By
April White, Smithsonian Magazine
For the last several years, Brian Hochman has been studying electronic surveillance—both the technological developments that have made eavesdropping possible and the cultural and political realities that have made it a part of American life for more than 150 years...
How far back do we have to go to find the origins of wiretapping?
It starts long before the telephone. The earliest statute prohibiting wiretapping was written in California in 1862, just after the Pacific Telegraph Company reached the West Coast, and the first person convicted was a stock broker named D.C. Williams in 1864. His scheme was ingenious: He listened in on corporate telegraph lines and sold the information he overheard to stock traders...
It’s only in the 1920s that ordinary Americans start to take notice of wiretapping and it's not really until the 1950s that it's seen as a national problem...
 |
The House Intelligence Committee looked into illegal wiretapping in 1975 as part of its investigation of risks of U.S. intelligence operations.
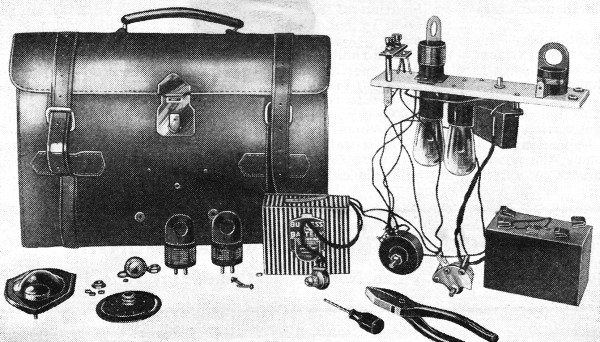
Michael Hershman (holding a 'plug bug') explaining surveillance and counter-surveillance technology. (AP Photo/Charles Gorry)
|
Historians are not in the business of prognostication, but the one thing that I can say with some certainty is that electronic surveillance and dataveillance are going to scale. They will be more global and more instantaneous. I can say with much more certainty that that public attention to these issues will wax and wane. more