|
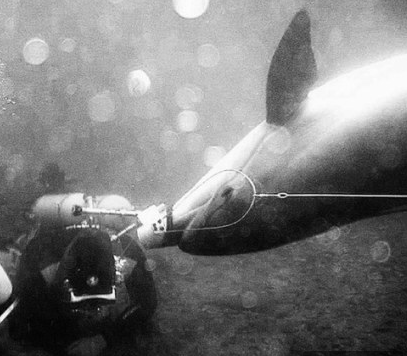
| Click CuteKitty.jpg to enlarge. |
Although this photo does NOT contain a virus, others might.
Many Windows computers will display emailed CuteKitty.jpg.exe – an executable program – as CuteKitty.jpg – which seems harmless.
When you click, you might be shown a cute kitty... while a virus is loading in the background.
Tip 1 - Don't click on stuff if you don't know where it has been.
Tip 2 - If you want to click anyway, open Windows search; enter "folder options"; select Folder Options; View tab, uncheck "Hide extensions for known file types." Check for the double extension trick.