An incredible archive of rare vintage spy cameras that would rival James Bond's own collection has emerged for sale for £400,000.
Among the rarities is one of only two existing examples of the Lucky Strike Spy Camera developed for the US Signal Corps between 1949 and 1950. The camera, made by the Mast Development Corp, was built to fit inside the outer wrapper from a packet of Lucky Strike cigarettes. Despite its size it was capable of taking 18 x 16mm still photographs with varying shutter speeds, but ultimately it was rejected. It is worth around £43,000. more
Thursday, November 26, 2015
Microsoft Makes Windows 10 Automatic Spying Worse - Update
When Windows 10 was released, many people were up in arms over the operating system’s ability to constantly track how users were interacting with it and would send that information back to Microsoft.
With the first major update for Windows 10 that came out earlier this month, Microsoft has seemingly removed Diagnostics Tracking Service, also known as DiagTrack, which was responsible for the tracking. But it turns out the company has just renamed the service. more
Those who don’t want Windows 10 to constantly send their data back to Microsoft, fear not. There’s a way to disable the service. Forbes has released instructions on how to do so:
With the first major update for Windows 10 that came out earlier this month, Microsoft has seemingly removed Diagnostics Tracking Service, also known as DiagTrack, which was responsible for the tracking. But it turns out the company has just renamed the service. more
Those who don’t want Windows 10 to constantly send their data back to Microsoft, fear not. There’s a way to disable the service. Forbes has released instructions on how to do so:
- Hold down the Windows key and tap the R key
- In the box that opens type ‘services.msc’ and press the Enter key
- In the ‘Services (Local)’ section locate ‘Connected User Experiences and Telemetry’ and double-click it
- In the ‘Service status’ section click ‘Stop’
- Under the ‘Startup type’ drop down menu select ‘Disabled’ and then confirm this and close the window by clicking ‘OK’
Privacy Journal's "Compilation of State and Federal Privacy Laws" - Updated
The Compilation of State and Federal Privacy Laws book
cites and describes more than 600 state and federal laws affecting the confidentiality of personal information and electronic surveillance.
The laws are listed by state, grouped in categories like medical, credit, financial, security breaches, tracking technologies, employment, government, school records, Social Security numbers, marketing, telephone privacy and many more. Canadian laws too.
The 2015 Supplement to Privacy Journal's "Compilation of State and Federal Privacy Laws" (2013) has just been published, adding 20 more laws enacted by states in the past 12 months.
cites and describes more than 600 state and federal laws affecting the confidentiality of personal information and electronic surveillance.
The laws are listed by state, grouped in categories like medical, credit, financial, security breaches, tracking technologies, employment, government, school records, Social Security numbers, marketing, telephone privacy and many more. Canadian laws too.
The 2015 Supplement to Privacy Journal's "Compilation of State and Federal Privacy Laws" (2013) has just been published, adding 20 more laws enacted by states in the past 12 months.
Wednesday, November 25, 2015
How Browser Extensions Steal Logins & Browsing Habits; Conduct Corporate Espionage
via boingboing.com
Seemingly harmless browser extensions that generate emojis, enlarge thumbnails, help you debug Javascript errors and other common utilities routinely run secret background processes that collect and retransmit your login credentials, private URLs that grant access to sensitive files, corporate secrets, full PDFs and other personally identifying, potentially compromising data.
Many extensions conduct surveillance without any notification at all, but some do legal backflips to cover up their activities -- characterizing your installation of the extension as explicit permission to spy; pretending that URLs are by nature anonymous and so on. The data is aggregated and sold to unnamed third parties, reputedly for $0.04/user/month. Many of the spying extensions have more than a million users. One of the extensions identified as conducting secret spying advertises itself as a privacy-enhancing tool (!).
Detectify Labs have posted a technical explanation of how Chrome extensions conduct surveillance, and note near the end of their analysis that Firefox extensions are just as prone to spying. more
Seemingly harmless browser extensions that generate emojis, enlarge thumbnails, help you debug Javascript errors and other common utilities routinely run secret background processes that collect and retransmit your login credentials, private URLs that grant access to sensitive files, corporate secrets, full PDFs and other personally identifying, potentially compromising data.
Many extensions conduct surveillance without any notification at all, but some do legal backflips to cover up their activities -- characterizing your installation of the extension as explicit permission to spy; pretending that URLs are by nature anonymous and so on. The data is aggregated and sold to unnamed third parties, reputedly for $0.04/user/month. Many of the spying extensions have more than a million users. One of the extensions identified as conducting secret spying advertises itself as a privacy-enhancing tool (!).
Detectify Labs have posted a technical explanation of how Chrome extensions conduct surveillance, and note near the end of their analysis that Firefox extensions are just as prone to spying. more
Microsoft Makes Windows 10 Automatic Spying Worse
Earlier this month Microsoft finally went on record admitting that automatic spying within Windows 10 cannot be stopped.
This sparked a lot of outrage and with ‘Threshold 2’ it appeared Microsoft had done a sharp U-turn because the background service at the heart tracking (the ‘Diagnostics Tracking Service’ aka ‘DiagTrack’) appeared to have been removed. Critics celebrated and it was another well deserved pat on the back for Microsoft.
Except it turns out Microsoft had just been very sneaky. What Tweakhound discovered and was subsequently confirmed by BetaNews, is Microsoft simply renamed DiagTrack. It is now called the ‘Connected User Experiences and Telemetry Service’ – which is both a) deliberately vague, and b) misleading (don’t ‘Connected User Experiences’ sound great). more
This sparked a lot of outrage and with ‘Threshold 2’ it appeared Microsoft had done a sharp U-turn because the background service at the heart tracking (the ‘Diagnostics Tracking Service’ aka ‘DiagTrack’) appeared to have been removed. Critics celebrated and it was another well deserved pat on the back for Microsoft.
Except it turns out Microsoft had just been very sneaky. What Tweakhound discovered and was subsequently confirmed by BetaNews, is Microsoft simply renamed DiagTrack. It is now called the ‘Connected User Experiences and Telemetry Service’ – which is both a) deliberately vague, and b) misleading (don’t ‘Connected User Experiences’ sound great). more
Two Spies Out This Week
Ronald Pelton, former National Security Agency employee convicted of selling defense and communication secrets he gained during his career has been released from federal custody 30 years after his arrest. more
Jonathan J. Pollard was released on parole from federal prison on Friday after serving 30 years of a life sentence for violations of the Espionage Act. more
Jonathan J. Pollard was released on parole from federal prison on Friday after serving 30 years of a life sentence for violations of the Espionage Act. more
FutureWatch: No Lens Spycams Thinner than a Dime
How thin can a camera be? Very, say Rice University researchers who have developed patented prototypes of their technological breakthrough.
FlatCam, invented by the Rice labs of electrical and computer engineers Richard Baraniuk and Ashok Veeraraghavan, is little more than a thin sensor chip with a mask that replaces lenses in a traditional camera.
"We can make curved cameras, or wallpaper that's actually a camera," says Richard Baraniuk, professor of electrical and computer engineering at Rice University. "You can have a camera on your credit card or a camera in an ultrathin tablet computer."
Making it practical are the sophisticated computer algorithms that process what the sensor detects and converts the sensor measurements into images and videos. more
FlatCam, invented by the Rice labs of electrical and computer engineers Richard Baraniuk and Ashok Veeraraghavan, is little more than a thin sensor chip with a mask that replaces lenses in a traditional camera.
"We can make curved cameras, or wallpaper that's actually a camera," says Richard Baraniuk, professor of electrical and computer engineering at Rice University. "You can have a camera on your credit card or a camera in an ultrathin tablet computer."
Making it practical are the sophisticated computer algorithms that process what the sensor detects and converts the sensor measurements into images and videos. more
Saturday, November 21, 2015
Ads Go from Subliminal to Ultrasonic - "PSSST... Any devices nearby?"
Privacy advocates are warning federal authorities of a new threat that uses inaudible, high-frequency sounds to surreptitiously track a person's online behavior across a range of devices, including phones, TVs, tablets, and computers.
The ultrasonic pitches are embedded into TV commercials or are played when a user encounters an ad displayed in a computer browser. While the sound can't be heard by the human ear, nearby tablets and smartphones can detect it. When they do, browser cookies can now pair a single user to multiple devices and keep track of what TV commercials the person sees, how long the person watches the ads, and whether the person acts on the ads by doing a Web search or buying a product.
Cross-device tracking raises important privacy concerns, the Center for Democracy and Technology wrote in recently filed comments to the Federal Trade Commission. The FTC has scheduled a workshop on Monday to discuss the technology. Often, people use as many as five connected devices throughout a given day—a phone, computer, tablet, wearable health device, and an RFID-enabled access fob. Until now, there hasn't been an easy way to track activity on one and tie it to another.
