A Maryland university student has pleaded guilty to illegally wiretapping a congressional staffer and putting the conversation on Facebook Live without consent...
Prosecutors say Burdett, a 21-year-old advocate for Maryland Marijuana Justice, took part in a rally in front of Rep. Andy Harris' office in Salisbury, Maryland, in October. Then he and others met with a member of the congressman's staff in his office.
Harris' staff told the group not to record the meeting, citing office policy, but prosecutors say Burdett recorded and streamed it on Facebook Live without the staffer's consent. more
Monday, March 25, 2019
FutureWatch - Who Really Lives in that Apartment
 NY - A Brooklyn landlord intends to install facial recognition technology at
the entrance of a roughly 700-unit rent-stabilized complex, raising
alarm among tenants and housing rights attorneys about what they say is a
far-reaching and egregious form of digital surveillance...
NY - A Brooklyn landlord intends to install facial recognition technology at
the entrance of a roughly 700-unit rent-stabilized complex, raising
alarm among tenants and housing rights attorneys about what they say is a
far-reaching and egregious form of digital surveillance...“We don’t want to be tracked,” said Icemae Downes, a longtime tenant. “We are not animals. This is like tagging us through our faces because they can’t implant us with a chip.” more
Thursday, March 21, 2019
Korea - Molka Means Spycam - Government Creates a Handbook for Women
The Seoul Metropolitan Government on Monday distributed guidelines on how to respond to spycam crimes for victims and law enforcement officers, amid a growing epidemic of spycam porn in the country.
Divided into two parts -- for civilians and police officers -- the handbook was designed to raise awareness of what constitutes secondary damage to victims of spycam porn and how police officers and victims can handle such cases, according to the Seoul city government.
For example, the guidelines recommend that victims secure evidence -- such as a hidden camera -- if possible and remember the perpetrator’s appearance. If illegally filmed videos have already been distributed, the advice is to copy the links and obtain screenshots. Then the victims should report the situation to the police and ask the website or social media companies to remove the videos, the handbook says. more
-----
The (K-Pop) scandal magnifies the proliferation of hidden camera porn in South Korea — an issue which drove 22,000 women to the streets last June in the largest women’s demonstration in the nation’s history. Known as molka, meaning “spycam”, hidden camera porn has become an increasingly visible issue in South Korea, as the distribution of footage from secret, tiny cameras — often depicting women in sexual or intimate circumstances without their consent — has grown in recent years. From 2013 to 2017, police estimate nearly 6,000 cases of spycam porn each year. more
Divided into two parts -- for civilians and police officers -- the handbook was designed to raise awareness of what constitutes secondary damage to victims of spycam porn and how police officers and victims can handle such cases, according to the Seoul city government.
For example, the guidelines recommend that victims secure evidence -- such as a hidden camera -- if possible and remember the perpetrator’s appearance. If illegally filmed videos have already been distributed, the advice is to copy the links and obtain screenshots. Then the victims should report the situation to the police and ask the website or social media companies to remove the videos, the handbook says. more
-----
The (K-Pop) scandal magnifies the proliferation of hidden camera porn in South Korea — an issue which drove 22,000 women to the streets last June in the largest women’s demonstration in the nation’s history. Known as molka, meaning “spycam”, hidden camera porn has become an increasingly visible issue in South Korea, as the distribution of footage from secret, tiny cameras — often depicting women in sexual or intimate circumstances without their consent — has grown in recent years. From 2013 to 2017, police estimate nearly 6,000 cases of spycam porn each year. more
Korea - 1,600 hotel guests were secretly filmed...
...on cameras hidden in wall sockets, with footage live-streamed to paying customers!
Two South Korean men have been arrested
after allegedly installing spy cameras in dozens of hotel rooms,
secretly recording more than 1,600 guests and live-streaming the
footage.
The men are accused
of installing cameras in electrical sockets, hair dryer holders
and digital TV boxes in 30 hotels in ten cities across South Korea, local police said.
They would then broadcast the footage on a website with thousands of members, charging a $44.95 monthly fee. more
Important: Learn how to inspect your hotel room (or any expectation of privacy area) for spy cameras ...and what to do if you find one.
On-line, self-paced, video training for private individuals and business.
Important: Learn how to inspect your hotel room (or any expectation of privacy area) for spy cameras ...and what to do if you find one.
On-line, self-paced, video training for private individuals and business.
Korea - K-pop Sex Scandal Reveals Practice of Sharing Spycam Porn
A sex scandal engulfing South Korea's K-pop industry is drawing attention and criticism to the country's problem with illegal spy cam "porn," says NPR's former Seoul correspondent...
 Earlier this month, police questioned K-pop star Jung Joon-young about allegations he secretly filmed himself having sex with women and then shared the footage in private group chats.
Earlier this month, police questioned K-pop star Jung Joon-young about allegations he secretly filmed himself having sex with women and then shared the footage in private group chats.
"Tiny cameras that can be the size of lipstick containers or lighters are hidden in public places like subway stations, but also in highly private places like dressing rooms and bathrooms," Hu explained.
"The most common kind that's traded online, and shared online, and sometimes profited off of online, is footage of women having sex." more
 Earlier this month, police questioned K-pop star Jung Joon-young about allegations he secretly filmed himself having sex with women and then shared the footage in private group chats.
Earlier this month, police questioned K-pop star Jung Joon-young about allegations he secretly filmed himself having sex with women and then shared the footage in private group chats."Tiny cameras that can be the size of lipstick containers or lighters are hidden in public places like subway stations, but also in highly private places like dressing rooms and bathrooms," Hu explained.
"The most common kind that's traded online, and shared online, and sometimes profited off of online, is footage of women having sex." more
Wednesday, March 20, 2019
Cops Spying on Cops, the Village President & Spycamer's in Crawlspaces
IN - A second lawsuit has been filed against New Carlisle alleging command staff in the police department secretly recorded private conversations... The five plaintiffs claim that Deputy Police Chief Brian Thompson and Chief Calleb Dittmar allegedly secretively “placed, or caused to be placed,” recording devices in the ceilings of non-essential areas of the department. more
-----
IL - Former Hinckley Chief of Police Kimberly S. Everhart has been charged with eavesdropping and official misconduct after Illinois State Police say she illegally recorded a conversation with the village president in 2017. more
-----
GA - A Catoosa County man is facing a handful of privacy invasion charges after he allegedly broke into a Ringgold residence and planted monitoring equipment, police say.
According to the Catoosa County Sheriff’s Office: Samuel David Townsend, 32, of 103 Parkview Drive in Ringgold, was arrested March 7 on charges of first-degree burglary, possession or sale of an eavesdropping device, unlawful eavesdropping, and Peeping Tom.
...resident reported suspicious sounds coming from underneath her home.
The victim said she was getting out of the shower when she heard a sound coming from the house’s master bathroom. The woman claimed she initially thought a mouse was in the home, but that the noise got louder almost like something was being cut...
 ...a white truck parked out on the street in front of the home and that the crawl space at the back of the house was open...
...a white truck parked out on the street in front of the home and that the crawl space at the back of the house was open...
