Swiss officials foiled an apparent spying operation by Russians posing as plumbers in Davos, site of the World Economic Forum's annual meeting, a newspaper reported on Tuesday, but police did not confirm key details of the account.
The report in the Tages-Anzeiger newspaper said the pair presented diplomatic passports and left the country. more
Tuesday, January 21, 2020
‘Spy Games’ - 10 Civilians Vie for $100,000 Prize
One can’t deny that there is a certain charm and pull around the life of
a spy - from going on undercover missions to just enjoying the finer
things in life à la James Bond, and if you are keen on seeing how one
goes about acquiring the skills needed to be a good spy, then Bravo’s
latest offering ‘Spy Games’ might just be what you have been looking
for...
One can’t deny that there is a certain charm and pull around the life of a spy - from going on undercover missions to just enjoying the finer things in life à la James Bond, and if you are keen on seeing how one goes about acquiring the skills needed to be a good spy, then Bravo’s latest offering ‘Spy Games’ might just be what you have been looking for. more
One can’t deny that there is a certain charm and pull around the life of a spy - from going on undercover missions to just enjoying the finer things in life à la James Bond, and if you are keen on seeing how one goes about acquiring the skills needed to be a good spy, then Bravo’s latest offering ‘Spy Games’ might just be what you have been looking for. more
Thursday, January 16, 2020
"I found this thing. Is it a bug?"
At Murray Associates we occasionally receive calls asking, "I found this thing. Is it a bug?"
 Usually, the identification is easy:
Usually, the identification is easy:
 Today,
a call comes in from a well-respected private investigator in Boston.
He has a corporate client whose employee "found this thing."
Today,
a call comes in from a well-respected private investigator in Boston.
He has a corporate client whose employee "found this thing."
She takes a photo, sends it to him, who sends it to us... via low resolution text message...
Rough guess...
A Bluetooth item finder, similar to a Tile, but a Chinese knockoff branded with some corporate logo. Possibly a promotional item?
 We
later learned it was in her bedroom, mounted to the wall, not found in a
covert location. She had pulled it off the wall to take the photo. We
did not receive a photo of the mounting piece, or a mention of its
placement.
We
later learned it was in her bedroom, mounted to the wall, not found in a
covert location. She had pulled it off the wall to take the photo. We
did not receive a photo of the mounting piece, or a mention of its
placement.
Later we eventually received a photo of the flip side...
Hummm... not too helpful, but no evidence of on the front of a pinhole for video, or a microphone on the circuit board. No battery seen, but the two large solder tabs and circles on the circuit board indicate there is a battery on the other side of the board.
Why would someone mount something like this on a bedroom wall?!?!
 One possibility emerged... "How to find your lost iPhone with Tile."
One possibility emerged... "How to find your lost iPhone with Tile."
Nope. Tiles have their logo on them. Ours looks different.
 Another possibility... Yahoo changed their logo last Fall.
Another possibility... Yahoo changed their logo last Fall.
Could they have sent out a promotional "Tile" with their newly designed exclamation point logo on it?
Close, but no prize.
Okay, let's start fresh.
Say, the Tile is a MacGuffin.
Look elsewhere.
What other wall-warts do we know of?
HVAC sensors, for one.
Google search....
Ah ha.... that's what this thing is.
Case closed.
This was a good investigative process refresher for us, and a thing we will all remember next time "this thing" shows up.
Extra Credit:
~Kevin
 Usually, the identification is easy:
Usually, the identification is easy:- it's a piece of electronic jewelry (blinky earring, or pin);
- an old annoy-a-tron;
- or Bluetooth tag, like a Tile item finder.
 Today,
a call comes in from a well-respected private investigator in Boston.
He has a corporate client whose employee "found this thing."
Today,
a call comes in from a well-respected private investigator in Boston.
He has a corporate client whose employee "found this thing."She takes a photo, sends it to him, who sends it to us... via low resolution text message...
Rough guess...
A Bluetooth item finder, similar to a Tile, but a Chinese knockoff branded with some corporate logo. Possibly a promotional item?
 We
later learned it was in her bedroom, mounted to the wall, not found in a
covert location. She had pulled it off the wall to take the photo. We
did not receive a photo of the mounting piece, or a mention of its
placement.
We
later learned it was in her bedroom, mounted to the wall, not found in a
covert location. She had pulled it off the wall to take the photo. We
did not receive a photo of the mounting piece, or a mention of its
placement.Later we eventually received a photo of the flip side...
Hummm... not too helpful, but no evidence of on the front of a pinhole for video, or a microphone on the circuit board. No battery seen, but the two large solder tabs and circles on the circuit board indicate there is a battery on the other side of the board.
