Foreign travel always brings security questions. For many countries the advice is mild, like "don't carry too much cash," and "don't drink the water".
Foreign travel always brings security questions. For many countries the advice is mild, like "don't carry too much cash," and "don't drink the water".Some countries are far different. They want your information. These are usually, but not always, "closed society countries".
The following is General Information Security Awareness & Advice to keep in mind while traveling in (or through) closed society countries. You may not be able to employ every bit of advice, in every situation. but everything that you can do will help. Security is a "how high can we build the wall" effort.
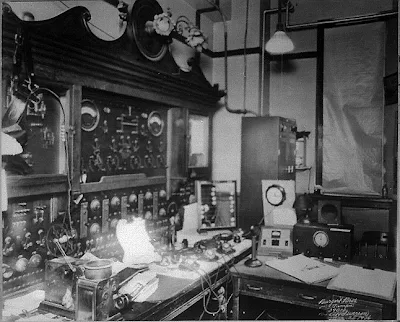
Awareness
1. Assume your communications can be monitored by the government. This includes hotel, meeting room, business office bugging, and all forms of electronic communications.
2. The use of communications encryption is generally illegal. Certain exceptions may be available to financial industry transactions. Encryption of data on your personal devices is usually allowed, though if seized you will be asked for the decryption key or password.
3. Conducting a full Technical Surveillance Countermeasures (TSCM) inspection in a closed society country is problematic. Most of the instrumentation required is not allowed to be imported, or requires a special permit. The answer or approval you receive from one government official may not be honored by another government official. Equipment may be confiscated without remuneration. This type of activity could be classified (mistakenly or intentionally) as spying, thus subjecting the participants to imprisonment, and the company to fines, loss of business, etc.
4. Anything left unattended may is subject to retrieval of information from it. This includes: computers, cell phones, USB sticks, external hard drives, and written items.
5. Spyware may be introduced onto computers, cell phones, and other devices which can hold computer instructions. This may be accomplished while the device is unattended, or via unintentional download from email or web sites.
6. Gifts may contain surveillance electronics (bugs, tracking, etc.).
7. Electronic surveillance devices may be planted in your transportation (rental car, corporate aircraft, etc.)
8. Personal surveillance and social engineering tactics may be used against you. Tactics may include: location tracking, to "the friendly stranger" who wants to help or talk, to engineering compromising positions for blackmail purposes.
9. Be aware that foreign nationals employed by your company may also be employed by, or under obligation to, the host government.
10. Provide business travelers a copy of: Staying Safe Abroad: Traveling, Working & Living in a Post-9/11 World by Edward L Lee II
by Edward L Lee II
1. Assume your communications can be monitored by the government. This includes hotel, meeting room, business office bugging, and all forms of electronic communications.
2. The use of communications encryption is generally illegal. Certain exceptions may be available to financial industry transactions. Encryption of data on your personal devices is usually allowed, though if seized you will be asked for the decryption key or password.
3. Conducting a full Technical Surveillance Countermeasures (TSCM) inspection in a closed society country is problematic. Most of the instrumentation required is not allowed to be imported, or requires a special permit. The answer or approval you receive from one government official may not be honored by another government official. Equipment may be confiscated without remuneration. This type of activity could be classified (mistakenly or intentionally) as spying, thus subjecting the participants to imprisonment, and the company to fines, loss of business, etc.
4. Anything left unattended may is subject to retrieval of information from it. This includes: computers, cell phones, USB sticks, external hard drives, and written items.
5. Spyware may be introduced onto computers, cell phones, and other devices which can hold computer instructions. This may be accomplished while the device is unattended, or via unintentional download from email or web sites.
6. Gifts may contain surveillance electronics (bugs, tracking, etc.).
7. Electronic surveillance devices may be planted in your transportation (rental car, corporate aircraft, etc.)
8. Personal surveillance and social engineering tactics may be used against you. Tactics may include: location tracking, to "the friendly stranger" who wants to help or talk, to engineering compromising positions for blackmail purposes.
9. Be aware that foreign nationals employed by your company may also be employed by, or under obligation to, the host government.
10. Provide business travelers a copy of: Staying Safe Abroad: Traveling, Working & Living in a Post-9/11 World
Advice
11. Bring only "isolated" electronics (cell phones, cameras, laptops, USB sticks – electronics only to be used on the trip, and which are never connected to other systems (like the company LAN, computer back-ups, or even computer-stored cell phone address books and back-ups).
12. Bring as few of these electronics as possible. If everything can be accomplished with a smartphone, just bring that.
13. Keep the amount of information on these electronics as small as possible.
14. Password protect your electronics. Encrypt the contents. A password alone will not prevent the theft of unencrypted information.
15. Do not purchase electronics while in a closed society country.
16. Keep electronic communications short, dull, boring and devoid of critical information.
17. Create alternate wording for sensitive or confidential information to use when communicating with the home office. Practice using the wording before leaving on the trip. You want to be low-key, but not sneaky.
18. Conduct TSCM inspections which are specially modified to conform with local restrictions. (The common mistake is giving up and deleting inspections from the security strategy.) There is still much that can be done. People other than the government also want your company's information. You can thwart them. Contract with an experienced specialist to accomplish this portion of your information security strategy.
19. Upon returning home, have the IT department check all electronics for spyware, wipe-erase all storage, and store the electronics for use on the next trip. Keep them isolated. Do not connect them to anything.
20. Upon returning home, have a Technical Surveillance Countermeasures (TSCM) inspection conducted of corporate aircraft, and all items brought back: gifts, meeting materials, audio-visual equipment, luggage, etc.
~Kevin