French prosecutors are recommending that Ikea France and 15 people, including police officials, be put on trial on charges of spying on employees and customers.
Three former senior Ikea executives including two ex-chief executive officers (CEOs) are among those charged after an investigation that dates back to 2012. more
Saturday, January 13, 2018
Creepy Peeper Spied 1000+ Computer Mics and Cameras... for 13+ years!
The technical description of the “Fruitfly” malware is “spyware.” But given the way it has allegedly been used, a better label would be creepware...
 According to a 16-count indictment unsealed on Wednesday in US District Court for the Northern District of Ohio, its creator, Phillip R. Durachinsky, 28, used it to spy on thousands of victims for more than 13 years. Durachinsky spent this time not only collecting personal data but also watching and listening to victims through their webcams and microphones, and using some of what he collected to produce child abuse imagery...
According to a 16-count indictment unsealed on Wednesday in US District Court for the Northern District of Ohio, its creator, Phillip R. Durachinsky, 28, used it to spy on thousands of victims for more than 13 years. Durachinsky spent this time not only collecting personal data but also watching and listening to victims through their webcams and microphones, and using some of what he collected to produce child abuse imagery...
The victims ranged from individuals to companies, schools, a police department and government entities including one owned by a subsidiary of the US Department of Energy.
According to the DoJ:
 According to a 16-count indictment unsealed on Wednesday in US District Court for the Northern District of Ohio, its creator, Phillip R. Durachinsky, 28, used it to spy on thousands of victims for more than 13 years. Durachinsky spent this time not only collecting personal data but also watching and listening to victims through their webcams and microphones, and using some of what he collected to produce child abuse imagery...
According to a 16-count indictment unsealed on Wednesday in US District Court for the Northern District of Ohio, its creator, Phillip R. Durachinsky, 28, used it to spy on thousands of victims for more than 13 years. Durachinsky spent this time not only collecting personal data but also watching and listening to victims through their webcams and microphones, and using some of what he collected to produce child abuse imagery...The victims ranged from individuals to companies, schools, a police department and government entities including one owned by a subsidiary of the US Department of Energy.
According to the DoJ:
(It) enabled him to control each computer by accessing stored data, uploading files, taking and downloading screenshots, logging a user’s keystrokes, and turning on the camera and microphone to surreptitiously record images and audio.It said he saved millions of images, kept detailed notes on what he observed, and designed it to alert him if a user typed words associated with pornography. more
(He) used the malware to steal the personal data of victims, including their logon credentials, tax records, medical records, photographs, banking records, internet searches, and potentially embarrassing communications.
Spycam Found in Mall Family Restroom
MD - Authorities say a man set up a spy camera that recorded both children and adults in the family restroom of a Baltimore-area mall.
The Baltimore Sun reports a patron at White Marsh Mall found the camera Dec. 23, and the incident was made public Thursday, when Baltimore County police released footage of the suspect. The camera was found at a restroom located near the food court. more
Like most spycamers, this guy gets our Darwin Award... for taking a video of himself while installing the camera.
Do you offer restrooms to employees, visitors and the public. A spycam incident will put you at risk of being sued. Proactive due diligence is your best defense. Click here for the complete solution.
The Baltimore Sun reports a patron at White Marsh Mall found the camera Dec. 23, and the incident was made public Thursday, when Baltimore County police released footage of the suspect. The camera was found at a restroom located near the food court. more
Like most spycamers, this guy gets our Darwin Award... for taking a video of himself while installing the camera.
Do you offer restrooms to employees, visitors and the public. A spycam incident will put you at risk of being sued. Proactive due diligence is your best defense. Click here for the complete solution.
Friday, January 12, 2018
Top Ten Unusual TSA Finds of 2017 & 2016
Imagine what went on before the days of airport security checks...
Thursday, January 11, 2018
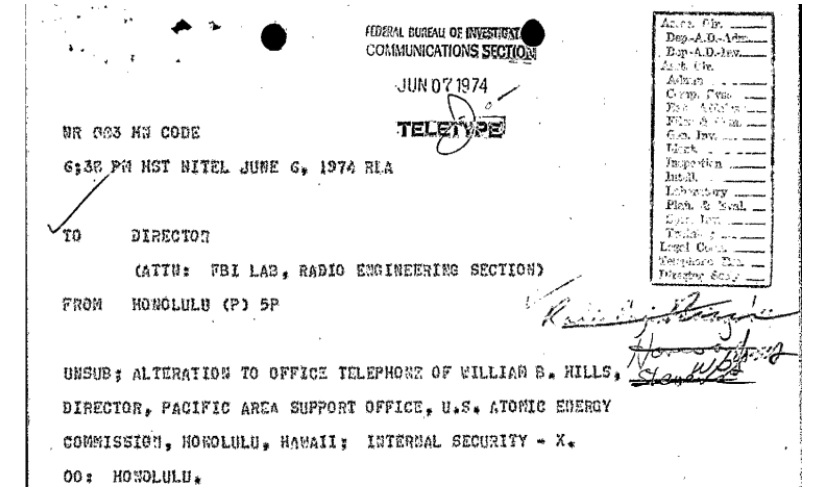
TSCM History: Wiretapped Phone Found at Nuclear Regulatory Commission’s Predecessor
According to the FBI file, a few months before it was abolished, a bug was discovered in the Honolulu offices of the Atomic Energy Commission. The device would not only let someone listen in on phone calls, but any conversations held around the phone - even when it wasn’t in use.
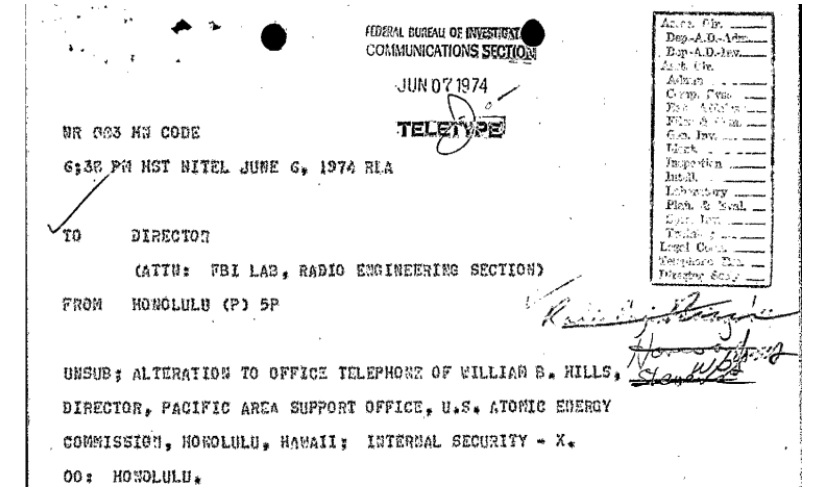
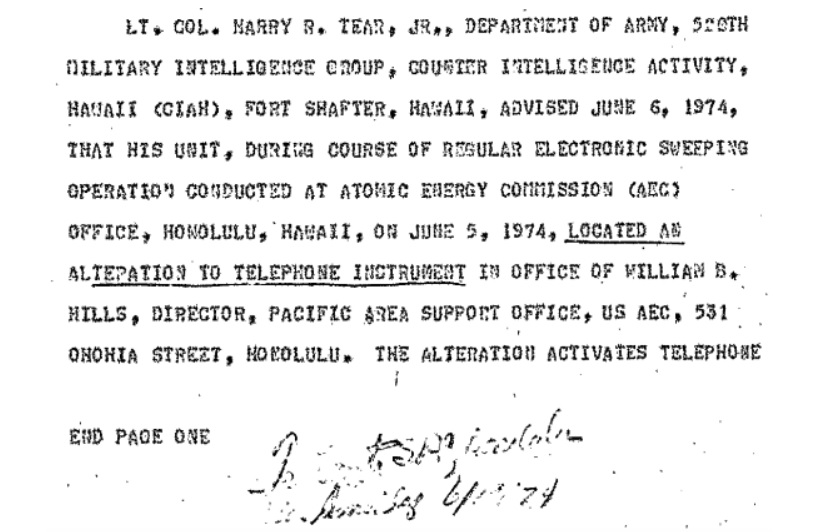
According to the file, the bug was discovered by one Lt. Colonel Harry Tear Jr., assigned to Army counterintelligence at Fort Shafter. While performing a regular electronics sweep in June of 1974, Tear discovered a modification to the phone of Williams Hills, who was the Director for the Atomic Energy Commission’s Pacific Area Support Office, reporting to the Nevada Operations Office.
