Wi-Charge uses safe infrared light to deliver power from a distance. Our products provide enough power to charge a phone across a room, to power smart devices and enable new experiences. With Wi-Charge, mobile and IoT devices appear to charge autonomously. New applications open for homes, offices, factories and public spaces.
Battery-powered devices are portable, but battery capacity limits functionality and the need to replace batteries degrades the user experience. Moving wired devices, routing or hiding the power cords is a pain. Wi-Charge delivers 100x the power budget of battery solutions. With Wi-Charge, you can have the convenience of wire-free portability with a power budget approaching to a wired solution. more
Lots of good uses, and possibly some evil ones.
Thanks to another Canadian Blue Blaze Irregular for spotting this one!
Monday, February 25, 2019
Electronic Footprint Army Boots Discovered
 Hamas-run security forces at the Kerem Shalom crossing in the Gaza Strip have seized a shipment of army boots outfitted with tracking devices, Turkey’s state-run news agency Anadolu reported on Saturday, citing a security source in the coastal enclave.
Hamas-run security forces at the Kerem Shalom crossing in the Gaza Strip have seized a shipment of army boots outfitted with tracking devices, Turkey’s state-run news agency Anadolu reported on Saturday, citing a security source in the coastal enclave.Hamas security forces were carrying out “a precise inspection of the tracking devices in order to… understand how they work,” the security source said. more
Looks like the same technology as shoplifting tags and card-keys. Clever.
Thanks to our Canadian Blue Blaze irregular for spotting this one!
Friday, February 8, 2019
Book - JUDGEMENT by Joe Finder - Fast-Paced Thriller with Technical Surveillance Overtones
 |
| Just Released |
Excerpt...
"It was nothing more than a one-night stand. Juliana Brody, a judge in the Superior Court of Massachusetts, is rumored to be in consideration for the federal circuit, maybe someday the highest court in the land.
At a conference in a Chicago hotel, she meets a gentle, vulnerable man and has an unforgettable night with him—something she’d never done before. They part with an explicit understanding that this must never happen again.
But back home in Boston, Juliana realizes that this was no random encounter. The man from Chicago proves to have an integral role in a case she's presiding over—a sex-discrimination case that's received national attention. Juliana discovers that she's been entrapped, her night of infidelity captured on video.
 Strings are being pulled in high places, a terrifying unfolding conspiracy that will turn her life upside down. But soon it becomes clear that personal humiliation, even the possible destruction of her career, are the least of her concerns, as her own life and the lives of her family are put in mortal jeopardy.
Strings are being pulled in high places, a terrifying unfolding conspiracy that will turn her life upside down. But soon it becomes clear that personal humiliation, even the possible destruction of her career, are the least of her concerns, as her own life and the lives of her family are put in mortal jeopardy. In the end, turning the tables on her adversaries will require her to be as ruthless as they are..."
Inside Information: Several Technical Surveillance Countermeasures practitioners (including myself) were consulted for plot twists and technical realism. New York Times bestselling author Joseph Finder does this kind of homework on all his novels. ~Kevin
more
Thursday, February 7, 2019
Ultrasonic Microphone Jammers — Do They Really Work?
It’s a question I get asked occasionally when one of our clients sees one of these devices being advertised on the internet.
 Who can blame them for asking? The ads claim they can stop microphones from working properly. Instant privacy from electronic eavesdroppers, and anyone who is attempting to record your conversations.
Who can blame them for asking? The ads claim they can stop microphones from working properly. Instant privacy from electronic eavesdroppers, and anyone who is attempting to record your conversations.
Finally, Kryptonite for microphones!?!? Wow, how does that work?
The ultrasonic microphone jammer explanation is really simple... more
 Who can blame them for asking? The ads claim they can stop microphones from working properly. Instant privacy from electronic eavesdroppers, and anyone who is attempting to record your conversations.
Who can blame them for asking? The ads claim they can stop microphones from working properly. Instant privacy from electronic eavesdroppers, and anyone who is attempting to record your conversations.Finally, Kryptonite for microphones!?!? Wow, how does that work?
The ultrasonic microphone jammer explanation is really simple... more
FutureWatch: Smartphone Comes with Optical Spy Pen
 |
| Click to enlarge. |
Abstract
The electric pen device includes an optical system including a lens and an image sensor configured to convert an image signal of light that has passed through the optical system to an electrical signal. The electric pen device includes a control board configured to interact with an electronic device and a communication module configured to communicate by wire or wirelessly with the electronic device, so that an image or a picture taken by a camera is confirmed and an optical zoom is controlled from the external electronic device. more
FutureWatch spy implications: Phone may be concealed in the pocket, backpack, or nearby desk drawer. Take high quality photos by aiming the top of the pen, pressing a button, and automatically transmitting the photo back to the phone. Pretty covert. No word about it transmitting audio, yet. Leaving phones outside of the conference room won't be enough. You'll have to check the pens, too.
