I received a question today about inductive coupling; gleaning computer data leaked on to power lines (aka, mains) from keyboards, screens, etc. The person mentioned this was possible if the residences shared the same power transformer.
"So, does the increase in work-from-home offices these days increase the business espionage threat?"
Interesting question. Got me thinking.
I replied...
You're correct about sharing a transformer. Information can be induced onto the mains and intercepted on that side of the circuit. Several floors in an apartment building and usually 3-4 homes in a residential neighborhood can share one transformer.
But, let's think this through...
Back before we all became computerized the mains lines were relatively noise-free. Carrier-current bugs and wireless intercoms worked quite well for transmitting audio. These days, the noise level is a digital cacophony, created by everyone who shares the circuit.
The very low signal level a keyboard might contribute would be difficult to hear. Segregating the signal from other digital noise would also be a challenge. With diligence and the right instrumentation deciphering this digital
data is doable. It would not be a nosy neighbor doing this. If you got that far, you're probably a government and the home worker has a bigger than average problem.
Realistically speaking...
A fairly static group of mains users also reduces risk. Your neighbors aren't deep cover spies who have waited years for the chance you might be forced to work from home. Moving into a neighborhood or apartment building with spying intentions is possible, but not easy to do on a moments notice. There are easier ways to obtain even
more information, with a lot
less work, and greater chance of success.
Worry about these things...
The weak links in a home office are: the computer, wireless keyboards, Wi-Fi, and internet modems. Current versions of wireless keyboards use Bluetooth (30 foot range) with some pretty good security features. As for date leaking onto the mains... Most smart people use a
UPS battery backup with filtering for their computers, so no problem there. For anyone without a UPS getting one is a very worthwhile recommendation for multiple reasons.
Threats the average home office faces...
- shared cable internet,
- Wi-Fi signal hacking,
- spyware viruses (data, audio and video compromise),
- Wi-Fi connected printer intercepts,
- information phishing scams,
- and none of the usual enterprise type protections.
Attacks can be instituted by
anybody, some staged from
anywhere. Being on one side of a transformer isn't necessary. No need to tap the mains.
Imagine this...
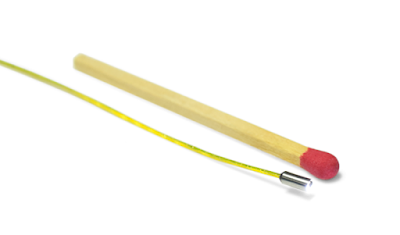
- Step #1: The spy purchases a USB Rubber Ducky (to crack into the computer) and an o.mg cable (to crack into the smartphone). Total cost: <$200.00.
- Step #2: Spy plops these into an old Amazon box and mails it to "the mark."
- Step #3: Mark goes, "Wow, cool. I didn't order this. Amazon must have screwed up. Not worth sending back. I'll keep it."
- Step #4: Mark plugs this windfall into his computer and phone.
- Step #5: Gotcha!
Think this isn't already happening? Think again. The USB Rubber Ducky is now on backorder.
Your company needs to have a
technical security consultant on retainer—because there is more to know.