One afternoon, security researcher Hristo Bojinov placed his Galaxy Nexus phone face up on the table in a cramped Palo Alto conference room. Then he flipped it over and waited another beat. And that was it. In a matter of seconds, the device had given up its "fingerprints."
Code running on the website in the device's mobile browser measured the tiniest defects in the device's accelerometer — the sensor that tracks movement — producing a unique set of numbers that advertisers could exploit to identify and track most modern smartphones.
The accelerometer enables, among other things, the browser to shift from landscape to vertical as a user tilts the phone. It turns out every accelerometer is predictably imperfect, and slight differences in the readings can be used to produce a fingerprint. Marketers could use the ID the same way they use cookies — the small files that download from websites to desktops — to identify particular users, monitor their online actions and target ads accordingly.
It's a novel approach that raises a new set of privacy concerns: Users couldn't delete the ID like browser cookies, couldn't mask it by adjusting app privacy preferences — and wouldn't even know their device had been tagged. (more)
Monday, November 4, 2013
Sunday, November 3, 2013
When Paranoids Collide they Blow the Whistle on Tea Kettles
Customs agents in Russia found tea kettles and irons bugged with tiny Spyware chips that exploit WiFi connections, reports a local news outlet coming out of St. Petersburg.
According to Gizmodo, the microchips are capable of spreading spam and malware to WiFi-enabled devices within 200 meters. Specific details of the dodgy shipments remain shady...
Simon Sharwood of The Register reports that it is indeed possible to build a spambot small enough to fit inside of a kettle, as the necessary components are small and cheap enough...
One question remains unanswered, however: why would China send bugged tea kettles to spy on the ordinary tea-drinkers of Russia?
Gizmodo suggests that perhaps local authorities were mistaken about their findings, pointing out that WiFi tea kettles already exist.
Business Insider speculates that if the kettles are bugged, it could very well be a test for larger operations to plant such microchips.
We'll let you weave your own intricate conspiracy theory. (more)
According to Gizmodo, the microchips are capable of spreading spam and malware to WiFi-enabled devices within 200 meters. Specific details of the dodgy shipments remain shady...
Simon Sharwood of The Register reports that it is indeed possible to build a spambot small enough to fit inside of a kettle, as the necessary components are small and cheap enough...
One question remains unanswered, however: why would China send bugged tea kettles to spy on the ordinary tea-drinkers of Russia?
Gizmodo suggests that perhaps local authorities were mistaken about their findings, pointing out that WiFi tea kettles already exist.
Business Insider speculates that if the kettles are bugged, it could very well be a test for larger operations to plant such microchips.
We'll let you weave your own intricate conspiracy theory. (more)
Labels:
eavesdropping,
government,
Hack,
product,
spybot,
weird,
Wi-Fi
This Judge is a Surveillance Expert. He has Cred.
James G. Carr ’62, a senior judge on the U.S. District Court for the Northern District of Ohio and a former member of the Foreign Intelligence Surveillance Court (FISC), described the process through which the federal government conducts electronic surveillance and railed against National Security Agency (NSA) whistleblower Edward Snowden in a talk in the Gund Gallery’s Community Foundation Theater...
Carr told his audience “every one of us in this room probably has been overheard under a FISA warrant... It’s a general search,” Carr said, “that which the Fourth Amendment most directly and most clearly, unequivocally prohibits. Nobody can dispute that.”...
In July, Carr wrote an op-ed in The New York Times calling for Congress to reform the court. He suggested judges be allowed to appoint outside lawyers to “represent the interests of the Constitution and the public” in cases where a novel issue, such as new surveillance technology, is present in the warrant application. Government agents are required to inform the court if their application raises that kind of issue...
Carr had harsh words for Edward Snowden, the former NSA contractor who provided documents about NSA surveillance procedures to journalists before fleeing to Hong Kong and then Russia. He asked audience members how many of them thought Snowden’s actions were worthwhile, and upon seeing hands raise, said, “I want to try and disabuse you of that view.”
 Snowden, he said, had been “in the hands of the Chinese and the Russians for months, and if anybody in this room thinks for a moment that they don’t know everything he learned … c’mon now.”
Snowden, he said, had been “in the hands of the Chinese and the Russians for months, and if anybody in this room thinks for a moment that they don’t know everything he learned … c’mon now.”
The NSA, Carr said, “does a crucially important job,” whereas Snowden, whom he mockingly called “the great American patriot,” had done “irredeemable” damage.
In the Q & A after the talk, one student asked Carr, “Why bother protecting our lives if you don’t first protect our rights?” Carr responded, “Because if we have no lives, we have no rights.” (more)
Why is Carr the expert?
Because he wrote the book. (more)
Carr told his audience “every one of us in this room probably has been overheard under a FISA warrant... It’s a general search,” Carr said, “that which the Fourth Amendment most directly and most clearly, unequivocally prohibits. Nobody can dispute that.”...
In July, Carr wrote an op-ed in The New York Times calling for Congress to reform the court. He suggested judges be allowed to appoint outside lawyers to “represent the interests of the Constitution and the public” in cases where a novel issue, such as new surveillance technology, is present in the warrant application. Government agents are required to inform the court if their application raises that kind of issue...
Carr had harsh words for Edward Snowden, the former NSA contractor who provided documents about NSA surveillance procedures to journalists before fleeing to Hong Kong and then Russia. He asked audience members how many of them thought Snowden’s actions were worthwhile, and upon seeing hands raise, said, “I want to try and disabuse you of that view.”
 Snowden, he said, had been “in the hands of the Chinese and the Russians for months, and if anybody in this room thinks for a moment that they don’t know everything he learned … c’mon now.”
Snowden, he said, had been “in the hands of the Chinese and the Russians for months, and if anybody in this room thinks for a moment that they don’t know everything he learned … c’mon now.” The NSA, Carr said, “does a crucially important job,” whereas Snowden, whom he mockingly called “the great American patriot,” had done “irredeemable” damage.
In the Q & A after the talk, one student asked Carr, “Why bother protecting our lives if you don’t first protect our rights?” Carr responded, “Because if we have no lives, we have no rights.” (more)
Why is Carr the expert?
Because he wrote the book. (more)
Labels:
book,
eavesdropping,
government,
law,
mores,
NSA,
privacy,
surveillance
10 Most Audacious Eavesdropping Plots
Operation Ivy Bells
At the height of the cold war, the National Security Agency, CIA and the US Navy collaborated to tap into underwater communication lines used by the Soviet Union.
Operation Stopwatch
This joint operation between the CIA and the British Secret Intelligence Service was again an attempt to tap into communications by the Soviet Military.
The Cambridge Spies
Rather than relying on modern eavesdropping, this operation used old fashioned infiltration.
The Gunman Project
During 1976, the KGB managed to install miniaturized eavesdropping equipment and transmitters inside 16 IBM Selectric Typewriters used by staff at the US embassy in Moscow and consulate in Leningrad.
The Bundesnachrichtendienst Trojan Horse Affair
Germany may have been the victim off NSA eavesdropping, but its own Federal Intelligence Service, the Bundesnachrichtendienst, has also engaged in such activities.
The MI6 Spy Rock
In a modern version of the dead letter drop, British spies working out of the embassy in Russia used a transmitter concealed in an artificial rock to pass classified data.
Acoustic Kitty
Acoustic Kitty was a top secret 1960s CIA project attempting to use cats in spy missions, intended to spy on the Kremlin and Soviet embassies. (more)
 In
1956, American and British agents tunneled into East German territory
in order to tap a telephone line. This allowed them to eavesdrop on
important conversations between Red Army leaders and the KGB. A segment
of the tunnel can now be visited. (more)
In
1956, American and British agents tunneled into East German territory
in order to tap a telephone line. This allowed them to eavesdrop on
important conversations between Red Army leaders and the KGB. A segment
of the tunnel can now be visited. (more)
U2
An international diplomatic crisis erupted in May 1960 when the Union of Soviet Socialist Republics (USSR) shot down an American U-2 spy plane in Soviet air space and captured its pilot, Francis Gary Powers. Confronted with the evidence of his nation's espionage, President Dwight D. Eisenhower was forced to admit to the Soviets that the U.S. Central Intelligence Agency (CIA) had been flying spy missions over the USSR for several years. (more)
Animal Spies
A former CIA trainer reveals, the U.S. government deployed nonhuman operatives—ravens, pigeons, even cats—to spy on cold war adversaries. “We never found an animal we could not train.” (more)
At the height of the cold war, the National Security Agency, CIA and the US Navy collaborated to tap into underwater communication lines used by the Soviet Union.
Operation Stopwatch
This joint operation between the CIA and the British Secret Intelligence Service was again an attempt to tap into communications by the Soviet Military.
The Cambridge Spies
Rather than relying on modern eavesdropping, this operation used old fashioned infiltration.
 |
| Click to enlarge. |
During 1976, the KGB managed to install miniaturized eavesdropping equipment and transmitters inside 16 IBM Selectric Typewriters used by staff at the US embassy in Moscow and consulate in Leningrad.
The Bundesnachrichtendienst Trojan Horse Affair
Germany may have been the victim off NSA eavesdropping, but its own Federal Intelligence Service, the Bundesnachrichtendienst, has also engaged in such activities.