"As a person goes about her business, her activity on each device generates different data streams about her preferences and behavior that are siloed in these devices and services that mediate them," CDT officials wrote. "Cross-device tracking allows marketers to combine these streams by linking them to the same individual, enhancing the granularity of what they know about that person." more
The ultrasonic pitches are embedded into TV commercials or are played when a user encounters an ad displayed in a computer browser. While the sound can't be heard by the human ear, nearby tablets and smartphones can detect it. When they do, browser cookies can now pair a single user to multiple devices and keep track of what TV commercials the person sees, how long the person watches the ads, and whether the person acts on the ads by doing a Web search or buying a product.
Cross-device tracking raises important privacy concerns, the Center for Democracy and Technology wrote in recently filed comments to the Federal Trade Commission. The FTC has scheduled a workshop on Monday to discuss the technology. Often, people use as many as five connected devices throughout a given day—a phone, computer, tablet, wearable health device, and an RFID-enabled access fob. Until now, there hasn't been an easy way to track activity on one and tie it to another.
"As a person goes about her business, her activity on each device generates different data streams about her preferences and behavior that are siloed in these devices and services that mediate them," CDT officials wrote. "Cross-device tracking allows marketers to combine these streams by linking them to the same individual, enhancing the granularity of what they know about that person." more
FBI Investigates Drone Crash Outside NJ Refinery
Industrial espionage, terrorists, or innocent hobbyist? You decide.
The FBI and local police are investigating after a drone fell out of the sky and crashed into a truck in New Jersey on Wednesday morning.
As CBS2’s Christine Sloan reported, of particular concern to authorities is that the incident happened on a road just outside a Phillips 66 refinery in Linden.
The driver of the truck apparently got out and had words with the operator of the drone, who took off, investigators said.
John Victor Jacobson, head of New Jersey-based Drone Service Systems, said he cannot think of a good reason to fly one of these air crafts in such a sensitive area. more
This location is also very close to Newark Airport, to the South of its runway flight path.
The FBI and local police are investigating after a drone fell out of the sky and crashed into a truck in New Jersey on Wednesday morning.
As CBS2’s Christine Sloan reported, of particular concern to authorities is that the incident happened on a road just outside a Phillips 66 refinery in Linden.
The driver of the truck apparently got out and had words with the operator of the drone, who took off, investigators said.
John Victor Jacobson, head of New Jersey-based Drone Service Systems, said he cannot think of a good reason to fly one of these air crafts in such a sensitive area. more
This location is also very close to Newark Airport, to the South of its runway flight path.
The New Cowboy Spy
From the Ol' Timer...
"Howdy, partner. There is a new surveillance risk in town, and he be a-aimin' at you.
Worried about board meeting eavesdroppers; business espionage desperados, and bad egg buggists? Darn tootin' you are, and you've hired the local TSCM-slinger to keep you above snakes. Does a fine job of it, too.
Oh, about Mr. New Surveillance Risk. He ain't no fancy foreign spy, crow-bait competitor, or even a chiseler employee. No sir, bub, he's the cow chip of the spy world; a tenderfoot with a mighty powerful weapon. A sneaky dude who'll leave you in court, emptyin' your wallet faster than greased lightning. Yes sir'ee, he's the Workplace Video Voyeur, and he ain't a-playing according to Hoyle."
Thanks for the warning, old timer. You're right as rain. I know. I've run into a couple of these hombres during my time on the trail. Let me tell you a story...
My Fortune 50 client called me a few months ago. Seems, an employee found a spy camera hidden in one of their restrooms. The news media caught wind of it and jumped all over the story. It was an embarrassing mess. It may also be an expensive mess if the people caught by the camera decide to sue.
We had been inspecting their boardroom, executive offices and off-site meeting locations for over two decades. This due diligence resulted in the capture of one spy, on-site (a competitor's employee), one wireless bug, and several general information security loopholes which they quickly patched up.
Nobody expected a bathroom video voyeur, however. Yet this incident held promise of greater damage than any corporate espionage attack. In addition to being costly in dollars and damaging reputation-wise, a video voyeur attack directly affects employee morale. Its hard to put a price on that.
The company asked me for help. They needed to prevent future incidents. Made sense. After one incident, they could face "foreseeability," a legal term. In short, it is the theory that if something happens once you become aware it could happen again. If you do nothing to correct the situation, and it does happen again, you are considered negligent. Sexual harassment in the workplace also plays into future incidents. This makes for an expensive mix in court.
In addition to protecting themselves, the company really wanted to assure their employees that they were taking the situation very seriously.
We discussed several possible solutions.
Sending our Technical Surveillance Countermeasures (TSCM) team to inspect all their restrooms and locker rooms (worldwide) was impractical, of course. What we eventually decided upon was a three-fold strategy, which turned out to be very cost-effective.
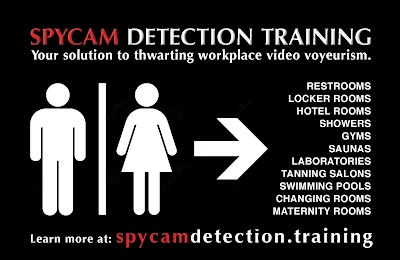 This company-wide solution cost them about as much as a one-day sweep of their executive offices, and it will be used at all their locations, for years to come.
This company-wide solution cost them about as much as a one-day sweep of their executive offices, and it will be used at all their locations, for years to come.
Other companies have not been so lucky. Another New York City firm paid two employees one million dollars apiece in connection with their video voyeur incident.
Yup, ol' timer. The times are changing. Companies need to start watching their butts, when it comes to butt watchers.
~Kevin
"Howdy, partner. There is a new surveillance risk in town, and he be a-aimin' at you.
Worried about board meeting eavesdroppers; business espionage desperados, and bad egg buggists? Darn tootin' you are, and you've hired the local TSCM-slinger to keep you above snakes. Does a fine job of it, too.
Oh, about Mr. New Surveillance Risk. He ain't no fancy foreign spy, crow-bait competitor, or even a chiseler employee. No sir, bub, he's the cow chip of the spy world; a tenderfoot with a mighty powerful weapon. A sneaky dude who'll leave you in court, emptyin' your wallet faster than greased lightning. Yes sir'ee, he's the Workplace Video Voyeur, and he ain't a-playing according to Hoyle."
Thanks for the warning, old timer. You're right as rain. I know. I've run into a couple of these hombres during my time on the trail. Let me tell you a story...
My Fortune 50 client called me a few months ago. Seems, an employee found a spy camera hidden in one of their restrooms. The news media caught wind of it and jumped all over the story. It was an embarrassing mess. It may also be an expensive mess if the people caught by the camera decide to sue.
We had been inspecting their boardroom, executive offices and off-site meeting locations for over two decades. This due diligence resulted in the capture of one spy, on-site (a competitor's employee), one wireless bug, and several general information security loopholes which they quickly patched up.
Nobody expected a bathroom video voyeur, however. Yet this incident held promise of greater damage than any corporate espionage attack. In addition to being costly in dollars and damaging reputation-wise, a video voyeur attack directly affects employee morale. Its hard to put a price on that.
The company asked me for help. They needed to prevent future incidents. Made sense. After one incident, they could face "foreseeability," a legal term. In short, it is the theory that if something happens once you become aware it could happen again. If you do nothing to correct the situation, and it does happen again, you are considered negligent. Sexual harassment in the workplace also plays into future incidents. This makes for an expensive mix in court.
In addition to protecting themselves, the company really wanted to assure their employees that they were taking the situation very seriously.
We discussed several possible solutions.
Sending our Technical Surveillance Countermeasures (TSCM) team to inspect all their restrooms and locker rooms (worldwide) was impractical, of course. What we eventually decided upon was a three-fold strategy, which turned out to be very cost-effective.
- A review of their Recording in the Workplace Policy for completeness and effectiveness. This policy covers all aspects of recording anything to do with the company (audio, video and data). Most companies don't even have policy.
- Development of an on-line spycam detection training program for their local facilities managers and security staff. This would professionally prepare them to conduct simple periodic inspections of the 'expectation of privacy' areas on company property. An inspection log and photos would be kept on file. The log documents inspection dates and results. The photos document changes in the area over time. Both may be used to show due diligence in court.
- A short on-line spycam awareness video was produced for all employees to view. This was placed on the company intranet. It explained the growing social problem of video voyeurism, the steps the company is taking to prevent the problem in the workplace, and self-protection tips employees can use to protect themselves and their families, wherever they are.
 This company-wide solution cost them about as much as a one-day sweep of their executive offices, and it will be used at all their locations, for years to come.
This company-wide solution cost them about as much as a one-day sweep of their executive offices, and it will be used at all their locations, for years to come.
Other companies have not been so lucky. Another New York City firm paid two employees one million dollars apiece in connection with their video voyeur incident.
