via Dolos Group, LLC
What can you do with a stolen laptop?
Can you get access to our internal network?
That was the question a client wanted answered recently. Spoiler alert: Yes, yes you can. This post will walk you through how we took a “stolen” corporate laptop and chained several exploits together to get inside the client’s corporate network.
Friday, July 30, 2021
Better Not Lose Your Laptop - A Cautionary Tale
From the Man Who Brought Us Every Kid's First Spy Toy - Ron Popel (RIP)
How many Mr. Microphones wound up behind the couch when the younger brother's older sister brought her date home?
Tuesday, July 27, 2021
There’s Almost Certainly a Spy in Your Office
A recent paper from the US Senate suggests advanced actors now regularly plant individuals in large organizations, with a view to stealing data and research that can be used for economic, scientific or military gain.
China, for example, is said to operate more than 200 different recruitment programs, the most elaborate of which is the Thousand Talents Plan, which is estimated to have recruited 7,000 operatives or more. And China is by no means the only country to engage in these behaviors...
In rare instances, when recruiters fail to gain access to an employee, they have been known to train up an individual specifically for the task. Known as “embeds”, these imposters are much closer to traditional spies and have a full understanding of the ambitions of their handlers.
“Sometimes, these embeds are quiet for a long time, even years. Then all of a sudden they gain access to the information they were recruited to hunt down, before disappearing into thin air. There is another level of tradecraft on display here.” more
Note: Embeds are in the best position to plant eavesdropping devices (disguised voice recorders, Wi-Fi data leaches, USB spy cables, GPS trackers, GSM cellular bugs, etc.) Periodic searches for these devices thwarts their efforts. Sometimes just by them knowing the organization conducts searches. And, of course, by discovering the devices before they can do long-term harm.
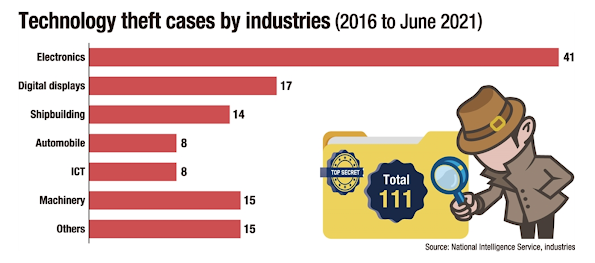
Corporate Espionage: Things are Tough All Over
Korea's tech industries are increasingly becoming the
target of technology and intellectual property theft that has been
growing in sophistication and harmfulness...
With
industrial espionage, competitors' poaching of skilled employees,
cyberattacks and other forms of theft being rampant, the world has been
introducing stricter rules to ban theft of competitors' technologies
across borders...
Industrial espionage and cyberattacks are still
favored forms of theft, with the targets changing from conglomerates to
their subcontractors, many of them small- and medium-sized enterprises
(SMEs) that are often ill-equipped in terms of security and management. more
Deadly Corporate Espionage Case Settled
Credit Suisse has reached an out-of-court settlement with former star banker Iqbal Khan over allegations of spying that led to the resignation of the Chief Executive Tidjane Thiam, a spokesperson for the Swiss bank said...
The affair became public when Khan, after defecting to UBS, confronted a private detective who was following him and his wife through Zurich.
What Credit Suisse initially described as a rogue spying case run by then-Chief Operating Officer Pierre-Olivier Bouee widened as details emerged of other instances of surveillance.
As
well as the departures of Bouee and Thiam, a private investigator who
organized the surveillance committed suicide after the affair came to
light. more
Pegasus v. iPhone Update - iOS 14.7.1 Plugs the Loophole
Apple has reportedly fixed the vulnerability in iOS 14.7.1.
The security notes don’t specifically mention Pegasus, but they refer
to “a memory corruption issue” that “may have been actively exploited.” more
Friday, July 23, 2021
Pegasus Spyware Update: How to Check Your iPhone
If you’re concerned about recent reports of the Pegasus spyware reportedly installed by the Israeli NSO Group to hack journalists and world leaders, there’s a tool to check if it’s hidden on your iPhone. But you probably have nothing to worry about...
But if you’re concerned, there’s a way to test whether your iPhone has
been targeted. It’s not an easy test, mind you, but if you’re using a Mac or Linux PC and have backed up your iPhone using it, Amnesty International’s the Mobile Verification Toolkit
will be able to detect whether your phone has the Pegasus spyware
installed on it. The tool, which TechCrunch tested, works using the
macOS Terminal app and searches your latest iPhone backup on your Mac,
“is not a refined and polished user experience and requires some basic
knowledge of how to navigate the terminal.” You’ll need to install
libusb as well as Python 3 using Homebrew. (You can learn more about the
installation here.) TechCrunch says the check only takes “about a minute or two to run” once it’s been set up. more
Monday, July 19, 2021
Private Espionage Is Booming - The US Needs a Spy Registry
via Wired Magazine...