Sheriff Gary Sisk said Townsend did some work at the home in the past, and that he planted a recording device. more
-----
IL - Former Hinckley Chief of Police Kimberly S. Everhart has been charged with eavesdropping and official misconduct after Illinois State Police say she illegally recorded a conversation with the village president in 2017. more
-----
GA - A Catoosa County man is facing a handful of privacy invasion charges after he allegedly broke into a Ringgold residence and planted monitoring equipment, police say.
According to the Catoosa County Sheriff’s Office: Samuel David Townsend, 32, of 103 Parkview Drive in Ringgold, was arrested March 7 on charges of first-degree burglary, possession or sale of an eavesdropping device, unlawful eavesdropping, and Peeping Tom.
...resident reported suspicious sounds coming from underneath her home.
The victim said she was getting out of the shower when she heard a sound coming from the house’s master bathroom. The woman claimed she initially thought a mouse was in the home, but that the noise got louder almost like something was being cut...
 ...a white truck parked out on the street in front of the home and that the crawl space at the back of the house was open...
...a white truck parked out on the street in front of the home and that the crawl space at the back of the house was open... Sheriff Gary Sisk said Townsend did some work at the home in the past, and that he planted a recording device. more
Spybuster Tip # 629 - Watch What You Say at the Drive-Thru
Next time you have a private conversation while in a drive-through, you might want to keep it quiet — as workers in fast food restaurants are able to hear you, even when you can’t hear them.
 Well, as long as they are wearing a headset and you’re parked next to the microphone with your window down, that is.
Well, as long as they are wearing a headset and you’re parked next to the microphone with your window down, that is.
...the revelation on r/LifeProTips: They posted; “If we apologize [sic] and say we’ll be with you in a minute – you’re not on hold, we can hear everything. If you’ve ordered but the drive-thru line won’t let you pull ahead yet – we can hear every single thing you’re saying.
Suggesting that having the ability to eavesdrop isn’t always a good thing, they added: “I wish I could forget some of the stuff I’ve heard.” more
 Well, as long as they are wearing a headset and you’re parked next to the microphone with your window down, that is.
Well, as long as they are wearing a headset and you’re parked next to the microphone with your window down, that is. ...the revelation on r/LifeProTips: They posted; “If we apologize [sic] and say we’ll be with you in a minute – you’re not on hold, we can hear everything. If you’ve ordered but the drive-thru line won’t let you pull ahead yet – we can hear every single thing you’re saying.
Suggesting that having the ability to eavesdrop isn’t always a good thing, they added: “I wish I could forget some of the stuff I’ve heard.” more
Labels:
#eavesdropping,
advice,
employee,
microphone,
privacy,
Tips
Mr. Blobby - UK TV Star & Accidential Voyeur
UK - Mr. Blobby is a big, pink blobby thing covered in yellow dots resembling a dangerous bout of liver cirrhosis. He also happens to be a dearly loved kids’ character on British TV.
 However, he could have some explaining to do to Mrs. Blobby after he was caught perving on a naked woman in a bath on a billboard in the northern British city of Leicester.
However, he could have some explaining to do to Mrs. Blobby after he was caught perving on a naked woman in a bath on a billboard in the northern British city of Leicester.
Thankfully, all is not what it seems and it appears ...
A storm on Friday damaged the existing billboard’s skin – an ad for telco firm BT that showed a woman in a bath watching her laptop – which then revealed the previous ad that featured Mr. Blobby. more
 However, he could have some explaining to do to Mrs. Blobby after he was caught perving on a naked woman in a bath on a billboard in the northern British city of Leicester.
However, he could have some explaining to do to Mrs. Blobby after he was caught perving on a naked woman in a bath on a billboard in the northern British city of Leicester.Thankfully, all is not what it seems and it appears ...
A storm on Friday damaged the existing billboard’s skin – an ad for telco firm BT that showed a woman in a bath watching her laptop – which then revealed the previous ad that featured Mr. Blobby. more
Doctor Charged with Filming Women in Bathroom
We're guessing, "It's okay, I'm a doctor," will not be a valid defense.
NJ - New evidence has emerged in the case of a former Rutgers Robert Wood Johnson Medical School doctor charged with secretly recording women in a bathroom at the city hospital, according to prosecutors.
...after being charged last month in a 160-count indictment with invasion of privacy, computer theft, wiretapping, burglary, official misconduct and impersonation. ...is facing third-degree charges of allegedly photographing or videotaping victims, without their consent or knowledge, while their "intimate parts" were exposed. He’s facing fourth-degree charges in similar instances, except the victims were wearing underwear. ...the FBI is still investigating. more
NJ - New evidence has emerged in the case of a former Rutgers Robert Wood Johnson Medical School doctor charged with secretly recording women in a bathroom at the city hospital, according to prosecutors.
...after being charged last month in a 160-count indictment with invasion of privacy, computer theft, wiretapping, burglary, official misconduct and impersonation. ...is facing third-degree charges of allegedly photographing or videotaping victims, without their consent or knowledge, while their "intimate parts" were exposed. He’s facing fourth-degree charges in similar instances, except the victims were wearing underwear. ...the FBI is still investigating. more
Security Director Alert: Mirai Botnet Targets Corporate Presentation Systems
A new variant of the crushing Mirai botnet, which specifically places enterprises in its crosshairs, has been discovered by security researchers...
Mirai is still a botnet designed to exploit IoT devices, but in its latest iteration it seeks out vulnerable business devices - specifically, wireless presentation systems and the TVs used to present to rooms full of clients, partners and colleagues.
"This new Mirai is a perfect example of why every organisation needs to map their own networks from an external point of view and close off everything that is open and does not need to be," said Jamo Niemela, principal researcher at F-secure. "The types of new devices that Mirai attacks have no business of being visible to the Internet."
The WePresent WiPG-1000 wireless presentation system and the LG Supersign TV were the two devices singled-out by researchers as most vulnerable to the attack. more
In addition to checking for electronic eavesdropping devices and general information security loopholes, make sure your TSCM technicians examine IoT device settings.
 |
| Click to enlarge. |
"This new Mirai is a perfect example of why every organisation needs to map their own networks from an external point of view and close off everything that is open and does not need to be," said Jamo Niemela, principal researcher at F-secure. "The types of new devices that Mirai attacks have no business of being visible to the Internet."
The WePresent WiPG-1000 wireless presentation system and the LG Supersign TV were the two devices singled-out by researchers as most vulnerable to the attack. more
In addition to checking for electronic eavesdropping devices and general information security loopholes, make sure your TSCM technicians examine IoT device settings.
Tuesday, March 19, 2019
Keep Your Number Private – And Still Receive Calls!
An inexpensive and easy service...