The MI6 Spy Rock
In a modern version of the dead letter drop, British spies working out of the embassy in Russia used a transmitter concealed in an artificial rock to pass classified data.
Acoustic Kitty
Acoustic Kitty was a top secret 1960s CIA project attempting to use cats in spy missions, intended to spy on the Kremlin and Soviet embassies. (more)
Moles in Berlin
U2
An international diplomatic crisis erupted in May 1960 when the Union of Soviet Socialist Republics (USSR) shot down an American U-2 spy plane in Soviet air space and captured its pilot, Francis Gary Powers. Confronted with the evidence of his nation's espionage, President Dwight D. Eisenhower was forced to admit to the Soviets that the U.S. Central Intelligence Agency (CIA) had been flying spy missions over the USSR for several years. (more)
Animal Spies
A former CIA trainer reveals, the U.S. government deployed nonhuman operatives—ravens, pigeons, even cats—to spy on cold war adversaries. “We never found an animal we could not train.” (more)
Labels:
aerial,
CIA,
eavesdropping,
espionage,
government,
Hack,
historical,
KGB,
MI6,
nature,
NSA,
social engineering,
telephone,
wireless,
wiretapping
What Corporations Can Learn from the Vatican
Contrary to a widely circulated report, the US National Security Agency (NSA) could not have eavesdropped on the conclave that elected Pope Francis, a veteran Vatican journalist has reported.
Andrea Tornielli of La Stampa writes that the Vatican had deployed sophisticated anti-bugging technology in the Sistine Chapel and throughout the apostolic palace in the days leading up to the conclave. The anti-bugging measures were already in place during the general congregations at which cardinals exchanged ideas prior to the opening of the conclave. Reporters who were in the building testified that internet connections were interrupted and cell-phone signals lost when the system was activated.
Vatican security experts take pride in their ability to foil espionage, Tornielli reports. (more)
Andrea Tornielli of La Stampa writes that the Vatican had deployed sophisticated anti-bugging technology in the Sistine Chapel and throughout the apostolic palace in the days leading up to the conclave. The anti-bugging measures were already in place during the general congregations at which cardinals exchanged ideas prior to the opening of the conclave. Reporters who were in the building testified that internet connections were interrupted and cell-phone signals lost when the system was activated.
Vatican security experts take pride in their ability to foil espionage, Tornielli reports. (more)
Can a Perv Skirt Privacy Laws by Raising The First Amendment?
MA - An Andover man is hoping to slip past the law by arguing women in skirts are taking a chance when they ride the T (Boston's transit system) because there’s no guarantee of privacy.
Michael Robertson is appealing to the state’s highest court saying he didn’t commit a crime when he allegedly tried to take cellphone photos up women’s dresses on the Green Line in August 2010.
That “up-skirt” case included an undercover transit cop and another T passenger. The 31-year-old now faces more than two years in jail if convicted of two counts of photographing an unsuspecting nude or partially nude person.
His lawyer argues it’s the outdated law that’s in the wrong — not her (sic) client — and other photographers could have their First Amendment rights trampled, too. (more)
Michael Robertson is appealing to the state’s highest court saying he didn’t commit a crime when he allegedly tried to take cellphone photos up women’s dresses on the Green Line in August 2010.
That “up-skirt” case included an undercover transit cop and another T passenger. The 31-year-old now faces more than two years in jail if convicted of two counts of photographing an unsuspecting nude or partially nude person.
His lawyer argues it’s the outdated law that’s in the wrong — not her (sic) client — and other photographers could have their First Amendment rights trampled, too. (more)
Music to Spy By
via Jason Whiton, SpyVibe.blogspot.com...The UK distributor, Network (the "Criterion Collection" of retro TV/Film), has been tempting us for some time with news of upcoming remastered vinyl soundtracks from spy shows like The Prisoner, Department S, and The Saint. Some lucky collectors in Britain even had a chance to pick up a limited-edition EP of spy tunes during the last Record Store Day.
From Network's On Air newsletter: "It’s a measure of the quality of the music from these series that it can be enjoyed outside of the context of the programmes themselves, as our previous soundtrack releases on CD have demonstrated.
Now, with the resurgence of interest in that formerly archaic artefact the LP record, we’re proud to present the first in a series of brand-new audiophile releases on 180g virgin vinyl.
Although high-quality masters were already available from the CD releases, we have returned to the original analogue tapes which have been mastered afresh for vinyl to take advantage of the format’s more subtle dynamic range. Mastering and vinyl cutting have been supervised by one of the very best in the business – Ray Staff of AIR Studios – ensuring that these tracks have never sounded so good since they went down onto tape in the late 1960s." (more)
From Network's On Air newsletter: "It’s a measure of the quality of the music from these series that it can be enjoyed outside of the context of the programmes themselves, as our previous soundtrack releases on CD have demonstrated.
Now, with the resurgence of interest in that formerly archaic artefact the LP record, we’re proud to present the first in a series of brand-new audiophile releases on 180g virgin vinyl.
Although high-quality masters were already available from the CD releases, we have returned to the original analogue tapes which have been mastered afresh for vinyl to take advantage of the format’s more subtle dynamic range. Mastering and vinyl cutting have been supervised by one of the very best in the business – Ray Staff of AIR Studios – ensuring that these tracks have never sounded so good since they went down onto tape in the late 1960s." (more)
Saturday, November 2, 2013
High School Football Spying?!?! - Four Destrehan Coaches Accused
LA - Five people, including four Destrehan High School assistant football coaches, were booked with unauthorized use of intellectual property Wednesday after they allegedly used a leaked computer password to get a sneak peek at the game plan of their upcoming opponent, South Lafourche.
Others could still be charged, said Brennan Matherne, public information officer for the Lafourche Parish Sheriff’s Office...
The criminal charges are the latest fallout stemming from an incident in which the coaches allegedly used computers to spy on South Lafourche’s football practices last week.
The scandal already has resulted in a forfeit for Destrehan and sanctions for the coaches involved. (more)
Others could still be charged, said Brennan Matherne, public information officer for the Lafourche Parish Sheriff’s Office...
The criminal charges are the latest fallout stemming from an incident in which the coaches allegedly used computers to spy on South Lafourche’s football practices last week.
The scandal already has resulted in a forfeit for Destrehan and sanctions for the coaches involved. (more)
Encryptor's Unite! - From Those Wonderful Folks Who Brought You Lavabit & Silent Circle
Our Mission - To bring the world our unique end-to-end encrypted protocol and architecture that is the 'next-generation' of private and secure email.
 As founding partners of The Dark Mail Alliance, both Silent Circle and Lavabit will work to bring other members into the alliance, assist them in implementing the new protocol and jointly work to proliferate the worlds first end-to-end encrypted 'Email 3.0' throughout the world's email providers.
As founding partners of The Dark Mail Alliance, both Silent Circle and Lavabit will work to bring other members into the alliance, assist them in implementing the new protocol and jointly work to proliferate the worlds first end-to-end encrypted 'Email 3.0' throughout the world's email providers.
Our goal is to open source the protocol and architecture and help others implement this new technology to address privacy concerns against surveillance and back door threats of any kind. (more)
 As founding partners of The Dark Mail Alliance, both Silent Circle and Lavabit will work to bring other members into the alliance, assist them in implementing the new protocol and jointly work to proliferate the worlds first end-to-end encrypted 'Email 3.0' throughout the world's email providers.
As founding partners of The Dark Mail Alliance, both Silent Circle and Lavabit will work to bring other members into the alliance, assist them in implementing the new protocol and jointly work to proliferate the worlds first end-to-end encrypted 'Email 3.0' throughout the world's email providers. Our goal is to open source the protocol and architecture and help others implement this new technology to address privacy concerns against surveillance and back door threats of any kind. (more)
Labels:
email,
encryption,
FutureWatch,
Hack,
privacy,
product,
software,
trade secret
In the Days Before Spread Spectrum Communications - Spread Wings Communications
Read all about America's secure communications laboratory, just miles from the Countermeasures Compound, in Ft. Monmouth, NJ... (more)
Friday, November 1, 2013
Mobile Phone Use a Significant Security Risk for Companies
New research suggests that companies are leaving themselves open to potentially serious security and legal risks by employees’ improper use of corporate mobile devices.
Experts from the University of Glasgow looked at a sample of mobile phones returned by the employees from one Fortune 500 company and found that they were able to retrieve large amounts of sensitive corporate and personal information. The loss of data such as this has potential security risks, inviting breaches on both an individual and corporate level.
A University of Glasgow release reports that the data yielded by this study on thirty-two handsets included a number of items that could potentially cause significant security risks and, lead to the leakage of valuable intellectual property or exposed the company to legal conflicts. (more)
 |
| Buy them the Cone of Silence. |
A University of Glasgow release reports that the data yielded by this study on thirty-two handsets included a number of items that could potentially cause significant security risks and, lead to the leakage of valuable intellectual property or exposed the company to legal conflicts. (more)
Wednesday, October 30, 2013
Kremlin Alledegly Slipped Spy Gadgets into G20 Summit Gift Bags
Russian hosts of the Group of 20 summit near St. Petersburg in September sent world leaders home with gifts designed to keep on giving: memory sticks and recharging cables programmed to spy on their communications, two Italian newspapers reported Tuesday.