Years ago, while stationed
in Moscow as the bureau chief for a major news magazine, I was
approached by a representative of a multinational company and presented
with a tantalizing offer. He said he had highly sensitive materials
exposing possible criminal activity by a Russian competitor. The
documents were mine with one condition: advance notice so he could be
out of the country when any story was published.
I had every reason to think the materials came from a private intelligence operative hired by the company—there were many such operatives in Moscow—but I didn’t ask my source for his source. Instead I embarked on a somewhat harrowing investigation of my own, and on corroborating the materials, I was able to publish a splashy story.
This episode came back to me while reading Barry Meier’s new book, Spooked: The Trump Dossier, Black Cube, and the Rise of Private Spies. A former New York Times investigative reporter, Meier casts a harsh light on both “private spies” and journalists who make frequent use of nuggets unearthed by these operatives. In the book’s afterword, he revives an idea for “a kind of ‘spy registry’ in which operatives for hire would have to disclose the names of their clients and assignments,” just as Congress now requires of lobbyists hired to influence legislators.Is this truly a problem in need of a solution? Or would a spy registry create worse problems?
It’s tempting to conclude that there is really nothing new here and that private spies may even supply a public service. In the original, late-19th-century Gilded Age, the Pinkerton Detective Agency devoted itself to the art of subterfuge. In 1890, a Pinkerton man went undercover on behalf of his client, the governor of North Dakota, and confirmed from rigorous barroom investigation that a fair amount of “boodle,” bribe money, was being dispensed by advocates of a state lottery opposed by the governor. The governor revealed the dirty dealings to the public, and the lottery scheme failed—all perhaps to the civic good.Today’s
circumstances are far different. Inexpensive, off-the-shelf
technologies for surveillance, hacking, and spoofing make the spy game
easier to play than ever before. What hired sleuth doesn’t now travel
with one of those metallic-fabric bags that blocks cellphone GPS
signals, like the GoDark Faraday model that sells online for $49.97?
It’s an insignificant item on the expense report. more
US Warns Businesses in Hong Kong About Electronic Surveillance
The advisory, which was nine pages long, was issued by the Departments of State, Treasury, Commerce and Homeland Security. It alerted businesses to the possible risks associated with doing business in Hong Kong. According to the advisory, businesses are at risk from electronic surveillance without warrants and the disclosure of customer and corporate data to authorities. more
Pegasus Spyware Back in the News
India Today... Pegasus spying: how Pegasus is installed on phone, what it does, and how to get rid of it...
- Pegasus can be installed on vulnerable phones through a web link or a missed call.
- The spyware can steal passwords, contacts, text messages, and photos.
- The only way to avoid Pegasus after it has infected a phone is by getting rid of the phone.
Pegasus, developed by Israeli cybersecurity firm NSO Group, is a highly sophisticated spyware that has been referred to as the "most sophisticated smartphone attack ever". It was first noticed in 2016 but created a lot of buzz in late 2019 when it was revealed that the spyware was used for snooping on journalists and human rights activists across the globe, including in India. more
Tech Xplore... Pegasus spyware: how does it work?More recent versions of Pegasus, developed by the Israeli firm the NSO Group, have exploited weak spots in software commonly installed on mobiles.
In 2019 the messaging service WhatsApp sued NSO, saying it used one of these so-called "zero-day vulnerabilities" in its operating system to install the spyware on some 1,400 phones.
By simply calling the target through WhatsApp, Pegasus could secretly download itself onto their phone—even if they never answered the call.
More recently, Pegasus is reported to have exploited weaknesses in Apple's iMessage software.
That would potentially give it access to the one billion Apple
iPhones currently in use—all without the owners needing to even click a
button. more
Why You Can't Get James Bond's Custom Martini These Days
via Futility Closet... (worth subscribing)
In the first James Bond novel, 1953’s Casino Royale, Bond orders a drink of his own invention:
‘A dry martini,’ he said. ‘One. In a deep champagne goblet.’
‘Oui, monsieur.’
‘Just a moment. Three measures of Gordon’s, one of vodka, half a measure of Kina Lillet. Shake it very well until it’s ice-cold, then add a large thin slice of lemon peel. Got it?’
‘Certainly monsieur.’ The barman seemed pleased with the idea.
