Thursday, February 17, 2022
What Could be the Penalty for Posting a Spycam Video to the Net?
Monday, February 14, 2022
An Update on AirTag and Unwanted Tracking
Apple has been working closely with various safety groups and law enforcement agencies. Through our own evaluations and these discussions, we have identified even more ways we can update AirTag safety warnings and help guard against further unwanted tracking...
Advancements Coming to AirTag and the Find My Network
The following updates represent important steps Apple is taking... more
Saturday, February 12, 2022
Why You Rarely Hear About Corporate Espionage
Corporations really hate publicity about their information security failures.
The smart ones sweep to mitigate the chances of failures.
The others just sweep the failures under the rug.
Case in point...
Spanish power company Iberdrola is suing the holding company of business news site El Confidencial over coverage of an industrial espionage case, a move the site's director says threatens its survival.The multinational energy firm, which is seeking $20 million in damages, said that for more than two years up to November 2021, El Confidencial published 225 stories on the espionage case, including 68 that harmed the company and 12 that were untrue.
The company contends the reports were a "violation of its right to honour," a term that in Spanish law refers to reputational damage. more
VR Headset Hacks Could Steal Sensitive Information
Researchers at Rutgers University-New Brunswick have published “Face-Mic,” the first work examining how voice command features on virtual reality headsets could lead to major privacy leakages, known as “eavesdropping attacks.”
The research shows that hackers could use popular virtual reality (AR/VR) headsets with built in motion sensors to record subtle, speech-associated facial dynamics to steal sensitive information communicated via voice-command, including credit card data and passwords.
Foreign Spies Use Dating Apps... to access government secrets
Foreign spies are using Tinder and other dating apps to recruit Australians with access to sensitive government secrets. ASIO boss Mike Burgess made the alarming revelation while delivering his annual threat assessment, in which he also warned identifying anti-vaccine activists who could turn violent was proving difficult. more
---
The National Security Service of Armenia (HAAT) has detained 19 people suspected of being members of an "espionage network" in the South Caucasus nation. The HAAT said on February 10 that dozens of servicemen in different units of the the armed forces may have been involved in the activities of the spy network, which worked for an unspecified nation.
According to the security agency, recruitment took place via an
online dating service through which Armenian servicemen who possessed
classified data and documents would eventually join the spy ring. more
9 Potential Signs of Corporate Espionage
If you suspect that your business has been a target of corporate espionage, it's essential to take action immediately — from doing an in-house investigation to hiring a private professional.
If you see any of the below signs, don't ignore them, but also take care not to make any unfounded accusations or statements. Keep your thoughts closely held and get the evidence first...
1. Unexplained or sudden changes in practices
2. Changes in business relationships
3. Unusual computer activity
4. Becoming defensive or secretive about work
5. Equipment or files go missing
6. Unexplained drops in sales or profits
7. Employees quitting suddenly
8. Accessing computer files without permission
9. Corporate secrets leaked to the press more
School Principal Arrested - Facing Felony Eavesdropping Charge
The Lee County Virtual School Principal faces charges for illegally recording a meeting.
It is an unusual case of consent because Florida Statute 934.03 talks
specifically about the interception and disclosure of wire, oral or
electronic communications prohibited. “Florida is a two-party consent state,” said FGCU Professor Dr. David Thomas. Lee County Sheriff’s deputies arrested (him) for recording a meeting without permission. more
Ford Wants to Hide Spy Drones in Autonomous Cars
Among the many challenges facing the autonomous car industry is how to keep an eye on the condition of the vehicles while they're out and about.
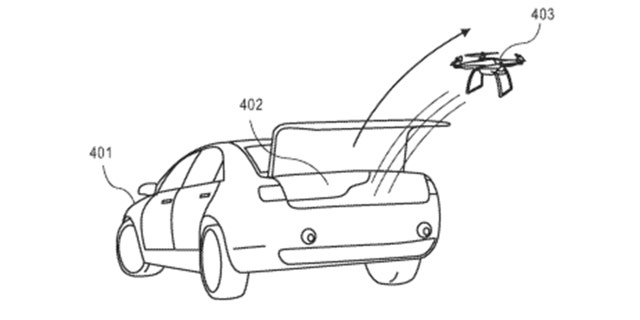
Ford, which co-owns the Argo AI autonomous car company that's planning to launch a ride-hailing service soon, has now patented a way to do just that. more
Hidden Wisconsin Restaurant Serves Espionage Fun With Food
A truly exceptional themed restaurant needs to go further than some wall decor and select menu items, it needs to provide a full theme experience, something that the SafeHouse Restaurant and Bar in Milwaukee, Wisconsin seems to have nailed completely. Let's put it this way, when you arrive at the 'hidden' SafeHouse, you need to provide a password to gain entry, but once you get inside the real show begins. morePersonal recommendation... The Mission Impossible - Go rogue with this mission. A large fishbowl filled with Bacardi Superior Rum, Roaring Dan's Dark Rum, orgeat, lemon, orange, pineapple, and grenadine - serves 2 spies nicely or 1 brave agent. more
Wednesday, February 9, 2022
GSM Eavesdropping Bugs: A Recent Find in a Corporate Office
While on lockdown, businesses and individuals must think about their unoccupied premises and possessions. Now that we are coming out of this lockdown and going back to work, Gurpreet Thathy and Mike Moran give their thoughts and go through a recent case with a client last week...
