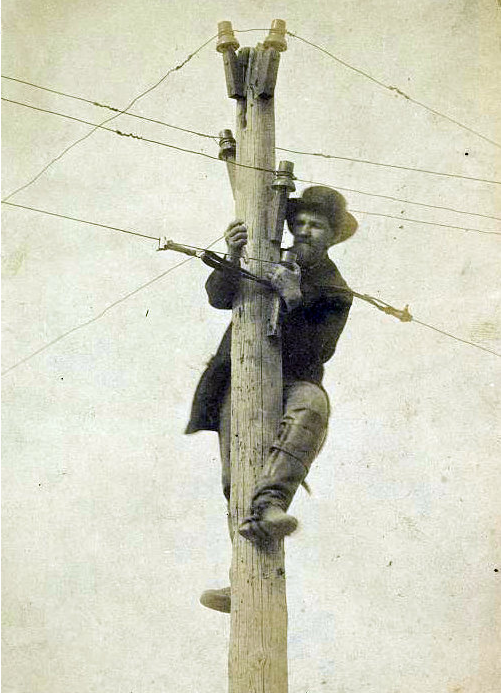
AR - A little wiretapping and a less than harmonious conversation with another man were the catalyst for romance in 1986 for Beth Guerin and the office telephone installation tech.
He had certainly noticed her. The really cute girl who was answering phones part time in the doctor's office? Yes, 19-year-old Darrin Adcock had noticed her. He was doing a job for a small telecommunications company in Hot Springs, and he likely would have left without exchanging a word with her had he not made a small mistake first.
"I had my test set and I accidentally clicked onto the line that she was on. And I listened. Maybe I shouldn't have, but I did," Darrin says. "I really didn't mean to do that, but in doing so I heard her talking to her then-boyfriend and realized her and her boyfriend were not getting along and I thought, 'Well, this is kind of neat.'" more
Sunday, March 15, 2015
Corporate Espionage: CBI Names PricewaterhouseCoopers as a Suspect
India - The Central Bureau of Investigation on Saturday named consultancy firm PricewaterhouseCoopers as a suspect in the corporate espionage case...
The Delhi Police had earlier last month arrested two more persons - one from the UPSC and the other from the Environment Ministry - broadening its probe into the corporate espionage case.
They were held for leaking sensitive documents to energy consultant Lokesh Sharma.
Around 17 people, including government employees, energy consultants and senior executives of top energy companies, have been arrested so far by the Delhi Police. more
The Delhi Police had earlier last month arrested two more persons - one from the UPSC and the other from the Environment Ministry - broadening its probe into the corporate espionage case.
They were held for leaking sensitive documents to energy consultant Lokesh Sharma.
Around 17 people, including government employees, energy consultants and senior executives of top energy companies, have been arrested so far by the Delhi Police. more
Friday, March 13, 2015
Business Espionage: The Cruffin Caper (and 230 other recipes swiped)
It takes three days to make a cruffin, a muffin-croissant hybrid that is the signature of Ry Stephen, a 28-year-old pastry chef. His shop, Mr Holmes Bakehouse, has been open three months and inspired a wild following, with customers lining up early to buy the ice-cream-cone-shaped cruffins, which reliably sell out before the line is gone...
 Now, the tempting sweet may have inspired a crime. Overnight last week, a thief stole the recipe for cruffins, and Mr. Stephen’s 230 other recipes, from binders in the bakery’s kitchen. Nothing else in the store was touched: not money, valuable baking equipment, an iPad or other computers...
Now, the tempting sweet may have inspired a crime. Overnight last week, a thief stole the recipe for cruffins, and Mr. Stephen’s 230 other recipes, from binders in the bakery’s kitchen. Nothing else in the store was touched: not money, valuable baking equipment, an iPad or other computers...
Mr. Stephen does not think it was an inside job. He said he trusts his employees and has told them, “You can have any recipe you want, provided you know how to execute it.” Plus a new surveillance system had been installed, but was not yet operational, although the employees did not know that. more
This is a cautionary tale with important points for your business...
1. Secure your proprietary information and business secrets. Keeping them in your "locked" office, on a shelf, where everyone knows where they are, is not adequate.
2. Use top notch security to protect your business secrets. Hire an independent security consultant to assist you with this. Periodically double-check to make sure your security systems are 100% operational.
Expect to see cruffins everywhere, soon.
 Now, the tempting sweet may have inspired a crime. Overnight last week, a thief stole the recipe for cruffins, and Mr. Stephen’s 230 other recipes, from binders in the bakery’s kitchen. Nothing else in the store was touched: not money, valuable baking equipment, an iPad or other computers...