 "Keep your real phone number hidden while making calls and sending texts
for work, dating, Craigslist sales, and more thanks to Hushed. You'll
use their simple and secure app to easily make calls on your second
number (you'll even choose the area code) without committing to another
long, expensive phone contract. Customize your voicemail and use Wi-Fi
or data to talk without expensive service charges. It's true
communication anonymity delivered." more
"Keep your real phone number hidden while making calls and sending texts
for work, dating, Craigslist sales, and more thanks to Hushed. You'll
use their simple and secure app to easily make calls on your second
number (you'll even choose the area code) without committing to another
long, expensive phone contract. Customize your voicemail and use Wi-Fi
or data to talk without expensive service charges. It's true
communication anonymity delivered." more
Bonus:
 "Keep your real phone number hidden while making calls and sending texts
for work, dating, Craigslist sales, and more thanks to Hushed. You'll
use their simple and secure app to easily make calls on your second
number (you'll even choose the area code) without committing to another
long, expensive phone contract. Customize your voicemail and use Wi-Fi
or data to talk without expensive service charges. It's true
communication anonymity delivered." more
"Keep your real phone number hidden while making calls and sending texts
for work, dating, Craigslist sales, and more thanks to Hushed. You'll
use their simple and secure app to easily make calls on your second
number (you'll even choose the area code) without committing to another
long, expensive phone contract. Customize your voicemail and use Wi-Fi
or data to talk without expensive service charges. It's true
communication anonymity delivered." moreBonus:
- The Murray Associates Smartphone Security Tips
- How to Block Caller ID
Monday, March 18, 2019
Ten Years of Bugging a Woman's Home Brings... a misconduct hearing?!?!
UK - A serving South Yorkshire police officer will face a misconduct hearing after being accused of bugging a woman’s home to listen in on her private conversations.
PC Christopher Birkett is accused of placing covert listening devices in a woman’s home on ‘various dates’ between March 2007 and August 2017 to listen in on her conversations.
It is alleged that on some of the occasions, PC Birkett was on duty at the time. more
PC Christopher Birkett is accused of placing covert listening devices in a woman’s home on ‘various dates’ between March 2007 and August 2017 to listen in on her conversations.
It is alleged that on some of the occasions, PC Birkett was on duty at the time. more
Facebook - Also Concerned About Their Privacy
Nick Lovrien, the tech behemoth's chief global security officer, said in an interview...
"We work to protect intellectual property in many ways, and that's everything from making sure [employees'] computer screens on airplanes are covered so people don't accidentally share information they're not supposed to, to accidentally leaving things on the printers ... to white boards being cleaned at night," Lovrien said, adding that Facebook has additional systems in place "that identify if people are inappropriately accessing information they shouldn't have."
 That's not just a theoretical risk. In the last six months, two Chinese Apple employees working on the company's secretive self-driving car project have been charged with stealing the iPhone maker's trade secrets...
That's not just a theoretical risk. In the last six months, two Chinese Apple employees working on the company's secretive self-driving car project have been charged with stealing the iPhone maker's trade secrets...
Business Insider has spoken with numerous current and former employees and reviewed internal documents for an in-depth investigation into how Facebook handles its corporate security.
Sources described a hidden world of stalkers, stolen prototypes, state-sponsored espionage concerns, secret armed guards, car-bomb concerns, and more. Today, there are a staggering 6,000 people in Facebook's global security organization, working to safeguard the company's 80,000-strong workforce of employees and contractors around the world. more
"We work to protect intellectual property in many ways, and that's everything from making sure [employees'] computer screens on airplanes are covered so people don't accidentally share information they're not supposed to, to accidentally leaving things on the printers ... to white boards being cleaned at night," Lovrien said, adding that Facebook has additional systems in place "that identify if people are inappropriately accessing information they shouldn't have."
 That's not just a theoretical risk. In the last six months, two Chinese Apple employees working on the company's secretive self-driving car project have been charged with stealing the iPhone maker's trade secrets...
That's not just a theoretical risk. In the last six months, two Chinese Apple employees working on the company's secretive self-driving car project have been charged with stealing the iPhone maker's trade secrets...Business Insider has spoken with numerous current and former employees and reviewed internal documents for an in-depth investigation into how Facebook handles its corporate security.
Sources described a hidden world of stalkers, stolen prototypes, state-sponsored espionage concerns, secret armed guards, car-bomb concerns, and more. Today, there are a staggering 6,000 people in Facebook's global security organization, working to safeguard the company's 80,000-strong workforce of employees and contractors around the world. more
The Case of The Handyman Cam
A Kentucky man accused of installing a video camera in a family’s bathroom is now facing additional felony charges...41-year-old Ryan C. Lloyd was charged with video voyeurism...
Police say a family hired Lloyd to fix a light fixture. A few days later, the family discovered a camera with an SD card had been wired to the light fixture. Police found 87 recordings on the card, including two images of a naked juvenile and images of two partially nude adults. more
Police say a family hired Lloyd to fix a light fixture. A few days later, the family discovered a camera with an SD card had been wired to the light fixture. Police found 87 recordings on the card, including two images of a naked juvenile and images of two partially nude adults. more
Friday, March 15, 2019
FutureWatch: Stingrays May Be Stung by Apple Cell Phone Patent
Apple has filed a patent application on a new method of encryption, which complicates obtaining of confidential information.
The patent describes a technology that will not allow any device to keep track of the IMSI (international mobile subscriber identifier)...
Innovation may interfere with the use of Stingray devices, which act as masts for mobile phones. These devices can track the location of users or even to listen to personal calls. They are also sometimes called IMSI catchers. more
The patent describes a technology that will not allow any device to keep track of the IMSI (international mobile subscriber identifier)...
Innovation may interfere with the use of Stingray devices, which act as masts for mobile phones. These devices can track the location of users or even to listen to personal calls. They are also sometimes called IMSI catchers. more
FutureWatch: Cheaper Infrared Cameras
 A new breakthrough by scientists with the University of Chicago, however, may one day lead to much more cost-effective infrared cameras—which in turn could enable infrared cameras for common consumer electronics like phones, as well as sensors to help autonomous cars see their surroundings more accurately.
A new breakthrough by scientists with the University of Chicago, however, may one day lead to much more cost-effective infrared cameras—which in turn could enable infrared cameras for common consumer electronics like phones, as well as sensors to help autonomous cars see their surroundings more accurately.They tweaked the quantum dots so that they had a formula to detect short-wave infrared and one for mid-wave infrared. Then they laid both together on top of a silicon wafer.
The resulting camera performs extremely well and is much easier to produce. "It's a very simple process," Tang said. "You take a beaker, inject a solution, inject a second solution, wait five to 10 minutes, and you have a new solution that can be easily fabricated into a functional device." more
The New 'Cone of Silence', or The Death of Acoustical Ducting
Boston University researchers, Xin Zhang, a professor at the College of Engineering, and Reza Ghaffarivardavagh, a Ph.D. student in the Department of Mechanical Engineering, released a paper in Physical Review B demonstrating it's possible to silence noise using an open, ringlike structure, created to mathematically perfect specifications, for cutting out sounds while maintaining airflow.
"Today's sound barriers are literally thick heavy walls," says Ghaffarivardavagh. ...they are a clunky approach not well suited to situations where airflow is also critical...
They calculated the dimensions and specifications that the metamaterial would need to have in order to interfere with the transmitted sound waves, preventing sound—but not air—from being radiated through the open structure. The basic premise is that the metamaterial needs to be shaped in such a way that it sends incoming sounds back to where they came from, they say.
As a test case, they decided to create a structure that could silence sound from a loudspeaker. Based on their calculations, they modeled the physical dimensions that would most effectively silence noises... The metamaterial, ringing around the internal perimeter of the pipe's mouth, worked like a mute button. more
"Today's sound barriers are literally thick heavy walls," says Ghaffarivardavagh. ...they are a clunky approach not well suited to situations where airflow is also critical...
