All Windows users should update immediately as ‘Complete Control’ hack is confirmed.
In case you were underestimating the tool, it can allow a hacker to remoting shutdown or reboot the system, remotely browse files, access and control the Task Manager, Registry Editor, and even the mouse.
Not only that, but the attacker can also open web pages, disable the webcam activity light to spy on the victim unnoticed and capture audio and video.
Since the attacker has full access to the computer, they can also recover passwords and obtain login credentials using a keylogger as well as lock the computer with custom encryption that can act like ransomware. more
Showing posts with label cautionary tale. Show all posts
Showing posts with label cautionary tale. Show all posts
Tuesday, August 27, 2019
Friday, August 23, 2019
Fighting Corporate Espionage — by a Counterintelligence Agent
Corporate executives must bear the responsibility... No longer is “Security” to the facility and personnel all that is required. Many foreign countries and interests take short cuts to becoming competitive through the theft of trade secrets, products and overt and covert espionage of all sorts...
Many of the tactics utilized in private sector counterintelligence have much in common with the secrets and information the government does its best to safeguard from theft...
 There are open and legal methods of collection open that are harmful and a good counterintelligence program should target this as well as illegal activities such as electronic eavesdropping, hacking, etc.
There are open and legal methods of collection open that are harmful and a good counterintelligence program should target this as well as illegal activities such as electronic eavesdropping, hacking, etc.
Passive counterintelligence tries to curtail what a collector may do through countermeasures, and awareness training. Active counterintelligence will prove beneficial to identify and detect a threat, and will conduct operations including eliminating threats or ongoing targeting... The leaders in the private sector need to be proactive and realize that it is no longer only local threats they face. The threats can be global and may not only be an economic threat but also a threat to national security. more
Many of the tactics utilized in private sector counterintelligence have much in common with the secrets and information the government does its best to safeguard from theft...
 There are open and legal methods of collection open that are harmful and a good counterintelligence program should target this as well as illegal activities such as electronic eavesdropping, hacking, etc.
There are open and legal methods of collection open that are harmful and a good counterintelligence program should target this as well as illegal activities such as electronic eavesdropping, hacking, etc.Passive counterintelligence tries to curtail what a collector may do through countermeasures, and awareness training. Active counterintelligence will prove beneficial to identify and detect a threat, and will conduct operations including eliminating threats or ongoing targeting... The leaders in the private sector need to be proactive and realize that it is no longer only local threats they face. The threats can be global and may not only be an economic threat but also a threat to national security. more
Tuesday, August 20, 2019
Phone Phreaking - The Next Frontier - Elevator Eavesdropping
Next time you’re in an elevator, be advised that someone – besides
building security and fellow elevator riders – might be listening.
A recent Wired article
exposed the hidden world of elevator phreaking. By calling an unsecured
elevator phone, a third party can expose a person, and potentially an
enterprise, to a major security and privacy risk.
Since elevator phones
don’t require anyone to pick up the phone to open the circuit, a third
party can make a call and be connected – allowing them to eavesdrop on
conversations happening inside the elevator.
Given the competitive
nature of industries like banking and technology, it isn’t completely
unthinkable for a hacker to eavesdrop this way. more
I know of a hotel in Miami which has bugged elevator—the one nearest the Boardroom; located on the Conference Floor level.
But, if bugged elevators aren't freaky enough, eavesdrop on elevators that talk! ~Kevin
Friday, August 9, 2019
Warshipping - The Next Corporate Espionage Headache
Hackers looking to gain access to your Wi-Fi network don’t necessarily have to lurk around your home or office, warns IBM X-Force Red.
Instead, writes Charles Henderson, global head of that security unit, they could simply ship you a package with a tiny, concealed device they can remotely control.
“In fact, they could ship multiple devices to their target location thanks to low build cost,” Henderson writes. “The device, a 3G-enabled, remotely controlled system, can be tucked into the bottom of a packaging box or stuffed in a toy (a device no bigger than the palm of your hand) and delivered right into the hands or desk of an intended victim.”...
Such a device could even set up a rogue wireless network of its own to sniff login credentials to use on the real target network, according to the post. Devices made for the technique, which IBM has dubbed warshipping, can be built for under $100, the company says.