A Kremlin spokesman denied the allegations reported by Il Corriere della Sera and La Stampa, both of which attributed their stories to findings of technical investigations ordered by the president of the European Council and carried out by German intelligence.
The USB thumb drives marked with the Russia G20 logo and the three-pronged European phone chargers were "a poisoned gift" from Russian President Vladimir Putin, Turin-based La Stampa said in its report.
“They were Trojan horses designed to obtain information from computers and cellphones,” the paper said.
The bugging devices were included in gift bags given to all delegates who attended the Sept. 5-6 summit at the palace in Stelna, outside of St. Petersburg, the newspapers said. (more)
Too obvious to be true?
You decide.
A Kremlin spokesman denied the allegations reported by Il Corriere della Sera and La Stampa, both of which attributed their stories to findings of technical investigations ordered by the president of the European Council and carried out by German intelligence.
The USB thumb drives marked with the Russia G20 logo and the three-pronged European phone chargers were "a poisoned gift" from Russian President Vladimir Putin, Turin-based La Stampa said in its report.
“They were Trojan horses designed to obtain information from computers and cellphones,” the paper said.
The bugging devices were included in gift bags given to all delegates who attended the Sept. 5-6 summit at the palace in Stelna, outside of St. Petersburg, the newspapers said. (more)
Too obvious to be true?
You decide.
Monday, October 28, 2013
Do You Have an IT Spy Guy?
Two tales to get you thinking...
Old tech equipment rarely dies, it just finds a new home -- and sometimes, that home is with your IT employees... The problem with taking equipment bound for the scrap heap or the recycling bin is that it often still contains sensitive data, which if lost could result in massive liability for the company that owns the equipment. Think... It is more than just theft, much more.
"There are no secrets for IT," says Pierluigi Stella, CTO for managed security service provider Network Box USA. "I can run a sniffer on my firewall and see every single packet that comes in and out of a specific computer. I can see what people write in their messages, where they go to on the Internet, what they post on Facebook. In fact, only ethics keep IT people from misusing and abusing this power. Think of it as having a mini-NSA in your office." Also think... "The scariest thing is that the same people who present the greatest risk are often the very people who approve access." (more)
Old tech equipment rarely dies, it just finds a new home -- and sometimes, that home is with your IT employees... The problem with taking equipment bound for the scrap heap or the recycling bin is that it often still contains sensitive data, which if lost could result in massive liability for the company that owns the equipment. Think... It is more than just theft, much more.
"There are no secrets for IT," says Pierluigi Stella, CTO for managed security service provider Network Box USA. "I can run a sniffer on my firewall and see every single packet that comes in and out of a specific computer. I can see what people write in their messages, where they go to on the Internet, what they post on Facebook. In fact, only ethics keep IT people from misusing and abusing this power. Think of it as having a mini-NSA in your office." Also think... "The scariest thing is that the same people who present the greatest risk are often the very people who approve access." (more)
Saturday, October 26, 2013
Business Espionage in America - We Lose More Than We Take in Taxes
The United States has known for sometime that it has been victimized by economic espionage mounted by other countries, especially China and Russia. According to a counterintelligence expert hired by companies to help them counter this threat, the toll for these crimes is far, far higher than what has been officially reported.
Economic espionage represents “the greatest transfer of wealth in history,” said General Keith Alexander, NSA director and commander of U.S. Cyber Command, at the American Enterprise Institute in 2012...
Due to the nature of the business, it is often difficult to place solid numbers on the cost of economic espionage. To protect their investors, companies rarely want to announce breaches by spies or hackers to the public, and government agents often find gathering enough evidence to charge an insider with espionage difficult.
The lack of transparency on economic espionage makes it a difficult problem to tackle.
The FBI estimates that economic espionage costs the U.S. $13 billion a year, yet their numbers are based only on current FBI cases where spies have been caught and charged. It does not include the majority of theft that was not reported, or the scale of breaches that are unknown to the companies...
During his speech, General Alexander said investigations by the FBI and other agencies find that for every company that detects a cyberattack there are 100 others that are unknowingly being hacked...
Nonetheless, U.S. companies are still largely on their own when it comes to defending against economic espionage, and the threat is very real. When the “Economic Espionage Penalty Enhancement Act of 2011″ was passed, former U.S. Senator Herb Kohl said in a press release “As much as 80 percent of the assets of today’s companies are intangible trade secrets.” (more)
You don't have to be on your own. Help is available. Call me.
Economic espionage represents “the greatest transfer of wealth in history,” said General Keith Alexander, NSA director and commander of U.S. Cyber Command, at the American Enterprise Institute in 2012...
Due to the nature of the business, it is often difficult to place solid numbers on the cost of economic espionage. To protect their investors, companies rarely want to announce breaches by spies or hackers to the public, and government agents often find gathering enough evidence to charge an insider with espionage difficult.
The lack of transparency on economic espionage makes it a difficult problem to tackle.
The FBI estimates that economic espionage costs the U.S. $13 billion a year, yet their numbers are based only on current FBI cases where spies have been caught and charged. It does not include the majority of theft that was not reported, or the scale of breaches that are unknown to the companies...
During his speech, General Alexander said investigations by the FBI and other agencies find that for every company that detects a cyberattack there are 100 others that are unknowingly being hacked...
Nonetheless, U.S. companies are still largely on their own when it comes to defending against economic espionage, and the threat is very real. When the “Economic Espionage Penalty Enhancement Act of 2011″ was passed, former U.S. Senator Herb Kohl said in a press release “As much as 80 percent of the assets of today’s companies are intangible trade secrets.” (more)
You don't have to be on your own. Help is available. Call me.
Ankle Bracelets Have Criminals Bugged
Ankle bracelets featuring GPS tracking technology can do more than allow authorities to follow the whereabouts of criminals ordered to wear them. They also can be used to eavesdrop on conversations without the wearer knowing what’s going on.
In Puerto Rico, defense lawyer Fermín L. Arraiza-Navas learned about the bracelet’s expanded surveillance capabilities after meeting with clients fitted with the technology. He told the Puerto Rico Center for Investigative Reporting (CPIPR) that clients noticed the bracelets would vibrate when having conversations with lawyers and others.
One client said authorities spoke to him through a hidden phone feature included in the bracelets, which are manufactured by a Utah-based company, SecureAlert. (more)
In Puerto Rico, defense lawyer Fermín L. Arraiza-Navas learned about the bracelet’s expanded surveillance capabilities after meeting with clients fitted with the technology. He told the Puerto Rico Center for Investigative Reporting (CPIPR) that clients noticed the bracelets would vibrate when having conversations with lawyers and others.
One client said authorities spoke to him through a hidden phone feature included in the bracelets, which are manufactured by a Utah-based company, SecureAlert. (more)
Friday, October 25, 2013
A Brilliant Halloween Costume, More LED Fun, and a tip of the tin foil hat to the ultimate paranoid!
It's Friday.
Oddball time!
Weekend Electronics Project
Extreme LED Throwies
 LED throwies are cheery glow-dots you can make in seconds from simple
components and stick to any ferro-magnetic surface. But that’s just the
beginning — click link to learn how to hack and modify them. Easy to make!
LED throwies are cheery glow-dots you can make in seconds from simple
components and stick to any ferro-magnetic surface. But that’s just the
beginning — click link to learn how to hack and modify them. Easy to make!
...and an anti-NSA home... (just kidding)
Oddball time!
Weekend Electronics Project
Extreme LED Throwies
 |
| Click to enlarge. |
 LED throwies are cheery glow-dots you can make in seconds from simple
components and stick to any ferro-magnetic surface. But that’s just the
beginning — click link to learn how to hack and modify them. Easy to make!
LED throwies are cheery glow-dots you can make in seconds from simple
components and stick to any ferro-magnetic surface. But that’s just the
beginning — click link to learn how to hack and modify them. Easy to make!...and an anti-NSA home... (just kidding)
Wednesday, October 23, 2013
Citing "Terrifying" Surveillance Tactics, Yet Another U.S. Privacy Service Shuts Down
Yet another American Internet privacy service has bitten the dust, prompted by fears about broad government surveillance demands.
San Francisco-based CryptoSeal, a provider of virtual private networks that can be used to browse the Internet anonymously, has closed its doors to users of its private VPN service.
In a statement posted online, CryptoSeal announced that a key factor in the closure was the government’s recently revealed attempt to force email provider Lavabit to turn over its private encryption keys. Lavabit shut down in August as part of an effort to resist a surveillance demand believed to involve NSA whistle-blower Edward Snowden, who was a Lavabit customer. Lavabit was ordered to turn over its master encryption keys in a way that could have potentially compromised thousands of users’ private data. (more)
San Francisco-based CryptoSeal, a provider of virtual private networks that can be used to browse the Internet anonymously, has closed its doors to users of its private VPN service.