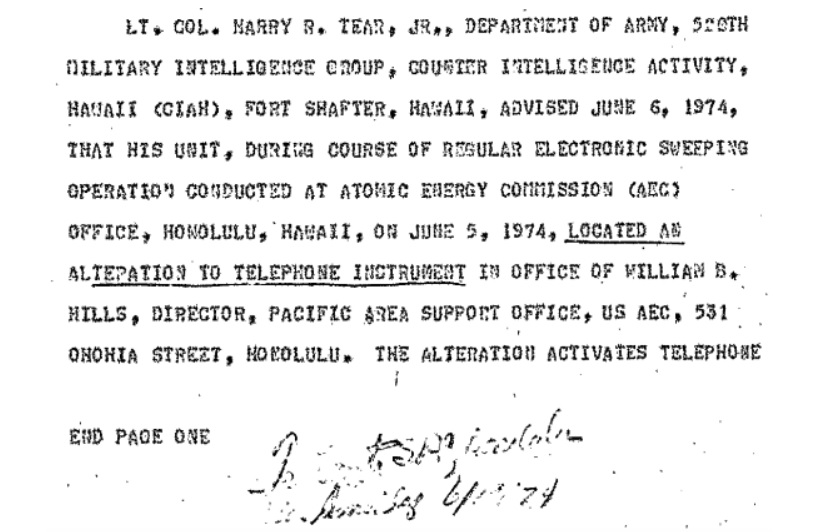
When it was discovered, the phone wasn’t being used to monitor the room. The file notes, however, that it easily could be. When connected, the phone wouldn’t just transmit the conversation being held, but every conversation in the room that happened to be in range of the phone’s receiver. They were unable to determine when it had been installed or how often it had been used, but noted that the wiring appeared to have been done professionally. They were also able to confirm that the device could pick up conversation in the room in practice, not just in theory...
And now for some good advice if you find an electronic surveillance device...
...Simply knowing what information has gotten out does little good without an idea of who will have it, and it’s next to impossible to judge how information will be used without knowing who has it. This is one of the primary reasons for law enforcement to leave a bug in place. While counterintelligence officers would also be interested in the same information, a clever officer or group of officers would use the bug as a way of feeding the listener specific information and misinformation in order to manipulate them in various ways. more
According to the file, the bug was discovered by one Lt. Colonel Harry Tear Jr., assigned to Army counterintelligence at Fort Shafter. While performing a regular electronics sweep in June of 1974, Tear discovered a modification to the phone of Williams Hills, who was the Director for the Atomic Energy Commission’s Pacific Area Support Office, reporting to the Nevada Operations Office.
When it was discovered, the phone wasn’t being used to monitor the room. The file notes, however, that it easily could be. When connected, the phone wouldn’t just transmit the conversation being held, but every conversation in the room that happened to be in range of the phone’s receiver. They were unable to determine when it had been installed or how often it had been used, but noted that the wiring appeared to have been done professionally. They were also able to confirm that the device could pick up conversation in the room in practice, not just in theory...
And now for some good advice if you find an electronic surveillance device...
...Simply knowing what information has gotten out does little good without an idea of who will have it, and it’s next to impossible to judge how information will be used without knowing who has it. This is one of the primary reasons for law enforcement to leave a bug in place. While counterintelligence officers would also be interested in the same information, a clever officer or group of officers would use the bug as a way of feeding the listener specific information and misinformation in order to manipulate them in various ways. more
Wednesday, January 10, 2018
Krebs Arraigned for Wiretapping (Joshua, not our esteemed Brian.)
 |
| What a teacher's lounge should look like. |
Court papers allege Krebs electronically eavesdropped on conversations in the elementary school faculty break room in April 2016...
On April 5, 2016, it is alleged that Krebs, with the assistance of Pleasant Valley School District Technology Supervisor Alex Sterenchock planted a video and audio recording device in the teacher’s lounge, in order, Krebs later said, to catch a custodial staff member in dereliction of their duties.
The device, was discovered a day later, positioned to capture audio and video in the seating area of the lounge. more
Tuesday, January 9, 2018
The Case of the Spying Judge, or Your Honor's Poor Judgement
Two state judges have sued the New Mexico Judicial Standards Commission, demanding secret surveillance recordings they say were made by another judge who was spying on them.
 Plaintiffs Trudy Reed-Chase and Barry Sharer are magistrate court judges in Aztec, New Mexico, the seat of San Juan County. Aztec, a town of about 6,000 is in a remote area of northeastern New Mexico. The nearest large town is Farmington.
Plaintiffs Trudy Reed-Chase and Barry Sharer are magistrate court judges in Aztec, New Mexico, the seat of San Juan County. Aztec, a town of about 6,000 is in a remote area of northeastern New Mexico. The nearest large town is Farmington.
Reed-Chase, Sharer and nine other court employees sued Magistrate Court Judge Connie Lee Johnston, her husband and sister-in-law and the state in February 2016, claiming that Johnston had planted listening devices around the Aztec Municipal Courthouse, including in the offices of Reed-Chase and Sharer. They claimed that electronic surveillance equipment also was placed in the court manager’s office and other workspaces, in inmate holding facilities and in at least one bathroom. more
 Plaintiffs Trudy Reed-Chase and Barry Sharer are magistrate court judges in Aztec, New Mexico, the seat of San Juan County. Aztec, a town of about 6,000 is in a remote area of northeastern New Mexico. The nearest large town is Farmington.
Plaintiffs Trudy Reed-Chase and Barry Sharer are magistrate court judges in Aztec, New Mexico, the seat of San Juan County. Aztec, a town of about 6,000 is in a remote area of northeastern New Mexico. The nearest large town is Farmington. Reed-Chase, Sharer and nine other court employees sued Magistrate Court Judge Connie Lee Johnston, her husband and sister-in-law and the state in February 2016, claiming that Johnston had planted listening devices around the Aztec Municipal Courthouse, including in the offices of Reed-Chase and Sharer. They claimed that electronic surveillance equipment also was placed in the court manager’s office and other workspaces, in inmate holding facilities and in at least one bathroom. more
One Million License Plates Misread by Spy Cameras in UK... every day!
 UK - A network of ‘Big Brother’ spy cameras is misreading 1.2million number plates a day – meaning innocent motorists could be caught up in police investigations while criminals and terrorists escape scot-free.
UK - A network of ‘Big Brother’ spy cameras is misreading 1.2million number plates a day – meaning innocent motorists could be caught up in police investigations while criminals and terrorists escape scot-free.A bombshell report by Britain’s surveillance tsar has warned of problems with Automatic Number Plate Recognition (ANPR) technology, which senior officers insist is invaluable in preventing and solving serious crimes
Around 9,000 cameras across the country take photos of up to 40million number plates each day. more
Unresolved Bugging of Employees Haunts Accused CEO
The newly-appointed acting CEO of the Passenger Rail Association of
South Africa (Prasa), Cromet Molepo, was facing disciplinary proceedings
for bugging telephones — including that of a senior shop steward — when
he resigned as the head of Umgeni Water... attorney Julian von Klemperer, was tasked by the board to investigate the phone tapping allegations.... The “bugging” scandal received widespread publicity at the time... Von Klemperer found that the telephones of three people — two former
employees and the shop steward — were bugged on the instructions of
Molepo...
Payments — totaling R51 000 — for the illegal surveillance were made through an attorney’s office in order to conceal them. When the attorney discovered the truth, he withdrew his services and blew the whistle. more
Payments — totaling R51 000 — for the illegal surveillance were made through an attorney’s office in order to conceal them. When the attorney discovered the truth, he withdrew his services and blew the whistle. more
Reward if Found?
Lost in Space: Highly Classified Spy Satellite
An expensive, highly classified U.S. spy satellite is presumed to be a total loss after it failed to reach orbit atop a Space Exploration Technologies Corp. rocket on Sunday, according to industry and government officials.
Lawmakers and congressional staffers from the Senate and the House have been briefed about the botched mission, some of the officials said. The secret payload—code-named Zuma and launched from Florida on board a Falcon 9 rocket—is believed to have plummeted back into the atmosphere, they said, because it didn’t separate as planned from the upper part of the rocket. more

An expensive, highly classified U.S. spy satellite is presumed to be a total loss after it failed to reach orbit atop a Space Exploration Technologies Corp. rocket on Sunday, according to industry and government officials.
Lawmakers and congressional staffers from the Senate and the House have been briefed about the botched mission, some of the officials said. The secret payload—code-named Zuma and launched from Florida on board a Falcon 9 rocket—is believed to have plummeted back into the atmosphere, they said, because it didn’t separate as planned from the upper part of the rocket. more

What Becomes of Industrial Espionage?