To avoid such attacks, Henderson’s team recommends companies set up policies to inspect and isolate packages and potentially discourage employees from getting personal shipments at work. more
Instead, writes Charles Henderson, global head of that security unit, they could simply ship you a package with a tiny, concealed device they can remotely control.
“In fact, they could ship multiple devices to their target location thanks to low build cost,” Henderson writes. “The device, a 3G-enabled, remotely controlled system, can be tucked into the bottom of a packaging box or stuffed in a toy (a device no bigger than the palm of your hand) and delivered right into the hands or desk of an intended victim.”...
 |
| Scheduled TSCM inspections find electronic surveillance items like this. Dead or alive. |
To avoid such attacks, Henderson’s team recommends companies set up policies to inspect and isolate packages and potentially discourage employees from getting personal shipments at work. more
Tuesday, July 23, 2019
Spycam Report from China
Sales of spy cameras are rampant at Shenzhen’s gadget paradise, Huaqiangbei, according to a report by state broadcaster CCTV. The report, secretly filmed (ironically) by CCTV reporters, found vendors selling secret cameras disguised as pens, lighters and alarm clocks, among a number of other things. This is in spite of the fact that it's illegal in China to sell “espionage equipment” that can be used for secretly monitoring and photographing people.
In one case, the CCTV reporter bought a fake power socket with a camera hidden in one of the holes and double-sided tape on the back to allow for mounting on a wall. It included an SD card socket and a charging port at the bottom...
In another example from the report, one shop demonstrated a different power socket that hides the camera in a small hole in the bottom-right corner. The video can also be watched in real time from a smartphone app.
In recent months, a series of events that show just how easy it is to secretly film people in hotels has unnerved people in China. The apparent prevalence of the practice has raised concerns about people’s privacy and safety...
In another case, a couple found a hidden camera in the TV in their hotel room in the city of Zhengzhou. Police later determined one person had installed hidden cameras in at least five rooms. Then they detained a manager at the hotel when he claimed more than 80% of the hotels in the city have hidden cameras. more
In one case, the CCTV reporter bought a fake power socket with a camera hidden in one of the holes and double-sided tape on the back to allow for mounting on a wall. It included an SD card socket and a charging port at the bottom...
In another example from the report, one shop demonstrated a different power socket that hides the camera in a small hole in the bottom-right corner. The video can also be watched in real time from a smartphone app.
In recent months, a series of events that show just how easy it is to secretly film people in hotels has unnerved people in China. The apparent prevalence of the practice has raised concerns about people’s privacy and safety...
In another case, a couple found a hidden camera in the TV in their hotel room in the city of Zhengzhou. Police later determined one person had installed hidden cameras in at least five rooms. Then they detained a manager at the hotel when he claimed more than 80% of the hotels in the city have hidden cameras. more
Thursday, July 11, 2019
New Report Projects the Size of the World Spycam Market 2019-2025
An extensive analysis of the Global Spy Cameras market strategy of the leading companies in the precision of import/export consumption, supply and demand figures, cost, price, revenue and gross margins.
The report starts by an introduction about the company profiling and a comprehensive review about the strategy concept and the tools that can be used to assess and analyze strategy.
It also analyzes the company’s strategy in the light of Porter’s Value Chain, Porter’s Five Forces, SWOT analysis, and recommendation on Balanced Scorecard for supply chain analysis...
The Spy Cameras market was valued at xx Million US$ in 2018 and is projected to reach xx Million US$ by 2025, at a CAGR of xx% during the forecast period.
In this study, 2018 has been considered as the base year and 2019 to 2025 as the forecast period to estimate the market size for Spy Cameras.
This report presents the worldwide Spy Cameras market size (value, production and consumption), splits the breakdown (data status 2014-2019 and forecast to 2025), by manufacturers, region, type and application. more
If you want to fill in the X's, you'll have to purchase the report ($4,600.).
Takeaway... It must be a monster market if professional forecast reports are covering it. But, we already knew that. ~Kevin
The report starts by an introduction about the company profiling and a comprehensive review about the strategy concept and the tools that can be used to assess and analyze strategy.