Need a spy pen camera you can actually buy today, or worry about being used to steal your secrets? Check here. ~Kevin
Thanks to our sharp-eyed Blue Blaze Irregular in the shadows of Pennsylvania for this.
Smart Light Bulbs May Not Be a Bright Idea
Your discarded smart lightbulbs reveal your wifi passwords, because they are stored in the clear.
Not to mention, someone replacing your bulb and getting the password that way.
Yes, I know, the spy might not program the replacement bulb to operate like the old one. Dead give-a-way, right? My bet is that you'll think the bulb just forgot it's settings, or not notice at all.
This hack was publicized here, and originally researched here, if you want to know more.
Thanks to our Blue Blaze Irregular from the Jersey shore for this one.
Not to mention, someone replacing your bulb and getting the password that way.
Yes, I know, the spy might not program the replacement bulb to operate like the old one. Dead give-a-way, right? My bet is that you'll think the bulb just forgot it's settings, or not notice at all.
This hack was publicized here, and originally researched here, if you want to know more.
Thanks to our Blue Blaze Irregular from the Jersey shore for this one.
Wednesday, February 6, 2019
Business Espionage: The Case of the Broken Unbreakable Glass
In what sounds like a half-baked movie script about corporate espionage,
an FBI sting conducted in collaboration with a specialized glass maker
(and watched from a gelato stand by a reporter from Bloomberg) led investigators to a meeting at a burger joint in Vegas during CES... Akhan Semiconductor, reached out to potential customers regarding its
recently developed Miraj Diamond Glass, a new take on the protective
screens used in devices like smartphones that Akhan claims is six times
stronger and ten times more scratch-resistant than Corning Gorilla
Glass. Among Akhan’s potential clients was Huawei... more more sing-a-long
This Week in Technical Surveillance
Ukraine - Head of the election headquarters of the presidential candidate of Ukraine, leader of the Civil Position Party Anatoliy Hrytsenko, independent deputy, Viktor Chumak, has said that wiretapping devices were found in their headquarters, and therefore, called on other candidates to be vigilant. more
Australia - Australia is to establish a new sweeping anti-corruption regime which
will be overseen by a national watchdog which will tackle both cheating
and match-fixing in the Australian sports sector... It would also have the power to conduct electronic surveillance
of coaches, sports officials, and athletes and look for signs of suspected
match-fixing... more
...and one for the birds...
Israel - The Israel Police admitted on Tuesday that it
eavesdropped on journalists’ telephone conversations with suspects,
despite these conversations being protected by journalistic privilege. more
U.S. - A head custodian for the city's public school
district was arrested after a female co-worker found a hidden camera
that had recorded her using a restroom... Francisco
Javier Lopez-Martinez, 59, was arrested...after an overnight police search... Lopez-Martinez was found hiding...police said he threatened suicide while holding a
handgun...the gun was determined to be an
air-soft weapon... A
day earlier, a woman reported to police that she had discovered the
camera while using a bathroom...she found footage of her and also a clip of,
Lopez-Martinez, installing the camera. more
...and one for the birds...
New Zealand - In a technology that's been heralded as a breakthrough in conservation, a
remote recording device is 'eavesdropping' on one of the rarest birds
in New Zealand to monitor how they're adjusting after being released
back into the wild. more
Facilities Manager Alert: Your Smart Building May Start Doing Dumb Things
Researchers at enterprise security vendor ForeScout have warned that malware specifically targeting smart buildings is an inevitable next step given the rapidly expanding attack surface that building automation systems expose.
The operational technology researchers at ForeScout should know: they created proof-of-concept malware that revealed smart building vulnerabilities every business should be concerned about.
...just yesterday, Tenable Research revealed it had discovered several zero-day vulnerabilities in a premises access control system used by Fortune 500 companies. Among the many attack scenarios these vulnerabilities could facilitate was 'unfettered access to the badge system database' which in turn meant an ability to create fraudulent access badges and disable building locks. more
The operational technology researchers at ForeScout should know: they created proof-of-concept malware that revealed smart building vulnerabilities every business should be concerned about.
...just yesterday, Tenable Research revealed it had discovered several zero-day vulnerabilities in a premises access control system used by Fortune 500 companies. Among the many attack scenarios these vulnerabilities could facilitate was 'unfettered access to the badge system database' which in turn meant an ability to create fraudulent access badges and disable building locks. more
Spybusters Tip #847: Stop Car Theft via Key Fob Signal Intercept
By simply wrapping your key FOB in aluminum foil you can prevent a thief
from intercepting the signal.