Ever wonder what happens to all the intellectual property that is collected by corporate espionage snoops? An article in Wired Magazine gives some clues in Tesla's Latest Chinese Competitor Takes Screens to an Extreme...
Keep an eye out to see where your intellectual property is popping up. Better yet, keep an eye out for the easiest-to-spot, early warning sign you are under attack, electronic eavesdropping.
Smart businesses conduct regularly scheduled Technical Surveillance Countermeasures bug sweeps, aka TSCM. It's a standard security practice. You can learn more about it, here.
Chinese car startup Byton unveiled an SUV... if the company manages to sell for the quoted $45,000 price, will excite people who can’t wait for a Tesla Model 3...Ostensibly, this is an article about a new car, but the espionage undertones are obvious.
“What’s significant here is they seem to have done a thorough job of answering all the questions,” said Stephanie Brinley, Senior Analyst at IHS Markit, as we pushed through the crowds trying to take pictures of the crazy interior through the windows. “They seem to have learnt from some of the others who had more ideas, and less detail.”...
The SUV should be good for over 300 miles of range from a 71- or 95-kwh battery back, quite similar to what Tesla offers. The battery can be fast charged to 80 percent in 30 minutes, totally plausible with current technology. It will come with single, or dual motors, just like Tesla cars.
Keep an eye out to see where your intellectual property is popping up. Better yet, keep an eye out for the easiest-to-spot, early warning sign you are under attack, electronic eavesdropping.
Smart businesses conduct regularly scheduled Technical Surveillance Countermeasures bug sweeps, aka TSCM. It's a standard security practice. You can learn more about it, here.
Sunday, January 7, 2018
Corporate Espionage Alert - Whale Phishing in 2018
Phishing scams are becoming ever more sophisticated...
“We need to focus on people patching and the human firewall,” said Anthony Dagostino, global head of cyber risk at Willis Towers Watson. “This requires more effective training and awareness campaigns to make sure people aren’t clicking on things...
“We will see more whale phishing in 2018, where cyber criminals will target individuals based on things like their LinkedIn or Facebook profiles,” Dagostino told Insurance Business. “General counsel, chief financial officers and even board members are being very specifically targeted just for hackers to get certain information they have.
“It doesn’t necessarily have to be for a data breach – it’s really corporate espionage driven. They either want to get information on an up-coming acquisition, or future business plans that they can use for insider trading.” more
“We need to focus on people patching and the human firewall,” said Anthony Dagostino, global head of cyber risk at Willis Towers Watson. “This requires more effective training and awareness campaigns to make sure people aren’t clicking on things...
“We will see more whale phishing in 2018, where cyber criminals will target individuals based on things like their LinkedIn or Facebook profiles,” Dagostino told Insurance Business. “General counsel, chief financial officers and even board members are being very specifically targeted just for hackers to get certain information they have.
“It doesn’t necessarily have to be for a data breach – it’s really corporate espionage driven. They either want to get information on an up-coming acquisition, or future business plans that they can use for insider trading.” more
UPDATE - PA State Police Investigating Possible Wiretapping... of them.
A New Milford man suspected of listening in to phone calls in the Gibson barracks had an assault-style rifle and bombs at home, state police said.
 Nathan J. Grover, 28, 512 Old Route 11, is sought on charges of weapons of mass destruction, prohibited weapons and drug-related crimes. Capt. Christopher Paris, commander of Troop R, which includes the Gibson barracks, confirmed Friday that Grover was not in custody.
Nathan J. Grover, 28, 512 Old Route 11, is sought on charges of weapons of mass destruction, prohibited weapons and drug-related crimes. Capt. Christopher Paris, commander of Troop R, which includes the Gibson barracks, confirmed Friday that Grover was not in custody.
State police became aware that Grover, who worked for North-Eastern Pennsylvania Telephone Co., may have been using his position to listen to phone calls at the Gibson barracks, according to a criminal complaint filed Thursday by Sgt. Michael Joyce...
Anyone with information on his whereabouts should contact the Gibson barracks at 570-465-3154. more
 Nathan J. Grover, 28, 512 Old Route 11, is sought on charges of weapons of mass destruction, prohibited weapons and drug-related crimes. Capt. Christopher Paris, commander of Troop R, which includes the Gibson barracks, confirmed Friday that Grover was not in custody.
Nathan J. Grover, 28, 512 Old Route 11, is sought on charges of weapons of mass destruction, prohibited weapons and drug-related crimes. Capt. Christopher Paris, commander of Troop R, which includes the Gibson barracks, confirmed Friday that Grover was not in custody. State police became aware that Grover, who worked for North-Eastern Pennsylvania Telephone Co., may have been using his position to listen to phone calls at the Gibson barracks, according to a criminal complaint filed Thursday by Sgt. Michael Joyce...
Anyone with information on his whereabouts should contact the Gibson barracks at 570-465-3154. more
Amazon Echo ‘Drop In’ Feature - Easy Eavesdropping?
As voice-based “personal assistants” are becoming ubiquitous in modern, connected American homes, so is the feeling they might be listening in on people when they least expect it or want it.
Amazon Echo, Dot and Show users know that Alexa is always listening. With a simple command she can turn on your lights, play music and even order pizza.
But do you know who else might be listening in to everything going on in your home? more
Saturday, January 6, 2018
Workplace Spycam Man Pleads Guilty
PA - A Douglass man faces court supervision after he admitted to invading the privacy of a female co-worker by planting a camera under her desk and recording her at their Montgomery Township workplace.
Anthony Joseph DePaul, 35, of the 100 block of Chalet Road, was sentenced in Montgomery County Court to four years’ probation after he pleaded guilty to misdemeanor charges of invasion of privacy in connection with the incidents...
“The device was attached to the bottom of her desk with Velcro and was pointed in the direction of her chair,” Montgomery Township Police Officer James T. Matlack alleged in the criminal complaint...
The device, which was provided to police, was small with a lens at one end, court documents indicate...several employees stated they had observed DePaul near the desk of the female victim in the weeks leading up to the discovery of the camera...
When detectives interviewed DePaul about the matter he admitted to placing the camera under the woman’s desk four to five times and to recording the victim as she sat at her desk, according to the criminal complaint. more
Anthony Joseph DePaul, 35, of the 100 block of Chalet Road, was sentenced in Montgomery County Court to four years’ probation after he pleaded guilty to misdemeanor charges of invasion of privacy in connection with the incidents...
 |
| Lens on a typical key-fob spy camera. |
The device, which was provided to police, was small with a lens at one end, court documents indicate...several employees stated they had observed DePaul near the desk of the female victim in the weeks leading up to the discovery of the camera...
When detectives interviewed DePaul about the matter he admitted to placing the camera under the woman’s desk four to five times and to recording the victim as she sat at her desk, according to the criminal complaint. more
Friday, January 5, 2018
Counter-Espionage For Business Travelers Course
The Counter-Espionage for Business Travelers Course
is a two-day seminar designed to educate those individuals in your
organization who may become targets of espionage, whether knowingly or
unknowingly, from an economic competitor or a hostile intelligence
service.
Unfortunately, most business travelers are untrained, and thus unprepared, to handle even the most common espionage tactics, such as:

 If you can't go for the course, at least go for some good books on the subject:
If you can't go for the course, at least go for some good books on the subject:
Among Enemies: Counter Espionage for the Business Traveler by Luke Bencie.
Staying Safe Abroad: Traveling, Working & Living in a Post-9/11 World by Edward L. Lee
Unfortunately, most business travelers are untrained, and thus unprepared, to handle even the most common espionage tactics, such as:
- Elicitation
- Bribery
- Blackmail
- Extortion
- Electronic Surveillance
- Electronic Exploitation
- Physical Surveillance
- Hotel/Office Covert Intrusions
- Economic vs. Industrial Espionage
- Foreign Intelligence Collection Methods
- How to Recognize Elicitation and Recruiting Techniques
- Operational Security (OPSEC) Awareness
- Communication Security (COMSEC) Awareness
- Data Attack and Intrusion Methodologies
- How to become an "Invisible Traveler"
- Surveillance Detection Techniques

 If you can't go for the course, at least go for some good books on the subject:
If you can't go for the course, at least go for some good books on the subject:Among Enemies: Counter Espionage for the Business Traveler by Luke Bencie.
Staying Safe Abroad: Traveling, Working & Living in a Post-9/11 World by Edward L. Lee
Court Rules: Agricultural Spying is Free Speech
A federal appeals court panel says Idaho’s ban on spying at farms, dairies and slaughterhouses violates free speech rights.
 The 9th U.S. Circuit Court of Appeals on Thursday ruled that sections of the law illegally targeted free speech and investigative journalism. However, the panel also ruled the law correctly criminalized those who made false statements to obtain records at an agricultural facility.
