military dolphins in Crimea will be transferred to the Russian Navy
Last year three of five spy dolphins went absent without leave in the Black Sea - apparently in search of love, but returned to their duties shortly afterwards.
Yury Plyachenko, a former Soviet naval anti-sabotage officer, explained that this was something that had to be taken into account in working with the 007 mammals.
‘If a male dolphin saw a female dolphin during the mating season, then he would immediately set off after her. But they come back in a week or so.’ (more)
In Washington, DC this Spring? Need Something Cool to Do?
Check out The International Spy Museum...
U.S. Notified 3,000 Companies About Cyberattacks in 2013
Federal agents notified more than 3,000 U.S. companies last year that their computer systems had been hacked, White House officials have told industry executives, marking the first time the government has revealed how often it tipped off the private sector to cyber intrusions.
The alerts went to firms large and small, from local banks to major defense contractors to national retailers...
“Three thousand companies is astounding,” said James A. Lewis, a senior fellow and cyberpolicy expert at the Center for Strategic and International Studies. “The problem is as big or bigger than we thought.”
The number reflects only a fraction of the true scale of cyberintrusions into the private sector by criminal groups and foreign governments and their proxies, particularly in China and Eastern Europe. The estimated cost to U.S. companies and consumers is up to $100 billion annually, analysts say. (more)
The alerts went to firms large and small, from local banks to major defense contractors to national retailers...
“Three thousand companies is astounding,” said James A. Lewis, a senior fellow and cyberpolicy expert at the Center for Strategic and International Studies. “The problem is as big or bigger than we thought.”
The number reflects only a fraction of the true scale of cyberintrusions into the private sector by criminal groups and foreign governments and their proxies, particularly in China and Eastern Europe. The estimated cost to U.S. companies and consumers is up to $100 billion annually, analysts say. (more)
How do the FBI and Secret Service know...
...your network has been breached before you do?
Knock, knock! Secret Service here. "Is this your customer payment card data?"
By all accounts, many of the massive data breaches in the news these days are first revealed to the victims by law enforcement, the Secret Service and Federal Bureau of Investigation (FBI). But how do the agencies figure it out before the companies know they have been breached, especially given the millions companies spend on security and their intense focus on compliance?
 The agencies do the one thing companies don’t do. They attack the problem from the other end by looking for evidence that a crime has been committed. Agents go undercover in criminal forums where stolen payment cards, customer data and propriety information are sold. They monitor suspects and sometimes get court permission to break into password-protected enclaves where cyber-criminals lurk.
The agencies do the one thing companies don’t do. They attack the problem from the other end by looking for evidence that a crime has been committed. Agents go undercover in criminal forums where stolen payment cards, customer data and propriety information are sold. They monitor suspects and sometimes get court permission to break into password-protected enclaves where cyber-criminals lurk.
They have informants, they do interviews with people already incarcerated for cybercrime, and they see clues in the massive data dumps of information stolen from companies whose networks have been breached. (more)
Knock, knock! Secret Service here. "Is this your customer payment card data?"
By all accounts, many of the massive data breaches in the news these days are first revealed to the victims by law enforcement, the Secret Service and Federal Bureau of Investigation (FBI). But how do the agencies figure it out before the companies know they have been breached, especially given the millions companies spend on security and their intense focus on compliance?
 The agencies do the one thing companies don’t do. They attack the problem from the other end by looking for evidence that a crime has been committed. Agents go undercover in criminal forums where stolen payment cards, customer data and propriety information are sold. They monitor suspects and sometimes get court permission to break into password-protected enclaves where cyber-criminals lurk.