‘Gosh, that’s certainly a drink,’ said Leiter.
Bond laughed. ‘When I’m … er … concentrating,’ he explained, ‘I never have more than one drink before dinner. But I do like that one to be large and very strong and very cold, and very well-made. I hate small portions of anything, particularly when they taste bad. This drink’s my own invention. I’m going to patent it when I think of a good name.’
The name he thinks of is the Vesper, ostensibly inspired by the character Vesper Lynd. But in fact the recipe wasn’t original to Bond — Fleming had first received the drink from the butler of an elderly couple in Jamaica — it was named after vespers, a service of evening prayer. Bond says, “It sounds perfect and it’s very appropriate to the violet hour when my cocktail will now be drunk all over the world.” He’d have trouble getting one today — Kina Lillet was discontinued in 1986, and the strength of Gordon’s Gin was reduced in 1992.
Thursday, July 15, 2021
The "Encrypted" Cell Phones Had One Flaw: The FBI Controlled Them
The criminals texted each other about drug deals and money laundering, confident in special encrypted devices using a platform dubbed Anom. There was just one problem for the crime rings: The FBI was being copied on every message — millions of them worldwide. In fact, the agency had sent the Anom devices into the black market in the first place.
Those are the details and allegations that are now emerging about Operation Trojan Shield, an international effort coordinated by the FBI that has resulted in more than 800 arrests.
With the help of Europol, the FBI identified "over 300 distinct TCOs [transnational criminal organizations] using Anom, including Italian organized crime, Outlaw Motorcycle Gangs, and various international narcotics source, transportation, and distribution cells," according to a search warrant affidavit filed in court by Nicholas Cheviron*, an FBI special agent in San Diego. The document was unsealed Monday.
In addition to heading the investigation, FBI Special Agent, Nic Cheviron (son of the best corporate security director ever), wrote the search warrant. It is a fascinating read.
Wednesday, July 14, 2021
Quantum Disappointment to Quantum Reserection
In theory, quantum cryptography enables two or more people to communicate with one another in complete secrecy. In practice, eavesdroppers can exploit weaknesses in the equipment used to send and receive secret keys.
Researchers in Singapore have now shown how practice can be brought closer to theory—by inserting a fairly simple passive device to prevent eavesdropping attacks involving bright light (Phys. Rev. X, doi: 10.1103/PRXQuantum.2.030304). They reckon their solution could be widely adopted in future, having shown that it can be applied to a number of popular cryptographic schemes...Here is how it works.Don't worry if you don't get it.
Just pretend Dr. Emilio Lizardo is doing the explaining.
Their device exploits an acrylic prism with a negative thermo-optical
coefficient. Incoming light generates a gradient in temperature, and
therefore in refractive-index, inside the prism that turns the acrylic
into a concave lens. A small aperture placed behind the prism blocks
most of the resulting diverged light beam, diminishing the beam power. more
Weird Science - Windows that Prevent and Facilitate Eavesdropping (you decide)
Radio frequency defense film, also known as RF
attenuation window film or anti-eavesdropping film, protects homes or
workplaces against radio frequencies and electromagnetic radiation. The
RF film that the customer requires meets strict security requirements
for facilities handling classified or other sensitive information. The
government customer has requested to remain anonymous for security
reasons. more
We've been down this road before, in 2007 and 2009.
•••
Listening & Anti-Eavesdropping Device
(18 years ago this month)
Abstract
A method and apparatus for transmitting information from a conversation in a room to a remote listener comprising selecting a structure (101) in the room which is capable of supporting vibration, selecting an electromechanical force transducer (90) which has an intended operative frequency range and comprises a resonant element (84, 86) having a frequency distribution of modes in the operative frequency range, mounting the transducer (90) to the structure (101) using coupling means (68) whereby the transducer excites vibration in the structure, positioning a sensor to detect vibration in the structure (101), determining information from the detected vibration and transmitting said information to a remote listener. There is also provided an anti-eavesdropping system which is the reverse of the method and apparatus according to the first and second aspects of the invention. (self-licking ice cream cone) more
Nervy Doctor Arrested - Spy Cameras Found in Woman Doctor's Bedroom & Bath
"The accused doctor is a neurologist lecturer at a city-based medical college," said Jagannath Kalaskar, senior police inspector, Bharti Vidyapeeth police station.
Last week, the trainee doctor had tried to switch on the bulb in her bathroom, however, it did not work. She then called an electrician who spotted a spy camera installed in the bulb. The doctor found another spy camera in her bedroom too, following which she lodged a police complaint. more