Why would someone mount something like this on a bedroom wall?!?!
 One possibility emerged... "How to find your lost iPhone with Tile."
One possibility emerged... "How to find your lost iPhone with Tile."Nope. Tiles have their logo on them. Ours looks different.
Could they have sent out a promotional "Tile" with their newly designed exclamation point logo on it?
Close, but no prize.
Okay, let's start fresh.
Say, the Tile is a MacGuffin.
Look elsewhere.
What other wall-warts do we know of?
HVAC sensors, for one.
Google search....
Case closed.
This was a good investigative process refresher for us, and a thing we will all remember next time "this thing" shows up.
Extra Credit:
~Kevin
Wednesday, January 15, 2020
The Case of “Eddie Spaghetti” and the First Spycam News of 2020
We are only halfway through, the first month, of the first year, in a new decade... and the spycam pandemic is off to a roaring start.
Like corporate espionage and other forms of illegal electronic surveillance, only the failures make the news. The vast majority of illegal covert electronic surveillance goes undetected.
Learn how to spot spycams and keep scheduling your corporate TSCM inspections.
-----
Canada - Edward Casavant, 55, (who gave himself the nickname, “Eddie Spaghetti”) pleaded guilty to possession of child pornography, making child pornography, voyeurism and sexual exploitation of a person with a disability, and was sentenced to six years in prison. more
OH - A former Hillsdale Middle School and High School art teacher convicted of voyeurism was sentenced Tuesday to 180 days in jail. more
CA - Peterborough man charged with voyeurism after allegedly using electronics to peer through windows. more
Singapore - The alleged victims of a Singaporean undergraduate accused of illicitly filming 12 women want a gag order on his identity to be lifted, despite being fully aware of the risk of being identified. more
ID - Kory Ray West, the 34-year-old man accused of concealing a video camera in the bathroom of a Blackfoot home where he had been staying, and of stealing items of underclothing from bedrooms, could serve up to seven years in prison for his crimes. more
NY - The husband of a New York prosecutor who filmed his child's nanny on bathroom spycam, could have charges against him dropped, after he claimed he only used it to watch himself undress. more
HI - An $8,000 project to install covert security cameras in the Council Chambers of the county building in order to monitor an active shooter or hostage situation was kept secret from most council members and the public, county officials said. more
CA - Ring of fired: Amazon axes multiple workers who secretly snooped on netizens' surveillance camera footage. more
KY - A former teacher at a Kentucky high school admitted to filming students in a bathroom...
UK - staff and parents with children at Denmead Junior School were in shock at the grim discovery of an iPhone in a vent. Action
was taken by the school. A 23-year-old man from Waterlooville (was arrested) on
suspicion of voyeurism. He has been released under investigation. more
CT - An investigation that began in South Windsor in August that led to a Manchester man being charged with voyeurism after filming people in a locker room at L.A. Fitness resulted in more charges being filed against him Friday stemming from similar incidents in Farmington, police said. South Windsor police said that Selby had placed his cellphone in one of the lockers and left the door open. more
CA - A Desert Hot Springs man who was previously required to register as a sex offender pleaded not guilty Friday to charges of filming people inside a grocery store bathroom in Cathedral City...10 misdemeanor counts of unlawful use of a concealed camera to secretly videotape.... 2013 - Prosecutors alleged he concealed a video camera in a paper bag and entered a woman's restroom in a Los Angeles Macy's department store dressed as a woman and secretly videotaped women using the restroom. more
Wales - A sportsman who once represented Anglesey in the Island Games has admitted installing a camera in toilets where people, including youngsters, got changed. more
Like corporate espionage and other forms of illegal electronic surveillance, only the failures make the news. The vast majority of illegal covert electronic surveillance goes undetected.
Learn how to spot spycams and keep scheduling your corporate TSCM inspections.
-----
Canada - Edward Casavant, 55, (who gave himself the nickname, “Eddie Spaghetti”) pleaded guilty to possession of child pornography, making child pornography, voyeurism and sexual exploitation of a person with a disability, and was sentenced to six years in prison. more
OH - A former Hillsdale Middle School and High School art teacher convicted of voyeurism was sentenced Tuesday to 180 days in jail. more
CA - Peterborough man charged with voyeurism after allegedly using electronics to peer through windows. more
Singapore - The alleged victims of a Singaporean undergraduate accused of illicitly filming 12 women want a gag order on his identity to be lifted, despite being fully aware of the risk of being identified. more
ID - Kory Ray West, the 34-year-old man accused of concealing a video camera in the bathroom of a Blackfoot home where he had been staying, and of stealing items of underclothing from bedrooms, could serve up to seven years in prison for his crimes. more
NY - The husband of a New York prosecutor who filmed his child's nanny on bathroom spycam, could have charges against him dropped, after he claimed he only used it to watch himself undress. more
HI - An $8,000 project to install covert security cameras in the Council Chambers of the county building in order to monitor an active shooter or hostage situation was kept secret from most council members and the public, county officials said. more
CA - Ring of fired: Amazon axes multiple workers who secretly snooped on netizens' surveillance camera footage. more
KY - A former teacher at a Kentucky high school admitted to filming students in a bathroom...