Now, the tempting sweet may have inspired a crime. Overnight last week, a thief stole the recipe for cruffins, and Mr. Stephen’s 230 other recipes, from binders in the bakery’s kitchen. Nothing else in the store was touched: not money, valuable baking equipment, an iPad or other computers...Mr. Stephen does not think it was an inside job. He said he trusts his employees and has told them, “You can have any recipe you want, provided you know how to execute it.” Plus a new surveillance system had been installed, but was not yet operational, although the employees did not know that. more
This is a cautionary tale with important points for your business...
1. Secure your proprietary information and business secrets. Keeping them in your "locked" office, on a shelf, where everyone knows where they are, is not adequate.
2. Use top notch security to protect your business secrets. Hire an independent security consultant to assist you with this. Periodically double-check to make sure your security systems are 100% operational.
Expect to see cruffins everywhere, soon.
Tea - the "greatest single act of corporate espionage in history."
The Scottish Spy Who Stole China's Tea Empire
In the mid-19th century, Britain was an almost unchallenged empire. It controlled about a fifth of the world's surface, and yet its weakness had everything to do with tiny leaves soaked in hot water: tea. By 1800, it was easily the most popular drink among Britons.
The problem? All the tea in the world came from China, and Britain couldn't control the quality or the price. So around 1850, a group of British businessmen set out to create a tea industry in a place they did control: India.
For All the Tea In China: How England Stole the World's Favorite Drink and Changed History is writer Sarah Rose's account of the effort to control the tea market, what she calls the "greatest single act of corporate espionage in history." more
 |
| Robert Fortune |
The problem? All the tea in the world came from China, and Britain couldn't control the quality or the price. So around 1850, a group of British businessmen set out to create a tea industry in a place they did control: India.
For All the Tea In China: How England Stole the World's Favorite Drink and Changed History is writer Sarah Rose's account of the effort to control the tea market, what she calls the "greatest single act of corporate espionage in history." more
Wednesday, March 11, 2015
Barbie Learns How to Talk. (It only took her 50 years.)
In a recent demonstration of its Internet-connected doll, Hello Barbie, a Mattel spokesperson greeted the souped-up version of the iconic doll by saying, “Welcome to New York, Barbie.”
 Thanks to voice-recognition technology, Barbie was able to analyze that remark and give a relevant, conversational response: “I love New York! Don’t you? Tell me, what’s your favorite part about the city? The food, fashion or the sights?”
Thanks to voice-recognition technology, Barbie was able to analyze that remark and give a relevant, conversational response: “I love New York! Don’t you? Tell me, what’s your favorite part about the city? The food, fashion or the sights?”
The company promises that the software will enable the doll “to listen and learn each girl’s preferences and then adapt to those accordingly.”
The interactive doll is slated to hit shelves in the fall, and Mattel is likely hoping it will help revive sinking sales of its flagship brand.
But a children’s privacy advocacy group is calling for the company to cease production of the toy, saying Hello Barbie might more accurately be called "eavesdropping" Barbie. Because the doll works by recording children’s speech with an embedded microphone and then sending that data over the Web, these advocates call the technology “creepy” and say it could leave children vulnerable to stealth advertising tactics. On Wednesday, the Campaign for a Commercial-Free Childhood launched a petition urging Mattel to keep the doll from hitting store shelves. more
"Well, gag me with a spoon!"
 Thanks to voice-recognition technology, Barbie was able to analyze that remark and give a relevant, conversational response: “I love New York! Don’t you? Tell me, what’s your favorite part about the city? The food, fashion or the sights?”
Thanks to voice-recognition technology, Barbie was able to analyze that remark and give a relevant, conversational response: “I love New York! Don’t you? Tell me, what’s your favorite part about the city? The food, fashion or the sights?”The company promises that the software will enable the doll “to listen and learn each girl’s preferences and then adapt to those accordingly.”
The interactive doll is slated to hit shelves in the fall, and Mattel is likely hoping it will help revive sinking sales of its flagship brand.
But a children’s privacy advocacy group is calling for the company to cease production of the toy, saying Hello Barbie might more accurately be called "eavesdropping" Barbie. Because the doll works by recording children’s speech with an embedded microphone and then sending that data over the Web, these advocates call the technology “creepy” and say it could leave children vulnerable to stealth advertising tactics. On Wednesday, the Campaign for a Commercial-Free Childhood launched a petition urging Mattel to keep the doll from hitting store shelves. more
"Well, gag me with a spoon!"