It also analyzes the company’s strategy in the light of Porter’s Value Chain, Porter’s Five Forces, SWOT analysis, and recommendation on Balanced Scorecard for supply chain analysis...
The Spy Cameras market was valued at xx Million US$ in 2018 and is projected to reach xx Million US$ by 2025, at a CAGR of xx% during the forecast period.
In this study, 2018 has been considered as the base year and 2019 to 2025 as the forecast period to estimate the market size for Spy Cameras.
This report presents the worldwide Spy Cameras market size (value, production and consumption), splits the breakdown (data status 2014-2019 and forecast to 2025), by manufacturers, region, type and application. more
If you want to fill in the X's, you'll have to purchase the report ($4,600.).
Takeaway... It must be a monster market if professional forecast reports are covering it. But, we already knew that. ~Kevin
Wednesday, June 5, 2019
Corporate Secret Theft Through the Roof
IP theft is on the rise, and the threat landscape is way beyond the old days of targeted corporate espionage.
There are potentially tens of thousands of entities who want a business’s data and can profit from it, one way or another. This undercuts the potential success of its rightful owners and damages the future of the business. The good news, however, is that there are several strategies which can be deployed to protect IP, and these lessons can be applied across the entire business...
The first step of this process is understanding the nature of security threats to IP. Technological development and the interconnected nature of the digital world has made IP theft far easier than ever before, especially given that the majority of security breaches that go undetected. more
There are potentially tens of thousands of entities who want a business’s data and can profit from it, one way or another. This undercuts the potential success of its rightful owners and damages the future of the business. The good news, however, is that there are several strategies which can be deployed to protect IP, and these lessons can be applied across the entire business...
The first step of this process is understanding the nature of security threats to IP. Technological development and the interconnected nature of the digital world has made IP theft far easier than ever before, especially given that the majority of security breaches that go undetected. more
Wednesday, May 22, 2019
Snapple "Real Fact" #726 – Polar Bears v. Infrared Cameras v. TSCM
I had a Snapple tea the other day and found this "Real Fact" #726 under the cap.
We use infrared cameras in our work, and know how they work. This "Real Fact" struck all of us here as odd. An IR camera would not detect a polar bear because its fur was transparent?!?!
Oxymoron? No, just sensationalism. The mixing of two unrelated facts to manufacture an unexpected outcome designed to surprise... aka Fake News.
The real "Real Fact" reason...
Insulation is the "Real Fact"
It's not that the fur is mostly transparent, or that polar bears alone have super-powers. IR invisibility is also true for the Arctic fox and other mammals living in cold environments.
The Technical Surveillance Countermeasures field (TSCM) is also riddled with "Real Facts", like inflated bug-find claims, and pervasive laser beam eavesdropping fearmongering.
It always pays to scratch the surface.
Examine the science.
Apply some common sense.
Visit us for the Real Facts about TSCM. ~Kevin
We use infrared cameras in our work, and know how they work. This "Real Fact" struck all of us here as odd. An IR camera would not detect a polar bear because its fur was transparent?!?!
Oxymoron? No, just sensationalism. The mixing of two unrelated facts to manufacture an unexpected outcome designed to surprise... aka Fake News.
The real "Real Fact" reason...
- Yes, a polar bear's fur is mostly transparent, and hollow too!
- Yes, IR cameras would have a difficult time detecting a polar bear.
Insulation is the "Real Fact"
It's not that the fur is mostly transparent, or that polar bears alone have super-powers. IR invisibility is also true for the Arctic fox and other mammals living in cold environments.
The Technical Surveillance Countermeasures field (TSCM) is also riddled with "Real Facts", like inflated bug-find claims, and pervasive laser beam eavesdropping fearmongering.
It always pays to scratch the surface.
Examine the science.
Apply some common sense.
Visit us for the Real Facts about TSCM. ~Kevin
Monday, May 20, 2019
Spycam Brings Down Austrian Leader - A Cautionary Tale
Austrian Chancellor Sebastian Kurz called Saturday for an early election after his vice chancellor resigned over a covertly shot video that showed him apparently promising government contracts to a prospective Russian investor.