Police...reported finding a recording
device set up in the bathroom of the nurse's station. Police said the
video recorder captured the person putting the device in place. more
MI - A Canton man pleaded guilty last month
to three felony charges associated with illegal voyeurism at an
Aqua-Tots swim school in his hometown... Police said they were dispatched to the Canton Aqua-Tots swim school for young children...because a woman saw a recording device targeting her changing stall. She reported her suspicions to staff. more
CT - An investigation that began in South Windsor in August that led to a Manchester man being charged with voyeurism after filming people in a locker room at L.A. Fitness resulted in more charges being filed against him Friday stemming from similar incidents in Farmington, police said. South Windsor police said that Selby had placed his cellphone in one of the lockers and left the door open. more
CA - A Desert Hot Springs man who was previously required to register as a sex offender pleaded not guilty Friday to charges of filming people inside a grocery store bathroom in Cathedral City...10 misdemeanor counts of unlawful use of a concealed camera to secretly videotape.... 2013 - Prosecutors alleged he concealed a video camera in a paper bag and entered a woman's restroom in a Los Angeles Macy's department store dressed as a woman and secretly videotaped women using the restroom. more
Wales - A sportsman who once represented Anglesey in the Island Games has admitted installing a camera in toilets where people, including youngsters, got changed. more
Surveillance in Tombstone Territory
 |
One recent example we've come across is the Tombstone Cam... Click to enlarge. more The last time we heard of a bugged funeral.
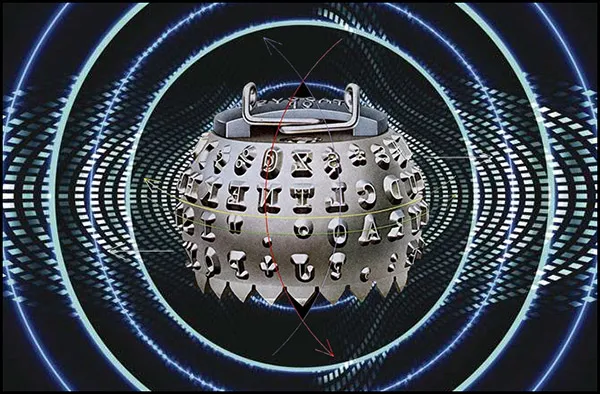
The Crazy Story of How Soviet Russia Bugged an American Embassy’s Typewriters
After tens of thousands of fruitless X-rays, a technician noticed a small coil of wire inside the on/off switch of an IBM Selectric typewriter. Gandy believed that this coil was acting as a step-down transformer to supply lower-voltage power to something within the typewriter. Eventually he uncovered a series of modifications that had been concealed so expertly that they had previously defied detection.
A solid aluminum bar, part of the structural support of the typewriter, had been replaced with one that looked identical but was hollow. Inside the cavity was a circuit board and six magnetometers. The magnetometers sensed movements of tiny magnets that had been embedded in the transposers that moved the typing “golf ball” into position for striking a given letter. more
Labels:
#eavesdropping,
#espionage,
#hack,
CIA,
counterespionage,
government,
KGB,
TSCM,
weird
Monday, January 13, 2020
Security Tip #792: Be Gone Phishing
via Krebs on Security
"Savvy readers here no doubt already know this, but to find the true domain referenced in a link, look to the right of “http(s)://” until you encounter the first backward slash (/). The domain directly to the left of that first slash is the true destination; anything that precedes the second dot to the left of that first slash is a subdomain and should be ignored for the purposes of determining the true domain name."
"For instance, in the case of the imaginary link below, example.com is the true destination, not apple.com: https://www.apple.com.example.com/findmyphone/" more
Double checking links before clicking can save you from sleeping with the phishers. Hover over links, but don't click, to see where you might be going.
"Savvy readers here no doubt already know this, but to find the true domain referenced in a link, look to the right of “http(s)://” until you encounter the first backward slash (/). The domain directly to the left of that first slash is the true destination; anything that precedes the second dot to the left of that first slash is a subdomain and should be ignored for the purposes of determining the true domain name."