They calculated the dimensions and specifications that the metamaterial would need to have in order to interfere with the transmitted sound waves, preventing sound—but not air—from being radiated through the open structure. The basic premise is that the metamaterial needs to be shaped in such a way that it sends incoming sounds back to where they came from, they say.
As a test case, they decided to create a structure that could silence sound from a loudspeaker. Based on their calculations, they modeled the physical dimensions that would most effectively silence noises... The metamaterial, ringing around the internal perimeter of the pipe's mouth, worked like a mute button. more
Corporate Security: Will Your "Secret" Status Hold Up in Court?
via Epstein Becker Green -
Peter A. Steinmeyer
A federal judge in Chicago recently taught a painful lesson to an Illinois employer: even if information is sufficiently sensitive and valuable that it could qualify as a “trade secret,” it won’t unless the owner of the information took adequate steps to protect its secrecy.
In a thorough opinion issued in the case, Abrasic 90 Inc., d/b/a CGW Camel Grinding Wheels, USA v. Weldcote Metals, Inc., Joseph O’Mera and Colleen Cervencik, U.S. District Judge John J. Tharp, Jr. of the Northern District of Illinois explained that “there are two basic elements to the analysis” of whether information qualifies as a “trade secret”:
(1) the information “must have been sufficiently secret to impart economic value because of its relative secrecy” and
(2) the owner “must have made reasonable efforts to maintain the secrecy of the information.” more
Contact a Technical Information Security Consultant if you are unsure about the "reasonable efforts" you should be taking.
A federal judge in Chicago recently taught a painful lesson to an Illinois employer: even if information is sufficiently sensitive and valuable that it could qualify as a “trade secret,” it won’t unless the owner of the information took adequate steps to protect its secrecy.
 |
| This doesn't qualify. |
(1) the information “must have been sufficiently secret to impart economic value because of its relative secrecy” and
(2) the owner “must have made reasonable efforts to maintain the secrecy of the information.” more
Contact a Technical Information Security Consultant if you are unsure about the "reasonable efforts" you should be taking.
Monday, February 25, 2019
FutureWatch: Invisible-Light-Powered Eavesdropping Devices
Wi-Charge uses safe infrared light to deliver power from a distance. Our products provide enough power to charge a phone across a room, to power smart devices and enable new experiences. With Wi-Charge, mobile and IoT devices appear to charge autonomously. New applications open for homes, offices, factories and public spaces.
Battery-powered devices are portable, but battery capacity limits functionality and the need to replace batteries degrades the user experience. Moving wired devices, routing or hiding the power cords is a pain. Wi-Charge delivers 100x the power budget of battery solutions. With Wi-Charge, you can have the convenience of wire-free portability with a power budget approaching to a wired solution. more
Lots of good uses, and possibly some evil ones.
Thanks to another Canadian Blue Blaze Irregular for spotting this one!
Battery-powered devices are portable, but battery capacity limits functionality and the need to replace batteries degrades the user experience. Moving wired devices, routing or hiding the power cords is a pain. Wi-Charge delivers 100x the power budget of battery solutions. With Wi-Charge, you can have the convenience of wire-free portability with a power budget approaching to a wired solution. more
Lots of good uses, and possibly some evil ones.
Thanks to another Canadian Blue Blaze Irregular for spotting this one!
Electronic Footprint Army Boots Discovered
 Hamas-run security forces at the Kerem Shalom crossing in the Gaza Strip have seized a shipment of army boots outfitted with tracking devices, Turkey’s state-run news agency Anadolu reported on Saturday, citing a security source in the coastal enclave.
Hamas-run security forces at the Kerem Shalom crossing in the Gaza Strip have seized a shipment of army boots outfitted with tracking devices, Turkey’s state-run news agency Anadolu reported on Saturday, citing a security source in the coastal enclave.Hamas security forces were carrying out “a precise inspection of the tracking devices in order to… understand how they work,” the security source said. more
Looks like the same technology as shoplifting tags and card-keys. Clever.
Thanks to our Canadian Blue Blaze irregular for spotting this one!
Friday, February 8, 2019
Book - JUDGEMENT by Joe Finder - Fast-Paced Thriller with Technical Surveillance Overtones
 |
| Just Released |
Excerpt...
"It was nothing more than a one-night stand. Juliana Brody, a judge in the Superior Court of Massachusetts, is rumored to be in consideration for the federal circuit, maybe someday the highest court in the land.
At a conference in a Chicago hotel, she meets a gentle, vulnerable man and has an unforgettable night with him—something she’d never done before. They part with an explicit understanding that this must never happen again.
But back home in Boston, Juliana realizes that this was no random encounter. The man from Chicago proves to have an integral role in a case she's presiding over—a sex-discrimination case that's received national attention. Juliana discovers that she's been entrapped, her night of infidelity captured on video.
 Strings are being pulled in high places, a terrifying unfolding conspiracy that will turn her life upside down. But soon it becomes clear that personal humiliation, even the possible destruction of her career, are the least of her concerns, as her own life and the lives of her family are put in mortal jeopardy.
Strings are being pulled in high places, a terrifying unfolding conspiracy that will turn her life upside down. But soon it becomes clear that personal humiliation, even the possible destruction of her career, are the least of her concerns, as her own life and the lives of her family are put in mortal jeopardy. In the end, turning the tables on her adversaries will require her to be as ruthless as they are..."
Inside Information: Several Technical Surveillance Countermeasures practitioners (including myself) were consulted for plot twists and technical realism. New York Times bestselling author Joseph Finder does this kind of homework on all his novels. ~Kevin
more
Thursday, February 7, 2019
Ultrasonic Microphone Jammers — Do They Really Work?
It’s a question I get asked occasionally when one of our clients sees one of these devices being advertised on the internet.
 Who can blame them for asking? The ads claim they can stop microphones from working properly. Instant privacy from electronic eavesdroppers, and anyone who is attempting to record your conversations.
Who can blame them for asking? The ads claim they can stop microphones from working properly. Instant privacy from electronic eavesdroppers, and anyone who is attempting to record your conversations.
Finally, Kryptonite for microphones!?!? Wow, how does that work?
The ultrasonic microphone jammer explanation is really simple... more
 Who can blame them for asking? The ads claim they can stop microphones from working properly. Instant privacy from electronic eavesdroppers, and anyone who is attempting to record your conversations.
Who can blame them for asking? The ads claim they can stop microphones from working properly. Instant privacy from electronic eavesdroppers, and anyone who is attempting to record your conversations.Finally, Kryptonite for microphones!?!? Wow, how does that work?
The ultrasonic microphone jammer explanation is really simple... more
FutureWatch: Smartphone Comes with Optical Spy Pen
 |
| Click to enlarge. |
Abstract
The electric pen device includes an optical system including a lens and an image sensor configured to convert an image signal of light that has passed through the optical system to an electrical signal. The electric pen device includes a control board configured to interact with an electronic device and a communication module configured to communicate by wire or wirelessly with the electronic device, so that an image or a picture taken by a camera is confirmed and an optical zoom is controlled from the external electronic device. more
FutureWatch spy implications: Phone may be concealed in the pocket, backpack, or nearby desk drawer. Take high quality photos by aiming the top of the pen, pressing a button, and automatically transmitting the photo back to the phone. Pretty covert. No word about it transmitting audio, yet. Leaving phones outside of the conference room won't be enough. You'll have to check the pens, too.