In a statement posted online, CryptoSeal announced that a key factor in the closure was the government’s recently revealed attempt to force email provider Lavabit to turn over its private encryption keys. Lavabit shut down in August as part of an effort to resist a surveillance demand believed to involve NSA whistle-blower Edward Snowden, who was a Lavabit customer. Lavabit was ordered to turn over its master encryption keys in a way that could have potentially compromised thousands of users’ private data. (more)
Labels:
business,
email,
encryption,
government,
Internet,
mores,
password
Court Rules: NO GPS for LEOs w/o CO
A federal appeals court has ruled that law enforcement officials must obtain a warrant before attaching a GPS unit to a suspect’s car and tracking them...
“Today’s decision is a victory for all Americans because it ensures that the police cannot use powerful tracking technology without court supervision and a good reason to believe it will turn up evidence of wrongdoing,” American Civil Liberties Union attorney Catherine Crump said in a statement. “These protections are important because where people go reveals a great deal about them, from who their friends are, where they visit the doctor and where they choose to worship.”
The three-judge panel determined that installing GPS technology was a violation of the Fourth Amendment to the US constitution, which prohibits unreasonable searches and seizures. The judges’ final decision said the actions of the police were “highly disconcerting.” (more)
“Today’s decision is a victory for all Americans because it ensures that the police cannot use powerful tracking technology without court supervision and a good reason to believe it will turn up evidence of wrongdoing,” American Civil Liberties Union attorney Catherine Crump said in a statement. “These protections are important because where people go reveals a great deal about them, from who their friends are, where they visit the doctor and where they choose to worship.”
The three-judge panel determined that installing GPS technology was a violation of the Fourth Amendment to the US constitution, which prohibits unreasonable searches and seizures. The judges’ final decision said the actions of the police were “highly disconcerting.” (more)
Rental Company Settles Spyware Case
The Federal Trade Commission says Atlanta-based furniture renter Aaron's Inc. has agreed to a settlement over allegations that it helped place spyware on computers that secretly monitored consumers by taking webcam pictures of them in their homes.
The FTC said in a Tuesday news release that Aaron's will be prohibited from using spyware that captures screenshots or activates the camera on a consumer's computer, except to provide requested technical support.
Aaron's officials previously blamed individual franchisees for the spyware. But the FTC said Aaron's knowingly played a direct role in the use of the spyware. (more)
The FTC said in a Tuesday news release that Aaron's will be prohibited from using spyware that captures screenshots or activates the camera on a consumer's computer, except to provide requested technical support.
Aaron's officials previously blamed individual franchisees for the spyware. But the FTC said Aaron's knowingly played a direct role in the use of the spyware. (more)
No Jail for Skype Sex Scandal Cadets
Australia - The two men at the centre of the Australian Defence Force Academy Skype scandal have avoided jail time.
Daniel McDonald, 21, secretly filmed himself having sex with a female cadet and streamed it live to Dylan Deblaquiere, 21, in a nearby dorm room at ADFA in Canberra in 2011.
Earlier this year a jury found the pair guilty of sending offensive material over the internet without consent. McDonald was also found guilty of an act of indecency.
In sentencing today in the ACT Supreme Court, Acting Justice John Nield rejected jail time... Instead he handed McDonald two 12-month good behaviour bonds, to be served concurrently, and Deblaquiere a single 12-month good behaviour bond. He warned they will go to jail if they breach their orders... "General deterrence has been achieved," he said...
The Department of Defence has confirmed it will take action in relation to McDonald. (more)
Daniel McDonald, 21, secretly filmed himself having sex with a female cadet and streamed it live to Dylan Deblaquiere, 21, in a nearby dorm room at ADFA in Canberra in 2011.
Earlier this year a jury found the pair guilty of sending offensive material over the internet without consent. McDonald was also found guilty of an act of indecency.
In sentencing today in the ACT Supreme Court, Acting Justice John Nield rejected jail time... Instead he handed McDonald two 12-month good behaviour bonds, to be served concurrently, and Deblaquiere a single 12-month good behaviour bond. He warned they will go to jail if they breach their orders... "General deterrence has been achieved," he said...
The Department of Defence has confirmed it will take action in relation to McDonald. (more)
Tuesday, October 22, 2013
Bugging Boss for a Raise Lands Three Employees in Jail
China - Three public officials were each sentenced to 20 months in jail for illegally wiretapping a county Communist Party chief of central China's Hunan Province, according to a local court ruling on Tuesday.

Li Yi, an official with the supervision office of the Mayang Miao Autonomous County Committee of the Communist Party of China (CPC), Yang Fan, a Mayang court officer and Liu Yang, a police officer, were guilty of illegal wiretapping and secretly filming a county Party chief, according to the ruling of the district people's court of Hecheng, Huaihua City, which administers Mayang County.
They were guilty of placing hidden cameras in the office of Hu Jiawu, secretary of the CPC Mayang Miao Autonomous County Committee, spying on Hu and storing video footage on a removable disk between March 13 and Oct. 2 in 2012. They used the footage to try and blackmail Hu for promotion, according to the ruling. (more)

Li Yi, an official with the supervision office of the Mayang Miao Autonomous County Committee of the Communist Party of China (CPC), Yang Fan, a Mayang court officer and Liu Yang, a police officer, were guilty of illegal wiretapping and secretly filming a county Party chief, according to the ruling of the district people's court of Hecheng, Huaihua City, which administers Mayang County.
They were guilty of placing hidden cameras in the office of Hu Jiawu, secretary of the CPC Mayang Miao Autonomous County Committee, spying on Hu and storing video footage on a removable disk between March 13 and Oct. 2 in 2012. They used the footage to try and blackmail Hu for promotion, according to the ruling. (more)
Landlord, Tenant, SpyCam - What Could Possibly...
I stopped posting these stories a while back, simply because there were so many of them. This is just a reminder. The SpyCam is the Number One illegal eavesdropping tool in use today.
Canada - An employee at a major Canadian broadcaster is facing charges of voyeurism, mischief and defamatory libel. 56-year-old David Sealey was arrested Saturday after a man saw a woman he knew secretly filmed in an online video. He notified the victim, who reported the incident to police.
A search warrant was issued and over 150 voyeuristic videos of women were found on a computer inside Sealey’s home, along with recording devices.
The female victim rented a room from Sealey in the Richmond Ave. and Spadina Ave. area and police believe there could be more victims. (more)
Canada - An employee at a major Canadian broadcaster is facing charges of voyeurism, mischief and defamatory libel. 56-year-old David Sealey was arrested Saturday after a man saw a woman he knew secretly filmed in an online video. He notified the victim, who reported the incident to police.
A search warrant was issued and over 150 voyeuristic videos of women were found on a computer inside Sealey’s home, along with recording devices.
The female victim rented a room from Sealey in the Richmond Ave. and Spadina Ave. area and police believe there could be more victims. (more)
Captain Crunch sez... "Here's looking at you, matey."
It’s not quite “Minority Report”-levels of creepiness, but it’s getting there.
Mondelez International, whose properties include Chips Ahoy, Nabisco, Ritz and other high-profile snack brands, says it’s planning to debut a grocery shelf in 2015 that comes equipped with sensors to determine the age and sex of passing customers.
The shelf, which is hooked up to Microsoft’s Kinect controller, will be able to use basic facial features like bone structure to build a profile of a potential snacker, Mondelez chief information officer Mark Dajani told the Wall Street Journal. While pictures of your actual face won’t be stored (yet), aggregate demographic data from thousands of transactions will be. (more)
I spy a tipping point. We are sailing into Fedup Bay. Watch the backlash, me hardies.
 |
| He saw this coming. |
The shelf, which is hooked up to Microsoft’s Kinect controller, will be able to use basic facial features like bone structure to build a profile of a potential snacker, Mondelez chief information officer Mark Dajani told the Wall Street Journal. While pictures of your actual face won’t be stored (yet), aggregate demographic data from thousands of transactions will be. (more)
I spy a tipping point. We are sailing into Fedup Bay. Watch the backlash, me hardies.
Labels:
FutureWatch,
mores,
privacy,
spybot,
surveillance,
tracking
Ex-School IT Director Faces Trial on Wiretapping Charge
PA - The former technology director for Easton Area School District accused of secretly recording a private meeting will face trial in Northampton County Court.
Thomas Drago, 54, acknowledged at a hearing Tuesday that prosecutors have enough evidence to merit a wiretap violation charge. Drago's attorney, Philip Lauer said his client will apply for a first-time offender's program. Drago remains free on $50,000 unsecured bail.
In August, Drago surrendered to authorities for allegedly recording a conversation with school officials without their permission. Drago, 54, of Bushkill Township resigned shortly before an internal probe this year uncovered nude photos on his work computer. (more)
Thomas Drago, 54, acknowledged at a hearing Tuesday that prosecutors have enough evidence to merit a wiretap violation charge. Drago's attorney, Philip Lauer said his client will apply for a first-time offender's program. Drago remains free on $50,000 unsecured bail.
In August, Drago surrendered to authorities for allegedly recording a conversation with school officials without their permission. Drago, 54, of Bushkill Township resigned shortly before an internal probe this year uncovered nude photos on his work computer. (more)
Sunday, October 20, 2013
Doc v. Doc Bugging Ends in House Call to Graybar Motel
India - Spying on his wife landed a qualified doctor husband behind bars on Saturday.