Two German publications, the daily Sueddeutsche Zeitung and the weekly Der Spiegel, published extracts Friday of a covert video purportedly showing Strache during an alcohol-fueled evening on the Spanish resort island of Ibiza offering Austrian government contracts to a Russian woman, purportedly the niece of a Russian oligarch and interested in investing large amounts of money in Austria.
In his resignation statement Saturday, Strache apologized but said he was set up in a “political assassination” that illegally used surveillance equipment. more
Hey Politicos. Better learn how to detect spycams.
Two German publications, the daily Sueddeutsche Zeitung and the weekly Der Spiegel, published extracts Friday of a covert video purportedly showing Strache during an alcohol-fueled evening on the Spanish resort island of Ibiza offering Austrian government contracts to a Russian woman, purportedly the niece of a Russian oligarch and interested in investing large amounts of money in Austria.
In his resignation statement Saturday, Strache apologized but said he was set up in a “political assassination” that illegally used surveillance equipment. more
Hey Politicos. Better learn how to detect spycams.
The ASML Case - Trade Secret Theft - Sometimes the Good Guy Wins
Following a jury verdict rendered months earlier, a California court entered a final judgment for $845 million in favor of semiconductor maker, ASML, in its suit against rival, XTAL, for stealing trade secrets related to ASML’s lithography technology.
This judgment followed a jury award last year, which had included the potential for punitive damages because the jury found XTAL’s conduct to be malicious. The final judgment, which also reimbursed AMSL for costs relating to its investigation of XTAL’s theft...
AMSL will receive most, if not all, of XTAL’s intellectual property under a settlement agreement... more
Congratulations, ASML! ~ Kevin
This judgment followed a jury award last year, which had included the potential for punitive damages because the jury found XTAL’s conduct to be malicious. The final judgment, which also reimbursed AMSL for costs relating to its investigation of XTAL’s theft...
AMSL will receive most, if not all, of XTAL’s intellectual property under a settlement agreement... more
Congratulations, ASML! ~ Kevin
Thursday, May 16, 2019
To Catch a Spy - The Art of Counterintelligence
Longtime Central Intelligence Agency operative and former CIA chief of counterintelligence James “Jim” Olson delivered a talk on his career experiences and challenges Tuesday night to a near-capacity crowd at the Annenberg Presidential Conference Center.
Earlier this year, Olson released a book, To Catch a Spy: The Art of Counterintelligence, which he said is rooted in his three decades in the arena of counterintelligence. It offers “a wake-up call,” in Olson’s words, for the American public about why counterintelligence matters, and why America must protect its trade and national security secrets.
Olson said 50 countries are known to be spying against the U.S. currently. “The worst culprit, by far, is China — followed by Russia, Cuba and Iran,” he said.
“In my 31-year career in the CIA, I saw evil face-to-face more often than I care to remember,” Olson said. “People I knew and trusted — people I considered friends — betrayed us, and their treachery was close to me. It was personal, and indescribably painful. The damage that these traitors did to our country was devastating.” more
Earlier this year, Olson released a book, To Catch a Spy: The Art of Counterintelligence, which he said is rooted in his three decades in the arena of counterintelligence. It offers “a wake-up call,” in Olson’s words, for the American public about why counterintelligence matters, and why America must protect its trade and national security secrets.
Olson said 50 countries are known to be spying against the U.S. currently. “The worst culprit, by far, is China — followed by Russia, Cuba and Iran,” he said.
“In my 31-year career in the CIA, I saw evil face-to-face more often than I care to remember,” Olson said. “People I knew and trusted — people I considered friends — betrayed us, and their treachery was close to me. It was personal, and indescribably painful. The damage that these traitors did to our country was devastating.” more
Cautionary Tale: Why Scheduled Bug Sweeps (TSCM) Protect You
Consider this recent event...
NY - In the annals of jaw-dropping East Hampton political miscalculation, the bugging of the town trustees office is a new low.
As indicated by an edited version now circulating, someone or multiple conspirators were able to make illegal secret recordings of conversations beginning in the early fall or perhaps earlier.