The 9th U.S. Circuit Court of Appeals on Thursday ruled that sections of the law illegally targeted free speech and investigative journalism. However, the panel also ruled the law correctly criminalized those who made false statements to obtain records at an agricultural facility.
Idaho lawmakers passed the law making it a crime to surreptitiously videotape agriculture operations in 2014 after the state’s $2.5 billion dairy industry complained that videos of cows being abused at a southern Idaho dairy unfairly hurt their businesses. more
 The 9th U.S. Circuit Court of Appeals on Thursday ruled that sections of the law illegally targeted free speech and investigative journalism. However, the panel also ruled the law correctly criminalized those who made false statements to obtain records at an agricultural facility.
The 9th U.S. Circuit Court of Appeals on Thursday ruled that sections of the law illegally targeted free speech and investigative journalism. However, the panel also ruled the law correctly criminalized those who made false statements to obtain records at an agricultural facility.Idaho lawmakers passed the law making it a crime to surreptitiously videotape agriculture operations in 2014 after the state’s $2.5 billion dairy industry complained that videos of cows being abused at a southern Idaho dairy unfairly hurt their businesses. more
Digital Spying And Divorce In The Smartphone Age
 |
| Typical magnetic mount GPS tracker. |
It was the summer of 2016, and M was worried her ex-husband was stalking her. She would get out of town and stay with friends. But, as she noted in court documents, her ex seemed to know exactly where she was and whom she visited — down to the time of day and street...
Welcome to divorce in the 21st century — when what it means to be safe and how much privacy you're entitled to are open questions.
M's case is not unique. NPR talked with dozens of marital experts. They say digital spying is changing divorce as we know it. The tools are abundant. Clients use it in an effort to stay in control after a separation or to gather evidence of extra-marital affairs or drug abuse. But the laws are murky, and law enforcement is lagging far behind. more
Multiple Bathroom Spy Cameras = 30 Days in Jail
 |
| Typical air freshener spy camera. |
Joseph J. McGrath, 32, of East Longmeadow, Mass., was charged in September with 10 counts of violation of privacy after police in York were called to the home, where hidden cameras – some disguised as air fresheners – were found in four bathrooms, according to the York Police Department...
The cameras allegedly placed by McGrath targeted both children and adults staying at the home while on vacation with him, police said. more
Thursday, January 4, 2018
The White House West Wing Bans Personal Mobile Phones
The White House is banning its employees from using personal mobile phones while at work in the West Wing... White House chief of staff John Kelly imposed the ban, citing security concerns...
There are too many devices connected to the White House wireless network, and personal phones aren’t as secure as those issued by the federal government, said an official who spoke on condition of anonymity to discuss an internal White House matter.
Aides who opposed the ban said they cannot use their work phones for personal use, and that work phones can’t accommodate texting. They believe the ban will be a hardship because texting is often the easiest way for their families to reach them in the middle of a busy day of meetings. more
"How are they going to enforce that!" I hear you say.
Most likely with AirPatrolTM for Security.
There are too many devices connected to the White House wireless network, and personal phones aren’t as secure as those issued by the federal government, said an official who spoke on condition of anonymity to discuss an internal White House matter.
Aides who opposed the ban said they cannot use their work phones for personal use, and that work phones can’t accommodate texting. They believe the ban will be a hardship because texting is often the easiest way for their families to reach them in the middle of a busy day of meetings. more
"How are they going to enforce that!" I hear you say.
Most likely with AirPatrolTM for Security.
TV Producer Accused of Using Unauthorized Camera
NY - A Pleasantville CNBC-TV producer accused of spying on his teenage nanny with a secret camera he placed in the bathroom of his home is due to appear in village court Tuesday evening.
Dan Switzen, 44, who was arrested by Pleasantville Police in November, allegedly hid a camera inside a tissue box on the counter of the bathroom, according to authorities.
The camera was discovered when his 18-year-old live-in nanny and two friends discovered the camera and took it to police. more
 |
| From a Walmart on-line ad. |
The camera was discovered when his 18-year-old live-in nanny and two friends discovered the camera and took it to police. more
PA State Police Investigating Possible Wiretapping... of them.
PA - Newswatch 16 has learned state police in Susquehanna County have been investigating a possible case of eavesdropping on their own barracks.
The man they've been investigating was one of the lead network techs at the phone company until recently.
 At the Gibson state police barracks in Susquehanna County, all kinds of calls come in and out, and many of the phone conversations relate to active criminal investigations.
At the Gibson state police barracks in Susquehanna County, all kinds of calls come in and out, and many of the phone conversations relate to active criminal investigations.
Back in September, troopers were investigating an alleged assault at Nathan Grover's home near New Milford. That's when someone told them Grover, 28, a self-proclaimed hacker, was eavesdropping on state police...
There are questions over two suspicious "trouble tickets" found during NEP Telephone's internal investigation. One was a request that didn't come from troopers that could essentially route a phone call made to state police anywhere.
Another was trouble on a phone line registered to a man near Nicholson that somehow was connected to the Gibson barracks account. more
The man they've been investigating was one of the lead network techs at the phone company until recently.
 At the Gibson state police barracks in Susquehanna County, all kinds of calls come in and out, and many of the phone conversations relate to active criminal investigations.
At the Gibson state police barracks in Susquehanna County, all kinds of calls come in and out, and many of the phone conversations relate to active criminal investigations. Back in September, troopers were investigating an alleged assault at Nathan Grover's home near New Milford. That's when someone told them Grover, 28, a self-proclaimed hacker, was eavesdropping on state police...
There are questions over two suspicious "trouble tickets" found during NEP Telephone's internal investigation. One was a request that didn't come from troopers that could essentially route a phone call made to state police anywhere.
Another was trouble on a phone line registered to a man near Nicholson that somehow was connected to the Gibson barracks account. more
Wednesday, January 3, 2018
Counterespionage Tip # 022: The Encryption & Password Mistake
An excerpt from the Forever 21 press release last week...
This happens frequently on devices which are introduced after the initial set-up of similar devices. It's similar to the not changing the default password syndrome.
Counterespionage Tip # 022: When installing new devices:
You may be surprised how many devices offer password protection and encryption these days...
Security settings on items in your environment should be checked periodically. A knowledgeable Technical Surveillance Countermeasures (TSCM) team can do this for you. It should be part of their inspection for electronic surveillance devices and information security loopholes.
If you don't have a TSCM team already, or are not sure of their capabilities, give me a call. ~Kevin
...After receiving a report from a third party in mid-October 2017 suggesting there may have been unauthorized access to data from payment cards that were used at certain Forever 21 stores, we immediately began an investigation. We hired leading payment technology and security firms to assist. The investigation determined that the encryption technology on some point-of-sale (POS) devices at some stores was not always on... moreThe setting to enable encryption may never have been set to on. If it was, the setting may not have been password protected, thus allowing the encryption to be turned on and off. Costly mistakes.
This happens frequently on devices which are introduced after the initial set-up of similar devices. It's similar to the not changing the default password syndrome.
Counterespionage Tip # 022: When installing new devices:
- Change the default password.
- Review all the settings. Turn off all the eavesdropper and espionage friendly settings.
- Pay particular attention to security-related settings.
- Enable encryption.
- Change the administrator's password if the device has one.
- Deter physical access to internal memory and components using security tape. Check often for tampering.
 |
| Removing an unencrypted printer drive for covert duplication. Murray Associates case history photo. |
- Point-of-sale (POS) devices.
- Wi-Fi Access Points.
- Audio and video teleconferencing equipment.
- Networked print centers.
- Stand-alone printers with Wi-Fi capabilities.
- VoIP telephone systems.
- Interactive white boards.
- Fax machines with memory vaults.
- Computers, tablets, mobile phones.
- Manufacturing equipment.
- Medical devices.
- CCTV cameras and recording systems.
Security settings on items in your environment should be checked periodically. A knowledgeable Technical Surveillance Countermeasures (TSCM) team can do this for you. It should be part of their inspection for electronic surveillance devices and information security loopholes.
If you don't have a TSCM team already, or are not sure of their capabilities, give me a call. ~Kevin
Carl Størmer - 1890's Spy Cam Man
These days, when it's so easy to sneak a hidden photo with your phone, we can forget just how unusual candid photography was during the 19th century.
 With technological limitation, our first photographs are mainly seated posed images that somehow give the impression that everyone in the 1800s was elegant and composed. But, thanks to one clever Norwegian student, we have a hidden glimpse of life in the 1890s.