The agencies do the one thing companies don’t do. They attack the problem from the other end by looking for evidence that a crime has been committed. Agents go undercover in criminal forums where stolen payment cards, customer data and propriety information are sold. They monitor suspects and sometimes get court permission to break into password-protected enclaves where cyber-criminals lurk. They have informants, they do interviews with people already incarcerated for cybercrime, and they see clues in the massive data dumps of information stolen from companies whose networks have been breached. (more)
Labels:
business,
computer,
counterespionage,
data,
detection,
FBI,
Hack,
surveillance
Spyware & Malware Odds & Ends
A spyware app developed by two researchers has shown that Google Glass can
be used to secretly take photos of whatever a Glass wearer is looking
at without their knowledge - making the Glass user the one whose privacy
and security is potentially compromised. (more)
Security researchers said they have uncovered bugs in Google's Android operating system that could allow malicious apps to send vulnerable devices into a spiral of endlessly looping crashes and possibly delete all data stored on them. (more)
Stingray is a US law enforcement spoof cell tower used to track the location of mobile phones. Snoopy is a project conducted by London-based Sensepost Research Labs that does similar and much more with any WIFI-enabled device. Now Snoopy has gone airborne – mounted on a drone it can hover above a target area and trick mobile devices into connecting: a form of flying man-in-the-middle attack... The drones collect the devices' probe requests, which could be looking for networks that the user has recently connected to, and mimic them. "If your device is probing for 'Starbucks', we'll pretend to be Starbucks, and your device will connect." Once that connection is made, Snoopy can listen in. (more)
Security researchers said they have uncovered bugs in Google's Android operating system that could allow malicious apps to send vulnerable devices into a spiral of endlessly looping crashes and possibly delete all data stored on them. (more)
Stingray is a US law enforcement spoof cell tower used to track the location of mobile phones. Snoopy is a project conducted by London-based Sensepost Research Labs that does similar and much more with any WIFI-enabled device. Now Snoopy has gone airborne – mounted on a drone it can hover above a target area and trick mobile devices into connecting: a form of flying man-in-the-middle attack... The drones collect the devices' probe requests, which could be looking for networks that the user has recently connected to, and mimic them. "If your device is probing for 'Starbucks', we'll pretend to be Starbucks, and your device will connect." Once that connection is made, Snoopy can listen in. (more)
Tuesday, March 25, 2014
Capital One Bank Settles in $3 Million Wiretp Law Suit (Now we know what's in cardholder's wallets.)
A putative class of Capital One Bank NA cardholders in five states have
secured a $3 million settlement of claims that the bank covertly
recorded outbound customer service calls, according to documents filed
Monday in California federal court.
The pact puts to rest a suit over the bank’s alleged violations of California’s Invasion of Privacy Act and the similar two-party consent laws of Florida, Maryland, Nevada and New Hampshire. (more)
Is your organization doing any recording? What's in your policy?
The pact puts to rest a suit over the bank’s alleged violations of California’s Invasion of Privacy Act and the similar two-party consent laws of Florida, Maryland, Nevada and New Hampshire. (more)
Is your organization doing any recording? What's in your policy?
The Bug Stopped Here - Ireland's Police Chief Resigns
Ireland's police chief resigned Tuesday following months of criticism of how his force handled allegations of illegal wire-tapping and corrupt enforcement of traffic laws.
Underscoring a growing sense of public unease at police standards and behavior, government leaders announced that they would open a judge-led probe into new revelations that telephone calls at many police stations had been illegally recorded since the 1980s.
The government said it didn't yet know why the widespread recording was secretly happening. Security analysts said it could partly reflect an effort by senior commanders to monitor rank-and-file officers' communications...
It said a judge would be appointed to examine why police had secretly recorded telephone conversations in and out of many police stations for several years, a practice ended only in November after the first wire-tap scandal became public knowledge. (more)
Underscoring a growing sense of public unease at police standards and behavior, government leaders announced that they would open a judge-led probe into new revelations that telephone calls at many police stations had been illegally recorded since the 1980s.
The government said it didn't yet know why the widespread recording was secretly happening. Security analysts said it could partly reflect an effort by senior commanders to monitor rank-and-file officers' communications...
It said a judge would be appointed to examine why police had secretly recorded telephone conversations in and out of many police stations for several years, a practice ended only in November after the first wire-tap scandal became public knowledge. (more)
New Bot Targets Apple iOS Devices - Tip: Don't Jailbreak
A new bot with the name Zorenium has landed in the criminal underground, with the ability to target Apple iOS devices like iPhone and iPad. It's not widely known, nor is it widely detectable...
The analysis suggests that Apple devices must be jail-broken to be vulnerable, which makes sense given Apple’s tight control over the iOS ecosystem—there’s a reason after all that virtually all mobile malware targets Android. (more)
The analysis suggests that Apple devices must be jail-broken to be vulnerable, which makes sense given Apple’s tight control over the iOS ecosystem—there’s a reason after all that virtually all mobile malware targets Android. (more)
Ex-President Spills His Secret to Ducking Electronic Surveillance
Former US President Jimmy Carter has said he hand-writes letters to foreign and US leaders in an effort to evade what he described as pervasive US electronic surveillance.
Mr Carter, 89, told the Associated Press he had "no doubt" the US monitored and recorded "almost every telephone call" and email.
His humanitarian efforts bring him in contact with a range of foreign and US political leaders. (more)
Mr Carter, 89, told the Associated Press he had "no doubt" the US monitored and recorded "almost every telephone call" and email.
His humanitarian efforts bring him in contact with a range of foreign and US political leaders. (more)
Subscribe to:
Comments (Atom)