Tuesday, March 10, 2015
Defense Against the Spy - 1967 CIA Training Film
The United States Central Intelligence Agency (CIA) presents a case
study of devices that were used for espionage purposes during the
1960's.
Security Director Alert - Time to Update Your BYOD Policy (You do have one don't you?)
According to Alcatel-Lucent’s Motive Security Labs, around 16 million mobile devices are already infected by malicious software designed to spy on users and steal confidential data.
This form of malware is capable of tracking the phone and its owner’s location, monitoring ingoing and outgoing calls, text messages and emails, as well as tracking web browsers.
Cyber-criminals are now targeting Android devices with infection rates for Android and Windows devices estimated to be split 50/50.
Many multinational firms, however, still employ an unmonitored bring-your-own-device (BYOD) policy. This frequently means key staff are connecting to the corporate communications network via unsecured smartphones. It has also led to a situation where staff access social networking sites and audio/visual entertainment of all kinds, exposing them to a growing number of malware attacks. more
This form of malware is capable of tracking the phone and its owner’s location, monitoring ingoing and outgoing calls, text messages and emails, as well as tracking web browsers.
Cyber-criminals are now targeting Android devices with infection rates for Android and Windows devices estimated to be split 50/50.
Many multinational firms, however, still employ an unmonitored bring-your-own-device (BYOD) policy. This frequently means key staff are connecting to the corporate communications network via unsecured smartphones. It has also led to a situation where staff access social networking sites and audio/visual entertainment of all kinds, exposing them to a growing number of malware attacks. more
Spycams and Wiretaps - Motives for Murder
PA - A man has shot his neighbor eight times - leaving her in critical condition - and taken his own life after accusing her of wiretapping his apartment in a years-long rift.
Steven Outlaw, 51, confronted his downstairs neighbor, 46-year-old Mary Pitts-Devine, in the first-floor hallway of their West Philadelphia building just before 11am on Sunday, WPVI reported.
 He shot at her 10 times, hitting her with eight bullets and leaving her in critical condition.
He shot at her 10 times, hitting her with eight bullets and leaving her in critical condition.
Outlaw then went to his second-floor apartment and shot himself dead, police said.
The shooting came after a simmering argument over whether Pitts-Devine was wiretapping the telephone lines of Outlaw's apartment, Philly.com reported...
He had also written down accusations that she was spying on him with video cameras, according to the channel. more
Steven Outlaw, 51, confronted his downstairs neighbor, 46-year-old Mary Pitts-Devine, in the first-floor hallway of their West Philadelphia building just before 11am on Sunday, WPVI reported.
 He shot at her 10 times, hitting her with eight bullets and leaving her in critical condition.
He shot at her 10 times, hitting her with eight bullets and leaving her in critical condition.Outlaw then went to his second-floor apartment and shot himself dead, police said.
The shooting came after a simmering argument over whether Pitts-Devine was wiretapping the telephone lines of Outlaw's apartment, Philly.com reported...
He had also written down accusations that she was spying on him with video cameras, according to the channel. more
Friday, March 6, 2015
FutureWatch - FM Bugs Are So Arco - Coming Soon... Bugs with Pluck
For the first time in history, a prototype radio has been created that is claimed to be completely digital, generating high-frequency radio waves purely through the use of integrated circuits and a set of patented algorithms without using conventional analog radio circuits in any way whatsoever. This breakthrough technology promises to vastly improve the wireless communications capabilities of everything from 5G mobile technology to the multitude devices aimed at supporting the Internet of Things.
The significance of this new technology cannot be overstated: Every aspect of radio frequency generation is said to be created using a string of digital bits, and nothing else. There are no analog circuits, no filters, no chokes, none of the traditional circuitry and components expected in a radio transmitter. Consisting of a mere handful of components, including a couple of integrated circuits, an antenna, and not much else, the transmitter – dubbed Pizzicato – promises to change the face of wireless transmission.
Created by Cambridge Consultants, the initial trials of the Pizzicato have been claimed to show that it has fully met all the expectations of its myriad performance requirements. But more than this, the Pizzicato has brought bulky radio circuits down to microprocessor levels, with the promise of even smaller, more efficient uses of the technology in future. more
The significance of this new technology cannot be overstated: Every aspect of radio frequency generation is said to be created using a string of digital bits, and nothing else. There are no analog circuits, no filters, no chokes, none of the traditional circuitry and components expected in a radio transmitter. Consisting of a mere handful of components, including a couple of integrated circuits, an antenna, and not much else, the transmitter – dubbed Pizzicato – promises to change the face of wireless transmission.