With technological limitation, our first photographs are mainly seated posed images that somehow give the impression that everyone in the 1800s was elegant and composed. But, thanks to one clever Norwegian student, we have a hidden glimpse of life in the 1890s.
Carl Størmer (1874-1957) was a young student of mathematics when he purchased his first hidden camera. It was so small that the lens fit through the buttonhole in his vest with a cord that led down to his pocket, allowing him to secretly snap away.
In his biography for the Fellows of the Royal Society, he revealed it was actually a secret crush that led him toward photography. “When he was a young man at Oslo University he fell in love with a lady whom he did not know and with whom he was too bashful to become acquainted,” writes his biographer. “Wishing at least to have a picture of her, he decided that this was possible only by taking a photograph of her himself, without her knowing.” more
 With technological limitation, our first photographs are mainly seated posed images that somehow give the impression that everyone in the 1800s was elegant and composed. But, thanks to one clever Norwegian student, we have a hidden glimpse of life in the 1890s.
With technological limitation, our first photographs are mainly seated posed images that somehow give the impression that everyone in the 1800s was elegant and composed. But, thanks to one clever Norwegian student, we have a hidden glimpse of life in the 1890s.Carl Størmer (1874-1957) was a young student of mathematics when he purchased his first hidden camera. It was so small that the lens fit through the buttonhole in his vest with a cord that led down to his pocket, allowing him to secretly snap away.
In his biography for the Fellows of the Royal Society, he revealed it was actually a secret crush that led him toward photography. “When he was a young man at Oslo University he fell in love with a lady whom he did not know and with whom he was too bashful to become acquainted,” writes his biographer. “Wishing at least to have a picture of her, he decided that this was possible only by taking a photograph of her himself, without her knowing.” more
Tuesday, January 2, 2018
Stop Your Apps from Spying on Your TV Viewing
That innocent-looking mobile game you just downloaded might just have an ulterior motive. Behind the scenes, hundreds of different apps could be using your smartphone's microphone to figure out what you watch on TV, a new report from The New York Times reveals...
 Basically, a bunch of apps with innocuous names like "Pocket Bowling 3D" include extra software that's designed to listen for recognizable audio from your TV, including specific shows and commercials...
Basically, a bunch of apps with innocuous names like "Pocket Bowling 3D" include extra software that's designed to listen for recognizable audio from your TV, including specific shows and commercials...
All of these apps need to get your permission before they can record in the background. So the easiest way is just to deny that permission. However, it's possible that you might approved the request without realising it, or your kid might do it while playing with your phone. In that case, switching it off is pretty easy...
Just head into Settings on your device and check the permissions for the app in question. If the app has microphone access when it doesn't need to (why would a bowling game need to use your microphone?), just toggle that permission off. more
 Basically, a bunch of apps with innocuous names like "Pocket Bowling 3D" include extra software that's designed to listen for recognizable audio from your TV, including specific shows and commercials...
Basically, a bunch of apps with innocuous names like "Pocket Bowling 3D" include extra software that's designed to listen for recognizable audio from your TV, including specific shows and commercials...All of these apps need to get your permission before they can record in the background. So the easiest way is just to deny that permission. However, it's possible that you might approved the request without realising it, or your kid might do it while playing with your phone. In that case, switching it off is pretty easy...
Just head into Settings on your device and check the permissions for the app in question. If the app has microphone access when it doesn't need to (why would a bowling game need to use your microphone?), just toggle that permission off. more
Labels:
#eavesdropping,
advice,
Android,
App,
cell phone,
cybersecurity,
Hack,
iOS,
microphone,
privacy,
recording,
tracking
Ex-DA Disbarred for Illegal Tapping
 The former Brooklyn district attorney convicted of setting up an illegal wiretap on a romantic target and forging judges' signatures to get secure cellphone warrants has been disbarred by a New York appeals panel.
The former Brooklyn district attorney convicted of setting up an illegal wiretap on a romantic target and forging judges' signatures to get secure cellphone warrants has been disbarred by a New York appeals panel.The Dec. 29 order against Tara Frances Lenich comes about nine months after she admitted in New York federal court to using her position as a DA and investigator to illicitly create judicial orders authorizing cellphone intercepts.
One of her targets was reportedly a New York City Police Department detective... more
Proof 2018 will be a Great Year for TSCM Teams
The cost of eavesdropping, espionage, spying, and general snooping has gone the way of "long-distance" phone bills. For the cost of a visit to Starbucks, a few bucks can make everyone an eavesdropper, and apparently it's happening. Just look at the ad below for an FM wireless bug. China can't produce them fast enough. They are sold out! (more)
But, fear not dear buggers, you can still obtain GSM USB charger plug bugs. Unlike the FM bug, you don't have to be somewhere nearby to listen-in. Just call it from your cell phone, anywhere in the world. (more)
Happy New Year. Be safe... Support your favorite Technical Surveillance Countermeasures team.
 |
| Click to enlarge. |
 |
| Click to enlarge. |
 |
Labels:
#eavesdropping,
#espionage,
#TSCM,
advice,
cell phone,
product,
spybot,
wireless
Wednesday, December 27, 2017
Norway & Germany Call Time Out on Kiddy Smartwatches
Recently, Germany's Federal Network Agency (FNA) called foul on smartwatches that worked as listening devices — specifically those worn by children between the ages of 5 and 12, and used by parents, in particular, to eavesdrop on their kids while at school.
The German regulating body said that parents would listen in on classes and teachers without consent...
These special watches, work like a baby monitor — allowing someone to tap into the device and listen in to anything happening around it. And people are being asked now to not only keep an eye out for these particular smartwatches — but destroy them, and then send proof back to the FNA....
Germany's not alone in worrying about children's smartwatches. The Norwegian Consumer Council (NCC) had the same type of reaction a full month before the FNA, issuing a report about security concerns around the devices.
The NCC noted that smartwatches — besides acting as listening devices — can also transmit the location of a child — presumably to parents — but have security flaws which could open that information up easily to others. more
Glad they didn't have these forearm ankle bracelets when I was a kid. ~Kevin
 |
| "Piss off." |
These special watches, work like a baby monitor — allowing someone to tap into the device and listen in to anything happening around it. And people are being asked now to not only keep an eye out for these particular smartwatches — but destroy them, and then send proof back to the FNA....
Germany's not alone in worrying about children's smartwatches. The Norwegian Consumer Council (NCC) had the same type of reaction a full month before the FNA, issuing a report about security concerns around the devices.
The NCC noted that smartwatches — besides acting as listening devices — can also transmit the location of a child — presumably to parents — but have security flaws which could open that information up easily to others. more
Glad they didn't have these forearm ankle bracelets when I was a kid. ~Kevin
Labels:
#eavesdropping,
advice,
government,
GPS,
privacy,
product,
Ra-parents,
spybot
Revenge Spycam Shooting Gets Shooter Shot
GA - Macon Judicial Circuit District Attorney David Cooke said Thursday a man was sentenced to three years in prison after pleading guilty to burglary and spying on his ex-girlfriend.
 Cooke said Blake Herman, 35, of Macon broke into his ex-girlfriend's home on Jones Road and planted a camera in her bedroom as revenge for her breaking up with him.
Cooke said Blake Herman, 35, of Macon broke into his ex-girlfriend's home on Jones Road and planted a camera in her bedroom as revenge for her breaking up with him.
When Herman returned to his ex-girlfriend's home to remove the camera, her brother caught him and shot him thinking Herman was about to pull a gun.
The camera fell out of Herman's pocket during the ordeal, according to Cooke. more
 Cooke said Blake Herman, 35, of Macon broke into his ex-girlfriend's home on Jones Road and planted a camera in her bedroom as revenge for her breaking up with him.
Cooke said Blake Herman, 35, of Macon broke into his ex-girlfriend's home on Jones Road and planted a camera in her bedroom as revenge for her breaking up with him.When Herman returned to his ex-girlfriend's home to remove the camera, her brother caught him and shot him thinking Herman was about to pull a gun.
The camera fell out of Herman's pocket during the ordeal, according to Cooke. more
IT Spy Guy Hacks Computer Cameras
MI - A Charlevoix County man from the United Kingdom is in jail and facing more than 40 charges for disturbing, computer-related crimes.
 Police say Wayne Tambling got access to several victims’ computers and photographed them naked using the computer’s camera, without them knowing.
Police say Wayne Tambling got access to several victims’ computers and photographed them naked using the computer’s camera, without them knowing.
“They just noticed some strange things, some coincidences that led them to believe that someone might be spying on them,” Trooper Jeff Mercer, said.
State police say three victims came forward with that eerie feeling...