Need a spy pen camera you can actually buy today, or worry about being used to steal your secrets? Check here. ~Kevin
Thanks to our sharp-eyed Blue Blaze Irregular in the shadows of Pennsylvania for this.
Smart Light Bulbs May Not Be a Bright Idea
Your discarded smart lightbulbs reveal your wifi passwords, because they are stored in the clear.
Not to mention, someone replacing your bulb and getting the password that way.
Yes, I know, the spy might not program the replacement bulb to operate like the old one. Dead give-a-way, right? My bet is that you'll think the bulb just forgot it's settings, or not notice at all.
This hack was publicized here, and originally researched here, if you want to know more.
Thanks to our Blue Blaze Irregular from the Jersey shore for this one.
Not to mention, someone replacing your bulb and getting the password that way.
Yes, I know, the spy might not program the replacement bulb to operate like the old one. Dead give-a-way, right? My bet is that you'll think the bulb just forgot it's settings, or not notice at all.
This hack was publicized here, and originally researched here, if you want to know more.
Thanks to our Blue Blaze Irregular from the Jersey shore for this one.
Wednesday, February 6, 2019
Business Espionage: The Case of the Broken Unbreakable Glass
In what sounds like a half-baked movie script about corporate espionage,
an FBI sting conducted in collaboration with a specialized glass maker
(and watched from a gelato stand by a reporter from Bloomberg) led investigators to a meeting at a burger joint in Vegas during CES... Akhan Semiconductor, reached out to potential customers regarding its
recently developed Miraj Diamond Glass, a new take on the protective
screens used in devices like smartphones that Akhan claims is six times
stronger and ten times more scratch-resistant than Corning Gorilla
Glass. Among Akhan’s potential clients was Huawei... more more sing-a-long
This Week in Technical Surveillance
Ukraine - Head of the election headquarters of the presidential candidate of Ukraine, leader of the Civil Position Party Anatoliy Hrytsenko, independent deputy, Viktor Chumak, has said that wiretapping devices were found in their headquarters, and therefore, called on other candidates to be vigilant. more
Australia - Australia is to establish a new sweeping anti-corruption regime which
will be overseen by a national watchdog which will tackle both cheating
and match-fixing in the Australian sports sector... It would also have the power to conduct electronic surveillance
of coaches, sports officials, and athletes and look for signs of suspected
match-fixing... more
...and one for the birds...
Israel - The Israel Police admitted on Tuesday that it
eavesdropped on journalists’ telephone conversations with suspects,
despite these conversations being protected by journalistic privilege. more
U.S. - A head custodian for the city's public school
district was arrested after a female co-worker found a hidden camera
that had recorded her using a restroom... Francisco
Javier Lopez-Martinez, 59, was arrested...after an overnight police search... Lopez-Martinez was found hiding...police said he threatened suicide while holding a
handgun...the gun was determined to be an
air-soft weapon... A
day earlier, a woman reported to police that she had discovered the
camera while using a bathroom...she found footage of her and also a clip of,
Lopez-Martinez, installing the camera. more
...and one for the birds...
New Zealand - In a technology that's been heralded as a breakthrough in conservation, a
remote recording device is 'eavesdropping' on one of the rarest birds
in New Zealand to monitor how they're adjusting after being released
back into the wild. more
Facilities Manager Alert: Your Smart Building May Start Doing Dumb Things
Researchers at enterprise security vendor ForeScout have warned that malware specifically targeting smart buildings is an inevitable next step given the rapidly expanding attack surface that building automation systems expose.
The operational technology researchers at ForeScout should know: they created proof-of-concept malware that revealed smart building vulnerabilities every business should be concerned about.
...just yesterday, Tenable Research revealed it had discovered several zero-day vulnerabilities in a premises access control system used by Fortune 500 companies. Among the many attack scenarios these vulnerabilities could facilitate was 'unfettered access to the badge system database' which in turn meant an ability to create fraudulent access badges and disable building locks. more
The operational technology researchers at ForeScout should know: they created proof-of-concept malware that revealed smart building vulnerabilities every business should be concerned about.
...just yesterday, Tenable Research revealed it had discovered several zero-day vulnerabilities in a premises access control system used by Fortune 500 companies. Among the many attack scenarios these vulnerabilities could facilitate was 'unfettered access to the badge system database' which in turn meant an ability to create fraudulent access badges and disable building locks. more
Spybusters Tip #847: Stop Car Theft via Key Fob Signal Intercept
By simply wrapping your key FOB in aluminum foil you can prevent a thief
from intercepting the signal.
If you park your car outside at home then you might consider using a foil-lined container or placing your keys in a coffee can.
I’m going to start wrapping mine in aluminum foil when I travel and stay in a hotel. If you doubt that this issue is a serious threat then watch How Thieves Unlock A Car. more
A big thank you to our Blue Blaze Irregular ensconced in Illinois for alerting us to this tip. ~Kevin
If you park your car outside at home then you might consider using a foil-lined container or placing your keys in a coffee can.
I’m going to start wrapping mine in aluminum foil when I travel and stay in a hotel. If you doubt that this issue is a serious threat then watch How Thieves Unlock A Car. more
A big thank you to our Blue Blaze Irregular ensconced in Illinois for alerting us to this tip. ~Kevin
Sunday, February 3, 2019
Hackers Now Banking on Two-Factor Authentication for Profit
Sophisticated hackers have long exploited flaws in SS7, a protocol used by telecom companies to coordinate how they route texts and calls around the world. Those who exploit SS7 can potentially track phones across the other side of the planet, and intercept text messages and phone calls without hacking the phone itself.
This activity was typically only within reach of intelligence agencies or surveillance contractors, but now Motherboard has confirmed that this capability is much more widely available in the hands of financially-driven cybercriminal groups, who are using it to empty bank accounts. So-called SS7 attacks against banks are, although still relatively rare, much more prevalent than previously reported. Motherboard has identified a specific bank—the UK's Metro Bank—that fell victim to such an attack...
One source familiar with SS7 attacks across banks said the exploitation has targeted banks globally, but that American banks seem to be less impacted. more
Reader comment: "Please note the Motherboard reporter carefully differentiates between "sophisticated hackers" and "financially-driven cybercriminal groups". I hope you'll consider being equally judicious in your own reporting and online comments."
This activity was typically only within reach of intelligence agencies or surveillance contractors, but now Motherboard has confirmed that this capability is much more widely available in the hands of financially-driven cybercriminal groups, who are using it to empty bank accounts. So-called SS7 attacks against banks are, although still relatively rare, much more prevalent than previously reported. Motherboard has identified a specific bank—the UK's Metro Bank—that fell victim to such an attack...
One source familiar with SS7 attacks across banks said the exploitation has targeted banks globally, but that American banks seem to be less impacted. more
Reader comment: "Please note the Motherboard reporter carefully differentiates between "sophisticated hackers" and "financially-driven cybercriminal groups". I hope you'll consider being equally judicious in your own reporting and online comments."
Friday, February 1, 2019
Book Review Request: Technical Surveillance Counter-Measures a Complete Guide
If any TSCM'er out there buys this book. Please send me a review.