Yup, ol' timer. The times are changing. Companies need to start watching their butts, when it comes to butt watchers.
~Kevin
Wednesday, November 18, 2015
A Survey of Behind the Scenes Personal Data Sharing to Third Parties by Mobile Apps
A Survey of Behind the Scenes Personal Data Sharing to Third Parties by Mobile Apps
Tested - 110 popular, free Android and iOS apps to look for apps that shared personal, behavioral, and location data with third parties
73% of Android apps shared personal information such as email address with third parties, and 47% of iOS apps shared geo-coordinates and other location data with third parties
93% of Android apps tested connected to a mysterious domain, safemovedm.com, likely due to a background process of the Android phone
A significant proportion of apps share data from user inputs such as personal information or search terms with third parties without Android or iOS requiring a notification to the user more
 |
| Click to Enlarge |
73% of Android apps shared personal information such as email address with third parties, and 47% of iOS apps shared geo-coordinates and other location data with third parties
93% of Android apps tested connected to a mysterious domain, safemovedm.com, likely due to a background process of the Android phone
A significant proportion of apps share data from user inputs such as personal information or search terms with third parties without Android or iOS requiring a notification to the user more
FCC Chairman Suggests Expanded Wiretap Laws
The nation’s top telecom regulator recommended broadening America’s wiretapping laws Tuesday, in response to the recent attacks in Paris by the Islamic State that left more than 120 people dead.
While the Federal Communications Commission cannot take direct action against the Islamic State, such as shutting down its Web sites or social media accounts, Congress could do “specific things” allowing the FCC to assist law enforcement more effectively, agency Chairman Tom Wheeler told a House subcommittee.
That includes revisiting the wiretap legislation, said Wheeler. The 1994 law, known as the Communications Assistance for Law Enforcement Act, or CALEA, provides for the “lawful intercept” of a suspect’s telephone and online communications. It requires telecom companies and Internet providers, not to mention some online voice services, to build their networks in ways that grant authorities easier access to those communications. more
While the Federal Communications Commission cannot take direct action against the Islamic State, such as shutting down its Web sites or social media accounts, Congress could do “specific things” allowing the FCC to assist law enforcement more effectively, agency Chairman Tom Wheeler told a House subcommittee.
That includes revisiting the wiretap legislation, said Wheeler. The 1994 law, known as the Communications Assistance for Law Enforcement Act, or CALEA, provides for the “lawful intercept” of a suspect’s telephone and online communications. It requires telecom companies and Internet providers, not to mention some online voice services, to build their networks in ways that grant authorities easier access to those communications. more
A $50. Audio Video Bugging Device is Child's Play
Remote Spy Mode
The Video Walkie Talkies act as a hidden camera. Place one Walkie in a secret location, press the activation button on the other and you’ll instantly have a hidden, live-feed surveillance cam. If you leave your Video Walkies for 15 minutes unused they automatically turn off to save power. When your mission is complete, the Video Walkie Talkies easily fold up for compact storage and screen protection! Gear up with the Spy Gear Video Walkie Talkies!
No Data or Wi-Fi Required
The Video Walkie Talkies do not require Data or Wi-Fi to use! Just press the activation button and you can wirelessly communicate with your friends on video! With a range of up to 160 feet you’ll be in constant communication with your fellow agent.
Quick Set Up – Easy As 1-2-3
Only Spy Gear has the spy technology to let you stay in constant 2-way, visual and audio communication at long range! Open up your Video Walkie Talkies and turn the power on. You’ll instantly be able to see your friends on the LCD screen. Now press the TRANSMIT BUTTON for audio communication with the other Video Walkie. Want to go stealth? Plug headphones into both Video Walkies to listen in secret and communicate without pressing the TRANSMIT BUTTON. more
The Video Walkie Talkies act as a hidden camera. Place one Walkie in a secret location, press the activation button on the other and you’ll instantly have a hidden, live-feed surveillance cam. If you leave your Video Walkies for 15 minutes unused they automatically turn off to save power. When your mission is complete, the Video Walkie Talkies easily fold up for compact storage and screen protection! Gear up with the Spy Gear Video Walkie Talkies!
No Data or Wi-Fi Required
The Video Walkie Talkies do not require Data or Wi-Fi to use! Just press the activation button and you can wirelessly communicate with your friends on video! With a range of up to 160 feet you’ll be in constant communication with your fellow agent.
Quick Set Up – Easy As 1-2-3
Only Spy Gear has the spy technology to let you stay in constant 2-way, visual and audio communication at long range! Open up your Video Walkie Talkies and turn the power on. You’ll instantly be able to see your friends on the LCD screen. Now press the TRANSMIT BUTTON for audio communication with the other Video Walkie. Want to go stealth? Plug headphones into both Video Walkies to listen in secret and communicate without pressing the TRANSMIT BUTTON. more
Monday, November 16, 2015
BlackBerry SecuSUITE - Voice Encryption for iOS, Android & BlackBerry
BlackBerry Limited and its subsidiary Secusmart has today announced the release of SecuSUITE for Enterprise,
a new voice encryption solution that protects mobile calls on the Android, iOS and BlackBerry operating systems.
By using the VoIP, software-based, cloud-hosted solution, employees will be able to conduct secure conversations worldwide and be able to send encrypted text messages of any length.
Voice and text messages are encrypted with 128-bit Advanced Encryption Standard (AES) on the individual device level, meaning messages are stored on the receiver’s smartphone and only sent to the recipient when they are available to receive them. more
a new voice encryption solution that protects mobile calls on the Android, iOS and BlackBerry operating systems.
By using the VoIP, software-based, cloud-hosted solution, employees will be able to conduct secure conversations worldwide and be able to send encrypted text messages of any length.
Voice and text messages are encrypted with 128-bit Advanced Encryption Standard (AES) on the individual device level, meaning messages are stored on the receiver’s smartphone and only sent to the recipient when they are available to receive them. more
The Newest Anti-Espionage Agents... Monks & Nuns!?!?
China is training Buddhist monks and nuns in Tibet to carry out anti-espionage operations
 along the remote Sino-Indian border to prevent attempts to create "conflict" by "ethnic separatists", in a veiled reference to the Dalai Lama and his supporters.
along the remote Sino-Indian border to prevent attempts to create "conflict" by "ethnic separatists", in a veiled reference to the Dalai Lama and his supporters.
"Twenty-two monks and nuns from three temples in Nyingchi, a city in southeastern Tibet, close to the Sino-Indian border, received the three-hour lecture at Lamaling Temple on the counter-espionage law by local and national security officials," state-run news portal Tibet.Cn reported.
The lecture conducted in the Himalayan region along the border with India was about how to abide by the counter-espionage law and the legal consequences of violating the law, it said. more
 along the remote Sino-Indian border to prevent attempts to create "conflict" by "ethnic separatists", in a veiled reference to the Dalai Lama and his supporters.
along the remote Sino-Indian border to prevent attempts to create "conflict" by "ethnic separatists", in a veiled reference to the Dalai Lama and his supporters. "Twenty-two monks and nuns from three temples in Nyingchi, a city in southeastern Tibet, close to the Sino-Indian border, received the three-hour lecture at Lamaling Temple on the counter-espionage law by local and national security officials," state-run news portal Tibet.Cn reported.
The lecture conducted in the Himalayan region along the border with India was about how to abide by the counter-espionage law and the legal consequences of violating the law, it said. more
Sunday, November 15, 2015
The $8 USB Memory Stick Lock
3 Digit Combination USB Flash Drive Security Lock.
 A physical lock for your USB Flash Drive.
A physical lock for your USB Flash Drive.
Set your own 3 digits code to prevent your flash drive from being inserted into another computer.
Of course, it won't stop everyone, but it may thwart general snoops. more
 A physical lock for your USB Flash Drive.
A physical lock for your USB Flash Drive.Set your own 3 digits code to prevent your flash drive from being inserted into another computer.
Of course, it won't stop everyone, but it may thwart general snoops. more
Saturday, November 14, 2015
Visit Switzerland in June - Information Security and Cryptography Seminar
INFORMATION SECURITY AND CRYPTOGRAPHY, FUNDAMENTALS AND APPLICATIONS (June 13-15, 2016)
Lecturers: Prof. David Basin and Prof. Ueli Maurer, ETH Zurich
The topics covered include cryptography and its foundations, system and network security, PKIs and key management, authentication and access control, privacy and data protection, and advanced topics in cryptography. The seminar takes place in Zurich, Switzerland. The lectures and all course material are in English.
This seminar provides an in-depth coverage of Information Security and Cryptography. Concepts are explained in a way understandable to a wide audience, as well as mathematical, algorithmic, protocol-specific, and system-oriented aspects.