Tambling works in IT at Wojan Window and Door, the company says they are fully cooperating with police. more
 Police say Wayne Tambling got access to several victims’ computers and photographed them naked using the computer’s camera, without them knowing.
Police say Wayne Tambling got access to several victims’ computers and photographed them naked using the computer’s camera, without them knowing. “They just noticed some strange things, some coincidences that led them to believe that someone might be spying on them,” Trooper Jeff Mercer, said.
State police say three victims came forward with that eerie feeling...
Tambling works in IT at Wojan Window and Door, the company says they are fully cooperating with police. more
Double Oh Concession
The UK government is going to speed up the way it vets and hires new recruits at its spy agency Government Communications Headquarters, which is responsible for electronic surveillance, after it fell short of hiring targets at the end of the last fiscal year (pdf).
The spy agency has said that it’s losing potential top recruits to huge tech companies because of bumper salaries. GCHQ’s lengthy vetting process, which is backlogged, also doesn’t help...
GCHQ, one of Britain’s three intelligence and security agencies alongside MI5 and MI6, aims to increase headcount by 14% over the next four years to 6,639 people.
This is after it had a shortfall in recruitment of 22% in the fiscal year. The report added that in order to get more recruits through the door, it will have to assign more people to the vetting process. more
 |
| GCHQ v TECH |
GCHQ, one of Britain’s three intelligence and security agencies alongside MI5 and MI6, aims to increase headcount by 14% over the next four years to 6,639 people.
This is after it had a shortfall in recruitment of 22% in the fiscal year. The report added that in order to get more recruits through the door, it will have to assign more people to the vetting process. more
Tuesday, December 26, 2017
Seoul Trained Trackers, or Party Police Bugged
South Korea - One maintenance office of a Seoul apartment complex is in hot water after it took its investigation into noise complaints one step too far.
 According to residents and security personnel, during a recent five-day period, the maintenance office dispatched security guards to investigate the source of excessive noise among suites on floors 9 through 15 in one building. The guards, deployed from midnight to three in the morning on the apartment corridors, were armed with sound amplifying equipment.
According to residents and security personnel, during a recent five-day period, the maintenance office dispatched security guards to investigate the source of excessive noise among suites on floors 9 through 15 in one building. The guards, deployed from midnight to three in the morning on the apartment corridors, were armed with sound amplifying equipment.

“Throughout the course of the investigation, I ended up listening to the conversations of the residents in each suite, even though I didn’t want to,” one security guard said. “Problems of excessive noise should be resolved through legal and appropriate means, but I think that using a sound amplifier that can result in an invasion of privacy is taking things too far.” more
 According to residents and security personnel, during a recent five-day period, the maintenance office dispatched security guards to investigate the source of excessive noise among suites on floors 9 through 15 in one building. The guards, deployed from midnight to three in the morning on the apartment corridors, were armed with sound amplifying equipment.
According to residents and security personnel, during a recent five-day period, the maintenance office dispatched security guards to investigate the source of excessive noise among suites on floors 9 through 15 in one building. The guards, deployed from midnight to three in the morning on the apartment corridors, were armed with sound amplifying equipment.
“Throughout the course of the investigation, I ended up listening to the conversations of the residents in each suite, even though I didn’t want to,” one security guard said. “Problems of excessive noise should be resolved through legal and appropriate means, but I think that using a sound amplifier that can result in an invasion of privacy is taking things too far.” more
Labels:
#eavesdropping,
business,
ethics,
microphone,
privacy,
spybot,
tracking,
weird
Monday, December 25, 2017
Santa Claus is Coming to Town

You'd better watch out,
You'd better not cry,
You'd better not pout;
I'm telling you why.
Santa Claus is tapping
Your phone.
He's bugging your room,
He's reading your mail,
He's keeping a file
And running a tail.
Santa Claus is tapping
Your phone.
He hears you in the bedroom,
Surveills you out of doors,
And if that doesn't get the goods,
Then he'll use provocateurs.
So–you mustn't assume
That you are secure.
On Christmas Eve
He'll kick in your door.
Santa Claus is tapping
Your phone.
Author unknown
Sunday, December 24, 2017
Espionage Backdoor Installs via Printer-Spoofing Campaign
For many large organizations, emails from corporate printers and scanners are commonplace, and cyber-criminals are finding this vector to be a lucrative host to launch cyber-attacks.
Barracuda Networks has tracked an uptick in attacks through Canon, HP and Epson printer and scanner email attachments of late: Since late November, cyber-criminals have made millions of attempts to infect unsuspecting users by sending impersonated or spoofed emails from these common printer and scanner brands, with attachments that contain malware.
Once unpacked, the malware installs a backdoor on the machine that offers unauthorized access to a victim PC and cyber-espionage capabilities...
Further, indicating a ramsomware-ready aspect, attackers also can change the victim’s wallpaper to display a message of their choice.
Workers should use common sense to avoid the threat:
Barracuda Networks has tracked an uptick in attacks through Canon, HP and Epson printer and scanner email attachments of late: Since late November, cyber-criminals have made millions of attempts to infect unsuspecting users by sending impersonated or spoofed emails from these common printer and scanner brands, with attachments that contain malware.
Once unpacked, the malware installs a backdoor on the machine that offers unauthorized access to a victim PC and cyber-espionage capabilities...
Further, indicating a ramsomware-ready aspect, attackers also can change the victim’s wallpaper to display a message of their choice.
Workers should use common sense to avoid the threat:
- double-check with the sender if one didn’t know a scanned document was coming;
- hovering the mouse over every hyperlink to make sure it’s legitimate;
- and simply not clicking if there’s any doubt whatsoever. more
 |
| Example of a fake email. |
Fun Spy Facts
 |
| Too much training. |
- The first editorial assistant to work on the Oxford English Dictionary was sacked for industrial espionage.
- Secret agents have to be trained to forget their advanced driving courses.
- The French air force have a squad of golden eagles, trained to hunt down drones.
"Hey, kids. Make BIG money in your spare time. Train spies!"
The UAE is recruiting former CIA and US government officials in a bid to create a professional intelligence body modeled on leading Western agencies.
 The Gulf state has long relied on Western countries to build up its intelligence infrastructure, but are now paying big bucks to hire former US intelligence employees to build its spying capabilities.
The Gulf state has long relied on Western countries to build up its intelligence infrastructure, but are now paying big bucks to hire former US intelligence employees to build its spying capabilities.
Details of the training were reviewed by Foreign Policy and show daily seminars, scavenger hunts and training exercises in four-to-six man surveillance teams.
The following weeks provide advanced training on creating undercover identities when attending embassy functions and how to groom intelligence assets...
Former CIA and US government officials are drawn to the promise of a lucrative career, with instructor salaries of up to $1,000 a day funding an extravagant lifestyle, Foreign Policy reported. more
 The Gulf state has long relied on Western countries to build up its intelligence infrastructure, but are now paying big bucks to hire former US intelligence employees to build its spying capabilities.
The Gulf state has long relied on Western countries to build up its intelligence infrastructure, but are now paying big bucks to hire former US intelligence employees to build its spying capabilities. Details of the training were reviewed by Foreign Policy and show daily seminars, scavenger hunts and training exercises in four-to-six man surveillance teams.
The following weeks provide advanced training on creating undercover identities when attending embassy functions and how to groom intelligence assets...
Former CIA and US government officials are drawn to the promise of a lucrative career, with instructor salaries of up to $1,000 a day funding an extravagant lifestyle, Foreign Policy reported. more
The Catch Santa in the Act App, by Snowden?!?!
Earlier this year, NSA whistleblower Edward Snowden met with Jacqueline Moudeina, the first female lawyer in Chad and a legendary human rights advocate...
 Snowden told Moudeina that he was working on an app that could turn a mobile device into a kind of motion sensor in order to notify you when your devices are being tampered with.
Snowden told Moudeina that he was working on an app that could turn a mobile device into a kind of motion sensor in order to notify you when your devices are being tampered with.
The app could also tell you when someone had entered a room without you knowing, if someone had moved your things, or if someone had stormed into your friend’s house in the middle of the night.
Snowden recounted that pivotal conversation in an interview with the Verge. “She got very serious and told me, ‘I need this. I need this now. There’s so many people around us who need this.’”
Haven, announced today, is an app that does just that. Installed on a cheap burner Android device, Haven sends notifications to your personal, main phone in the event that your laptop has been tampered with.
If you leave your laptop at home or at an office or in a hotel room, you can place your Haven phone on top of the laptop, and when Haven detects motion, light, or movement — essentially, anything that might be someone messing with your stuff — it logs what happened. It takes photos, records sound, even takes down changes in light or acceleration, and then sends notifications to your main phone.