If you park your car outside at home then you might consider using a foil-lined container or placing your keys in a coffee can.
I’m going to start wrapping mine in aluminum foil when I travel and stay in a hotel. If you doubt that this issue is a serious threat then watch How Thieves Unlock A Car. more
A big thank you to our Blue Blaze Irregular ensconced in Illinois for alerting us to this tip. ~Kevin
If you park your car outside at home then you might consider using a foil-lined container or placing your keys in a coffee can.
I’m going to start wrapping mine in aluminum foil when I travel and stay in a hotel. If you doubt that this issue is a serious threat then watch How Thieves Unlock A Car. more
A big thank you to our Blue Blaze Irregular ensconced in Illinois for alerting us to this tip. ~Kevin
Sunday, February 3, 2019
Hackers Now Banking on Two-Factor Authentication for Profit
Sophisticated hackers have long exploited flaws in SS7, a protocol used by telecom companies to coordinate how they route texts and calls around the world. Those who exploit SS7 can potentially track phones across the other side of the planet, and intercept text messages and phone calls without hacking the phone itself.
This activity was typically only within reach of intelligence agencies or surveillance contractors, but now Motherboard has confirmed that this capability is much more widely available in the hands of financially-driven cybercriminal groups, who are using it to empty bank accounts. So-called SS7 attacks against banks are, although still relatively rare, much more prevalent than previously reported. Motherboard has identified a specific bank—the UK's Metro Bank—that fell victim to such an attack...
One source familiar with SS7 attacks across banks said the exploitation has targeted banks globally, but that American banks seem to be less impacted. more
Reader comment: "Please note the Motherboard reporter carefully differentiates between "sophisticated hackers" and "financially-driven cybercriminal groups". I hope you'll consider being equally judicious in your own reporting and online comments."
This activity was typically only within reach of intelligence agencies or surveillance contractors, but now Motherboard has confirmed that this capability is much more widely available in the hands of financially-driven cybercriminal groups, who are using it to empty bank accounts. So-called SS7 attacks against banks are, although still relatively rare, much more prevalent than previously reported. Motherboard has identified a specific bank—the UK's Metro Bank—that fell victim to such an attack...
One source familiar with SS7 attacks across banks said the exploitation has targeted banks globally, but that American banks seem to be less impacted. more
Reader comment: "Please note the Motherboard reporter carefully differentiates between "sophisticated hackers" and "financially-driven cybercriminal groups". I hope you'll consider being equally judicious in your own reporting and online comments."
Friday, February 1, 2019
Book Review Request: Technical Surveillance Counter-Measures a Complete Guide
If any TSCM'er out there buys this book. Please send me a review.
Thank you, Kevin
Evil Child Watch Spies
In late 2017, the Norwegian Consumer Council published its audit of kids' smart-watches, reporting that the leading brands allowed strangers to follow your kids around and listen in on their conversations; a year later, Pen Test Partners followed up to see if anything had changed (it hadn't).
Now, a year and a half later, Pen Test Partners have done another security audit of kids' smart watches and you'll never guess what they found! Kids' smart-watches are still a dumpster-fire: anyone can access the entire database of kids' data, including "real time child location, name, parents details etc," and since most leading brands use the same back-end from Gator, virtually every kid's smart-watch is vulnerable. more
Smartphone Security Tips
2/4/19 UPDATE: European Commission orders mass recall of creepy, leaky child-tracking smartwatch. more
Now, a year and a half later, Pen Test Partners have done another security audit of kids' smart watches and you'll never guess what they found! Kids' smart-watches are still a dumpster-fire: anyone can access the entire database of kids' data, including "real time child location, name, parents details etc," and since most leading brands use the same back-end from Gator, virtually every kid's smart-watch is vulnerable. more
Smartphone Security Tips
2/4/19 UPDATE: European Commission orders mass recall of creepy, leaky child-tracking smartwatch. more
Thursday, January 31, 2019
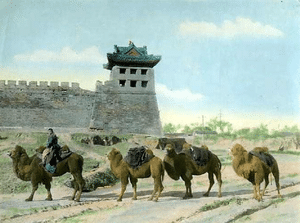
Business Espionage – A Cunning Protection Plan to Protect us and U.S.
We are bombarded with news stories and court trials tornado-ing around Chinese spies. They’re everywhere. Collecting everything. They are such a fixture in and around our hapless businesses that it only seems right to offer them health insurance, a pension plan, cookies and milk.
But wait. Let’s think this through.
Aren’t these the folks who had the secrets of silk stolen from them by Justinian I? Humm, could this be why great neckties are made in Italy, not China? Even their espionage death penalty law couldn’t protect them. Boom! Business espionage devastated their economy.