Dr Gyaneshwar Maini, who owns a private hospital, was arrested for keeping a tab on the locations and conversations of his wife, while installing a high-quality Global Positioning System (GPS) along with a micro-mike packed in a black box in the steering wheel of her sedan car for the past eight months.
The victim is also a qualified doctor and employed with a leading private hospital in Mohali.
Police have also decided to take legal action against employees of a private firm, who installed the device in the car of the woman.
The GPS system, along with a mike, was in a black box worth Rs 18,000 ($293.76), which was detected with the help of an expert from a private company, which supplies these gadgets.
The black box was linked with a 10-digit cell number used by Dr Maini's friend. Police said the installer of the device in the car has identified Dr Maini. In her complaint to the police, the woman suspected that there was some instrument in her car, which was keeping a tab on her movements and conversations, about which her husband would come to know even without her telling him. (more)
Dr Gyaneshwar Maini, who owns a private hospital, was arrested for keeping a tab on the locations and conversations of his wife, while installing a high-quality Global Positioning System (GPS) along with a micro-mike packed in a black box in the steering wheel of her sedan car for the past eight months.
The victim is also a qualified doctor and employed with a leading private hospital in Mohali.
Police have also decided to take legal action against employees of a private firm, who installed the device in the car of the woman.
The GPS system, along with a mike, was in a black box worth Rs 18,000 ($293.76), which was detected with the help of an expert from a private company, which supplies these gadgets.
The black box was linked with a 10-digit cell number used by Dr Maini's friend. Police said the installer of the device in the car has identified Dr Maini. In her complaint to the police, the woman suspected that there was some instrument in her car, which was keeping a tab on her movements and conversations, about which her husband would come to know even without her telling him. (more)
Labels:
amateur,
eavesdropping,
GPS,
lawsuit,
spybot,
surveillance,
tracking
No more, "Gee, I thought you said..." — Record Your Cell Phone Calls
Here's a useful item for PIs, Security and LEOs — a way to document important cell phone calls, without app sapping charges. No more, "Gee, I thought you said..."
Recording Cell Phone conversations using apps is not possible on iPhone, Droid or BlackBerry without paying per minute charges. The Call Mynah Cell Phone Recorder gives you complete control of Recording Cell Phone Calls. You decide to Record Mobile Phone Calls or not, set up your Call Mynah to Record Cell Phone (all calls) or only as you choose.
Recording Cell Phone conversations using apps is not possible on iPhone, Droid or BlackBerry without paying per minute charges. The Call Mynah Cell Phone Recorder gives you complete control of Recording Cell Phone Calls. You decide to Record Mobile Phone Calls or not, set up your Call Mynah to Record Cell Phone (all calls) or only as you choose.
- 340 hours of Cell Phone Recording storage
- Connects to any mobile phone via Bluetooth to create a simple Cell Phone Call Recorder
- Automatically Record Cell Phone Calls (manual recording options too)
- Saves all Cell Phone Records, call details (date, time, number, duration, call type)
- Add comments to calls and flag as 'Important'
- Upload calls to your PC for easy management (software supplied)
- 150 Hours standby, 8 hours talking before battery charge
- Call recording warn tone or prompt can be sent to callers (optional)
- Handset, Speakerphone or Headset (supplied) operation
- Security features to prevent unauthorized listening to your calls (more)
Saturday, October 19, 2013
RARE - Politico Admits to Phone Tapping & Butt Bugging
Zambia - Zambian President Admits to Spying on Fellow Officials
During his 2011 election campaign, the current president of Zambia, Michael Sata rose to popularity by playing on anti-Chinese sentiment and the anger of laborers over poor standards at the many large Chinese-run mines in Zambia... According to Global Voices, he tapped the phone of his foreign minister and also planted a bug underneath a chair in the office of the leader of Barotseland region, whose citizens want to secede from Zambia. (more)
During his 2011 election campaign, the current president of Zambia, Michael Sata rose to popularity by playing on anti-Chinese sentiment and the anger of laborers over poor standards at the many large Chinese-run mines in Zambia... According to Global Voices, he tapped the phone of his foreign minister and also planted a bug underneath a chair in the office of the leader of Barotseland region, whose citizens want to secede from Zambia. (more)
Industrial Espionage Threats to Small and Medium-sized Enterprises (SMEs)
The former president of a transportation company in Texas was sentenced in federal court last month to five years in prison for hacking into his former employer’s computer network and stealing proprietary business information he intended to use for his start-up. The case underscores the fact that much like major corporations, small and medium-sized enterprises (SMEs) are targets for industrial espionage.
SMEs are in many ways are more vulnerable than big businesses, which are capable of employing a small army of security specialists to safeguard intellectual property, said Michel Juneau-Katsuya, president and CEO of the Northgate Group, an international security firm based in Canada.
SMEs very often perceive security as an extravagance. “In times of austerity that sin of security expense is one of the first things that get eliminated,” he told IMT.
To a certain extent, the strategic importance of protection has become even more critical for SMEs. When it comes to stolen prototypes or proprietary technology, larger companies seem more capable of absorbing the loss. “If you’re a big guy and you lose a gadget, you can probably recover from that,” he said. “But if you’re a small or medium-sized company, you lose your intellectual property, you might actually break your back and lose your company." (more)
Sometimes it is smart to be extravagant. ~Kevin
SMEs are in many ways are more vulnerable than big businesses, which are capable of employing a small army of security specialists to safeguard intellectual property, said Michel Juneau-Katsuya, president and CEO of the Northgate Group, an international security firm based in Canada.
SMEs very often perceive security as an extravagance. “In times of austerity that sin of security expense is one of the first things that get eliminated,” he told IMT.
To a certain extent, the strategic importance of protection has become even more critical for SMEs. When it comes to stolen prototypes or proprietary technology, larger companies seem more capable of absorbing the loss. “If you’re a big guy and you lose a gadget, you can probably recover from that,” he said. “But if you’re a small or medium-sized company, you lose your intellectual property, you might actually break your back and lose your company." (more)
Sometimes it is smart to be extravagant. ~Kevin
Yet Another Bird Spying Story
Headlines of fowl accused of spying for Israel are making rounds again in Middle Eastern press, with the most recent bird of espionage 'arrested' in Lebanon. Hezbollah and Iranian-affiliated websites reported today that an Israeli 'spy eagle' had been caught this past weekend in Lebanon.
According to one Lebanese news site, the eagle had been caught in the town of Achkout by local hunters who alerted authorities after discovering that the bird had an ID ring attached to its leg with the words "Israel" and "Tel Aviv University" printed on it. (really bad spycraft :)
The Hezbollah- affiliated Al-Manar TV, whose news site's section on Israel is simply called "Enemy Entity," claimed that the eagle was one of many birds sent by Israel to spy and gather information via GPS transmitters across the Middle East. The report pointed to the "arrest of birds carrying similar devices" in Saudi Arabia, Turkey and most recently in Egypt. (more) (sing-a-long)
According to one Lebanese news site, the eagle had been caught in the town of Achkout by local hunters who alerted authorities after discovering that the bird had an ID ring attached to its leg with the words "Israel" and "Tel Aviv University" printed on it. (really bad spycraft :)
 |
| "On the lookout for bird spies here." |
Gordon Ramsay Knows What's Cooking... in His Daughter's Bedroom... using a SpyCam
Gordon Ramsay has admitted to being all kinds of inappropriate by revealing he put a video camera in his 15 year old daughter's bedroom to see what she gets up to with her boyfriend.
It seems Ramsay is not the first. Last year an American college student was granted a civil stalking order against her overprotective parents after they installed spying software on her electronic devices.(more)
It seems Ramsay is not the first. Last year an American college student was granted a civil stalking order against her overprotective parents after they installed spying software on her electronic devices.(more)
Business Espionage - Top Businessman Bugs Other Top Businessman
Australia - When prominent Melbourne businessmen Grant Custance and David Morrell first crossed paths in 1975 as students at prestigious Geelong Grammar, neither could have foreseen that almost 40 years later they would be locked in a brutal feud involving police, lawyers, tracking devices and crisis management consultants.
The public stoush between the Toorak heavyweights, which dates to a business deal between the two in 2010 that landed Mr Custance in the Magistrates Court, has taken a new twist, with allegations Mr Custance paid for a private detective to shadow Mr Morrell and scrutinise his ''business practices and moral conduct''.
An electronic tracking device was fitted to Mr Morrell's luxury car in March last year, with other plans to ''manipulate and extract information from mobile phones, computers and listening devices'', according to a report prepared for Mr Custance by private investigator and former police officer Damian Marrett. The two-week surveillance was code-named Operation Bulldog and included extensive background checks, company searches and tailing Mr Morrell, who is a buyer's advocate with an extensive list of wealthy and powerful clients. (more)
The public stoush between the Toorak heavyweights, which dates to a business deal between the two in 2010 that landed Mr Custance in the Magistrates Court, has taken a new twist, with allegations Mr Custance paid for a private detective to shadow Mr Morrell and scrutinise his ''business practices and moral conduct''.