Thank you, Kevin
Evil Child Watch Spies
In late 2017, the Norwegian Consumer Council published its audit of kids' smart-watches, reporting that the leading brands allowed strangers to follow your kids around and listen in on their conversations; a year later, Pen Test Partners followed up to see if anything had changed (it hadn't).
Now, a year and a half later, Pen Test Partners have done another security audit of kids' smart watches and you'll never guess what they found! Kids' smart-watches are still a dumpster-fire: anyone can access the entire database of kids' data, including "real time child location, name, parents details etc," and since most leading brands use the same back-end from Gator, virtually every kid's smart-watch is vulnerable. more
Smartphone Security Tips
2/4/19 UPDATE: European Commission orders mass recall of creepy, leaky child-tracking smartwatch. more
Now, a year and a half later, Pen Test Partners have done another security audit of kids' smart watches and you'll never guess what they found! Kids' smart-watches are still a dumpster-fire: anyone can access the entire database of kids' data, including "real time child location, name, parents details etc," and since most leading brands use the same back-end from Gator, virtually every kid's smart-watch is vulnerable. more
Smartphone Security Tips
2/4/19 UPDATE: European Commission orders mass recall of creepy, leaky child-tracking smartwatch. more
Thursday, January 31, 2019
Business Espionage – A Cunning Protection Plan to Protect us and U.S.
We are bombarded with news stories and court trials tornado-ing around Chinese spies. They’re everywhere. Collecting everything. They are such a fixture in and around our hapless businesses that it only seems right to offer them health insurance, a pension plan, cookies and milk.
But wait. Let’s think this through.
Aren’t these the folks who had the secrets of silk stolen from them by Justinian I? Humm, could this be why great neckties are made in Italy, not China? Even their espionage death penalty law couldn’t protect them. Boom! Business espionage devastated their economy.
 I also recall a dude from the UK, Robert Fortune, sort of an early 007. He was sent to steal the secrets of tea production from… Have you guessed yet? China! That caper is now know as The Great British Tea Heist. Boom! Business espionage devastated their economy yet again.
I also recall a dude from the UK, Robert Fortune, sort of an early 007. He was sent to steal the secrets of tea production from… Have you guessed yet? China! That caper is now know as The Great British Tea Heist. Boom! Business espionage devastated their economy yet again.
Oh, and what about the Chinese secret of making porcelain? A French Catholic priest stole that one. BOOM!! I could go on and on. Gunpowder, paper, etc. Bing! Bam! BOOM!
Feeling sorry for China yet? Don’t. They are making up for it, right now. The disk drive that just started whirring in your computer… it might be them.
And, don’t think this is just some cosmic Yin and Yang, great mandella, or as we say here in New Jersey, “What goes around, comes around.” No, that explanation is too simplistic, not to mention fatalistic. There is more to this industrial espionage business. The circle is bigger. This is history repeating itself, over and over and over, but I think I have the solution... more
But wait. Let’s think this through.
Aren’t these the folks who had the secrets of silk stolen from them by Justinian I? Humm, could this be why great neckties are made in Italy, not China? Even their espionage death penalty law couldn’t protect them. Boom! Business espionage devastated their economy.
 I also recall a dude from the UK, Robert Fortune, sort of an early 007. He was sent to steal the secrets of tea production from… Have you guessed yet? China! That caper is now know as The Great British Tea Heist. Boom! Business espionage devastated their economy yet again.
I also recall a dude from the UK, Robert Fortune, sort of an early 007. He was sent to steal the secrets of tea production from… Have you guessed yet? China! That caper is now know as The Great British Tea Heist. Boom! Business espionage devastated their economy yet again.Oh, and what about the Chinese secret of making porcelain? A French Catholic priest stole that one. BOOM!! I could go on and on. Gunpowder, paper, etc. Bing! Bam! BOOM!
Feeling sorry for China yet? Don’t. They are making up for it, right now. The disk drive that just started whirring in your computer… it might be them.
And, don’t think this is just some cosmic Yin and Yang, great mandella, or as we say here in New Jersey, “What goes around, comes around.” No, that explanation is too simplistic, not to mention fatalistic. There is more to this industrial espionage business. The circle is bigger. This is history repeating itself, over and over and over, but I think I have the solution... more
Second Apple Pickin' Spy Caught in Last 6 Months
The United States FBI this week accused a Chinese citizen working for
Apple of attempting to steal trade secrets that are related to the
company's autonomous vehicle program, reports NBC Bay Area.
 Apple launched an investigation into the employee, Jizhong Chen, when
another employee spotted him taking photographs "in a sensitive work
space."
Apple launched an investigation into the employee, Jizhong Chen, when
another employee spotted him taking photographs "in a sensitive work
space."
Apple Global Security employees searched his personal computer and found "thousands" of Apple files, including manuals, schematics, photographs, and diagrams.
Chen had recently applied for a position with a China-based autonomous vehicle company that is a direct Apple competitor. Chen was arrested a day before he was set to fly to China.
 Apple launched an investigation into the employee, Jizhong Chen, when
another employee spotted him taking photographs "in a sensitive work
space."
Apple launched an investigation into the employee, Jizhong Chen, when
another employee spotted him taking photographs "in a sensitive work
space." Apple Global Security employees searched his personal computer and found "thousands" of Apple files, including manuals, schematics, photographs, and diagrams.
Chen had recently applied for a position with a China-based autonomous vehicle company that is a direct Apple competitor. Chen was arrested a day before he was set to fly to China.
Apple in a statement said that it
is working with the authorities."Apple takes
confidentiality and the protection of our IP very seriously," the
company said in a statement Tuesday. "We are working with authorities on
this matter and are referring all questions to the FBI."
This is not the first time an employee has been caught trying to steal secrets from Apple's car team. Back in July, the FBI charged former Apple employee Xiaolang Zhang with theft of trade secrets for stealing hardware and software that included prototypes and detailed prototype requirements. more
This is not the first time an employee has been caught trying to steal secrets from Apple's car team. Back in July, the FBI charged former Apple employee Xiaolang Zhang with theft of trade secrets for stealing hardware and software that included prototypes and detailed prototype requirements. more
Wednesday, January 30, 2019
Tired of Smartphone Security Vulnerabilities? Go Dumb!
 Punkt - The MP02 is significantly more complex than the MP01, so we have teamed up with BlackBerry to keep it secure. BlackBerry adds enhanced security to the device at the point of manufacture, which means the MP02 is hardened and highly secure. With BlackBerry’s integrated software components, the MP02 will be built with security from the start so you can trust that your data will be safe. more
Punkt - The MP02 is significantly more complex than the MP01, so we have teamed up with BlackBerry to keep it secure. BlackBerry adds enhanced security to the device at the point of manufacture, which means the MP02 is hardened and highly secure. With BlackBerry’s integrated software components, the MP02 will be built with security from the start so you can trust that your data will be safe. more The new Nokia 3310 2.4” polarized and curved screen
window makes for better readability in sunlight. Remember when you could leave the house without a charger? Well, with the Nokia 3310, you can. It comes with a long-lasting battery, so you can talk all day, or leave the phone on standby for up to a month. When needed, a Micro-USB port makes charging simple. more
The new Nokia 3310 2.4” polarized and curved screen
window makes for better readability in sunlight. Remember when you could leave the house without a charger? Well, with the Nokia 3310, you can. It comes with a long-lasting battery, so you can talk all day, or leave the phone on standby for up to a month. When needed, a Micro-USB port makes charging simple. more The Light Phone 2 is a 4G LTE phone with a beautiful black &
white matte display. It's a more reliable, durable, and practical phone
than its predecessor. It brings a few essential tools to the Light
Phone, like messaging, an alarm clock, or a ride home, so you can leave
behind your smartphone more often... or for good. We call this
experience 'going light'. more (An indiegogo project at the moment.)