A full description of the seminar, including a detailed listing of topics covered, is available at www.infsec.ch
Lecturers: Prof. David Basin and Prof. Ueli Maurer, ETH Zurich
The topics covered include cryptography and its foundations, system and network security, PKIs and key management, authentication and access control, privacy and data protection, and advanced topics in cryptography. The seminar takes place in Zurich, Switzerland. The lectures and all course material are in English.
This seminar provides an in-depth coverage of Information Security and Cryptography. Concepts are explained in a way understandable to a wide audience, as well as mathematical, algorithmic, protocol-specific, and system-oriented aspects.
A full description of the seminar, including a detailed listing of topics covered, is available at www.infsec.ch
Friday, November 13, 2015
How to Stop Your Vizio TV form Spying On You
from vizio.com
Beginning October 31, 2015, VIZIO will use Viewing Data together with your IP address and other Non-Personal Information in order to inform third party selection and delivery of targeted and re-targeted advertisements. These advertisements may be delivered to smartphones, tablets, PCs or other internet-connected devices that share an IP address or other identifier with your Smart TV...
Smart Interactivity is a feature on Internet-connected VIZIO televisions that recognizes onscreen content. Currently, we only use this feature to gather data on a non-personal or anonymous basis, as described below...
...your VIZIO Smart TV can intelligently recognize linear television and other content shown on the screen and in the future may display accompanying interactive features such as bonus features related to the content you are viewing, the ability to vote in polls, or advertisements that match your interests...
Smart Interactivity collects information from your product which triggers events, such as pop-ups, about what you are viewing. Follow the steps below on how to turn on or off Smart Interactivity based on the version of VIZIO Internet Apps (VIA) installed on your television.
Beginning October 31, 2015, VIZIO will use Viewing Data together with your IP address and other Non-Personal Information in order to inform third party selection and delivery of targeted and re-targeted advertisements. These advertisements may be delivered to smartphones, tablets, PCs or other internet-connected devices that share an IP address or other identifier with your Smart TV...
Smart Interactivity is a feature on Internet-connected VIZIO televisions that recognizes onscreen content. Currently, we only use this feature to gather data on a non-personal or anonymous basis, as described below...
...your VIZIO Smart TV can intelligently recognize linear television and other content shown on the screen and in the future may display accompanying interactive features such as bonus features related to the content you are viewing, the ability to vote in polls, or advertisements that match your interests...
Smart Interactivity collects information from your product which triggers events, such as pop-ups, about what you are viewing. Follow the steps below on how to turn on or off Smart Interactivity based on the version of VIZIO Internet Apps (VIA) installed on your television.
Thursday, November 12, 2015
Security Director Alert - Don't Be a Business Espionage Target While Traveling
via http://seriouslyvc.com
The following list represents the most important procedures you and your colleagues should follow on your next trip abroad:
The following list represents the most important procedures you and your colleagues should follow on your next trip abroad:
- Avoid disclosing your travel details to strangers.
- Never put electronics in your checked luggage.
- Consider traveling with a disposable cellphone (they are less susceptible to eavesdropping).
- Use a separate “throw-away” email to communicate with your family and coworkers (this prevents hackers from penetrating your company’s email system even after you have completed your trip).
- Consider installing an asymmetric email encryption program such as “Pretty Good Privacy” (PGP) on your computer, which allows you to encrypt and decrypt your email over the Internet.
- Put sensitive business documents on password-protected USB drives (such as “Iron Key” or “BitLocker”).
- Never use complimentary WiFi when traveling, unless absolutely necessary, and always use a trusted VPN.
- Never leave your sensitive business materials and/or electronics unattended in your hotel room — and your hotel safe is not safe! Carry all electronics with you at all times (hence, the need for smaller devices).
- If you spend time in the hotel bar, be cautious of what you say and to whom, because they are prime hunting grounds for espionage operatives.
- Be mindful of sexual entrapment (the Russians are still the masters of “honeypots” and have blackmailed many a business traveler into disclosing sensitive information in exchange for keeping their affairs secret).
- Use a strong passphrase (instead of password) containing up to 14-18 characters (and change it every 180 days or after every international trip).
- Make it a habit to power-off your devices when they are not in use. more
Book - How to Be a Spy - WWII Training Manual
In the early years of World War II, Special Operations Executive (SOE) set up top secret training schools to instruct prospective agents in the art of being a spy.
By the end of 1941, an international network of schools was in operation in secluded locations ranging from the Scottish Highlands to Singapore and Canada.
How to Be a Spy reproduces the extensive training manuals used to prepare agents for their highly dangerous missions behind enemy lines. The courses cover a variety of clandestine skills including disguise, surveillance, burglary, interrogation, close combat, and assassination - everything needed to wreak havoc in occupied Europe.
By the end of 1941, an international network of schools was in operation in secluded locations ranging from the Scottish Highlands to Singapore and Canada.
How to Be a Spy reproduces the extensive training manuals used to prepare agents for their highly dangerous missions behind enemy lines. The courses cover a variety of clandestine skills including disguise, surveillance, burglary, interrogation, close combat, and assassination - everything needed to wreak havoc in occupied Europe.
Contest - Tell Us Everything You Know About this Wiretapping Device
I am guessing anyone who as ever used this is now pushing up punchdown blocks.
But, there is a nice prize for the person who can tell us about this device...
• the manufacturer,
• who used this device,
• approximate year of manufacturer.
BONUS PRIZE if you send me the manual.
Information you submit will be shared below.
Enter HERE.
Winner: RH - Regarding your mystery wiretapping device, it is a Western Electric
model 300ABC telephone line recording unit. Western Electric was the
manufacturing company of AT&T up until the mid-90s, and furnished a
lot of kit for the military. Based on the design and housing of this
unit, it was likely manufactured some time between 1939 and 1946. While
this could be used for wiretapping, these devices were common in
military command posts were it would be used to record phone
conversations between officers, and the recording would subsequently be
transcribed and filed.
(Additional insights welcome.)
But, there is a nice prize for the person who can tell us about this device...
• the manufacturer,
• who used this device,
• approximate year of manufacturer.
BONUS PRIZE if you send me the manual.
Information you submit will be shared below.
Enter HERE.
(Additional insights welcome.)
Slurpee Sound Cups - Now Imagine a Cup Made with Wiretaps
By now, you probably know all about 7 Eleven's Bring Your Own Cup Day, the minimart's annual event during which anyone can bring practically any sort of container into the store and fill it up with Slurpee, all for the same low price.
 Well, earlier this fall during BYO Cup Day in Australia, 7 Eleven, along with its agency Leo Burnett Melbourne, took the cup idea up a notch by allowing consumers to fill up radio ads with Slurpee.
Well, earlier this fall during BYO Cup Day in Australia, 7 Eleven, along with its agency Leo Burnett Melbourne, took the cup idea up a notch by allowing consumers to fill up radio ads with Slurpee.
Come again? Yes, radio ads became drink containers in the inventive campaign "Slurpee Sound Cup" campaign. 7 Eleven took the sound waves of three radio spots, themed around Viking opera, Brazilian soccer fans and randy whales, and transformed them into a series of distinctive 3D-printed vessels that were given away to Slurpee fans for the big day. Consumers could also download the 3D files and make the cups themselves. video
 Well, earlier this fall during BYO Cup Day in Australia, 7 Eleven, along with its agency Leo Burnett Melbourne, took the cup idea up a notch by allowing consumers to fill up radio ads with Slurpee.
Well, earlier this fall during BYO Cup Day in Australia, 7 Eleven, along with its agency Leo Burnett Melbourne, took the cup idea up a notch by allowing consumers to fill up radio ads with Slurpee.Come again? Yes, radio ads became drink containers in the inventive campaign "Slurpee Sound Cup" campaign. 7 Eleven took the sound waves of three radio spots, themed around Viking opera, Brazilian soccer fans and randy whales, and transformed them into a series of distinctive 3D-printed vessels that were given away to Slurpee fans for the big day. Consumers could also download the 3D files and make the cups themselves. video
Big Taps in The Big House
Thousands of confidential phone conversations between inmates and their lawyers have been recorded
by a leading prison phone company that also serves New York City jails — a major data breach exposed by a hacker, according to a report.
The anonymous hacker believes the company, Securus Technologies, is violating prisoners’ constitutional rights by recording privileged conversations, The Intercept reported Wednesday.
Of 70 million phone-call records obtained by The Intercept, 14,000 were for legally protected calls made to prisoners’ attorneys, The Intercept said. more
by a leading prison phone company that also serves New York City jails — a major data breach exposed by a hacker, according to a report.
The anonymous hacker believes the company, Securus Technologies, is violating prisoners’ constitutional rights by recording privileged conversations, The Intercept reported Wednesday.