An electronic tracking device was fitted to Mr Morrell's luxury car in March last year, with other plans to ''manipulate and extract information from mobile phones, computers and listening devices'', according to a report prepared for Mr Custance by private investigator and former police officer Damian Marrett. The two-week surveillance was code-named Operation Bulldog and included extensive background checks, company searches and tailing Mr Morrell, who is a buyer's advocate with an extensive list of wealthy and powerful clients. (more)
Thursday, October 17, 2013
Three Tips to Keep Your Mobile Data Safe
Keeping your mobile gear secure while you’re zipping across the grid is tricky business. Laptops and tablets—veritable gold mines of personal information—are popular targets for thieves. Law enforcement officials, meanwhile, could confiscate your smartphone and then examine the data—merely as a result of a routine traffic stop.
If you’re packing an Android device, it gets even trickier, because with such a device, you stand a better chance of falling prey to the booming mobile malware market. Independent malware testing lab AV-Test had less than 10,000 Android malware samples in its database by late 2011. Now, two years later, that number has blossomed to around 1.3 million.
Step One:
Encrypt everything
One of the easiest things you can do to protect an Android or iOS device is to take advantage of built-in hardware encryption. This feature will turn the data on your phone into nearly unreadable junk—unless it's properly unlocked with your password.
Let's start with the easy one: iOS. Owners of iPhones or iPads can rest easy knowing the data is already encrypted, provided you create a passcode from the lock screen.
Step Two:
Keep malware at bay
Android users are particularly vulnerable to malware. Google, unlike Apple, doesn’t vet applications before they go live on Google Play. This has proven an easy way for malware creators to sneak malicious apps onto Google’s app store. Malware-laden apps range from those offering free device wallpaper to games, and even to impostors that try to look like popular apps.
That’s why security vendors such as Avast, Kaspersky, and Lookout offer antivirus and security apps for Android to help keep you secure online. But how good are these apps, really? Back in late 2011, results from the AV-Test lab found that the free solutions were nearly useless.
Step Three:
Go Covert
You can protect your data from being nabbed by a Customs agent and downloaded into some massive data silo in the Utah desert. The Electronic Frontier Foundation suggests an interesting option: Leave the hard drive at home and boot your laptop from an SD card.
(Full instructions on how to create a Ubuntu boot disk or USB boot drive in Ubuntu guide for displaced Windows users.) ...Even if you don’t have any sensitive data to protect, this is such a great, secret-agent-style use for your laptop that you might want to try it simply for the cool factor. (more)
If you’re packing an Android device, it gets even trickier, because with such a device, you stand a better chance of falling prey to the booming mobile malware market. Independent malware testing lab AV-Test had less than 10,000 Android malware samples in its database by late 2011. Now, two years later, that number has blossomed to around 1.3 million.
Step One:
Encrypt everything
One of the easiest things you can do to protect an Android or iOS device is to take advantage of built-in hardware encryption. This feature will turn the data on your phone into nearly unreadable junk—unless it's properly unlocked with your password.
Let's start with the easy one: iOS. Owners of iPhones or iPads can rest easy knowing the data is already encrypted, provided you create a passcode from the lock screen.
Step Two:
Keep malware at bay
Android users are particularly vulnerable to malware. Google, unlike Apple, doesn’t vet applications before they go live on Google Play. This has proven an easy way for malware creators to sneak malicious apps onto Google’s app store. Malware-laden apps range from those offering free device wallpaper to games, and even to impostors that try to look like popular apps.
That’s why security vendors such as Avast, Kaspersky, and Lookout offer antivirus and security apps for Android to help keep you secure online. But how good are these apps, really? Back in late 2011, results from the AV-Test lab found that the free solutions were nearly useless.
Step Three:
Go Covert
You can protect your data from being nabbed by a Customs agent and downloaded into some massive data silo in the Utah desert. The Electronic Frontier Foundation suggests an interesting option: Leave the hard drive at home and boot your laptop from an SD card.
(Full instructions on how to create a Ubuntu boot disk or USB boot drive in Ubuntu guide for displaced Windows users.) ...Even if you don’t have any sensitive data to protect, this is such a great, secret-agent-style use for your laptop that you might want to try it simply for the cool factor. (more)
Labels:
amateur,
Android,
App,
cell phone,
computer,
counterespionage,
encryption,
Tips
Wednesday, October 16, 2013
Eavesdropping on the Brain: Mind-Reading Devices Could be Possible in the Future
Could we read minds? Scientists are certainly one step closer after this latest study. Researchers have managed to collect the first solid evidence that the pattern of brain activity seen in someone performing a mathematical exercise under experimentally controlled conditions very similar to that observed when the person engages in quantitative thought in the course of daily life. The findings could lead researchers to a way to "eavesdrop" on the brain in real life.
 "This is exciting and a little scary," said Henry Greely who played no role in the study but is familiar with its contents, in a news release. "It demonstrates, first, that we can see when someone's dealing with numbers and, second, that we may conceivably someday be able to manipulate the brain to affect how someone deals with numbers."
"This is exciting and a little scary," said Henry Greely who played no role in the study but is familiar with its contents, in a news release. "It demonstrates, first, that we can see when someone's dealing with numbers and, second, that we may conceivably someday be able to manipulate the brain to affect how someone deals with numbers."
In order to examine the thought processes of volunteers, the researchers monitored electrical activity in a region of the brain called the intraparietal sulcus. This part of the brain is known to be important in attention and hand motion. Previous studies have hinted that some nerve-cell clusters in this area are also involved in numerosity, the mathematical equivalent of literacy.
The scientists used a method called intracranial recording, which allowed them to monitor brain activity while people were immersed in real-life situations. The researchers tapped into the brains of three volunteers who were being evaluated for possible surgical treatment of their recurring, drug-resistant epileptic seizures; this involved removing a portion of the patient's skull and positioning packets of electrodes against the exposed brain surface. (more)
 "This is exciting and a little scary," said Henry Greely who played no role in the study but is familiar with its contents, in a news release. "It demonstrates, first, that we can see when someone's dealing with numbers and, second, that we may conceivably someday be able to manipulate the brain to affect how someone deals with numbers."
"This is exciting and a little scary," said Henry Greely who played no role in the study but is familiar with its contents, in a news release. "It demonstrates, first, that we can see when someone's dealing with numbers and, second, that we may conceivably someday be able to manipulate the brain to affect how someone deals with numbers." In order to examine the thought processes of volunteers, the researchers monitored electrical activity in a region of the brain called the intraparietal sulcus. This part of the brain is known to be important in attention and hand motion. Previous studies have hinted that some nerve-cell clusters in this area are also involved in numerosity, the mathematical equivalent of literacy.
The scientists used a method called intracranial recording, which allowed them to monitor brain activity while people were immersed in real-life situations. The researchers tapped into the brains of three volunteers who were being evaluated for possible surgical treatment of their recurring, drug-resistant epileptic seizures; this involved removing a portion of the patient's skull and positioning packets of electrodes against the exposed brain surface. (more)
Two Arrested for Eavesdropping on Previous Employer's Conference Call
A man and a woman surrendered at Wilton Police headquarters on warrants issued by Norwalk Superior Court. They were charged with eavesdropping on a former employer.
The two had worked for a business at 64 Danbury Rd and been released from employment in March of 2013. During their employment they had participated in a weekly conference call with other employees beyond the site. During a June 2013 conference call, which included upwards of 50 people one of the employees picked up background noise, according to Wilton Police, and the noise was traced back to the cell phones belonging to the two former employees.
According to Wilton Police, the former employer was concerned because of the confidential nature of the conference calls, which may have included information pertaining to company strategy that might be used by a competitor and information concerning client relationships, billing and operations. (more)
Over the years, you have read many posts here about organizations being victimized by eavesdroppers on their conference calls. Hence...
Spybusters Tip # 879
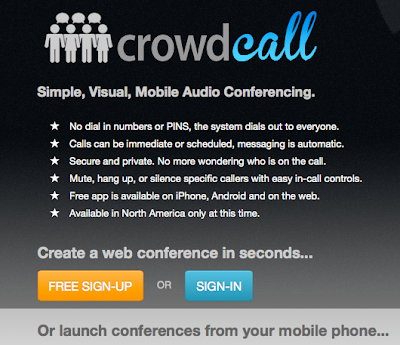
CrowdCall, a specialized conference-calling app available for iOS and Android smartphones and the web.
Instead of scheduling a dial-in line, e-mailing all parties involved and then hoping everyone calls at the appointed time, CrowdCall's interface lets users choose up to 20 participants from their contacts list and LinkedIn connections and dial them immediately (assuming the contacts have added their phone number to their LinkedIn profiles). When participants answer, they simply push "1" to enter the conference--they don't even need to have the app to participate.
...one feature in particular makes it attractive to small businesses. Because the call originator controls invitations, unauthorized participants can't use dial-in information to access the call, providing a measure of security when discussing sensitive information. (more)
The two had worked for a business at 64 Danbury Rd and been released from employment in March of 2013. During their employment they had participated in a weekly conference call with other employees beyond the site. During a June 2013 conference call, which included upwards of 50 people one of the employees picked up background noise, according to Wilton Police, and the noise was traced back to the cell phones belonging to the two former employees.
According to Wilton Police, the former employer was concerned because of the confidential nature of the conference calls, which may have included information pertaining to company strategy that might be used by a competitor and information concerning client relationships, billing and operations. (more)
Over the years, you have read many posts here about organizations being victimized by eavesdroppers on their conference calls. Hence...