The Light Phone 2 is a 4G LTE phone with a beautiful black &
white matte display. It's a more reliable, durable, and practical phone
than its predecessor. It brings a few essential tools to the Light
Phone, like messaging, an alarm clock, or a ride home, so you can leave
behind your smartphone more often... or for good. We call this
experience 'going light'. more (An indiegogo project at the moment.) Another dumb phone, the Alba Flip fits right between the borderline-brain-dead dumbness of the Light Phone and the smarter-than-you’d-think trickery of the Nokia remakes. Plus, it's a flip phone, which you've got to love. The Alba Flip is not designed to be a basic phone. Alba are a brand designed for those who struggle with conventional mobile phones, either through technophobia or because of visual impairments. more (Warning: 2G only which is becoming harder to rely upon as it is phasing out. In the U.S. that means T-Mobile 2G.)

And, the dumbest one I've ever used... The BM70 is the smallest phone which supports 4G network. With built-in Micro SIM card slot, it can store 250 contact numbers. Not only a mini cell phone, also a Bluetooth earphone more (Only $12.99, and yes it really works.) ~Kevin
If you don't go dumb, go smart, and smarter.
Shred Bin Security – Yours Stinks – Fix it for Free
Shred Bin Security — How to upgrade it... probably for free!
If you have a sizable contract with a shredding company, keep reading.
The Shred Bin Security Conundrum
Your organization realizes they need help getting rid of their wastepaper. Some of it can be recycled. Easy. There are plenty of recycling companies around. Some of it, however, contains sensitive information that must be destroyed.
So, you contact your local "I-Rip-A-Part" shredding company.
You are offered your choice of two shred bin styles, if you are lucky. The elegant particle board beige box, or the converted garbage can.
Both scream security joke. But hey, they only gave you two choices. So, you take what "I-Rip-A-Part" gives you. After all, it's their business. They know best.
Your employees may not laugh out loud, but they get the message. Management either doesn't know much about shred bin security, or they only care enough to make it look like they are doing their due diligence. The result...
Pretty soon these start popping up.
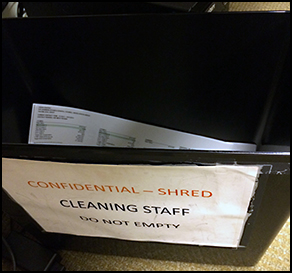
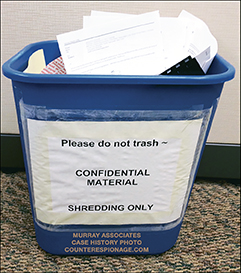
Who's laughing now?
Just the office snoops, competitive intelligence professionals, activists, news media, hackers, etc.
Let me provide some background before providing a workable solution. The crummy shred bin issue is a problem for most U.S. based organizations.
The problem has two roots:
Attacks include: unscrewing the cabinet, picking the cheap lock, sticking a $8.00 flexible grabber through the slot, bending the plastic lid back, or pulling the inner liner bag through the slot... more
If you have a sizable contract with a shredding company, keep reading.
The Shred Bin Security Conundrum
Your organization realizes they need help getting rid of their wastepaper. Some of it can be recycled. Easy. There are plenty of recycling companies around. Some of it, however, contains sensitive information that must be destroyed.
So, you contact your local "I-Rip-A-Part" shredding company.
You are offered your choice of two shred bin styles, if you are lucky. The elegant particle board beige box, or the converted garbage can.
Both scream security joke. But hey, they only gave you two choices. So, you take what "I-Rip-A-Part" gives you. After all, it's their business. They know best.
Your employees may not laugh out loud, but they get the message. Management either doesn't know much about shred bin security, or they only care enough to make it look like they are doing their due diligence. The result...
Pretty soon these start popping up.
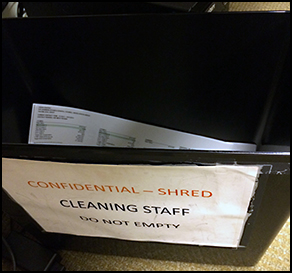
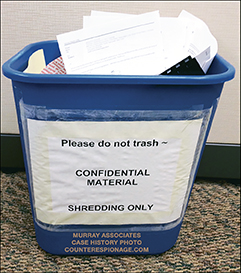
Who's laughing now?
Just the office snoops, competitive intelligence professionals, activists, news media, hackers, etc.
Let me provide some background before providing a workable solution. The crummy shred bin issue is a problem for most U.S. based organizations.
The problem has two roots:
- A lack of understanding about information security on the part of the confidential information custodians.
- Shredding companies preying on this ignorance to maximize their profits. (Number one allows number two.)
Attacks include: unscrewing the cabinet, picking the cheap lock, sticking a $8.00 flexible grabber through the slot, bending the plastic lid back, or pulling the inner liner bag through the slot... more
Inside Information: Email Sales Pitches Some Spies Receive
Only the names have been changed to protect the reticent.
Intercept and capture any phone ANYWHERE in the world... Remotely!
 Are your clients looking for a powerful solution to capture all app messages?
Are your clients looking for a powerful solution to capture all app messages?
Our new monitoring technology for deployment on cellphones is now available.
This advanced method of interception does not require any infrastructure or tactical equipment to gain access to a target’s communication path.
The latest model, Octo+2, can target up to 10 phones at any one time and convert their microphones to a listening post for worldwide audio and video monitoring.
It’s now time to turn on the microphone on your target’s phone so you can listen from any where in the world!
.... Available to authorized agencies only.
Intercept and capture any phone ANYWHERE in the world... Remotely!
 Are your clients looking for a powerful solution to capture all app messages?
Are your clients looking for a powerful solution to capture all app messages?Our new monitoring technology for deployment on cellphones is now available.
- Penetrate cellular defenses
- Generate effective access to Target devices
- Perform interception of their data communications
- Operate in 'new' locations, without requiring any integration
- Extract data from phones without any user interaction required
This advanced method of interception does not require any infrastructure or tactical equipment to gain access to a target’s communication path.
The latest model, Octo+2, can target up to 10 phones at any one time and convert their microphones to a listening post for worldwide audio and video monitoring.
It’s now time to turn on the microphone on your target’s phone so you can listen from any where in the world!
.... Available to authorized agencies only.
Tuesday, January 29, 2019
The Case of the Bumbling Spy
Just the interesting bits...
The case of the bumbling spy is the latest episode involving undercover agents, working for private intelligence firms or other clients, who adopt false identities to dig up compromising information about or elicit embarrassing statements from their targets...
The phenomenon of private spies drew widespread attention in 2017, when Black Cube, an Israeli private intelligence firm, was found to have used undercover agents to approach women who had accused Harvey Weinstein, the Hollywood producer, of sexual misconduct...
