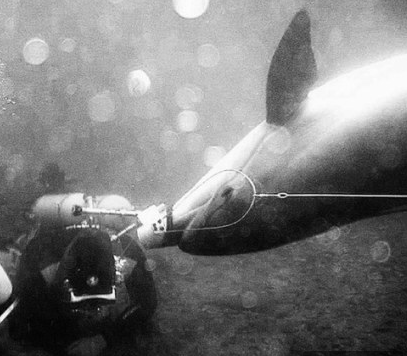
Ukraine’s secret unit of spy DOLPHINS that can plant bombs and attack divers with guns have defected to Russia.
- The Ukraine Army has been using dolphins and seals since the 70s
- After the fall of the USSR, the 'dolphin spies' remained in the Ukraine
- The dolphins have been trained to hunt for mines and plant bombs
- They can also attack divers with knives or pistols attached to their heads
- Now, military dolphins in Crimea will be transferred to the Russian Navy
While the dolphins show extraordinary intelligence, sometimes they disobeyed their Ukrainian commanders.
Last year three of five spy dolphins went absent without leave in the Black Sea - apparently in search of love, but returned to their duties shortly afterwards.
Yury Plyachenko, a former Soviet naval anti-sabotage officer, explained that this was something that had to be taken into account in working with the 007 mammals.
‘If a male dolphin saw a female dolphin during the mating season, then he would immediately set off after her. But they come back in a week or so.’ (more)
Federal agents notified more than 3,000 U.S. companies last year that their computer systems had been hacked, White House officials have told industry executives, marking the first time the government has revealed how often it tipped off the private sector to cyber intrusions.
The alerts went to firms large and small, from local banks to major defense contractors to national retailers...
“Three thousand companies is astounding,” said James A. Lewis, a senior fellow and cyberpolicy expert at the Center for Strategic and International Studies. “The problem is as big or bigger than we thought.”
The number reflects only a fraction of the true scale of cyberintrusions into the private sector by criminal groups and foreign governments and their proxies, particularly in China and Eastern Europe. The estimated cost to U.S. companies and consumers is up to $100 billion annually, analysts say. (more)
...your network has been breached before you do?
Knock, knock! Secret Service here. "Is this your customer payment card data?"
By all accounts, many of the massive data breaches in the news these days are first revealed to the victims by law enforcement, the Secret Service and Federal Bureau of Investigation (FBI). But how do the agencies figure it out before the companies know they have been breached, especially given the millions companies spend on security and their intense focus on compliance?
 The agencies do the one thing companies don’t do. They attack the problem from the other end by looking for evidence that a crime has been committed. Agents go undercover in criminal forums where stolen payment cards, customer data and propriety information are sold. They monitor suspects and sometimes get court permission to break into password-protected enclaves where cyber-criminals lurk.
They have informants, they do interviews with people already incarcerated for cybercrime, and they see clues in the massive data dumps of information stolen from companies whose networks have been breached. (more)
The agencies do the one thing companies don’t do. They attack the problem from the other end by looking for evidence that a crime has been committed. Agents go undercover in criminal forums where stolen payment cards, customer data and propriety information are sold. They monitor suspects and sometimes get court permission to break into password-protected enclaves where cyber-criminals lurk.
They have informants, they do interviews with people already incarcerated for cybercrime, and they see clues in the massive data dumps of information stolen from companies whose networks have been breached. (more)
A spyware app developed by two researchers has shown that Google Glass can
be used to secretly take photos of whatever a Glass wearer is looking
at without their knowledge - making the Glass user the one whose privacy
and security is potentially compromised. (more)
Security researchers said they have uncovered bugs in Google's Android
operating system that could allow malicious apps to send vulnerable
devices into a spiral of endlessly looping crashes and possibly delete
all data stored on them. (more)
Stingray is a US law enforcement spoof cell tower used to track the location of mobile phones. Snoopy is a project conducted by London-based Sensepost Research Labs that does similar and much more with any WIFI-enabled device. Now Snoopy has gone airborne – mounted on a drone it can hover above a target area and trick mobile devices into connecting: a form of flying man-in-the-middle attack... The drones collect the devices' probe requests, which could be looking for networks that the user has recently connected to, and mimic them. "If your device is probing for 'Starbucks', we'll pretend to be Starbucks, and your device will connect." Once that connection is made, Snoopy can listen in. (more)
A putative class of Capital One Bank NA cardholders in five states have
secured a $3 million settlement of claims that the bank covertly
recorded outbound customer service calls, according to documents filed
Monday in California federal court.
The pact puts to rest a suit
over the bank’s alleged violations of California’s Invasion of Privacy
Act and the similar two-party consent laws of Florida, Maryland, Nevada
and New Hampshire. (more)
Is your organization doing any recording? What's in your policy?