Spybusters Tip # 879
CrowdCall, a specialized conference-calling app available for iOS and Android smartphones and the web.
Instead of scheduling a dial-in line, e-mailing all parties involved and then hoping everyone calls at the appointed time, CrowdCall's interface lets users choose up to 20 participants from their contacts list and LinkedIn connections and dial them immediately (assuming the contacts have added their phone number to their LinkedIn profiles). When participants answer, they simply push "1" to enter the conference--they don't even need to have the app to participate.
...one feature in particular makes it attractive to small businesses. Because the call originator controls invitations, unauthorized participants can't use dial-in information to access the call, providing a measure of security when discussing sensitive information. (more)
Video Game CEO Throws Employees Arrested for Spying Under the Virtual Bus
Two Bohemia Interactive developers have been arrested on
the Greek island of Lemnos for spying, company CEO Marek Spanel
confirmed today. The executive explained on the company's official forums that the firm will not go into further details on the matter.
 According to Greek reports
surfacing recently, the pair were in possession of videos and photos of
military compounds in Lemnos at the time of their arrest. The Greek
island is the main location for Bohemia Interactive's upcoming shooter Arma III, with the two reportedly claiming they were collecting reference material for the game.
According to Greek reports
surfacing recently, the pair were in possession of videos and photos of
military compounds in Lemnos at the time of their arrest. The Greek
island is the main location for Bohemia Interactive's upcoming shooter Arma III, with the two reportedly claiming they were collecting reference material for the game.
UPDATE: Bohemia Interactive CEO Marek Spanel has released a statement about the incident, claiming the two employees were visiting the island of Lemnos "with the sole purpose of experiencing the island's beautiful surroundings".
"Since its establishment in 1999, Bohemia Interactive has created games based only upon publicly available information," Spanel said. "We always respect the law and we've never instructed anybody to violate the laws of any country. The same is true for Arma III."
Spanel said the studio is training its efforts on supporting the two employees arrested in Greece, and that he hopes the incident is nothing more than "an unfortunate misunderstanding of their passion as artists and creators of virtual worlds". (more)
 According to Greek reports
surfacing recently, the pair were in possession of videos and photos of
military compounds in Lemnos at the time of their arrest. The Greek
island is the main location for Bohemia Interactive's upcoming shooter Arma III, with the two reportedly claiming they were collecting reference material for the game.
According to Greek reports
surfacing recently, the pair were in possession of videos and photos of
military compounds in Lemnos at the time of their arrest. The Greek
island is the main location for Bohemia Interactive's upcoming shooter Arma III, with the two reportedly claiming they were collecting reference material for the game. UPDATE: Bohemia Interactive CEO Marek Spanel has released a statement about the incident, claiming the two employees were visiting the island of Lemnos "with the sole purpose of experiencing the island's beautiful surroundings".
"Since its establishment in 1999, Bohemia Interactive has created games based only upon publicly available information," Spanel said. "We always respect the law and we've never instructed anybody to violate the laws of any country. The same is true for Arma III."
Spanel said the studio is training its efforts on supporting the two employees arrested in Greece, and that he hopes the incident is nothing more than "an unfortunate misunderstanding of their passion as artists and creators of virtual worlds". (more)
Tuesday, October 15, 2013
Forget the NSA. That Smartphone Snooper May Be Your Spouse
It's not just the National Security Agency spying on smartphones. Many ordinary people are also using sophisticated software to eavesdrop on the wireless communications of their lovers, children and business rivals.
According to a new study that examined the data traffic of mobile devices operating on the Middle Eastern network of a European carrier, hundreds of people had some form of surveillance software installed on their phones.
These aren't malicious apps that the users had been tricked into downloading. They're pieces of commercially available spyware that people with physical access to the devices have installed to secretly log each text message, phone call and contact, and in some cases, eavesdrop on calls in real time. (more)
According to a new study that examined the data traffic of mobile devices operating on the Middle Eastern network of a European carrier, hundreds of people had some form of surveillance software installed on their phones.
These aren't malicious apps that the users had been tricked into downloading. They're pieces of commercially available spyware that people with physical access to the devices have installed to secretly log each text message, phone call and contact, and in some cases, eavesdrop on calls in real time. (more)
Business Espionage Cautionary Tale - How Bugs Get Planted and More
Last Christmas Eve, a man broke into Adara Networks’ San Jose headquarters, using copies of both physical and electronic keys. He seemed to know exactly what he was looking for. The thief left rows of desks untouched as he cruised toward the lab holding the source code for Adara’s proprietary data-center networking software. Fortunately for Adara, he triggered an alarm on the lab door and fled.
“Snatch and grab” crimes, in which crooks enter an office and carts off a few loose laptops, happen occasionally in Silicon Valley. Chief Executive Officer Eric Johnson sensed that his case was more serious, though. Adara’s next-generation networking technology could be attractive to nations hoping to capture more of the global telecommunications market. So Johnson brought in contractors to sweep the offices for bugs, in case a foreign government was listening...
To make it harder for the thieves, some companies are paying for “penetration testing,” hiring security consultants to probe their defenses... Silicon Valley has a long history of thievery and espionage. (more)
Many of my reports for clients contain details and photos about how an after-hours espionage/eavesdropping attack can easily happen to them. They receive recommendations for remediation, too.
Spybuster Tip #004: Periodic inspections help deter penetrations and information losses. Conduct them once per quarter.
“Snatch and grab” crimes, in which crooks enter an office and carts off a few loose laptops, happen occasionally in Silicon Valley. Chief Executive Officer Eric Johnson sensed that his case was more serious, though. Adara’s next-generation networking technology could be attractive to nations hoping to capture more of the global telecommunications market. So Johnson brought in contractors to sweep the offices for bugs, in case a foreign government was listening...
To make it harder for the thieves, some companies are paying for “penetration testing,” hiring security consultants to probe their defenses... Silicon Valley has a long history of thievery and espionage. (more)
Many of my reports for clients contain details and photos about how an after-hours espionage/eavesdropping attack can easily happen to them. They receive recommendations for remediation, too.
Spybuster Tip #004: Periodic inspections help deter penetrations and information losses. Conduct them once per quarter.
D-Link Promises Fix for Home Router Firmware Flaw by End of the Month
A backdoor has been found in firmware used in several models of D-Link and Planex home routers. The flaw can easily be exploited to take
control of vulnerable devices and spy on browsing activity. D-Link is
aware of the issue and says a fix will be available by the end of the
month. (more)
How NSA Breakthrough May Allow 'Burner' Phone Tracking
via Dan Goodin, Ars Technica
In the HBO hit series The Wire, disposable cell phones were the bane of detectives' lives. Drug dealers obtained these prepaid "burners" in mass quantities with cash at multiple stores hundreds of miles away from where they were used.
After a week or two of use, a crook would destroy one cheap handset and fetch a new one. The Baltimore Police detectives' inability to tap the phones stymied their investigation into one of the city's most ruthless crime families — until they found a way to track the devices.
The National Security Agency may have made a similar breakthrough. Cato Institute researcher Julian Sanchez recently pulled a few sentences from a 2009 declaration by NSA Director Keith Alexander. They describe an unnamed tool that routinely accessed the vast database of call records assembled by the NSA. Sanchez argues that the purpose may be to identify burner phones used by NSA targets. (more) (via Schneier)
In the HBO hit series The Wire, disposable cell phones were the bane of detectives' lives. Drug dealers obtained these prepaid "burners" in mass quantities with cash at multiple stores hundreds of miles away from where they were used.
After a week or two of use, a crook would destroy one cheap handset and fetch a new one. The Baltimore Police detectives' inability to tap the phones stymied their investigation into one of the city's most ruthless crime families — until they found a way to track the devices.
The National Security Agency may have made a similar breakthrough. Cato Institute researcher Julian Sanchez recently pulled a few sentences from a 2009 declaration by NSA Director Keith Alexander. They describe an unnamed tool that routinely accessed the vast database of call records assembled by the NSA. Sanchez argues that the purpose may be to identify burner phones used by NSA targets. (more) (via Schneier)
The Taliban's Ultimate Bug? - A Bomb in a Microphone!
A bomb planted inside a mosque killed the governor of Afghanistan's eastern Logar province as he was delivering a speech Tuesday morning to mark the Muslim holiday of Eid al-Adha, officials said...
Tuesday's explosion took place as Jamal was speaking inside the mosque to worshipers gathered for one of Islam's holiest days, said Logar's deputy police chief, Rais Khan Abbul Rahimzai.
The bomb was apparently planted inside a microphone in the front part of the mosque, said two officials, speaking on condition of anonymity because they were not authorized to speak to the media. (more)
Tuesday's explosion took place as Jamal was speaking inside the mosque to worshipers gathered for one of Islam's holiest days, said Logar's deputy police chief, Rais Khan Abbul Rahimzai.