"For instance, in the case of the imaginary link below, example.com is the true destination, not apple.com: https://www.apple.com.example.com/findmyphone/" more
Double checking links before clicking can save you from sleeping with the phishers. Hover over links, but don't click, to see where you might be going.
Death by Spycam
The wedding hall was booked and home furnishings all bought... but the bride — one of thousands of women to fall victim to an epidemic of high-tech voyeurism in South Korea — is not here.

Lee Yu-jung took her own life after a colleague secretly filmed her in the changing room of the hospital where they both worked, the country’s first reported spy-cam death.
Footage of Lee was found among a bigger video cache of women, all illegally snatched in the country’s spy-cam epidemic, often with cheap devices as small as a key ring. more

Lee Yu-jung took her own life after a colleague secretly filmed her in the changing room of the hospital where they both worked, the country’s first reported spy-cam death.
Footage of Lee was found among a bigger video cache of women, all illegally snatched in the country’s spy-cam epidemic, often with cheap devices as small as a key ring. more
Spybuster Tip #632: Fortify Your Two-factor Authentication
Two-factor authentication is a must, but don't settle for the SMS version. Use a more secure authenticator app instead.
The most popular authenticator apps are Google Authenticator and Authy, but password managers 1Password and LastPass offer the service as well, if that helps you streamline. If you're heavy into Microsoft's ecosystem, you might want Microsoft Authenticator. While they all differ somewhat in features, the core functionality is the same no matter which one you use. more
The most popular authenticator apps are Google Authenticator and Authy, but password managers 1Password and LastPass offer the service as well, if that helps you streamline. If you're heavy into Microsoft's ecosystem, you might want Microsoft Authenticator. While they all differ somewhat in features, the core functionality is the same no matter which one you use. more
Tuesday, January 7, 2020
The Art of Investigation (book)
The editors and contributing authors* are the best in their field, and bring a wealth of real-world knowledge and experience to the subject. There are several publications available on the nuts-and-bolts of the process and stages of an investigation. That ground has been covered. However, little has been published on the investigative skills required, the traits necessary, and the qualities endemic to an inquisitive mind that can be cultivated to improve an investigator’s professional skill-set.
Each chapter discusses the applicability of the traits to the contributor’s own work and experience as an investigator. more
*Robert Rahn (Lt. Ret.) is one of the excellent contributors.
ISBN-13:
978-1138353787
ISBN-10:
1138353787
FutureWatch: The Demise of the Common Spies
Not so long ago, Secret Agent Man could globe-hop with impunity (sing-a-long) and hide with undercover diplomatic immunity. Now, he may as well wear the Scarlet Letter "A", for Agent.
WTF happened? Quite a bit...
9/11, for one. It's not so easy to fly under the radar these days.
In 2014, U.S. spies were exposed when the Office of Personnel Management was hacked. About 22 million fingerprints, security clearance background information, and personnel records allegedly fell into Chinese hands. In 2015 it happened again.
One can be fairly sure this isn't just a problem for U.S. spies. Other countries get hacked, too. You just don't hear about it.
If all this wasn't bad enough, a spy's best friend turned on him in the 2000's. Technology.
Video cameras are planted everywhere, and facial recognition is becoming more accurate every day. It is being used at airports, in buildings, and with in conjunction with city surveillance cameras. This list will grow, of course.
The latest advancement is analysis of video streams using artificial intelligence logarithms. Suspicious movements, packages left unattended, predictions of future movements and crimes are analyzed by mindless machines 24/7, waiting to trigger an alert.
On the communications side spyware is a concern. Smartphone and GPS tracking don't help spies hide either.
It has been reported that some countries are compiling real-time databases which incorporate the above-mentioned speed bumps with: taxis, hotel, train, airline, credit card, customs and immigration information. As soon as one enters the country, they know where you are—minute by minute. And, if one takes too long going between locations, or a dual timeline appears (being in different places at the same time), a security alert is generated.
Couple all this with countries sharing information, e.g. EU, being a spy who needs to make in-person contacts becomes nearly impossible.
Think staying out of view is a good spy strategy? For now, perhaps. However, progress is being made by constructing a person's face by the sound of their voice.
The future of spying (no, it won't go away) will be radically different out of necessity. One can only guess how, but I understand they are working very hard on mind-reading.
Be seeing you.
WTF happened? Quite a bit...
9/11, for one. It's not so easy to fly under the radar these days.
In 2014, U.S. spies were exposed when the Office of Personnel Management was hacked. About 22 million fingerprints, security clearance background information, and personnel records allegedly fell into Chinese hands. In 2015 it happened again.