Ireland's police chief resigned Tuesday following months of criticism of how his force handled allegations of illegal wire-tapping and corrupt enforcement of traffic laws.
Underscoring a growing sense of public unease at police standards and behavior, government leaders announced that they would open a judge-led probe into new revelations that telephone calls at many police stations had been illegally recorded since the 1980s.
The government said it didn't yet know why the widespread recording was secretly happening. Security analysts said it could partly reflect an effort by senior commanders to monitor rank-and-file officers' communications...
It said a judge would be appointed to examine why police had secretly recorded telephone conversations in and out of many police stations for several years, a practice ended only in November after the first wire-tap scandal became public knowledge. (more)
A new bot with the name Zorenium has landed in the criminal underground, with the ability to target Apple iOS devices like iPhone and iPad. It's not widely known, nor is it widely detectable...
The analysis suggests that Apple devices must be jail-broken to be vulnerable, which makes sense given Apple’s tight control over the iOS ecosystem—there’s a reason after all that virtually all mobile malware targets Android. (more)
Former US President Jimmy Carter has said he hand-writes letters to foreign and US leaders in an effort to evade what he described as pervasive US electronic surveillance.
Mr Carter, 89, told the Associated Press he had "no doubt" the US monitored and recorded "almost every telephone call" and email.
His humanitarian efforts bring him in contact with a range of foreign and US political leaders. (more)
UK - A man who thought someone was using a security camera to spy on his girlfriend tried to break the devices, a court has heard.
The man, 33-year-old Richard Hill, later assaulted the operator (Mr. Jordan) when confronting him over his use of the devices...
Peter Love, prosecuting, told Worcester Magistrates’ Court...
“He was swearing at him (Mr. Jordan) and punched him in the face.
“He then head-butted him in the nose and ran off towards the city centre.”
When Hill was interviewed about the offences he said he struck the camera because he was told Mr Jordan was using the device to watch his girlfriend. He said he assaulted him because he had made him angry. (more)
"It's a well-known fact that businesses world-wide invest thousands or even millions protecting themselves from hackers and perceived cyber threats, but often fail to protect themselves against the threat of technical surveillance." –Peter Rucinski of Assure Technical, speaking about lack of attention businesses pay to finding bugs, wiretaps, spycams and other forms of electronic surveillance. (source)
What do you get when you combine 368, 5.0-megapixel smartphone cameras into a mosaic and then add some other classified parts?
The DARPA-funded Autonomous Real-Time Ground Ubiquitous Surveillance Imaging System (or ARGUS-IS) of course. According to PetaPixel, "ARGUS-IS is a 1.8 Gigapixel drone-mounted surveillance system that took 30 months and $18.5M to become a reality. The video above is a clip from a new PBS documentary titled 'Rise of the Drones'. It offers a fascinating peek at what the drone cam is capable of." (more)
Wireless surveillance (company) iWatchLife today released the results of a new poll indicating that nearly one in three people are completely comfortable with the idea of using electronic surveillance to watch over their elderly parents who live alone.
The poll, commissioned by iWatchLife and undertaken by Persona Research on March 16, 2014, surveyed 500 people. Respondents were asked if they would ever consider using electronic surveillance to ensure that their parents were safe. Over 30 percent said yes. (more)
While classified and clearly-defined national security information will always be sought-after by our adversaries, there is a rapidly growing interest in corporate America’s intellectual property.
By Doug Thomas, Lockheed Martin Corporation, a 2014 CSO40 award recipient
Throughout much of my 35 years of government service, I was focused on what many people are still focused on today: cleared people, classified programs, and traditional national security...
Yesterday’s spies were government employees or military personnel, stealing classified information... Today’s depiction of espionage takes on a very different picture.
Today’s spies also come from private industry -- financial institutions, industrial fabricators, defense contractors, members of academia, etc. ...stealing information on behalf of the intelligence service of a foreign nation state, or industrial espionage, where information is stolen to benefit a competitor, either foreign or domestic...
Today there is no difference between national security and economic security. By failing to safeguard the fruits of our innovative labor... we face the prospect of losing our position as a leader in the global marketplace.
The threat... is very real and growing at an aggressive rate...
I urge private industry leadership to take steps to counter this growing threat to our economic prosperity and national security. (more)
My two cents.
My other two cents.
A former Idaho lawmaker decided to hide in a Senate chamber closet for five to six hours on Tuesday, presumably to eavesdrop on her colleagues.
A rule in the Idaho Legislature allows floor privileges for former state senators. But the state Senate voted 28-6 on Wednesday to suspend that rule for one of their former colleagues—Nicole LeFavour. The day before, LeFavour—Idaho's first openly gay state lawmaker—had been discovered hiding in a closet behind the Senate chamber and was asked to leave.
"Closets are never safe for gay or transgender people," she told the Spokesman-Review. (more)