The bomb was apparently planted inside a microphone in the front part of the mosque, said two officials, speaking on condition of anonymity because they were not authorized to speak to the media. (more)
Monday, October 14, 2013
The CIA’s Most Highly-Trained Spies Weren’t Even Human
There would be a rustle of oily black feathers as a raven settled on the window ledge of a once-grand apartment building in some Eastern European capital. The bird would pace across the ledge a few times but quickly depart. In an apartment on the other side of the window, no one would shift his attention from the briefing papers or the chilled vodka set out on a table. Nor would anything seem amiss in the jagged piece of gray slate resting on the ledge, seemingly jetsam from the roof of an old and unloved building.
Those in the apartment might be dismayed to learn, however, that the slate had come not from the roof but from a technical laboratory at CIA headquarters in Langley, Virginia. In a small cavity at the slate’s center was an electronic transmitter powerful enough to pick up their conversation. The raven that transported it to the ledge was no random city bird, but a U.S.-trained intelligence asset.
Half a world away from the murk of the cold war, it would be a typical day at the I.Q. Zoo, one of the touristic palaces that dotted the streets of Hot Springs, Arkansas, in the 1960s. With their vacationing parents inca tow, children would squeal as they watched chickens play baseball, macaws ride bicycles, ducks drumming and pigs pawing at pianos. You would find much the same in any number of mom-and-pop theme parks or on television variety shows of the era. But chances are that if an animal had been trained to do something whimsically human, the animal—or the technique—came from Hot Springs.
Two scenes, seemingly disjointed: the John le Carré shadows against the bright midway lights of county-fair Americana. But wars make strange bedfellows, and in one of the most curious, if little-known, stories of the cold war, the people involved in making poultry dance or getting cows to play bingo were also involved in training animals, under government contract, for defense and intelligence work. (more)
Those in the apartment might be dismayed to learn, however, that the slate had come not from the roof but from a technical laboratory at CIA headquarters in Langley, Virginia. In a small cavity at the slate’s center was an electronic transmitter powerful enough to pick up their conversation. The raven that transported it to the ledge was no random city bird, but a U.S.-trained intelligence asset.
Half a world away from the murk of the cold war, it would be a typical day at the I.Q. Zoo, one of the touristic palaces that dotted the streets of Hot Springs, Arkansas, in the 1960s. With their vacationing parents inca tow, children would squeal as they watched chickens play baseball, macaws ride bicycles, ducks drumming and pigs pawing at pianos. You would find much the same in any number of mom-and-pop theme parks or on television variety shows of the era. But chances are that if an animal had been trained to do something whimsically human, the animal—or the technique—came from Hot Springs.
Two scenes, seemingly disjointed: the John le Carré shadows against the bright midway lights of county-fair Americana. But wars make strange bedfellows, and in one of the most curious, if little-known, stories of the cold war, the people involved in making poultry dance or getting cows to play bingo were also involved in training animals, under government contract, for defense and intelligence work. (more)
Labels:
CIA,
espionage,
government,
historical,
nature,
spybot,
weird
Sunday, October 13, 2013
NIST - Not Indelibly Secure & Trustworthy?
The National Institute of Standards and Technology (NIST) has an image problem.
Last month, revelations surfaced indicating that the National Security Agency (NSA) may have planted a vulnerability in a widely used NIST-approved encryption algorithm to facilitate its spying activities. And cryptographers are also questioning subtle changes that might weaken a new security algorithm called Secure Hash Algorithm-3, or SHA-3.
Encryption experts say NIST’s reputation has been seriously undermined but that the security community would like to continue using it as a standards body if it can show that it has reformed. (more)
Last month, revelations surfaced indicating that the National Security Agency (NSA) may have planted a vulnerability in a widely used NIST-approved encryption algorithm to facilitate its spying activities. And cryptographers are also questioning subtle changes that might weaken a new security algorithm called Secure Hash Algorithm-3, or SHA-3.
Encryption experts say NIST’s reputation has been seriously undermined but that the security community would like to continue using it as a standards body if it can show that it has reformed. (more)
Lawsuit Blames Companies for Hiring Voyeur
IN - A Hammond man who was convicted in 2011 of using his cellphone to record a woman in a Kmart changing room had a voyeurism conviction, so the victim is suing him, Kmart and the construction and staffing companies that hired him.
The companies shouldn’t have hired a convicted sex offender to remodel the bathroom, said Randy K. Fleming of Sarkisian, Fleming, Grabarek, Sarkisian.
The suit names Mark Anthony Fetzko, 28, of Hammond, as well as Kmart, Sturzenbecker Construction Company Inc. and Labor Ready Midwest Indiana as defendants. (more)
Blue Light Special - "Attention business owners."
Avoid this type of lawsuit by doing your due diligence.
• Conduct quality background checks before hiring.
• Conduct periodic inspections for planted spycams in all areas where the visiting public and your employees have an expectation of privacy.
The companies shouldn’t have hired a convicted sex offender to remodel the bathroom, said Randy K. Fleming of Sarkisian, Fleming, Grabarek, Sarkisian.
The suit names Mark Anthony Fetzko, 28, of Hammond, as well as Kmart, Sturzenbecker Construction Company Inc. and Labor Ready Midwest Indiana as defendants. (more)
Blue Light Special - "Attention business owners."
Avoid this type of lawsuit by doing your due diligence.
• Conduct quality background checks before hiring.
• Conduct periodic inspections for planted spycams in all areas where the visiting public and your employees have an expectation of privacy.
Saturday, October 12, 2013
One Way Your Android Phone Can Get a Virus
Kevin McNamee stands in front of his laptop on a low stage, a phone in his hand as he scrolls through a program showing his phone’s screen, magnified on a projector screen beside him.
 Bits of code start flashing up the screen as he injects command-and-control malware into the command window of the app for Rovio Entertainment Ltd.’s trademark game, Angry Birds – transforming the app into a new version he’s dubbed “Very Angry Birds.”
Bits of code start flashing up the screen as he injects command-and-control malware into the command window of the app for Rovio Entertainment Ltd.’s trademark game, Angry Birds – transforming the app into a new version he’s dubbed “Very Angry Birds.”
“And here we go,” he says, frowning down at the screen as he begins to run the new app.
McNamee was presenting at Sector 2013, a conference on all things IT security held in Toronto from Oct. 7 to 9. The director of Kindsight Security Labs at Alcatel-Lucent Canada Inc. in Ottawa, McNamee wanted to show how simple it is to use an Android software development kit to add in malware.
When a user downloads a malware-infested version of the app, he or she is asked to sign off on all kinds of permissions, like access to contact lists, the camera, and so on. If a user carelessly checks off ‘yes’ on all the options, the app is activated with a piece of malware called “Droid Whisper,” and the hacker who wrote it now has access to the phone owner’s contact lists, location, messages, camera, and microphone. That means someone can remotely listen in and record phone conversations, send messages to the phone owner’s contacts, and even take pictures from that phone.
This process can work by injecting malware into basically any Android app by using its application package tool, and it just runs as a service in the background, McNamee said. (more) (presentation)
 Bits of code start flashing up the screen as he injects command-and-control malware into the command window of the app for Rovio Entertainment Ltd.’s trademark game, Angry Birds – transforming the app into a new version he’s dubbed “Very Angry Birds.”
Bits of code start flashing up the screen as he injects command-and-control malware into the command window of the app for Rovio Entertainment Ltd.’s trademark game, Angry Birds – transforming the app into a new version he’s dubbed “Very Angry Birds.” “And here we go,” he says, frowning down at the screen as he begins to run the new app.
McNamee was presenting at Sector 2013, a conference on all things IT security held in Toronto from Oct. 7 to 9. The director of Kindsight Security Labs at Alcatel-Lucent Canada Inc. in Ottawa, McNamee wanted to show how simple it is to use an Android software development kit to add in malware.
When a user downloads a malware-infested version of the app, he or she is asked to sign off on all kinds of permissions, like access to contact lists, the camera, and so on. If a user carelessly checks off ‘yes’ on all the options, the app is activated with a piece of malware called “Droid Whisper,” and the hacker who wrote it now has access to the phone owner’s contact lists, location, messages, camera, and microphone. That means someone can remotely listen in and record phone conversations, send messages to the phone owner’s contacts, and even take pictures from that phone.
This process can work by injecting malware into basically any Android app by using its application package tool, and it just runs as a service in the background, McNamee said. (more) (presentation)
George Washington's Top-Secret Spy Ring Coming to Cable TV
VA - Gov. Bob McDonnell says a television series about George Washington's top-secret spy ring will be filmed in central Virginia.
The pilot for the AMC Studios project was shot in the Richmond area earlier this year, and AMC has ordered a 10-episode season that will start on AMC in 2014. McDonnell says the first season of the series will begin filming this fall and be completed in the spring.
The working title for the series is "Turn." It's based on the nonfiction book "Washington's Spies: The Story of America's First Spy Ring," by Alexander Rose. It's about the band of spies who helped Washington win the Revolutionary War. (more)
The pilot for the AMC Studios project was shot in the Richmond area earlier this year, and AMC has ordered a 10-episode season that will start on AMC in 2014. McDonnell says the first season of the series will begin filming this fall and be completed in the spring.
The working title for the series is "Turn." It's based on the nonfiction book "Washington's Spies: The Story of America's First Spy Ring," by Alexander Rose. It's about the band of spies who helped Washington win the Revolutionary War. (more)
Subscribe to:
Comments (Atom)