Created by Cambridge Consultants, the initial trials of the Pizzicato have been claimed to show that it has fully met all the expectations of its myriad performance requirements. But more than this, the Pizzicato has brought bulky radio circuits down to microprocessor levels, with the promise of even smaller, more efficient uses of the technology in future. more
Tuesday, March 3, 2015
A Short History of Wiretapping
Wiretapping has been around almost since the invention of the telegraph.
Union and Confederate soldiers intercepted one another’s telegraph wires during the Civil War, scraping off a small piece of insulation and splicing their own line to the enemy’s.
Later, private detectives spied for clients. The use of a wiretap in a Connecticut divorce case in the 1880s led that state to ban the practice in 1889. News services stole one another’s articles. The use of a wiretap to convey false cotton prices in London, a plot aimed at stock speculators, set off a panic in New Orleans in 1899.
But in the postwar 19th century, much wiretapping of telegraphs and, later, telephones was carried out by crooks trying to cheat other crooks.
more
Union and Confederate soldiers intercepted one another’s telegraph wires during the Civil War, scraping off a small piece of insulation and splicing their own line to the enemy’s.
Later, private detectives spied for clients. The use of a wiretap in a Connecticut divorce case in the 1880s led that state to ban the practice in 1889. News services stole one another’s articles. The use of a wiretap to convey false cotton prices in London, a plot aimed at stock speculators, set off a panic in New Orleans in 1899.
But in the postwar 19th century, much wiretapping of telegraphs and, later, telephones was carried out by crooks trying to cheat other crooks.
more
Workplace Video Voyeurism - Domino’s Falls This Time
NY - An alleged voyeuristic Domino’s worker was arrested after a young woman noticed something odd in the employee bathroom, according to the Nassau County Police Department.
In the early hours of Tuesday morning, a 20-year-old female employee at the 935 Front Street Domino’s in Uniondale took a break to use the bathroom.
The coat rack inside the facility caught her eye, however — specifically, a cell phone peeking out of a jacket pocket. She notified the manager, and her manager dialed 911. The jacket, according to police, belonged to the woman’s co-worker, 19-year-old Jonathan Parra.
Along with footage of the young woman, an investigation revealed images of a 51-year-old man using the bathroom as well.
Parra faces two counts of unlawful surveillance and will be arraigned Tuesday at First District Court in Hempstead.
more
In the early hours of Tuesday morning, a 20-year-old female employee at the 935 Front Street Domino’s in Uniondale took a break to use the bathroom.
 |
| Murray Associates composite photo. |
Along with footage of the young woman, an investigation revealed images of a 51-year-old man using the bathroom as well.
Parra faces two counts of unlawful surveillance and will be arraigned Tuesday at First District Court in Hempstead.
more
Spying With a Drone May Become a Criminal Offense in CO
Colorado lawmakers want to criminalize the use of drones when they’re used to monitor someone without their consent.
The proposal up for a House committee vote Tuesday would make it a crime of first-degree trespassing to take images of someone when they have an expectation of privacy. Drone users could also be charged with harassment if they use the technology to monitor someone’s movements.
 “As technology moves forward, our privacy is becoming more dear to us,” said the bill sponsor, Rep. Polly Lawrence, R-Littleton.
“As technology moves forward, our privacy is becoming more dear to us,” said the bill sponsor, Rep. Polly Lawrence, R-Littleton.
Lawrence’s bill is not just about drones, but “any type of electronic surveillance when a person has a reasonable expectation of privacy.”
more
Get your (novelty) drone hunting license here. I have one.
The proposal up for a House committee vote Tuesday would make it a crime of first-degree trespassing to take images of someone when they have an expectation of privacy. Drone users could also be charged with harassment if they use the technology to monitor someone’s movements.
 “As technology moves forward, our privacy is becoming more dear to us,” said the bill sponsor, Rep. Polly Lawrence, R-Littleton.
“As technology moves forward, our privacy is becoming more dear to us,” said the bill sponsor, Rep. Polly Lawrence, R-Littleton.Lawrence’s bill is not just about drones, but “any type of electronic surveillance when a person has a reasonable expectation of privacy.”
more
Get your (novelty) drone hunting license here. I have one.
Yet More Invisibility Eyeglasses
This year, AVG will reveal a set of concept invisibility glasses at Pepcom in Barcelona before Mobile World Congress.
What are invisibility glasses?
Developed by AVG Innovation Labs, the glasses help protect your visual identity in the digital age.