None of this logging is stored in the cloud, and the notifications you receive on your main phone are end-to-end encrypted over Signal. more
 Snowden told Moudeina that he was working on an app that could turn a mobile device into a kind of motion sensor in order to notify you when your devices are being tampered with.
Snowden told Moudeina that he was working on an app that could turn a mobile device into a kind of motion sensor in order to notify you when your devices are being tampered with.The app could also tell you when someone had entered a room without you knowing, if someone had moved your things, or if someone had stormed into your friend’s house in the middle of the night.
Snowden recounted that pivotal conversation in an interview with the Verge. “She got very serious and told me, ‘I need this. I need this now. There’s so many people around us who need this.’”
Haven, announced today, is an app that does just that. Installed on a cheap burner Android device, Haven sends notifications to your personal, main phone in the event that your laptop has been tampered with.
If you leave your laptop at home or at an office or in a hotel room, you can place your Haven phone on top of the laptop, and when Haven detects motion, light, or movement — essentially, anything that might be someone messing with your stuff — it logs what happened. It takes photos, records sound, even takes down changes in light or acceleration, and then sends notifications to your main phone.
None of this logging is stored in the cloud, and the notifications you receive on your main phone are end-to-end encrypted over Signal. more
NJ Spycam'er Gets Slammer
A Williamstown, New Jersey, man was sentenced to 180 months in
prison for receiving images and videos of child sexual abuse and for
producing child pornography using a hidden camera in his bathroom,
Acting U.S. Attorney William E. Fitzpatrick announced. more
Wednesday, December 20, 2017
TSCM - A Prudent Business Practice - Misunderstood by the Press
The head of the Environmental Protection Agency used public money to have his office swept for hidden listening devices and bought sophisticated biometric locks for additional security.
The spending items, totaling nearly $9,000, are among a string of increased counter-surveillance precautions taken by EPA Administrator Scott Pruitt...
EPA spokesman Jahan Wilcox defended the spending. "Administrator Pruitt has received an unprecedented amount of threats against him...
Wilcox said that under the Obama administration, then-EPA Administrator Lisa Jackson also had her office swept for listening devices. more
Conducting Technical Surveillance Countermeasures (TSCM) is an integral part of any competent information security program.
It is a common, albeit subtle, business practice in the private sector, and an absolute requirement in governments worldwide.
The cost of a strategic information loss via undiscovered electronic surveillance makes proactive TSCM inspections look like pocket change cheap insurance. However, unlike insurance, TSCM inspections can prevent the loss.
Visit counterespionage.com to learn more. ~Kevin
The spending items, totaling nearly $9,000, are among a string of increased counter-surveillance precautions taken by EPA Administrator Scott Pruitt...
EPA spokesman Jahan Wilcox defended the spending. "Administrator Pruitt has received an unprecedented amount of threats against him...
Wilcox said that under the Obama administration, then-EPA Administrator Lisa Jackson also had her office swept for listening devices. more
It is a common, albeit subtle, business practice in the private sector, and an absolute requirement in governments worldwide.
The cost of a strategic information loss via undiscovered electronic surveillance makes proactive TSCM inspections look like pocket change cheap insurance. However, unlike insurance, TSCM inspections can prevent the loss.
Visit counterespionage.com to learn more. ~Kevin
Tuesday, December 19, 2017
Hollywood Has Always Played by a Different Set of Rules
Terry Crews is alleging that he and his family are the victims of a plot to "track" and "possibly bug" them, the actor and Time Magazine Silence Breaker posted on Twitter.
"My assailant Adam Venit is the founding partner at @WME, a corporation worth over $8 billion. I believe my family is being tracked and possibly bugged," he wrote as part of a series of tweets.
Crews also claims that someone possibly hacked into his son's computer. more
"My assailant Adam Venit is the founding partner at @WME, a corporation worth over $8 billion. I believe my family is being tracked and possibly bugged," he wrote as part of a series of tweets.
Crews also claims that someone possibly hacked into his son's computer. more
Saturday, December 16, 2017
Video Voyeurism: Carnival Cruise's Botched Investigation
A Florida family was shocked to discover a camera hidden among wires in their Carnival Cruise Line cabin.
The Pensacola couple, along with their 10-year-old son, found the device while searching undusted areas of the room after the father suffered an allergy attack during the second night of their journey from Mobile, Al., to Mexico, the Miami New Times reported.
According to the father, who was not identified by name, the camera was placed behind a TV in their room. The lens was sticking out a bit, pointing directly at the bed.
The man claimed the device was "warm to the touch" and appeared to have an antenna, which leads him to believe it may have been transmitting information to a third party. more
The couple reported the presence of the camera and transmitter in their cabin to the cruise ship’s security department. One of Carnival’s security personnel arrived in their cabin. He disconnected and removed the camera and transmitter with no gloves on and did not attempt to secure the room. In the video below, you can hear the passenger asking the officer why he was not wearing gloves.
The passenger thereafter communicated with the security staff to obtain an update. According to the passengers, the Carnival security personnel confirmed that the camera and transmitter: (1) were operational; (2) were typically the type of devices used on video drones: and (3) the transmitter was a long range device. To the passenger's knowledge, Carnival did not promptly report the incident to the Federal Bureau of Investigation (FBI). more
This is a cautionary tale. Video voyeurism can happen to any business which offers hospitality, restrooms, changing rooms, shower areas, etc., to customers, visitors or employees.
Handling the situation properly when it arises is important, and easy to do. Visit spycamdetection.training to learn how. Mishandling an incident, or sweeping it under the rug, will likely result in expensive litigation. Litigation you will likely lose.
 |
| Click to enlarge. |
According to the father, who was not identified by name, the camera was placed behind a TV in their room. The lens was sticking out a bit, pointing directly at the bed.
The man claimed the device was "warm to the touch" and appeared to have an antenna, which leads him to believe it may have been transmitting information to a third party. more
The couple reported the presence of the camera and transmitter in their cabin to the cruise ship’s security department. One of Carnival’s security personnel arrived in their cabin. He disconnected and removed the camera and transmitter with no gloves on and did not attempt to secure the room. In the video below, you can hear the passenger asking the officer why he was not wearing gloves.
The passenger thereafter communicated with the security staff to obtain an update. According to the passengers, the Carnival security personnel confirmed that the camera and transmitter: (1) were operational; (2) were typically the type of devices used on video drones: and (3) the transmitter was a long range device. To the passenger's knowledge, Carnival did not promptly report the incident to the Federal Bureau of Investigation (FBI). more
This is a cautionary tale. Video voyeurism can happen to any business which offers hospitality, restrooms, changing rooms, shower areas, etc., to customers, visitors or employees.
Handling the situation properly when it arises is important, and easy to do. Visit spycamdetection.training to learn how. Mishandling an incident, or sweeping it under the rug, will likely result in expensive litigation. Litigation you will likely lose.
Are Google and Amazon Patently Eavesdropping?
Patent applications from Amazon and Google revealed how their Alexa and Voice Assistant powered smart speakers are 'spying' on you.
 The findings were published in a report created by Santa Monica, California based advocacy group Consumer Watchdog.
The findings were published in a report created by Santa Monica, California based advocacy group Consumer Watchdog.
The study warns of an Orwellian future in which the gadgets eavesdrop on everything from confidential conversations to your toilet flushing habits...
The study found that digital assistants can be 'awake' even when users think they aren't listening...
In fact, the devices listen all the time they are turned on – and Amazon has envisioned Alexa using that information to build profiles on anyone in the room to sell them goods. more
 The findings were published in a report created by Santa Monica, California based advocacy group Consumer Watchdog.
The findings were published in a report created by Santa Monica, California based advocacy group Consumer Watchdog.The study warns of an Orwellian future in which the gadgets eavesdrop on everything from confidential conversations to your toilet flushing habits...
The study found that digital assistants can be 'awake' even when users think they aren't listening...
In fact, the devices listen all the time they are turned on – and Amazon has envisioned Alexa using that information to build profiles on anyone in the room to sell them goods. more
Letter Accuses Uber of Corporate Espionage and Wiretapping
The legal battle between Uber the ride-hailing behemoth and Waymo the self-driving unit of Alphabet reached a pivotal point this week as the Judge presiding over the case released a letter based on the account of a former employee at Uber.
The letter alleged that a division with Uber has been responsible for carrying out acts such as theft of trade secrets, corporate espionage, bribery of officials in foreign countries, and different types of unlawful surveillance.
The letter, given the name “Jacobs Letter,” was authored by an attorney who represents Richard Jacobs, a former employee at Uber who held the position of global intelligence manager prior to his firing last April.