Of 70 million phone-call records obtained by The Intercept, 14,000 were for legally protected calls made to prisoners’ attorneys, The Intercept said. more
Wednesday, November 11, 2015
Uninstall InstaAgent From Your Phone Now
By
Andy Boxall
If you’re one of the thousands of people with an app named Who Viewed Your Profile – InstaAgent installed on your smartphone, stop using it and delete it right now.
Why? Because it’s stealing your password, transferring it to a server, and then posting images on your Instagram account suggesting others should also download the app.
The app is a third-party Instagram client that promised to tell you who visited your Instagram account, something it could only do once you’d handed over your username and password. This function was never carried out, and the app’s sole intention was to steal Instagram logins. more
If you’re one of the thousands of people with an app named Who Viewed Your Profile – InstaAgent installed on your smartphone, stop using it and delete it right now.
Why? Because it’s stealing your password, transferring it to a server, and then posting images on your Instagram account suggesting others should also download the app.
The app is a third-party Instagram client that promised to tell you who visited your Instagram account, something it could only do once you’d handed over your username and password. This function was never carried out, and the app’s sole intention was to steal Instagram logins. more
Wednesday, November 4, 2015
Dial 12339 To Report a Spy in China (Let the SWATing Begin)
China has set up a new national hot line for reporting “spies” as authorities grow increasingly sensitive over national security issues.
The new service was set up by officials in the north-eastern province of Jilin, the local New Cultural Newspaper said Sunday, with reports saying those who suspect “espionage activity” can call 12339.
“The hot line targets foreign organizations and individuals who conduct espionage activities or who instigate and sponsor others in conducting them,” the fiercely nationalist Global Times newspaper said.
A list of "guidelines" to help people identify spies appeared on Chinese social media soon after the hot line was announced, however it was unclear where it originated.
Potential spies included “those with vague job tiles and a lot of money” and “those who bring up controversial topics at parties and then only observe the discussion”, said the guidelines, which had been shared widely on Chinese messaging app Wechat. more
The new service was set up by officials in the north-eastern province of Jilin, the local New Cultural Newspaper said Sunday, with reports saying those who suspect “espionage activity” can call 12339.
“The hot line targets foreign organizations and individuals who conduct espionage activities or who instigate and sponsor others in conducting them,” the fiercely nationalist Global Times newspaper said.
A list of "guidelines" to help people identify spies appeared on Chinese social media soon after the hot line was announced, however it was unclear where it originated.
Potential spies included “those with vague job tiles and a lot of money” and “those who bring up controversial topics at parties and then only observe the discussion”, said the guidelines, which had been shared widely on Chinese messaging app Wechat. more
"If You're Not Paranoid, You're Crazy"
An excellent, thought provoking article on how others are predicting our next moves...
(excerpt from Walter Kirn's article in The Atlantic.) "I was already growing certain that we, the sensible majority, owe plenty of so-called crackpots a few apologies. We dismissed them, shrugging off as delusions or urban legends various warnings and anecdotes that now stand revealed, in all too many instances, as either solid inside tips or spooky marvels of intuition.
The Mormon elder who told me when I was a teenager back in 1975 that people soon would have to carry “chips” around or “be banished from the marketplace.”
The ex–Army ranger in the 1980s who said an “eye in the sky” could read my license plate.
The girlfriend in 1993 who forbade me to rent a dirty video on the grounds that “they keep lists of everything.”
The Hollywood actor in 2011 who declined to join me on his sundeck because he’d put on weight and a security expert had advised him that the paparazzi were flying drones.
The tattooed grad student who, about a year before Edward Snowden gave the world the lowdown on code-named snooping programs such as PRISM and XKeyscore, told me about a childhood friend of his who worked in military intelligence and refused to go to wild parties unless the guests agreed to leave their phones locked outside in a car trunk or a cooler, preferably with the battery removed, and who also confessed to snooping on a girlfriend through the camera in her laptop.
The night I vowed never again to mock such people, in January 2014, I was standing knee-deep in a field of crusty snow at the edge of a National Guard base near Saratoga Springs, Utah, a fresh-from-the-factory all-American settlement, densely flagpoled and lavishly front-porched, just south of Salt Lake City. Above its rooftops the moon was a pale sliver, and filling the sky were the sort of ragged clouds in which one might discern the face of Jesus. I had on a dark jacket, a dark wool cap, and a black nylon mask to keep my cheeks from freezing.
The key would be surviving those first days after the ATMs stopped working and the grocery stores were looted bare.
I’d gone there for purposes of counterespionage..." more
(excerpt from Walter Kirn's article in The Atlantic.) "I was already growing certain that we, the sensible majority, owe plenty of so-called crackpots a few apologies. We dismissed them, shrugging off as delusions or urban legends various warnings and anecdotes that now stand revealed, in all too many instances, as either solid inside tips or spooky marvels of intuition.
The Mormon elder who told me when I was a teenager back in 1975 that people soon would have to carry “chips” around or “be banished from the marketplace.”
The ex–Army ranger in the 1980s who said an “eye in the sky” could read my license plate.
The girlfriend in 1993 who forbade me to rent a dirty video on the grounds that “they keep lists of everything.”
The Hollywood actor in 2011 who declined to join me on his sundeck because he’d put on weight and a security expert had advised him that the paparazzi were flying drones.
The tattooed grad student who, about a year before Edward Snowden gave the world the lowdown on code-named snooping programs such as PRISM and XKeyscore, told me about a childhood friend of his who worked in military intelligence and refused to go to wild parties unless the guests agreed to leave their phones locked outside in a car trunk or a cooler, preferably with the battery removed, and who also confessed to snooping on a girlfriend through the camera in her laptop.
The night I vowed never again to mock such people, in January 2014, I was standing knee-deep in a field of crusty snow at the edge of a National Guard base near Saratoga Springs, Utah, a fresh-from-the-factory all-American settlement, densely flagpoled and lavishly front-porched, just south of Salt Lake City. Above its rooftops the moon was a pale sliver, and filling the sky were the sort of ragged clouds in which one might discern the face of Jesus. I had on a dark jacket, a dark wool cap, and a black nylon mask to keep my cheeks from freezing.
The key would be surviving those first days after the ATMs stopped working and the grocery stores were looted bare.
I’d gone there for purposes of counterespionage..." more
Smart Sheriff Chased Out of Town
Remember our Smart Sheriff post from May?
South Korea created this spyware for cell phones.
I'll wait while you check it out.
UPDATE: South Korea pulls plug on child monitoring app
The most widely used child surveillance app in South Korea is being quietly pulled from the market after security specialists raised serious concerns about the program’s safety...
Smart Sheriff’s disappearance is awkward news for South Korea’s effort to keep closer tabs on the online lives of its youngest citizens.
A law passed in April requires all new smartphones sold to those 18 and under to be equipped with software that parents can use to snoop on their kids’ social media activity. Smart Sheriff, the most popular of more than a dozen state-approved apps, was meant to keep children safe from pornography, bullying, and other threats, but experts say its abysmal security left the door wide open to hackers and put the personal information of some 380,000 users at risk. more
South Korea created this spyware for cell phones.
I'll wait while you check it out.
UPDATE: South Korea pulls plug on child monitoring app
The most widely used child surveillance app in South Korea is being quietly pulled from the market after security specialists raised serious concerns about the program’s safety...
Smart Sheriff’s disappearance is awkward news for South Korea’s effort to keep closer tabs on the online lives of its youngest citizens.
A law passed in April requires all new smartphones sold to those 18 and under to be equipped with software that parents can use to snoop on their kids’ social media activity. Smart Sheriff, the most popular of more than a dozen state-approved apps, was meant to keep children safe from pornography, bullying, and other threats, but experts say its abysmal security left the door wide open to hackers and put the personal information of some 380,000 users at risk. more
Friday, October 30, 2015
Security Director Alert - 80% Chance Your Card Key System Can Be Bypassed
A device the size of a quarter that can be installed in 60 seconds on a proximity card reader could potentially be used to break physical access controls in 80 percent of deployments.
The device, dubbed BLEKey, is used to read cleartext data sent from card readers to door controllers to either clone cards or feed that data to a mobile application that can be used to unlock doors at any number of installations.
The hack unveiled at Black Hat is worrisome for facilities reliant on proximity cards and readers for access to buildings in critical industries or enterprises. Researchers Eric Evenchick, an embedded systems architect at electric car manufacturer Faraday Future, and Mark Baseggio, a managing principal consultant at Optiv (formerly Accuvant), used the ubiquitous HID cards and readers in a number of successful demos during their talk, but said that it’s likely the same weaknesses that facilitate their attacks are present in devices from other manufacturers. more video
Really Scary: 29:35 minutes into the video they explain how to make a card-key interceptor, stick it into a back pack, go to the target workplace, get in an elevator with employees (or just close to one of them), secretly read everyone's cards, and make a clone card.