Through a mixture of technology and specialist materials, privacy wearables such as invisibility glasses can make it difficult for cameras or other facial recognition technologies to get a clear view of your identity.
...there are generally two different methods of combating unwanted facial recognition:
Infrared Light
The idea is to place infrared LEDs inserted around the eyes and the nose areas. Since the infrared lights are completely invisible to human eyes, they are only detectable by cameras which are sensitive to the wavelengths of these LEDs. They claim to break face detection when the lights are on.
 In this example we show how infrared can be used to avoid Facebook’s facial recognition technology.
In this example we show how infrared can be used to avoid Facebook’s facial recognition technology.
 Retro-reflective Materials
Retro-reflective Materials
These specialist materials help maintain your privacy at the moment that the image is actually taken.
PS - This is a proof-of-concept project. Not for sale. However, you can make your own.
Other glasses.
Note: Many cell phone cameras have infrared cutoff filters built into their lenses... and you can bet law enforcement facial recognition systems do too.
What are invisibility glasses?
Developed by AVG Innovation Labs, the glasses help protect your visual identity in the digital age.
Through a mixture of technology and specialist materials, privacy wearables such as invisibility glasses can make it difficult for cameras or other facial recognition technologies to get a clear view of your identity.
...there are generally two different methods of combating unwanted facial recognition:
Infrared Light
The idea is to place infrared LEDs inserted around the eyes and the nose areas. Since the infrared lights are completely invisible to human eyes, they are only detectable by cameras which are sensitive to the wavelengths of these LEDs. They claim to break face detection when the lights are on.
 In this example we show how infrared can be used to avoid Facebook’s facial recognition technology.
In this example we show how infrared can be used to avoid Facebook’s facial recognition technology. Retro-reflective Materials
Retro-reflective MaterialsThese specialist materials help maintain your privacy at the moment that the image is actually taken.
PS - This is a proof-of-concept project. Not for sale. However, you can make your own.
Note: Many cell phone cameras have infrared cutoff filters built into their lenses... and you can bet law enforcement facial recognition systems do too.
Monday, February 23, 2015
Fink RAT Co-creator Meets Big Daddy Uncle Sam
One of the co-creators of the Blackshades Remote Access Trojan (RAT) that infected more than 500,000 computers has pleaded guilty to charges of hacking.
 Alex Yücel, 24, faces up to 10 years in prison for his involvement with the $40 program designed to secretly remotely control victims' computers...
Alex Yücel, 24, faces up to 10 years in prison for his involvement with the $40 program designed to secretly remotely control victims' computers...
Through his creation and sale of the Blackshades RAT, Alex Yücel enabled anyone, for just $40, to violate the property and privacy of his victims...
According to documents filed in the Manhattan federal court, the Blackshades RAT - which was used to secretly take nude photos of Miss Teen USA - could give an attacker complete control over an infected system...
(more)
 Alex Yücel, 24, faces up to 10 years in prison for his involvement with the $40 program designed to secretly remotely control victims' computers...
Alex Yücel, 24, faces up to 10 years in prison for his involvement with the $40 program designed to secretly remotely control victims' computers...Through his creation and sale of the Blackshades RAT, Alex Yücel enabled anyone, for just $40, to violate the property and privacy of his victims...
According to documents filed in the Manhattan federal court, the Blackshades RAT - which was used to secretly take nude photos of Miss Teen USA - could give an attacker complete control over an infected system...
(more)
Indian Oil Ministry Investigating Possible Bugging
India - A sticky tape with a micro-insertion found beneath a table in the office of a top bureaucrat in the ministry has raised suspicion over snooping attempts to tap information on sensitive energy related matters, sources told HT.

“We cannot rule out any possibility... the matter has been brought to the notice of the investigative agencies, who will look into the matter,” a top petroleum ministry bureaucrat told HT requesting not to be identified...
A similar incident of a possible bugging of a government office was reported in June 2011 when suspicion surrounded the office of the then finance minister Pranab Mukherjee. The office of the home ministry and the Intelligence Bureau later confirmed that it was just a suspicion and no bugging took place in the office.
(more)

“We cannot rule out any possibility... the matter has been brought to the notice of the investigative agencies, who will look into the matter,” a top petroleum ministry bureaucrat told HT requesting not to be identified...
A similar incident of a possible bugging of a government office was reported in June 2011 when suspicion surrounded the office of the then finance minister Pranab Mukherjee. The office of the home ministry and the Intelligence Bureau later confirmed that it was just a suspicion and no bugging took place in the office.
(more)
Subscribe to:
Posts (Atom)