One can be fairly sure this isn't just a problem for U.S. spies. Other countries get hacked, too. You just don't hear about it.
If all this wasn't bad enough, a spy's best friend turned on him in the 2000's. Technology.
Video cameras are planted everywhere, and facial recognition is becoming more accurate every day. It is being used at airports, in buildings, and with in conjunction with city surveillance cameras. This list will grow, of course.
The latest advancement is analysis of video streams using artificial intelligence logarithms. Suspicious movements, packages left unattended, predictions of future movements and crimes are analyzed by mindless machines 24/7, waiting to trigger an alert.
On the communications side spyware is a concern. Smartphone and GPS tracking don't help spies hide either.
It has been reported that some countries are compiling real-time databases which incorporate the above-mentioned speed bumps with: taxis, hotel, train, airline, credit card, customs and immigration information. As soon as one enters the country, they know where you are—minute by minute. And, if one takes too long going between locations, or a dual timeline appears (being in different places at the same time), a security alert is generated.
Couple all this with countries sharing information, e.g. EU, being a spy who needs to make in-person contacts becomes nearly impossible.
Think staying out of view is a good spy strategy? For now, perhaps. However, progress is being made by constructing a person's face by the sound of their voice.
The future of spying (no, it won't go away) will be radically different out of necessity. One can only guess how, but I understand they are working very hard on mind-reading.
Be seeing you.
Surveillance is Hot at CES 2020
At CES show, devices that see, hear, track people are promoted. Privacy concerns? Not so much.
From the face scanner that will check in some attendees to the cameras-everywhere array of digital products, the CES gadget show is all-in on surveillance technology...
All these talking speakers, doorbell cameras and fitness trackers come with the promise of making life easier or more fun, but they're also potentially powerful spying tools.
And the skeptics who raise privacy and security concerns can be easily drowned out in the flashy spectacle of gee-whiz technology. more
From the face scanner that will check in some attendees to the cameras-everywhere array of digital products, the CES gadget show is all-in on surveillance technology...
All these talking speakers, doorbell cameras and fitness trackers come with the promise of making life easier or more fun, but they're also potentially powerful spying tools.
And the skeptics who raise privacy and security concerns can be easily drowned out in the flashy spectacle of gee-whiz technology. more
Monday, January 6, 2020
Information Security and Cryptography Seminar
 Information Security and Cryptography —
Information Security and Cryptography —Fundamentals and Applications
June 8-10, 2020 in Zurich, Switzerland
Lecturers: Prof. David Basin and Prof. Ueli Maurer
This seminar provides an in-depth coverage of Information Security and Cryptography from both a conceptual and an application-oriented viewpoint. At the same time, the mathematical, algorithmic, protocol-specific, and system-oriented aspects are explained in a way understandable to a wide audience.
A full description of the seminar, including all topics covered, is available at https://www.infsec.ch/seminar2020.html. Early registration is until February 28th.
The seminar takes place in Zurich Switzerland. The lectures and all course material are in English. more
Thursday, January 2, 2020
U.S. Securities & Exchange Commission Issues Guidance on IP and Tech Risks
 ...Among the risks faced by companies is the risk of theft of technology,
data and intellectual property through a direct intrusion by private
parties or foreign actors, including those affiliated with or controlled
by state actors.
...Among the risks faced by companies is the risk of theft of technology,
data and intellectual property through a direct intrusion by private
parties or foreign actors, including those affiliated with or controlled
by state actors.While not exclusive, examples of situations in which technology, data or intellectual property may be stolen or compromised through direct intrusion include cyber intrusions into a company’s computer systems and physical theft through corporate espionage, including with the assistance of insiders... more
Your Smart TV is Spying on You — How to stop it...
Those smart TVs that sold for unheard of low prices over the holidays come with a catch. The price is super low, but the manufacturers get to monitor what you're watching and report back to third parties, for a fee.
Or, in some cases, companies like Amazon (with its Fire TV branded sets from Toshiba and Insignia) and TCL, with its branded Roku sets, look to throw those same personalized, targeted ads at you that you get when visiting Facebook and Google.
It doesn't have to be this way. You have the controls to opt out. Within just a few clicks, you can stop the manufacturers from snooping on you in the living room... more and a bonus sing-a-long!
Or, in some cases, companies like Amazon (with its Fire TV branded sets from Toshiba and Insignia) and TCL, with its branded Roku sets, look to throw those same personalized, targeted ads at you that you get when visiting Facebook and Google.
It doesn't have to be this way. You have the controls to opt out. Within just a few clicks, you can stop the manufacturers from snooping on you in the living room... more and a bonus sing-a-long!
Subscribe to:
Comments (Atom)