Mike and his team conducted a ‘sweep’ of the offices in conjunction with our Cyber Audit. We identified a GSM eavesdropping device planted within a boardroom during the critical areas’ in-depth physical and electronic search. This device was cunningly disguised as a 3-way extension adapter which was fully operational.
A closer examination of the adapter revealed a SIM card and a microphone connected. The client was immediately informed, and as per our standard operating procedure (SOPs), the device was isolated from the infrastructure, bagged, tagged, and handed over to our internal forensic team to investigate.
The forensic investigation of the SIM card revealed dialled and received calls. more
What is a GSM Bug? When was the last time your organization conducted an inspection for one?
Leaked Tapes Reveal Corporate Espionage
Testimony that Vatican officials engaged in corporate espionage sheds new light on the breakdown of the London property deal.
Luciano Capaldo is a property developer who was closely involved in the Vatican’s Secretariat of State plans for the London London property deal at 60 Sloane Avenue...
Capaldo told investigators that he had access to surveillance cameras inside Torzi’s offices for some time.
So he passed information and images to Monsignor Mauro Carlino, a former official at the Secretariat of State currently indicted for extortion and abuse of office. The access, Capaldo said, came via a mobile phone app for which he had the login details. more
Investigation-driven Findings Identify Major Spikes in Industrial Espionage Incidents
Key findings of the DTEX Systems 2022 Insider Risk Report include:
The ‘Super Malicious Insider’ accounted for 32% of malicious insider incidents...
72% year-over-year increase in actionable insider threat incidents;
42% of actionable incidents were related to IP and data theft, including industrial espionage incidents related to the theft of trade secrets, source code, and active collusion with a foreign nexus;
75% of insider threat criminal prosecutions were the result of remote workers;
56% of organizations had an insider data theft incident resulting from employees leaving or joining companies;
+200% year-over-year increase in data loss associated with users taking screenshots during confidential Zoom and Microsoft Teams meetings; and
+300% year-over-year increase in employees utilizing corporate assets for non-work activities.
For more than a decade, insider threats have been categorized as either malicious, negligent or compromised. Based on the findings of the DTEX i3 team, a fourth persona has emerged—the Super Malicious Insider.
The Super Malicious Insider is a technically proficient employee who is acutely aware of an organization’s cyber security architecture, solutions, and processes and who understands both the technical and human analyst limitations in detecting insider threat indicators. more
It is time for your organization to implement a corporate counterespionage plan.
The Unnerving Rise of Video Games that Spy on You
Tech conglomerate Tencent caused a stir last year with the announcement that it would comply with China’s directive to incorporate facial recognition technology into its games in the country.
The move was in line with China’s strict gaming regulation policies, which impose limits on how much time minors can spend playing video games—an effort to curb addictive behavior, since gaming is labeled by the state as “spiritual opium."
...video games are a natural medium for tracking, and researchers have long argued that large data sets about players’ in-game activities are a rich resource in understanding player psychology and cognition. more
US Indictment: Chinese Firm Stole Motorola Trade Secrets
A federal indictment unsealed Monday accuses a Chinese telecommunications company of stealing technology from Illinois-based Motorola Solutions Inc., in another case highlighting longstanding fears about China pilfering vital U.S. business secrets to bolster its own economy...
In a 2008 email cited in the indictment, one unnamed individual writes
to another that, “We are trying to grab whatever we can. … Do you have
anything in mind that you need while we are still here?” In another,
someone writes “haha” after describing Hytera as copying Motorola
technology...
A Chinese-born American software developer, Hanjuan Jin, was convicted in 2012 of stealing secrets from Motorola... At trial, prosecutors said Jin “led a double life” as an outwardly loyal company worker plotting to steal Motorola secrets. more
The "loyal" insider has the time and opportunity to steal information, plant bugs, and take advantage of lax security procedures. Periodic sweeps for covert eavesdropping devices, with an information security survey, are how smart corporations reduce this risk.
Burglar Steals $20K From Business Specializing in Security Cameras
Pro Systems is a communications company in South Nashville that has been around since the eighties and specializes in security cameras. But when employees arrived at work just weeks ago, they found their fence cut, and about $20,000 worth of items stolen.
The company, of course, reviewed their own equipment and handed over surveillance footage to the Metro Nashville Police. Within hours, officers were able to identify and arrest the suspect seen on the business’ security cameras. more in other surveillance camera theft news