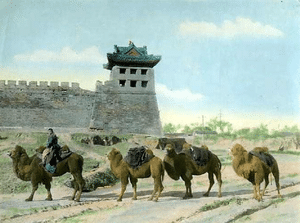 I also recall a dude from the UK, Robert Fortune, sort of an early 007. He was sent to steal the secrets of tea production from… Have you guessed yet? China! That caper is now know as The Great British Tea Heist. Boom! Business espionage devastated their economy yet again.
I also recall a dude from the UK, Robert Fortune, sort of an early 007. He was sent to steal the secrets of tea production from… Have you guessed yet? China! That caper is now know as The Great British Tea Heist. Boom! Business espionage devastated their economy yet again.
Oh, and what about the Chinese secret of making porcelain? A French Catholic priest stole that one. BOOM!! I could go on and on. Gunpowder, paper, etc. Bing! Bam! BOOM!
Feeling sorry for China yet? Don’t. They are making up for it, right now. The disk drive that just started whirring in your computer… it might be them.
And, don’t think this is just some cosmic Yin and Yang, great mandella, or as we say here in New Jersey, “What goes around, comes around.” No, that explanation is too simplistic, not to mention fatalistic. There is more to this industrial espionage business. The circle is bigger. This is history repeating itself, over and over and over, but I think I have the solution... more
But wait. Let’s think this through.
Aren’t these the folks who had the secrets of silk stolen from them by Justinian I? Humm, could this be why great neckties are made in Italy, not China? Even their espionage death penalty law couldn’t protect them. Boom! Business espionage devastated their economy.
 I also recall a dude from the UK, Robert Fortune, sort of an early 007. He was sent to steal the secrets of tea production from… Have you guessed yet? China! That caper is now know as The Great British Tea Heist. Boom! Business espionage devastated their economy yet again.
I also recall a dude from the UK, Robert Fortune, sort of an early 007. He was sent to steal the secrets of tea production from… Have you guessed yet? China! That caper is now know as The Great British Tea Heist. Boom! Business espionage devastated their economy yet again.Oh, and what about the Chinese secret of making porcelain? A French Catholic priest stole that one. BOOM!! I could go on and on. Gunpowder, paper, etc. Bing! Bam! BOOM!
Feeling sorry for China yet? Don’t. They are making up for it, right now. The disk drive that just started whirring in your computer… it might be them.
And, don’t think this is just some cosmic Yin and Yang, great mandella, or as we say here in New Jersey, “What goes around, comes around.” No, that explanation is too simplistic, not to mention fatalistic. There is more to this industrial espionage business. The circle is bigger. This is history repeating itself, over and over and over, but I think I have the solution... more
Second Apple Pickin' Spy Caught in Last 6 Months
The United States FBI this week accused a Chinese citizen working for
Apple of attempting to steal trade secrets that are related to the
company's autonomous vehicle program, reports NBC Bay Area.
 Apple launched an investigation into the employee, Jizhong Chen, when
another employee spotted him taking photographs "in a sensitive work
space."
Apple launched an investigation into the employee, Jizhong Chen, when
another employee spotted him taking photographs "in a sensitive work
space."
Apple Global Security employees searched his personal computer and found "thousands" of Apple files, including manuals, schematics, photographs, and diagrams.
Chen had recently applied for a position with a China-based autonomous vehicle company that is a direct Apple competitor. Chen was arrested a day before he was set to fly to China.
 Apple launched an investigation into the employee, Jizhong Chen, when
another employee spotted him taking photographs "in a sensitive work
space."
Apple launched an investigation into the employee, Jizhong Chen, when
another employee spotted him taking photographs "in a sensitive work
space." Apple Global Security employees searched his personal computer and found "thousands" of Apple files, including manuals, schematics, photographs, and diagrams.
Chen had recently applied for a position with a China-based autonomous vehicle company that is a direct Apple competitor. Chen was arrested a day before he was set to fly to China.
Apple in a statement said that it
is working with the authorities."Apple takes
confidentiality and the protection of our IP very seriously," the
company said in a statement Tuesday. "We are working with authorities on
this matter and are referring all questions to the FBI."
This is not the first time an employee has been caught trying to steal secrets from Apple's car team. Back in July, the FBI charged former Apple employee Xiaolang Zhang with theft of trade secrets for stealing hardware and software that included prototypes and detailed prototype requirements. more
This is not the first time an employee has been caught trying to steal secrets from Apple's car team. Back in July, the FBI charged former Apple employee Xiaolang Zhang with theft of trade secrets for stealing hardware and software that included prototypes and detailed prototype requirements. more
Subscribe to:
Posts (Atom)