The technology and those responsible have not been discovered, but from the way the recordings and an associated partial transcript were organized there is a sense that it was aimed at particular trustees and not the nine-person board as a whole. more
Regularly scheduled TSCM inspections for electronic eavesdropping devices work. Here's why...
Typical GSM bug. Easily planted. Call it from anywhere to listen in.
NY - In the annals of jaw-dropping East Hampton political miscalculation, the bugging of the town trustees office is a new low.
As indicated by an edited version now circulating, someone or multiple conspirators were able to make illegal secret recordings of conversations beginning in the early fall or perhaps earlier.
The technology and those responsible have not been discovered, but from the way the recordings and an associated partial transcript were organized there is a sense that it was aimed at particular trustees and not the nine-person board as a whole. more
Regularly scheduled TSCM inspections for electronic eavesdropping devices work. Here's why...
- Intelligence collection is a leisurely process.
- The bugging itself is harmless.
- The harm happens after the information is collected, and is then used against you.
Typical GSM bug. Easily planted. Call it from anywhere to listen in.
Friday, May 10, 2019
From Those Wonderful Emperors of Espionage...
A popular GPS tracker used as a panic alarm for elderly people and to monitor children's whereabouts can be hacked to spy on users, researchers have warned.
The white-label location tracker, manufactured in China, is rebranded and sold by multiple UK companies - including Pebbell 2 by HoIP Telecom , OwnFone Footprint , and SureSafeGo.
"There were no signs from the device when this was activated or when you called in, turning this device issued to vulnerable people into a remote listening bug,” said Fidus.
"This issue teamed with the location tracking abilities of the device allows you to conceive some pretty scary potential use cases."
The researchers also found it was possible to remotely reset the GPS tracker without needing a PIN, and kill signal to the device altogether, rendering it effectively useless.
Fidus estimates that there are at least 10,000 of these devices in use in the UK, and thousands more around the world.
The team has informed several of the device makers about the flaws, but there is no way to fix the vulnerabilities without recalling every device. more
The white-label location tracker, manufactured in China, is rebranded and sold by multiple UK companies - including Pebbell 2 by HoIP Telecom , OwnFone Footprint , and SureSafeGo.
"There were no signs from the device when this was activated or when you called in, turning this device issued to vulnerable people into a remote listening bug,” said Fidus.
"This issue teamed with the location tracking abilities of the device allows you to conceive some pretty scary potential use cases."
The researchers also found it was possible to remotely reset the GPS tracker without needing a PIN, and kill signal to the device altogether, rendering it effectively useless.
Fidus estimates that there are at least 10,000 of these devices in use in the UK, and thousands more around the world.
The team has informed several of the device makers about the flaws, but there is no way to fix the vulnerabilities without recalling every device. more
Even Popcorn Has Trade Secrets
Caramel Crisp LLC, the owner of Garrett Popcorn Shops (“Garrett”), the renowned Chicago-based purveyor of deliciously flavored popcorn, recently filed suit in federal court in Chicago against its former director of research and development, Aisha Putnam, alleging that she misappropriated the company’s trade secrets, including its recipes for Garret’s famous popcorn...
 Garrett alleges that when she learned about the termination, Putnam began downloading “virtually all of [Garrett’s] trade secrets and confidential information in her possession to a personal USB drive, which she took home.”...
Garrett alleges that when she learned about the termination, Putnam began downloading “virtually all of [Garrett’s] trade secrets and confidential information in her possession to a personal USB drive, which she took home.”...
This case offers two helpful reminders to employers that seek to protect their valuable trade secrets.
First, in determining whether something qualifies as a “trade secret,” one factor considered by courts are the reasonableness of the efforts to maintain the confidentiality of the trade secrets...
Second, whenever an employee with access to trade secrets leaves their employment (either voluntarily or involuntarily), employers should consider whether to conduct a forensic review of their computers and other storage devices to determine whether the employee took any confidential information on his or her way out the door. more
 Garrett alleges that when she learned about the termination, Putnam began downloading “virtually all of [Garrett’s] trade secrets and confidential information in her possession to a personal USB drive, which she took home.”...
