Japan - 'Bar set low for secret filming' The reason police in Japan commit voyeurism... It seems there is no end to police officers being subjected to
disciplinary measures for taking sneak footage. As law enforcers who are
in a position to crack down on camera voyeurs, why do they partake in
such crimes? The Mainichi Shimbun asked an expert... more
UK -
Professional photographer Roy Strutt, 64, installed a USB dongle with a hidden camera in the bedroom of his second home in Walberswick, Suffolk. He later invited a couple - who his wife knew through a friend - to stay at the property to celebrate their ninth wedding anniversary. The couple saw the dongle and unplugged it - with Strutt later telling them to plug it back in because it helped improve the Wi-Fi for the surrounding apartments.
moreLA - A Vidalia, Louisiana, man..
has also received additional charges... illicit videos involving a
juvenile taken by way of a hidden camera... investigators found evidence of a video
voyeurism set up by way of hidden camera, which illegally recorded
inappropriate videos of a juvenile. more
Singapore - Domestic helper jailed 17 months for filming elderly man in shower, uploading clips to TikTok, WhatsApp... One video was re-posted by an unknown user on a Facebook page titled SG Dirty Fella where it went viral. more
UK - A senior Metropolitan Police officer who
posed as an airline pilot and fake glamour photographer to picture up to
51 naked women has been dismissed from the force. Detective Inspector Neil Corbel, 40, took covert videos of his victims in hotel rooms, flats and Airbnbs... He
'used his anti-terror skills' to secretly film the women with spy
cameras hidden in tissue boxes, phone charges, glasses and keys after
contacting them under the guise of being an airline pilot named
Harrison. more
China - A male doctor live-streamed a patient’s gynecological procedure on a
China video-sharing website without her knowledge, raising a wave of
questions on medical ethics and privacy violations. more
UK - Scots student warns pervert stepdad will always be danger to kids after dodging jail for spying on her when she was 13... It came after the creep smirked as he was spared prison last week for secretly filming his stepdaughter through a gap drilled in her wardrobe. The predator also recorded her through the keyhole of a chest and a lens hidden in an alarm clock while on a family holiday in the US. more
WY - A 33-year-old Campbell County man has been charged with nine counts of
voyeurism after he allegedly set up a recording device in a bathroom and
took pictures of a female getting in and out of the shower and bathtub. more
Canada - Durham Regional Police have charged a man in connection with a voyeurism
investigation in Pickering, Ont... police were called to a Walmart store ... after a man was discovered
videotaping a female customer as she was using the change rooms. Police
said the suspect was confronted by the victim and her family and said he
had deleted the photos from his cellphone before fleeing. However,
police added there were other photos on his phone of other possible
victims and are asking for the public’s help in identifying the man. more more
LA - A Sulphur man was arrested after a
recording device was found in the women’s restroom of a local restaurant
Tuesday, according to information from the Sulphur Police Department. The device was found before anyone in the general public was captured on video, according to Sulphur officials. more
CT - A Vernon man is being charged after police say they discovered he put
cameras in his home bathroom and secretly recorded his girlfriend and
her children... a few years ago, two of the children, who were 13
and 18 years old at the time, discovered a bluetooth speaker in a
bathroom that was actually a hidden camera... After the children found it, they secretly swapped out its SD
card and delivered the card to a friend’s house for safekeeping, the
warrant said. more
FL -
The businessman who filmed two naked women in an adjoining Key West,
Florida hotel room has been sentenced to a year in prison for his
felonious voyeurism, court records show...
charged with sliding a tiny camera under the door separating his room at
the DoubleTree Grand Key resort from that of two female vacationers,
according to an
arrest report... Cops found the spy camera hidden in a chair cushion.
more WA - Former county fire marshal faces felony voyeurism charges... The charging documents allege Nicholson
had hidden a camera in a sleeping area at the station, filming a female
firefighter changing before getting into bed. When
contacted by the detective, the firefighter that was depicted in the
film stated she had not given consent to being filmed. The detective
investigated the room and discovered an outlet that matched up with the
angle of the video, although there was no recording device present when
he inspected the outlet. more
UK - Robert Davies, 32, came to the attention of National Crime Agency
investigators in 2019 after he purchased a number of cyber crime tools,
including crypters and remote administration tools (RATs)... Davies was infecting his victims’ phones or computers with malicious
software by disguising it with the crypters so their anti-virus
protection would not detect it. He then used the RATs to gain remote
access to their devices and steal any sexual images (mainly of females)
they had stored on there. On at least one occasion, he used his illegal access to spy on a
teenage girl through her webcam, turning the encounter into a number of
indecent images. more more
General - Laws on surveillance cameras at home can vary by state. As there’s no
comprehensive set of regulations that govern residential security
cameras or video surveillance, it’s essential to have a broad
understanding of the concerns involved with these systems and devices.
It’s just as important to know the laws at the state, county, and even
local levels. more
The Epoch Times - Video Report: Spy Cameras, Blackmail Rampant in China more
These stories are presented to raise awareness.
Spycam Facts:
- Only the failed video voyeurs make the news.
- Most spycam attacks go undetected.
- A few are discovered... almost all by accident.
- Only a few of these are reported to the police.
- Only a few of these cases are solved.
- Only few of these make it to my desk.
- I only share just a few of those with you.
- The problem is bigger than you think.
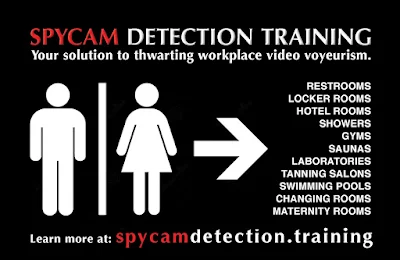
Any organization with expectation of privacy areas needs this to protect their employees, visitors and customers ... and themselves, from forseeability law suits.