Happy Halloween ~Kevin
The device, dubbed BLEKey, is used to read cleartext data sent from card readers to door controllers to either clone cards or feed that data to a mobile application that can be used to unlock doors at any number of installations.
The hack unveiled at Black Hat is worrisome for facilities reliant on proximity cards and readers for access to buildings in critical industries or enterprises. Researchers Eric Evenchick, an embedded systems architect at electric car manufacturer Faraday Future, and Mark Baseggio, a managing principal consultant at Optiv (formerly Accuvant), used the ubiquitous HID cards and readers in a number of successful demos during their talk, but said that it’s likely the same weaknesses that facilitate their attacks are present in devices from other manufacturers. more video
Really Scary: 29:35 minutes into the video they explain how to make a card-key interceptor, stick it into a back pack, go to the target workplace, get in an elevator with employees (or just close to one of them), secretly read everyone's cards, and make a clone card.
Happy Halloween ~Kevin
The Disorderly Orderly, or Spycam Peek-A-Boo in the ICU
India - Police have arrested a 30-year-old male orderly of Rajiv Gandhi Cancer Institute and Research Centre
 on charges of filming women after allegedly putting up spy camera in changing room for nurses.
on charges of filming women after allegedly putting up spy camera in changing room for nurses.
A nurse spotted the spy camera in the changing room inside the intensive care unit (ICU) on the third floor and alerted a security guard, said sources.
Police have reportedly recovered two obscene video clips from his spy camera, which was installed for around 12 hours, said sources. Police will now try to retrieve deleted data, added the sources. more
 on charges of filming women after allegedly putting up spy camera in changing room for nurses.
on charges of filming women after allegedly putting up spy camera in changing room for nurses.A nurse spotted the spy camera in the changing room inside the intensive care unit (ICU) on the third floor and alerted a security guard, said sources.
Police have reportedly recovered two obscene video clips from his spy camera, which was installed for around 12 hours, said sources. Police will now try to retrieve deleted data, added the sources. more
Police vs Spy Blimp in PA - Shotguns Preveil
PA - State police used shotguns Thursday to deflate a wayward military surveillance blimp that broke loose in Maryland and floated for hours before coming down into trees in the Pennsylvania countryside.
Curious residents trickled into a staging area as the military began gathering up some 6,000 feet of tether, the blimp’s huge hull and a smaller tail piece, a process expected to take at least through Friday.
The white behemoth still had helium in its nose when it went down in a steep ravine on Wednesday afternoon, and the easiest way to drain the gas was to shoot it, U.S. Army Captain Matthew Villa said. State police troopers peppered the blimp with about 100 shots. more How it all started.
Curious residents trickled into a staging area as the military began gathering up some 6,000 feet of tether, the blimp’s huge hull and a smaller tail piece, a process expected to take at least through Friday.
The white behemoth still had helium in its nose when it went down in a steep ravine on Wednesday afternoon, and the easiest way to drain the gas was to shoot it, U.S. Army Captain Matthew Villa said. State police troopers peppered the blimp with about 100 shots. more How it all started.
The Ultimate Spy vs Spy
via
Mark Frauenfelder, Boing Boing
It was a wordless one-page comic about two oddly pointy faced spies, one dressed in black and the other dressed in white. Other than their different colored outfits, they behaved identically. They hated each other and created elaborate Rube Goldberg type machines to try to kill each other. Sometimes their machines worked, often, they’d backfire. They were tricky but usually too clever for their own good.
This anthology colorizes 150 “Spy vs Spy” comics drawn by Antonio Prohías from 1961 until his death in 1987. The book also includes a collection of “Spy vs Spy” comics by the talented cartoonist Peter Kuper, who took over the strip when Prohías died. The anthology features a section of wonderful “Spy vs Spy” tribute drawings by noted cartoonists such as Peter Bagge, Bob Staake, Darwyn Cooke, Gilbert and Jaime Hernandez, and Bill Sienkiewicz. There’s also a biography of the Cuban-born Prohíasm and a new 4-page color strip by MAD luminary Sergio Aragones about his friendship with Prohías. With all the new material here, this book is a must for anyone who loves “Spy vs Spy.”
Spy Vs Spy: An Explosive Celebration
by Antonio Prohías and Peter Kuper
Liberty Street, 2015, 224 pages, 8.8 x 0.8 x 11.2 inches
$16.46 at Amazon
It was a wordless one-page comic about two oddly pointy faced spies, one dressed in black and the other dressed in white. Other than their different colored outfits, they behaved identically. They hated each other and created elaborate Rube Goldberg type machines to try to kill each other. Sometimes their machines worked, often, they’d backfire. They were tricky but usually too clever for their own good.
This anthology colorizes 150 “Spy vs Spy” comics drawn by Antonio Prohías from 1961 until his death in 1987. The book also includes a collection of “Spy vs Spy” comics by the talented cartoonist Peter Kuper, who took over the strip when Prohías died. The anthology features a section of wonderful “Spy vs Spy” tribute drawings by noted cartoonists such as Peter Bagge, Bob Staake, Darwyn Cooke, Gilbert and Jaime Hernandez, and Bill Sienkiewicz. There’s also a biography of the Cuban-born Prohíasm and a new 4-page color strip by MAD luminary Sergio Aragones about his friendship with Prohías. With all the new material here, this book is a must for anyone who loves “Spy vs Spy.”
Spy Vs Spy: An Explosive Celebration
by Antonio Prohías and Peter Kuper
Liberty Street, 2015, 224 pages, 8.8 x 0.8 x 11.2 inches
$16.46 at Amazon
Thursday, October 29, 2015
Spycam Ejection
Australia - A Brisbane landlord has been slammed for installing CCTV cameras inside his rental property and spying on his tenants, who he evicted once they complained.
Renters Ben and Lila - who withheld their surnames - told Channel Nine's A Current Affair they noticed they were being recorded on the first day they moved into their new apartment.
The security camera was set up in the lounge room, switched on and recording.
According to the program, the furious flatmates immediate flicked the switch on the camera, before they were contacted by the landlord who said they had to turn it back on. more video
Renters Ben and Lila - who withheld their surnames - told Channel Nine's A Current Affair they noticed they were being recorded on the first day they moved into their new apartment.
The security camera was set up in the lounge room, switched on and recording.
According to the program, the furious flatmates immediate flicked the switch on the camera, before they were contacted by the landlord who said they had to turn it back on. more video
Crackdown on Users of DroidJack Spyware
Law enforcement officials in almost half a dozen European countries have searched the homes of people suspected of having used software to spy on mobile phone users...
In Germany, prosecutors searched the homes of 13 people on Tuesday, they said, adding raids had also taken place in Britain, France, Belgium and Switzerland. They did not have further information on the raids in other countries.
 The suspects in Germany, aged between 19 and 51, are believed to have bought and used smartphone software DroidJack, which allows surveillance of phones that use Google's Android...
The suspects in Germany, aged between 19 and 51, are believed to have bought and used smartphone software DroidJack, which allows surveillance of phones that use Google's Android...
The software allows users to monitor a smartphone's data traffic, eavesdrop on phone conversations or hijack a phone's camera without its owner noticing. It can also be used to spy on smartphone users as they access online banking systems. more
In Germany, prosecutors searched the homes of 13 people on Tuesday, they said, adding raids had also taken place in Britain, France, Belgium and Switzerland. They did not have further information on the raids in other countries.
 The suspects in Germany, aged between 19 and 51, are believed to have bought and used smartphone software DroidJack, which allows surveillance of phones that use Google's Android...
The suspects in Germany, aged between 19 and 51, are believed to have bought and used smartphone software DroidJack, which allows surveillance of phones that use Google's Android...The software allows users to monitor a smartphone's data traffic, eavesdrop on phone conversations or hijack a phone's camera without its owner noticing. It can also be used to spy on smartphone users as they access online banking systems. more
Bud Flight - Spies on the Go
The two-state battle for a federal spy agency’s new regional headquarters is heating up,
 with Missouri Gov. Jay Nixon on Wednesday announcing plans to publicly push to keep the agency in St. Louis as hundreds of supporters gathered across the Mississippi River to tout a potential Illinois location.
with Missouri Gov. Jay Nixon on Wednesday announcing plans to publicly push to keep the agency in St. Louis as hundreds of supporters gathered across the Mississippi River to tout a potential Illinois location.
At stake in the bistate regional fight are more than 3,000 high-tech jobs at the National Geospatial-Intelligence Agency paying an average of $75,000.
The defense and intelligence agency is considering four sites to replace its current location near the Anheuser-Busch brewery south of downtown St. Louis. more
 with Missouri Gov. Jay Nixon on Wednesday announcing plans to publicly push to keep the agency in St. Louis as hundreds of supporters gathered across the Mississippi River to tout a potential Illinois location.
with Missouri Gov. Jay Nixon on Wednesday announcing plans to publicly push to keep the agency in St. Louis as hundreds of supporters gathered across the Mississippi River to tout a potential Illinois location.At stake in the bistate regional fight are more than 3,000 high-tech jobs at the National Geospatial-Intelligence Agency paying an average of $75,000.