Garrett alleges that when she learned about the termination, Putnam began downloading “virtually all of [Garrett’s] trade secrets and confidential information in her possession to a personal USB drive, which she took home.”...This case offers two helpful reminders to employers that seek to protect their valuable trade secrets.
First, in determining whether something qualifies as a “trade secret,” one factor considered by courts are the reasonableness of the efforts to maintain the confidentiality of the trade secrets...
Second, whenever an employee with access to trade secrets leaves their employment (either voluntarily or involuntarily), employers should consider whether to conduct a forensic review of their computers and other storage devices to determine whether the employee took any confidential information on his or her way out the door. more
Wednesday, April 24, 2019
Speak Like You Are Being Recorded
Michael Cohen has disavowed responsibility for some of the crimes to
which he has pleaded guilty, privately contending in a recent recorded
phone call that he hadn’t evaded taxes and that a criminal charge
related to his home-equity line of credit was "a lie."
“You would think that you would have folks, you know, stepping up and
saying, ‘You know what, this guy’s lost everything,’” Mr. Cohen said
during the March 25 call, recorded without Mr. Cohen’s knowledge by the
actor and comedian Tom Arnold...
Mr. Cohen has himself surreptitiously recorded conversations. During a
raid of his home, office and hotel room in April 2018, the Federal
Bureau of Investigation seized recordings the lawyer made while talking
to journalists, political allies, and others, including Mr. Trump. more
Granny Was A Spy
UK - In 1999, an 87-year-old British woman held a press conference in front of her home to announce that for nearly four decades, she’d worked as a spy for the Soviet Union.
In fact, Melita Norwood was the Soviet Union’s longest-serving British spy...
In 1979, she and her husband—who knew about her spying and disapproved—visited Moscow so the Soviet Union could award her the Order of the Red Banner (she accepted the honorary award, but turned down the financial reward).
How did Norwood get away with it for so long? more
In fact, Melita Norwood was the Soviet Union’s longest-serving British spy...
In 1979, she and her husband—who knew about her spying and disapproved—visited Moscow so the Soviet Union could award her the Order of the Red Banner (she accepted the honorary award, but turned down the financial reward).
How did Norwood get away with it for so long? more
Monday, April 8, 2019
Quote of the Week
“Boston is a target-rich environment for anyone who is interested in intellectual property.”
–US Assistant Attorney General John Demers more
–US Assistant Attorney General John Demers more
Sunday, March 31, 2019
Security Tip: Why it Always Pays to Hire The Best.
 Following the revelation that the The National Enquirer had obtained
intimate texts and images between Amazon CEO Jeff Bezos and Lauren
Sanches, Bezos ordered an investigation into who was behind the data
breach.
Following the revelation that the The National Enquirer had obtained
intimate texts and images between Amazon CEO Jeff Bezos and Lauren
Sanches, Bezos ordered an investigation into who was behind the data
breach. In a post on The Daily Beast, Bezos’ security consultant Gavin De Becker says that his team of investigators have “concluded with high confidence that the Saudis had access to Bezos’ phone...” more
Inside Info Discussed Outside is a Big Deal... killer
Careless talk costs dollars. That’s the lesson from a case heard last week by one of France’s financial regulators.
Lazard Ltd. dealmaker Vincent Le Stradic spent two and a half hours aboard a Eurostar train from London to Paris in 2014 working on a $15 billion takeover bid by Iliad SA for T-Mobile US Inc.
He was oblivious to the fact that the casually dressed man sitting next to him was Alexandre Zaluski, a UBS Group AG banker, who passed the information to a colleague, ultimately resulting in the bank pitching to Iliad to help finance the deal...
It’s an open secret in the media industry that some of the best scoops can be picked up by eavesdropping in lawyers and banker hangouts, from London’s Ye Olde Cheshire Cheese and Michael’s in Midtown Manhattan to Hong Kong’s Captain’s Bar and Mumbai’s Willingdon Sports Club. more
Working on a takeover, merger or acquisition?
Put an information security consultant on your team.
Lazard Ltd. dealmaker Vincent Le Stradic spent two and a half hours aboard a Eurostar train from London to Paris in 2014 working on a $15 billion takeover bid by Iliad SA for T-Mobile US Inc.
