 |
| Click to enlarge. |
After polling 1,500 users, he discovered that 52 percent of those users "open" their device with a simple slide or gesture, 25.5 percent have opted to locking their phones with drawing a pattern on a grid, and 15.1 percent are using a PIN.
Only 3.3 percent have opted for using a password, 2.3 percent for the option where the phone can recognize their face, and 1.8 percent are using other, 3rd party forms of authentication...
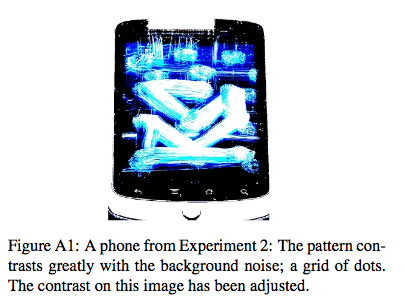
...no security is perfect. Both lock patterns and PIN codes can be vulnerable to smudge attacks, as a 2010 Usenix paper illustrates. So whether you use a PIN or a pattern you should change it from time to time. You might also want to go to your phone’s options screen and disable the display of the pattern so people can’t “shouldersurf” it. (more)
