The defense and intelligence agency is considering four sites to replace its current location near the Anheuser-Busch brewery south of downtown St. Louis. more
Business Espionage: Buy Your Batting Average with Blackmail
Former big leaguer Lenny Dykstra admitted to spending "half a million bucks" on private investigators to dig up dirt on umpires during his playing career.
Dykstra says he then used the information not necessarily to bribe umpires, but to intimidate them into giving him favorable calls. "Fear does a lot to a man," he says. Here's the video:
"Their blood is just as red as ours. Some of them like women, some of them like men, some of them gamble," said Dykstra. He then imagined a scenario in which he asked the umpire if he "covered the spread last night" after a called strike, then the strike zone shrunk to his advantage.
"It wasn't a coincidence that I led the league in walks the next few years," he added. Dykstra led the league with 129 walks in 1993 while with the Phillies. His previous career high was 89 walks, though he missed plenty of time with injuries. Dykstra's walk rate did spike from 1993-94:
Dykstra says he then used the information not necessarily to bribe umpires, but to intimidate them into giving him favorable calls. "Fear does a lot to a man," he says. Here's the video:
"Their blood is just as red as ours. Some of them like women, some of them like men, some of them gamble," said Dykstra. He then imagined a scenario in which he asked the umpire if he "covered the spread last night" after a called strike, then the strike zone shrunk to his advantage.
"It wasn't a coincidence that I led the league in walks the next few years," he added. Dykstra led the league with 129 walks in 1993 while with the Phillies. His previous career high was 89 walks, though he missed plenty of time with injuries. Dykstra's walk rate did spike from 1993-94:
This App Turns Your Smartwatch into an Eavesdropping Device
There are times when being able to easily record audio is a serious advantage in your day to day life. Whether that means you do it for work, school, or anything else, now you can easily do it with Wear Audio Recorder on your Android Wear device. Whether it's a short moment or a full meeting, this app has got you covered.
Wear Audio Recorder has a fantastic look that is both simple and stylish. Unsurprising when you realize that they're using Google's Material Design. On your Smart Watch, this app doesn't have a ton of features. What it does, it does well. Recording is as simple as opening the app, and tapping record. more
Why do I mention it?
So you will know what you're up against.
Wear Audio Recorder has a fantastic look that is both simple and stylish. Unsurprising when you realize that they're using Google's Material Design. On your Smart Watch, this app doesn't have a ton of features. What it does, it does well. Recording is as simple as opening the app, and tapping record. more
Why do I mention it?
So you will know what you're up against.
Wednesday, October 28, 2015
Spies in Space: The Final Frontier in Espionage
Space, the ‘final frontier’, is rapidly becoming an extra-terrestrial battleground for corporate espionage and other types of cyber attack as hackers seek to gain commercial advantage from rival networks operating in the $330-billion space economy...
The amount of data now being beamed between satellites supporting commercial networks on earth is growing rapidly, making them a ripe target for cyber attacks, said Luca del Monte, a senior strategist at the European Space Agency, and one of many experts who attended the annual International Astronautical Congress last week in Israel.
Space presents a double opportunity for hackers – the hardware up in orbit and the information it transmits. more
The amount of data now being beamed between satellites supporting commercial networks on earth is growing rapidly, making them a ripe target for cyber attacks, said Luca del Monte, a senior strategist at the European Space Agency, and one of many experts who attended the annual International Astronautical Congress last week in Israel.
Space presents a double opportunity for hackers – the hardware up in orbit and the information it transmits. more
The 'Spy in a Bag' Case Continues
Gareth Williams was blackmailed with 'staged photos in Las Vegas hotel room' by Russian spies, claims former KGB agent...
A former KGB major says he believes Gareth Williams was murdered by Russian hit men as the MI6 spy refused to become a double agent, even after they blackmailed him by taking compromising, staged photographs.
The former major and intelligence officer Boris Karpichkov, who was exiled from Russia and now lives in the UK with a new identity, told his version of events to The Daily Mail. He claims to have a source high up in Russian intelligence services.
Mr William’s dead body was found locked in a bag in his Pimlico flat in 2010. He has been a codebreaker at GCHQ but at the time was on secondment to MI6 at their offices in Vauxhall, London. more
A former KGB major says he believes Gareth Williams was murdered by Russian hit men as the MI6 spy refused to become a double agent, even after they blackmailed him by taking compromising, staged photographs.
The former major and intelligence officer Boris Karpichkov, who was exiled from Russia and now lives in the UK with a new identity, told his version of events to The Daily Mail. He claims to have a source high up in Russian intelligence services.
Mr William’s dead body was found locked in a bag in his Pimlico flat in 2010. He has been a codebreaker at GCHQ but at the time was on secondment to MI6 at their offices in Vauxhall, London. more
Criptyque Launches Pryvate™, the First Fully Secure Communications Platform
Criptyque, the secure communications provider, today announced the launch of Pryvate™, the first all-encompassing and fully encrypted communications platform for mobile devices. Pryvate secures communication services across email, voice calls, conference calls, video calls and instant messenger to protect consumers and businesses from cybercriminals, intruders, corporate espionage, hackers and more.
The Pryvate application provides triple-layered security powered by top-of-the-line 4096-bit encryption, with AES 256-bit key management and DH key exchange. It offers truly seamless independent, network agnostic security combined with high quality of service at a low cost.
Initially available on Apple and Google Play stores, the service provides security by generating unique encryption keys on the devices of both users who communicate via the application. Once a key is used, a new key is created for every subsequent interaction and auto renew for every call, IM, message, session etc. Pryvate has no access to users’ encryption keys past, present or future: making it impossible to leak, hack, collaborate or give away keys, which makes all communication through Pryvate totally secure and impervious to hacking. more
The Pryvate application provides triple-layered security powered by top-of-the-line 4096-bit encryption, with AES 256-bit key management and DH key exchange. It offers truly seamless independent, network agnostic security combined with high quality of service at a low cost.
Initially available on Apple and Google Play stores, the service provides security by generating unique encryption keys on the devices of both users who communicate via the application. Once a key is used, a new key is created for every subsequent interaction and auto renew for every call, IM, message, session etc. Pryvate has no access to users’ encryption keys past, present or future: making it impossible to leak, hack, collaborate or give away keys, which makes all communication through Pryvate totally secure and impervious to hacking. more
Business Espionage: HSBC Nemesis Falciani Mocks Swiss Justice a Mile From Border
Herve Falciani, the Frenchman wanted on charges of industrial espionage in Switzerland, has opted to skip his trial at the country’s top court and instead plead his case before a jury of journalists at a French hotel, less than a mile from the Swiss border.
The Frenchman was the star attraction at a conference billed “Investigative Journalism in the Time of Wikileaks” Wednesday at the Domaine de Divonne. The hotel and casino is a 20-minute drive from Geneva, where Falciani took client data from HSBC Holdings Plc’s private bank nearly a decade ago. more
The Frenchman was the star attraction at a conference billed “Investigative Journalism in the Time of Wikileaks” Wednesday at the Domaine de Divonne. The hotel and casino is a 20-minute drive from Geneva, where Falciani took client data from HSBC Holdings Plc’s private bank nearly a decade ago. more
Tuesday, October 27, 2015
What's in The Washington Post basement?
Nixon tapes and Cold War spy photos.
Deep in the basement of the Washington Post newsroom, national security reporter Walter Pincus is rediscovering 40 years worth of handwritten notes, White House telephone records and declassified spy photos. As the Post prepares to move into a new building in December, he’s digging up details on many of the historical stories he’s worked on. (Jorge Ribas and Jayne W. Orenstein / The Washington Post) more
Deep in the basement of the Washington Post newsroom, national security reporter Walter Pincus is rediscovering 40 years worth of handwritten notes, White House telephone records and declassified spy photos. As the Post prepares to move into a new building in December, he’s digging up details on many of the historical stories he’s worked on. (Jorge Ribas and Jayne W. Orenstein / The Washington Post) more
Corporate Espionage that Flies Below the Radar
by Kevin G. Coleman, SilverRhino
Headlines about economic, corporate and industrial espionage have been in abundance lately and for good reason... Several subject matter experts agree that much of these espionage activities that target businesses are criminal-based.
Recently while on the executive floor of one large company a new twist to espionage tradecraft popped up.