He was oblivious to the fact that the casually dressed man sitting next to him was Alexandre Zaluski, a UBS Group AG banker, who passed the information to a colleague, ultimately resulting in the bank pitching to Iliad to help finance the deal...
It’s an open secret in the media industry that some of the best scoops can be picked up by eavesdropping in lawyers and banker hangouts, from London’s Ye Olde Cheshire Cheese and Michael’s in Midtown Manhattan to Hong Kong’s Captain’s Bar and Mumbai’s Willingdon Sports Club. more
Working on a takeover, merger or acquisition?
Put an information security consultant on your team.
Thursday, January 31, 2019
Business Espionage – A Cunning Protection Plan to Protect us and U.S.
We are bombarded with news stories and court trials tornado-ing around Chinese spies. They’re everywhere. Collecting everything. They are such a fixture in and around our hapless businesses that it only seems right to offer them health insurance, a pension plan, cookies and milk.
But wait. Let’s think this through.
Aren’t these the folks who had the secrets of silk stolen from them by Justinian I? Humm, could this be why great neckties are made in Italy, not China? Even their espionage death penalty law couldn’t protect them. Boom! Business espionage devastated their economy.
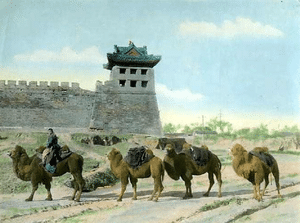
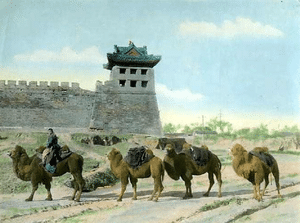 I also recall a dude from the UK, Robert Fortune, sort of an early 007. He was sent to steal the secrets of tea production from… Have you guessed yet? China! That caper is now know as The Great British Tea Heist. Boom! Business espionage devastated their economy yet again.
I also recall a dude from the UK, Robert Fortune, sort of an early 007. He was sent to steal the secrets of tea production from… Have you guessed yet? China! That caper is now know as The Great British Tea Heist. Boom! Business espionage devastated their economy yet again.
Oh, and what about the Chinese secret of making porcelain? A French Catholic priest stole that one. BOOM!! I could go on and on. Gunpowder, paper, etc. Bing! Bam! BOOM!
Feeling sorry for China yet? Don’t. They are making up for it, right now. The disk drive that just started whirring in your computer… it might be them.
And, don’t think this is just some cosmic Yin and Yang, great mandella, or as we say here in New Jersey, “What goes around, comes around.” No, that explanation is too simplistic, not to mention fatalistic. There is more to this industrial espionage business. The circle is bigger. This is history repeating itself, over and over and over, but I think I have the solution... more
But wait. Let’s think this through.
Aren’t these the folks who had the secrets of silk stolen from them by Justinian I? Humm, could this be why great neckties are made in Italy, not China? Even their espionage death penalty law couldn’t protect them. Boom! Business espionage devastated their economy.
 I also recall a dude from the UK, Robert Fortune, sort of an early 007. He was sent to steal the secrets of tea production from… Have you guessed yet? China! That caper is now know as The Great British Tea Heist. Boom! Business espionage devastated their economy yet again.
I also recall a dude from the UK, Robert Fortune, sort of an early 007. He was sent to steal the secrets of tea production from… Have you guessed yet? China! That caper is now know as The Great British Tea Heist. Boom! Business espionage devastated their economy yet again.Oh, and what about the Chinese secret of making porcelain? A French Catholic priest stole that one. BOOM!! I could go on and on. Gunpowder, paper, etc. Bing! Bam! BOOM!
Feeling sorry for China yet? Don’t. They are making up for it, right now. The disk drive that just started whirring in your computer… it might be them.
And, don’t think this is just some cosmic Yin and Yang, great mandella, or as we say here in New Jersey, “What goes around, comes around.” No, that explanation is too simplistic, not to mention fatalistic. There is more to this industrial espionage business. The circle is bigger. This is history repeating itself, over and over and over, but I think I have the solution... more
Subscribe to:
Posts (Atom)