In the highly detailed account accusations are leveled of systematic illegal activities inside the Strategic Services Group (SSG) of Uber, which allegedly sought out the trade secrets of other companies through data collection and eavesdropping. more
Quote from the letter...
Uber’s Marketplace Analytics team…fraudulently impersonates riders and drivers on competitor platforms, hacks into competitor networks, and conducts unlawful wiretapping. more
Another version of the story...
Uber illegally recorded phone calls and wiretapped the phones of executives at rival companies in a global “intelligence gathering” operation that went on for years, a former employee has alleged.
In a 37-page letter made public in federal court on Friday, Richard Jacobs, a former security employee with the ride-hailing service, alleges Uber set up internal teams whose sole purpose was to spy on competitors. “Uber has engaged, and continues to engage, in illegal intelligence gathering on a global scale,” Jacobs wrote, according to The New York Times.
The teams allegedly infiltrated chat rooms, impersonated drivers of rival companies, and placed surveillance on executives of those companies, including by illegally recording phone calls, the letter claims.
Jacobs’ allegations stem from a trade secrets case against Uber filed by Waymo, Alphabet’s self-driving unit, which says Uber stole information about autonomous driving technology. more
The letter alleged that a division with Uber has been responsible for carrying out acts such as theft of trade secrets, corporate espionage, bribery of officials in foreign countries, and different types of unlawful surveillance.
The letter, given the name “Jacobs Letter,” was authored by an attorney who represents Richard Jacobs, a former employee at Uber who held the position of global intelligence manager prior to his firing last April.
In the highly detailed account accusations are leveled of systematic illegal activities inside the Strategic Services Group (SSG) of Uber, which allegedly sought out the trade secrets of other companies through data collection and eavesdropping. more
Quote from the letter...
Uber’s Marketplace Analytics team…fraudulently impersonates riders and drivers on competitor platforms, hacks into competitor networks, and conducts unlawful wiretapping. more
Another version of the story...
Uber illegally recorded phone calls and wiretapped the phones of executives at rival companies in a global “intelligence gathering” operation that went on for years, a former employee has alleged.
In a 37-page letter made public in federal court on Friday, Richard Jacobs, a former security employee with the ride-hailing service, alleges Uber set up internal teams whose sole purpose was to spy on competitors. “Uber has engaged, and continues to engage, in illegal intelligence gathering on a global scale,” Jacobs wrote, according to The New York Times.
The teams allegedly infiltrated chat rooms, impersonated drivers of rival companies, and placed surveillance on executives of those companies, including by illegally recording phone calls, the letter claims.
Jacobs’ allegations stem from a trade secrets case against Uber filed by Waymo, Alphabet’s self-driving unit, which says Uber stole information about autonomous driving technology. more
Wednesday, December 13, 2017
For One Family - A New Christmas Gift Rule
Op-ed, NYT opinion By Ashley Boyd
During the holiday season, my husband and I tend to offer suggestions to those who are generous enough to insist on buying presents for our kids.
Things like “Don’t spend more than $50” and “No guns.” Or, for those with whom we can be comfortably blunt, “Just cash, please....
This year we’re adding a new rule to our list: No toys that can spy. The idea: to keep seemingly innocuous internet-connected devices that may compromise our privacy and security out of our home and especially out of our children’s hands. more
• CBS video report on holiday toys that can spy.
• All the cool gifts are made for spying on you.
 |
| Click to enlarge. |
During the holiday season, my husband and I tend to offer suggestions to those who are generous enough to insist on buying presents for our kids.
Things like “Don’t spend more than $50” and “No guns.” Or, for those with whom we can be comfortably blunt, “Just cash, please....
This year we’re adding a new rule to our list: No toys that can spy. The idea: to keep seemingly innocuous internet-connected devices that may compromise our privacy and security out of our home and especially out of our children’s hands. more
• CBS video report on holiday toys that can spy.
• All the cool gifts are made for spying on you.
Labels:
cautionary tale,
cybersecurity,
Internet,
IoT,
mores,
privacy,
Ra-parents,
Santa
FutureWatch: That Photo Can Now Be Traced to Your Phone
A University at Buffalo-led team of researchers has discovered how to identify smartphones by examining just one photo taken by the device.
 The advancement opens the possibility of using smartphones—instead of body parts—as a form of identification to deter cybercrime.
The advancement opens the possibility of using smartphones—instead of body parts—as a form of identification to deter cybercrime.
"Like snowflakes, no two smartphones are the same. Each device, regardless of the manufacturer or make, can be identified through a pattern of microscopic imaging flaws that are present in every picture they take," says Kui Ren, the study's lead author. "It's kind of like matching bullets to a gun, only we're matching photos to a smartphone camera."
The new technology, to be presented in February at the 2018 Network and Distributed Systems Security Conference in California, is not yet available to the public. However, it could become part of the authentication process—like PIN numbers and passwords—that customers complete at cash registers, ATMs and during online transactions. more
 The advancement opens the possibility of using smartphones—instead of body parts—as a form of identification to deter cybercrime.
The advancement opens the possibility of using smartphones—instead of body parts—as a form of identification to deter cybercrime."Like snowflakes, no two smartphones are the same. Each device, regardless of the manufacturer or make, can be identified through a pattern of microscopic imaging flaws that are present in every picture they take," says Kui Ren, the study's lead author. "It's kind of like matching bullets to a gun, only we're matching photos to a smartphone camera."
The new technology, to be presented in February at the 2018 Network and Distributed Systems Security Conference in California, is not yet available to the public. However, it could become part of the authentication process—like PIN numbers and passwords—that customers complete at cash registers, ATMs and during online transactions. more
Security Director Alert: HP Laptops with Hidden Keyloggers
Researcher Michael Myng found a deactivated keylogger in a piece of software found on over 460 HP laptop models. A full list of affected laptops is here. The keylogger is deactivated by default but could represent a privacy concern if an attacker has physical access to the computer...
The bottom line? Update your HP laptop as soon as possible. If you are on HP’s list of affected laptops you can download the fix here. more
The bottom line? Update your HP laptop as soon as possible. If you are on HP’s list of affected laptops you can download the fix here. more
Tuesday, December 12, 2017
33 Years Late, or You'll Never be a Stranger Here
China has been building what it calls "the world's biggest camera surveillance network".
 Across the country, 170 million CCTV cameras are already in place and an estimated 400 million new ones will be installed in the next three years.
Across the country, 170 million CCTV cameras are already in place and an estimated 400 million new ones will be installed in the next three years.
Many of the cameras are fitted with artificial intelligence, including facial recognition technology. The BBC's John Sudworth has been given rare access to one of the new hi-tech police control rooms. excellent video demo
 Across the country, 170 million CCTV cameras are already in place and an estimated 400 million new ones will be installed in the next three years.
Across the country, 170 million CCTV cameras are already in place and an estimated 400 million new ones will be installed in the next three years.Many of the cameras are fitted with artificial intelligence, including facial recognition technology. The BBC's John Sudworth has been given rare access to one of the new hi-tech police control rooms. excellent video demo
Monday, December 11, 2017
Mickey With the Big Ears - RIP
Mickey Gurdus was always a good listener.
For decades he commanded a battery of shortwave and FM radios, UHF and VHF receivers, tape recorders and other devices from a swivel chair in his Tel Aviv apartment, all to intercept and record foreign news broadcasts, secret satellite transmissions, confidential military messages and diplomatic conversations.
He was no vicarious eavesdropper, however. Mr. Gurdus listened for a living.
He monitored the airwaves for the state-run Israel Radio and tipped his editors — and, sometimes, intelligence agents — to hijackings, invasions and revolutions. In one instance he intercepted a telephone call between the White House and Air Force One. more
Amazingly, there was a time when anyone could eavesdrop on the radio-telephone calls from Air Force One. All one needed was a radio which could receive shortwave and/or frequencies around 409 MHz. More detailed instructions are still floating around the net. These days, communications are encrypted, and are mostly routed via satellite. ~Kevin
 |
| Click to enlarge |
He was no vicarious eavesdropper, however. Mr. Gurdus listened for a living.
He monitored the airwaves for the state-run Israel Radio and tipped his editors — and, sometimes, intelligence agents — to hijackings, invasions and revolutions. In one instance he intercepted a telephone call between the White House and Air Force One. more
Amazingly, there was a time when anyone could eavesdrop on the radio-telephone calls from Air Force One. All one needed was a radio which could receive shortwave and/or frequencies around 409 MHz. More detailed instructions are still floating around the net. These days, communications are encrypted, and are mostly routed via satellite. ~Kevin
Subscribe to:
Comments (Atom)