After entering a conference room, a note on the whiteboard caught my attention: “DO NOT ERASE.” Seeing that on a whiteboard filled with financial numbers, notes, diagrams and so on is not an uncommon occurrence. When I was looking out the windows, I saw a drone slowly fly by. Given the camera capabilities that are now available and becoming common on drones, it would not be difficult to capture what was on those whiteboards. The images are digitally captured, cropped, enhanced extracted and then sold...
Today economic, corporate and industrial espionage is big business. With significant money being made selling corporate secrets, this threat will only grow. more
Headlines about economic, corporate and industrial espionage have been in abundance lately and for good reason... Several subject matter experts agree that much of these espionage activities that target businesses are criminal-based.
Recently while on the executive floor of one large company a new twist to espionage tradecraft popped up.
 |
| Drone at office window story. |
Today economic, corporate and industrial espionage is big business. With significant money being made selling corporate secrets, this threat will only grow. more
His Spy Got Caught and was Arrested. The Handler Disavowes it as "Silly"
David Vitter calls spying arrest ‘silly’; Sheriff Newell Normand says Vitter would be ‘worst governor in Louisiana history’
Louisiana - The bungled political espionage that unfolded hours before Saturday’s election has exposed and perhaps deepened the enmity between U.S. Sen. David Vitter and Jefferson Parish Sheriff Newell Normand, fellow Republicans who traded barbs Monday as Vitter turned his attention to the gubernatorial runoff next month.
The animus between the two elected officials traces its roots to a similar split between Vitter and the late Harry Lee, Normand’s combative predecessor. And the relationship appears to have reached a nadir after Normand caught a private investigator hired by Vitter’s campaign secretly recording the sheriff’s regular coffee gathering at the Royal Blend cafe in Old Metairie. more
Louisiana - The bungled political espionage that unfolded hours before Saturday’s election has exposed and perhaps deepened the enmity between U.S. Sen. David Vitter and Jefferson Parish Sheriff Newell Normand, fellow Republicans who traded barbs Monday as Vitter turned his attention to the gubernatorial runoff next month.
The animus between the two elected officials traces its roots to a similar split between Vitter and the late Harry Lee, Normand’s combative predecessor. And the relationship appears to have reached a nadir after Normand caught a private investigator hired by Vitter’s campaign secretly recording the sheriff’s regular coffee gathering at the Royal Blend cafe in Old Metairie. more
Monday, October 26, 2015
A Tale of Two Law Suits - Eavesdroppers Won, Targets Zero
Facebook Wins Dismissal Of $15 Billion Privacy Lawsuit
It’s been more than three years since a federal judge in California heard arguments in a large class-action lawsuit filed against Facebook over its questionable privacy practices. Finally, on Friday that judge sided with the social network and threw out the case — while leaving open the option for plaintiffs to revise and re-file their case.
The complaint involves Facebook’s tracking of users both while they are logged in as Facebook users and after they log off.
The plaintiffs argued that, in exchange for offering free access to Facebook, the company “conditions its membership upon users providing sensitive and personal information… including name, birth date, gender and e-mail address,” and requires that users accept numerous Facebook “cookies” on their web browsers that allow Facebook to track that a user’s Internet browsing history — which is then marketed to advertisers.
Of particular concern to the plaintiffs was Facebook’s continued tracking of users even after they had logged out of Facebook. more
ACLU lawsuit against NSA mass spying dropped in federal court
A federal district court on Friday dismissed a lawsuit brought by the American Civil Liberties Union against the National Security Agency over its mass surveillance program.
Ashley Gorski, a staff attorney with the ACLU national security project told The Guardian the mass spying program was innately harmful, arguing it violates “our clients’ constitutional rights to privacy, freedom of speech, and freedom of association, and it poses a grave threat to a free internet and a free society.” more
It’s been more than three years since a federal judge in California heard arguments in a large class-action lawsuit filed against Facebook over its questionable privacy practices. Finally, on Friday that judge sided with the social network and threw out the case — while leaving open the option for plaintiffs to revise and re-file their case.
The complaint involves Facebook’s tracking of users both while they are logged in as Facebook users and after they log off.
The plaintiffs argued that, in exchange for offering free access to Facebook, the company “conditions its membership upon users providing sensitive and personal information… including name, birth date, gender and e-mail address,” and requires that users accept numerous Facebook “cookies” on their web browsers that allow Facebook to track that a user’s Internet browsing history — which is then marketed to advertisers.
Of particular concern to the plaintiffs was Facebook’s continued tracking of users even after they had logged out of Facebook. more
ACLU lawsuit against NSA mass spying dropped in federal court
A federal district court on Friday dismissed a lawsuit brought by the American Civil Liberties Union against the National Security Agency over its mass surveillance program.
Ashley Gorski, a staff attorney with the ACLU national security project told The Guardian the mass spying program was innately harmful, arguing it violates “our clients’ constitutional rights to privacy, freedom of speech, and freedom of association, and it poses a grave threat to a free internet and a free society.” more
A Downer for Drones
There's recently been a run of new anti-drone systems introduced to deal
with potential threats from UAVs, but these have been on the large and
expensive side. To provide an affordable alternatives to plug the gap
between shotguns and truck-mounted systems, national security research
and development firm Battelle is introducing DroneDefender. Billed as
the first portable, accurate, rapid-to-use UAV counter-weapon, it's a
rifle-like raygun device that uses a radio beam to jam drone control
systems and stop them in midair. more
Get Ready for Spectre - Battle of the Bonds Infographic
Battle of the Bonds: Kisses, Cocktails, Kills, Cars & Cash – An infographic by the team at GB Show Plates
Monday, October 5, 2015
Jealous Wives and Girlfriends Can Now Snoop on their Partner using a Spy Belt
Jealous wives and girlfriends can snoop on their fellas with a spy gadget disguised as a belt.
A tracking device hidden in the leather monitors the wearer’s location every 60 seconds. And it can be controlled remotely through Android and iPhone apps without the wearer noticing.
Unwary men could receive one as a present without knowing what they have let themselves in for.
The Belt Tracker, sold by Spymaster, in Marylebone, London, has a 12-hour battery life and can be used in 220 countries without incurring data roaming charges. It even has a flight safe mode to comply with airline regulations.
The GPS device was originally designed to monitor people working in dangerous environments, such as undercover police. And it can be used to track children and give peace of mind to parents. more
A tracking device hidden in the leather monitors the wearer’s location every 60 seconds. And it can be controlled remotely through Android and iPhone apps without the wearer noticing.
Unwary men could receive one as a present without knowing what they have let themselves in for.
The Belt Tracker, sold by Spymaster, in Marylebone, London, has a 12-hour battery life and can be used in 220 countries without incurring data roaming charges. It even has a flight safe mode to comply with airline regulations.
The GPS device was originally designed to monitor people working in dangerous environments, such as undercover police. And it can be used to track children and give peace of mind to parents. more
Scientist Pleads Guilty to Corporate Espionage
Researcher Xiwen Huang pleaded guilty Friday to one count of stealing trade secrets. But the legal battle over the punishment the former Charlotte resident receives already is underway.
Federal prosecutors say the 55-year-old chemical engineer stole proprietary technology and hundreds of pages of documents over the last decade from his government and civilian employers, including a company in Charlotte. Huang’s goal, according to court documents, was to aid both the Chinese government and his own company, which he started in North Carolina to do business in his Asian homeland.
Huang faces a maximum penalty of 10 years in prison and a $250,000 fine. He will be sentenced at a later date. Imprisonment is all but certain. more
Federal prosecutors say the 55-year-old chemical engineer stole proprietary technology and hundreds of pages of documents over the last decade from his government and civilian employers, including a company in Charlotte. Huang’s goal, according to court documents, was to aid both the Chinese government and his own company, which he started in North Carolina to do business in his Asian homeland.
Huang faces a maximum penalty of 10 years in prison and a $250,000 fine. He will be sentenced at a later date. Imprisonment is all but certain. more
Ai Weiwei Discovers Eavesdropping Devices in His Studio
Ai Weiwei has posted a number of pictures of what he says are listening devices found in his Beijing studio.
The Chinese dissident artist captioned one photo of a bug on Instagram with "There will always be surprises".
His friend Liu Xiaoyuan confirmed the bugs were found after the artist returned from a trip to Germany.
Xiaoyuan tweeted that they were found when redecoration started on Ai's home and were found in the office and a living room.
The artist also posted a video clip of firecrackers being set off in a metal bucket next to one of the devices. He wrote "Did you hear it?" next to the video. more
The Chinese dissident artist captioned one photo of a bug on Instagram with "There will always be surprises".
His friend Liu Xiaoyuan confirmed the bugs were found after the artist returned from a trip to Germany.
Xiaoyuan tweeted that they were found when redecoration started on Ai's home and were found in the office and a living room.
The artist also posted a video clip of firecrackers being set off in a metal bucket next to one of the devices. He wrote "Did you hear it?" next to the video. more
Subscribe to:
Comments (Atom)