At their lunch meeting, he read questions from cue cards of three colors that seemed to be organized by topic, explaining that at his age he needed them to keep the details straight. He held the cards in one hand, while in the other he held and awkwardly pointed a pen that appeared to contain a video recorder, Mr. Scott-Railton said. (John Scott-Railton, a senior researcher at Citizen Lab
In a phone conversation, he had told Mr. Scott-Railton that he had a son about his age. When they met, he said the child was a daughter. more
The point is obvious. Nine out of ten private investigators did not graduate in the top 10% of their class. However, there are plenty out their who did, and they can pretext you and bug your office quicker than a magician can make a coin disappear.
The case of the bumbling spy is the latest episode involving undercover agents, working for private intelligence firms or other clients, who adopt false identities to dig up compromising information about or elicit embarrassing statements from their targets...
The phenomenon of private spies drew widespread attention in 2017, when Black Cube, an Israeli private intelligence firm, was found to have used undercover agents to approach women who had accused Harvey Weinstein, the Hollywood producer, of sexual misconduct...
At their lunch meeting, he read questions from cue cards of three colors that seemed to be organized by topic, explaining that at his age he needed them to keep the details straight. He held the cards in one hand, while in the other he held and awkwardly pointed a pen that appeared to contain a video recorder, Mr. Scott-Railton said. (John Scott-Railton, a senior researcher at Citizen Lab
In a phone conversation, he had told Mr. Scott-Railton that he had a son about his age. When they met, he said the child was a daughter. more
The point is obvious. Nine out of ten private investigators did not graduate in the top 10% of their class. However, there are plenty out their who did, and they can pretext you and bug your office quicker than a magician can make a coin disappear.
Labels:
#espionage,
#spycam,
business,
cautionary tale,
PI,
scam
FaceTime Bug Lets Callers Hear You Before You Answer
Users have discovered a bug in Apple's FaceTime video-calling application that allows you to hear audio from a person you're calling before they accept the call—a critical bug that could potentially be used as a tool by malicious users to invade the privacy of others.
Apple: "We're aware of this issue, and we have identified a fix that will be released in a software update later this week." An hour or two after this post went live, Apple disabled Group FaceTime to mitigate the bug.
The bug requires you to perform a few actions while the phone is ringing, so if the person on the other end picks up quickly, they might not be affected. Knowledge of how to use the bug is already widespread.
The steps include:
Updates: What we have also found is that if the person presses the Power button from the Lock screen, their video is also sent to the caller — unbeknownst to them. In this situation, the receiver can now hear your own audio, but they do not know they are transmitting their audio and video back to you. From their perspective, all they can see is accept and decline. (Another update: It seems there are other ways of triggering the video feed eavesdrop too.) more
Temporary fix. General smartphone security tips.
Apple: "We're aware of this issue, and we have identified a fix that will be released in a software update later this week." An hour or two after this post went live, Apple disabled Group FaceTime to mitigate the bug.
The bug requires you to perform a few actions while the phone is ringing, so if the person on the other end picks up quickly, they might not be affected. Knowledge of how to use the bug is already widespread.
The steps include:
- Tap on a contact on your iPhone to start a FaceTime call with them.
- Swipe up and tap "Add Person."
- Instead of adding a new person, enter your own number and add yourself as another participant in the Group FaceTime call. more
Updates: What we have also found is that if the person presses the Power button from the Lock screen, their video is also sent to the caller — unbeknownst to them. In this situation, the receiver can now hear your own audio, but they do not know they are transmitting their audio and video back to you. From their perspective, all they can see is accept and decline. (Another update: It seems there are other ways of triggering the video feed eavesdrop too.) more
Temporary fix. General smartphone security tips.
Friday, January 25, 2019
Hackers Access Family Security Cameras - Then Yell and Curse
WA - If you have security cameras connected to the internet inside your home, you’re going to want to play close attention to this story. A local family says someone hacked their account and watched them for weeks inside their home; even yelling and cursing at their children...
The couple says things got really creepy this week, while Abby and the children sat here in the living room. She says could hear multiple male voices. At first, she thought it was Conrado just checking in via the security cameras.
“And then they started cussing...
Abby wanted proof. “I grabbed a chair and I was doing this, but my face was back here and my hand was right here because I didn’t want to look at them. They were like stop recording us! What the ‘F’ are you doing?...
Abby and Conrado called Auburn Police, who confirm they are investigating. more
The couple says things got really creepy this week, while Abby and the children sat here in the living room. She says could hear multiple male voices. At first, she thought it was Conrado just checking in via the security cameras.
“And then they started cussing...
Abby wanted proof. “I grabbed a chair and I was doing this, but my face was back here and my hand was right here because I didn’t want to look at them. They were like stop recording us! What the ‘F’ are you doing?...
Abby and Conrado called Auburn Police, who confirm they are investigating. more
Eyeglasses and Earbuds for Real Spies
Misumi Electronics Corp. is a prestigious name in the fields of Spy applications, Surveillance system, Industrial inspection, and Medical application. They specialize in making modules and finished products, including camera modules, transmitters, UVC, USB capture cards and grabbers, and accept customized camera request as well.
The example below shows off the high-resolution of their cameras, including the ability to read computer screens and instantly transmit the video elsewhere. A spy wearing these eyeglasses and earbuds can see in three directions at once, in high-definition, without anyone knowing!
Their tiny, high-quality, HD video cameras have been mass produced for years. Should you come across one, keep searching. There is likely more to find. more
The example below shows off the high-resolution of their cameras, including the ability to read computer screens and instantly transmit the video elsewhere. A spy wearing these eyeglasses and earbuds can see in three directions at once, in high-definition, without anyone knowing!
Their tiny, high-quality, HD video cameras have been mass produced for years. Should you come across one, keep searching. There is likely more to find. more
 |
| Click to enlarge. |
Cybercriminals Home in on Ultra-High Net Worth Individuals
Research shows that better corporate security has resulted in some hackers shifting their sights to the estates and businesses of wealthy families.
Threat intelligence experts and research groups have seen a shift of cybercriminals increasingly targeting ultra-high net worth (UHNW) individuals and their family businesses...
More than half the attacks were viewed as malicious. And, nearly one-third came from an inside threat, such as an employee intentionally leaking confidential information. more
Congratulations to the corporations who have instituted better information security practices. Their elevated security includes periodic checks for electronic surveillance, or Technical Surveillance Countermeasures (TSCM).
These checks are absolutely necessary at family compounds and home offices. There, guests, staff, and tradespeople have great opportunities to plant audio, video and data electronic surveillance devices.
Threat intelligence experts and research groups have seen a shift of cybercriminals increasingly targeting ultra-high net worth (UHNW) individuals and their family businesses...
More than half the attacks were viewed as malicious. And, nearly one-third came from an inside threat, such as an employee intentionally leaking confidential information. more
Congratulations to the corporations who have instituted better information security practices. Their elevated security includes periodic checks for electronic surveillance, or Technical Surveillance Countermeasures (TSCM).
These checks are absolutely necessary at family compounds and home offices. There, guests, staff, and tradespeople have great opportunities to plant audio, video and data electronic surveillance devices.
Subscribe to:
Comments (Atom)














